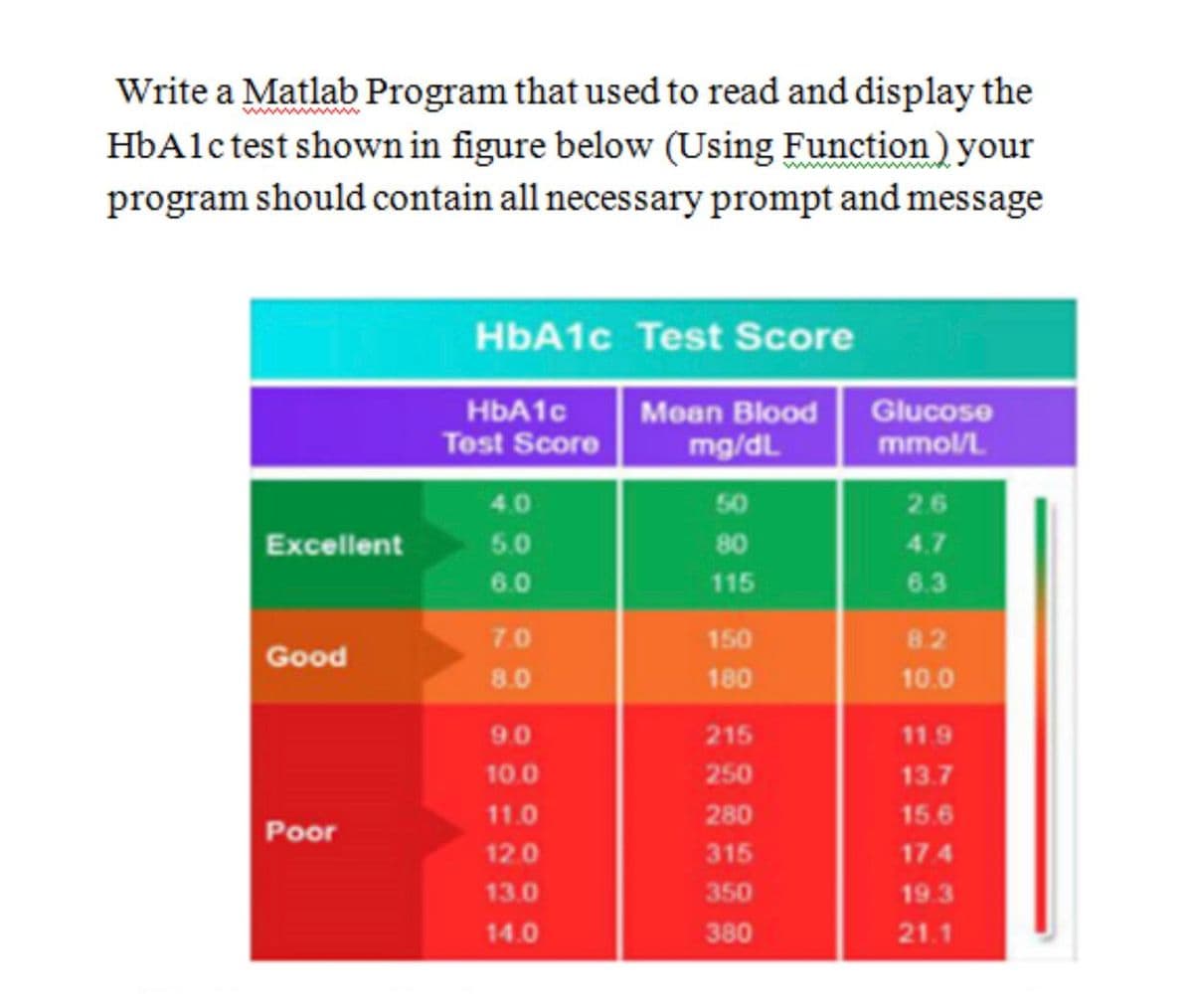
Write a Matlab Program that used to read and display the HbAlctest shown in figure below (Using Function) your program should contain all necessary prompt and message HbA1c Test Score HBA10 Test Score Glucose mmol/L Mean Blood mg/dL 4.0 50 26 Excellent 5.0 80 4.7 6.0 115 6.3 7.0 150 8.2 Good 8.0 180 10.0 90 215 11.9 10.0 250 13.7 11.0 280 15.6 Poor 12.0 315 17.4 13.0 350 19.3 14.0 380 21.1
Write a Matlab Program that used to read and display the HbAlctest shown in figure below (Using Function) your program should contain all necessary prompt and message HbA1c Test Score HBA10 Test Score Glucose mmol/L Mean Blood mg/dL 4.0 50 26 Excellent 5.0 80 4.7 6.0 115 6.3 7.0 150 8.2 Good 8.0 180 10.0 90 215 11.9 10.0 250 13.7 11.0 280 15.6 Poor 12.0 315 17.4 13.0 350 19.3 14.0 380 21.1
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter5: Repetition Statements
Section5.5: A Closer Look: Loop Programming Techniques
Problem 12E: (Program) Write a program that tests the effectiveness of the rand() library function. Start by...
Related questions
Question
Transcribed Image Text:Write a Matlab Program that used to read and display the
HbAlc test shown in figure below (Using Function) your
program should contain all necessary prompt and message
www
HbA1c Test Score
HBA1C
Test Score
Glucose
mmol/L
Moan Blood
mg/dL
4.0
50
26
Excellent
5.0
80
4.7
6.0
115
6.3
7.0
150
82
Good
8.0
180
10.0
90
215
11.9
10.0
250
13.7
11.0
280
15.6
Poor
12.0
315
17.4
13.0
350
19.3
14.0
380
21.1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 5 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr