Write a ladder program for a system that counts the number of cars entered into a parking (Assume the system has a sensor at the entrance gate of the parking): If the cars are between 0-39, a yellow lamp is ON. If the cars are between 40-59, an orange lamp is ON. If they are more than 59 a red lamp is ON. After 15s an alarm will start ringing until the system turn off. The system can start counting from the beginning by press a switch (START) that make the counter equal to zero. Use minimum number of instruction.
Write a ladder program for a system that counts the number of cars entered into a parking (Assume the system has a sensor at the entrance gate of the parking): If the cars are between 0-39, a yellow lamp is ON. If the cars are between 40-59, an orange lamp is ON. If they are more than 59 a red lamp is ON. After 15s an alarm will start ringing until the system turn off. The system can start counting from the beginning by press a switch (START) that make the counter equal to zero. Use minimum number of instruction.
Related questions
Question
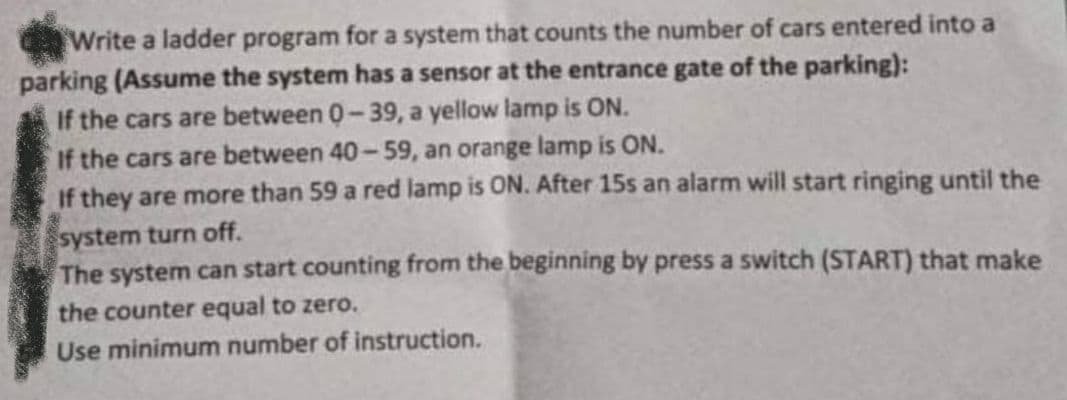
Transcribed Image Text:Write a ladder program for a system that counts the number of cars entered into a
parking (Assume the system has a sensor at the entrance gate of the parking):
If the cars are between 0-39, a yellow lamp is ON.
If the cars are between 40-59, an orange lamp is ON.
If they are more than 59 a red lamp is ON. After 15s an alarm will start ringing until the
system turn off.
The system can start counting from the beginning by press a switch (START) that make
the counter equal to zero.
Use minimum number of instruction.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images
