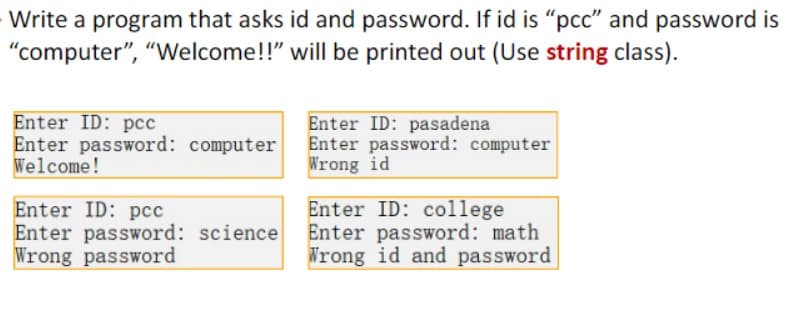
Write a program that asks id and password. If id is "pcc" and password is "computer", "Welcome!!" will be printed out (Use string class). Enter ID: pcc Enter password: computer Welcome! Enter ID: pcc Enter password: science Wrong password Enter ID: pasadena Enter password: computer Wrong id Enter ID: college Enter password: math Wrong id and password
Q: I am interested in learning more about the ethical dilemmas that system analysts face.
A: Answer:
Q: Having a wide variety of IT systems in use may provide its own challenges. What's the best strategy…
A: Introduction: From the perspective of the entire firm, integration It is challenging to agree on the…
Q: Given a number n, identify and print which in the given set of numbers are factors of n. Should…
A: The code in C++ is as follows #include <iostream> using namespace std; int main() { cout…
Q: What technique does Ubuntu use to get an IP address? Please explain why you are saying what you are.
A: Normally the NIC cards will be there for each system on which single IP addresses will be assigned.…
Q: To what extent have microcontrollers influenced the manufacturing industry, and what types of…
A: ClarificationA single-chip microcomputer created with VLSI technology is referred to as a…
Q: Is modern technology being used as effectively as it may be in the area of effective communication?
A: Introduction Communication is the most significant expect of human existence. To create, pass and…
Q: Q08.10 Write a function called r() that takes in a single variable x (a numeric value) and outputs a…
A: The given below code is in python.
Q: Multiple IP addresses cannot be assigned to a single network connection in Windows. Yes or No is the…
A: The answer is given below.
Q: An explanation of firewalls' function in the context of network security and protection is required.…
A: Firewall Function- A firewall is a type of network security device that keeps track of all incoming…
Q: Electronic mail provides two benefits over traditional mail in today's society. Your response should…
A: Given:- Electronic mail provides two benefits over traditional mail in today's society. Your…
Q: Explain Exact Algorithms on Dominating Pair Graphs?
A: Exact Algorithms on Dominating Pair Graphs:-
Q: Is the authentication procedure intended for a specific use case? To what extent do the advantages…
A: Below is a list of the advantages and disadvantages of different types of authentication. By…
Q: construct lexical analyzer program to recognize the strings of regular expression and convert it…
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: In Chapter 3 of Sharma et al. (2010), you will be introduced with a case study: "This case…
A: The question has been answered in step2
Q: Is it wise to use anything like this "Employee Management System"?
A: Please find the answer below:
Q: Find out more info about the
A: When it comes to protecting sensitive information, there are a few methods that may be utilized to…
Q: Question A washing machine works on the principle of Fuzzy System, the weight of clothes put inside…
A: Step-1: StartStep-2: Declare a variable weight and take input from userStep-3: if weight is eqaul to…
Q: What are some issues that may occur from using a non-integrated information system?
A: statement: Computer failure and loss are significant computer concerns that lead to unnecessary high…
Q: Write code to implement the expression: A = (B + C) * (D + E) on 3-, 2-, 1- and 0-address machines.…
A: INTRODUCTION: Given that When working with 3, 2, 1, and 0 address machines, the phrase A = (B + C) *…
Q: (Growth function bound and VC dimension) For any hypothesis space H. the growth function G mathcal H…
A: Growth function bound and VC dimension For any hypothesis space H:-
Q: Analyze how organizing and delivering a training session affects the application of interpersonal…
A: Introduction Interpersonal skills: The actions and strategies a person does to communicate with…
Q: Please be specific about the dangers a faulty system brings to the security of the network.
A: Risks to computer security: It may be characterised as an action that can harm computer hardware,…
Q: The internet is perhaps the best illustration of information and communication technology. Please…
A: The internet is perhaps the best illustration of information and communication technology. Please…
Q: Please provide some instances of data that does not fall within the purview of the Security Rule
A: Here Security means no restriction is applied and instances are basically examples. Instance are to…
Q: A3. Finite automata are useful components of computers and algorithms, thus it is important to be…
A: Automata hypothesis is the investigation of dynamic machines and automata, as well as the…
Q: Having a wide variety of IT systems in use may provide its own challenges. What's the best strategy…
A: Present day cloud-based ERP programming, as a coordinated across the board framework, assists you…
Q: Obtain a numerical solution of 2y + y - x = 0 using Euler's method with step size equal to (0.5) and…
A: In this question we have to solve the numerical solution where we have to use Euler's Method with…
Q: Enter letter of choice: c Queue: 0 1 2 3 Enqueue more item? Press y if yes, otherwise press any key:…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Please fix this code. 4.6.1: Overload salutation printing. Complete the second printSalutation()…
A: Coded using Java Language.
Q: When employing technology, the several processes of communication may be detailed in depth.
A: Introduction The communication process is characterized as the transmission or stream of data or a…
Q: In the case of a security breach, how does your company intend to communicate relevant information…
A: Here are a few steps to take in response to a breach: Step 1: Identify the Source AND Extent of the…
Q: What are some of a firewall's functions? Exactly how does it differ from anything else? Just what…
A: The data attempting to reach your computer or network is filtered by a firewall, which might be…
Q: Q3/Full the following blanks (15)10 = ( )Gray=( )BCD(5321)=( )EX-3 O O None of them O O (15)10 =…
A: (15)10 = ()Gray First Convert 15 into binary, which is 1111 Now convert the binary of 15 into GRAY…
Q: How can you calculate 4!, with a beginner Assembly Program x86 using a loop?
A: To find the factorial of a number we need to multiply each number from 1 up to that number. By using…
Q: Having a wide variety of IT systems in use may provide its own challenges. What's the best strategy…
A: Answer:
Q: What is the general process to implement lists and related ADTs with arrays? Please include:…
A: Abstract Data type:- The type of object o class for object whose behavior is defined by the set of…
Q: Define what a hack or virus is and how it works, and then describe the steps a firm may take to keep…
A: The following are some of the reasons why the word "hacker" is used to refer to those who are…
Q: Write a program that prompts the user to enter the side of an octagon and displays its area. The…
A: We will do this question by using user defined function. see below step for code and output.
Q: When developing and providing training, how can you tell whether the trainees are applying what…
A: INTRODUCTION In daily life, it refers to the kind of ability we use to communicate, such as language…
Q: Translate this JAVA program to C++ programming language: import java.util.Scanner; class HelloWorld…
A: As per the requirement code is converted in to c++. Algorithm: Step 1: Write the main method Step 2:…
Q: When developing and providing training, how can you tell whether the trainees are applying what…
A: INTRODUCTION: It is a capability similar to speaking or writing that we use to communicate in…
Q: Learn more about the varied uses of information systems across various types of companies via your…
A: Please find the answer below
Q: Is it possible to describe the specific difficulties, obstacles, and concerns that may arise due to…
A: Introduction: Cost reductions and excessively high costs are both caused by computer breakdown and…
Q: Define the term "authentication challenge-response system" and provide some examples of its use. As…
A: Password-based authentication is often used in databases in client-server systems. But since…
Q: Include a summary of the training and certification requirements, as well as some real-world…
A: The solution to the given question is: Certification and Training Required (Provide) : A product ,…
Q: Is it wise to use anything like this "Employee Management System"?
A: Introduction: Software called an employee management system helps your workers to work tirelessly…
Q: Companies may have trouble agreeing on what features constitute a hack or infection.
A: introduction: An expert programmer is a hacker if they is educated about computer operating systems.…
Q: Always be on the lookout for databases that can include your personal information. When will the…
A: How concerned are you about the potential invasion of your privacy while using the internet? Well,…
Q: Cybersecurity and network security cannot exist without auditing and log gathering. Explaining the…
A: A computer network's security is an important concern. It is a procedure for guaranteeing integrity…
Q: In light of the recent COVID 19 outbreak in Ghana, it is important to assess the positive and…
A: There are several benefits of information technology for the education industry.When effectively…
Use C++
Step by step
Solved in 2 steps with 3 images

- I have this code ( C#): there is an error, as in attached, What is the problem? >>>>>>>>>>>>>>>>>>>>>>>>>>>> using System;public class Rectangle{ double width, length, coorx, coory; public Rectangle() { width = 1; length = 1; coorx = 0; coory = 0; } public void move(double x, double y) { coorx += x; coory += y; } public double getArea() { return width * length; } public double getPerimeter() { return 2 * (width + length); } public override string ToString() { return "Rectangle with width: " + width.ToString() + ", length: " + length.ToString() + " with its center at : (" + coorx.ToString() + ", " + coory.ToString() + ")\n"; } public static void Main() { Rectangle[] arr = new Rectangle[2]; arr[0] = new Rectangle(); arr[1] = new Rectangle(3,4,0,0);…Write a program that uses a bar chart to display the percentagesof the overall market share represented by Apple, HTC, Samsung, andOthers, as shown in Figure . Suppose that Apple takes 20 percent and isdisplayed in red, HTC takes 26 percent and is displayed in blue, Samsung takes28 percent and is displayed in green, and the Others take 26 and are displayedin orange. Use the Rectangle class to display the bars. Interested readers mayexplore the JavaFX BarChart class for further study.Write a class, VoteAge, which does the following:a. Ask the user to enter their age (ex. XX)b. Get the age using a Scannerc. If the age is greater than or equal to 18, it prints: “You are XX years old, old enough to vote.”d. Otherwise, it prints: “You are XX years old, not old enough to vote.”Use an if-else statement
- Write a class that prompts the user for the day’s high and low temperatures. If the high is greater than or equal to 90 degrees, display the message, “Heat warning.” If the low is less than 32 degrees, display the message “Freeze warning.” If the difference between the high and low temperatures is more than 40 degrees, display the message, “Large temperature swing.”Below is the CustomerNumber Program. In the attached pictures is the assignment I am struggling with. import java.util.Scanner; /** * This program tests a customer number to determine * whether it is in the proper format. */ public class CustomerNumber { public static void main(String[] args) { String customer; // To hold a customer number // Create a Scanner object for keyboard input. Scanner keyboard = new Scanner(System.in); System.out.println("Enter a customer number in " + "the form LLLNNNN"); System.out.print("(LLL = letters and NNNN " + "= numbers): "); // Get a customer number from the user. customer = keyboard.nextLine(); // Determine whether it is valid. if (isValid(customer)) { System.out.println("That's a valid customer " + "number."); } else { System.out.println("That is not the proper " + "format."); System.out.println("Here is an example: " + "ABC1234"); } } /** * The isValid method accepts a String as its argument * and tests its contents for a valid customer number.…Write a program in which the user to type his own ID, if the ID is valid it will ask him to enter his password, if the password is correct the program will print the name of the user, otherwise the program will print Incorrect Password and if the ID does not exist , the program will print Incorrect ID.
- Implement a class that simulates a traffic light. The next method advances the color in the usual way, from green to yellow to red, then again to green. Provide two constructors, as described in the documentation of the public interface. Also supply a method that yields the number of times that this traffic light has been red. /** A simulated traffic light.*/public class TrafficLight{ private String color; private int reds; /** Constructs a green traffic light. */ public TrafficLight() { /* Your code goes here */ } /** Constructs a traffic light. @param initialColor the initial color "green", "yellow", or "red" */ public TrafficLight(String initialColor) { /* Your code goes here */ } /** Moves this traffic light to the next color. */ public void next() { /* Your code goes here */ } /** Returns the current color of this traffic light. @return the current color */ public String getColor() {…In java can you help with parts that are missing Email- date: Date- subject: String- urgent: boolean+ Email(date:Date,urgent:boolean,subject:String)+ getDate(): Date+ setDate(date: Date): void+ getSubject(): String+ setSubject(subject:String): void+ isUrgent(): boolean+ setUrgent(urgent: boolean): void+ toString(): String public class Email { private Date date; private String subject; privatebooleanurgent; public Email() { } public Email(Date date, booleanurgent, String subject) { this.date = date; this.urgent = urgent; this.subject = subject; } public Date getDate() { returndate; } publicvoid setDate(Date date) { this.date = date; } public String getSubject() { returnsubject; } publicvoid setSubject(String subject) { this.subject = subject; } publicboolean isUrgent() { returnurgent; } publicvoid setUrgent(booleanurgent) { this.urgent = urgent; } @Override public String toString() { return"Email [date=" + date + ", subject=" + subject + ", urgent=" + urgent +…Please write the Java code for a Time class: Leave comments as explaination for how the code work, and finish the code. Code: import java.util.Scanner; class Main { publicstaticvoid main(String args[]) { Scanner scan = new Scanner(System.in); String timeString; int numMeetings; System.out.print("What time is it now? "); timeString = scan.nextLine(); Time.setCurTime(timeString); System.out.print("Current time: "); Time.showCurTime(); System.out.println(); System.out.print("How many meetings do/did you have today? "); numMeetings = scan.nextInt(); scan.nextLine(); // dispose of newline character } } /* Sample Output: What time is it now? 15:45 Current time: 15:45 How many meetings do/did you have today? 5 What time is meeting #1? 16:00 What time is meeting #2? 16:50 What time is meeting #3? 9:00 What time is meeting #4? 10:00 What time is meeting #5? 15:00 Here are the times for your meetings that are later today: 16:00 16:50 Your last meeting of the day is at 16:50 What…
- I need help write this java code, described in the image below public class Person { private int ageYears; private String lastName; public void setName(String userName) { lastName = userName; } public void setAge(int numYears) { ageYears = numYears; } // Other parts omitted public void printAll() { System.out.print("Name: " + lastName); System.out.print(", Age: " + ageYears); }}// ===== end ===== // ===== Code from file Student.java =====public class Student extends Person { private int idNum; public void setID(int studentId) { idNum = studentId; } public int getID() { return idNum; }}// ===== end ===== // ===== Code from file StudentDerivationFromPerson.java =====public class StudentDerivationFromPerson { public static void main(String[] args) { Student courseStudent = new Student(); /* Your solution goes here */ }}// ===== end =====I have this problem and I keep getting a error. "ShoppingCartPrinter.java:29: error: reached end of file while parsing } ^ 1 error. " Idk what to do. This is my code. public class ItemToPurchase {public class ItemToPurchase{private String itemName;private int itemPrice;private int itemQuantity; public ItemToPurchase(){this.itemName = "none";this.itemPrice = 0;this.itemQuantity = 0;} public ItemToPurchase(String itemName, int itemPrice, int itemQuantity){this.itemName = itemName;this.itemPrice = itemPrice;this.itemQuantity = itemQuantity;} public void setName(String itemName){this.itemName = itemName;} public String getName(){return itemName;} public void setPrice(int itemPrice){this.itemPrice = itemPrice;} public int getPrice(){return itemPrice;} public void setQuantity(int itemQuantity){this.itemQuantity = itemQuantity;} public int getQuantity(){return itemQuantity;} } class ShoppingCartPrinter{public static void main(String[] args){Scanner scnr = new Scanner(System.in);String…It's a fun program to make, I am just short on time.. import java.util.Scanner; class Employee { private final String firstName; private final String lastName; private final String socialSecurityNumber; public Employee(String f, String l, String ssn){ this.firstName = f; this.lastName = l; this.socialSecurityNumber = ssn; } public String getFirstName(){ return this.firstName; } public String getLastName(){ return this.lastName; } public String getSocialSecurityNumber(){ return this.socialSecurityNumber; } public String toString(){ return String.format("%s: %s %s%n%s: %s", "employee", getFirstName(), getLastName(), "social security number", getSocialSecurityNumber()); }} Create an HourlyEmployee class that inherits from Employee (I have the code copied below). Remember, HourlyEmployees get paid an hourly wage with time-and-a-half—1.5 times the hourly…

