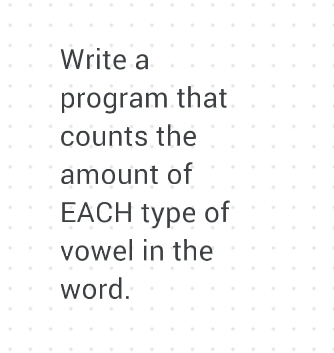
Write a program that counts the amount of EACH type of vowel in the word.
Q: Do you want to demonstrate the purpose of each phase in the traditional system development process?
A: System development cycle is an information system development approach which uses a series of steps…
Q: What would happen if the Domain Name System (DNS) didn't exist
A: Domain Name System: In DNS every device is connected to the internet which has it's own IP…
Q: What is the difference between computer organisation and computer architecture, and why is it vital…
A: According to the question the computer architecture is the hardware and on the other side the…
Q: List and explain each of a variable's four fundamental bindings
A: Answer
Q: All varieties of UTP, STP, and COAXIAL CABLES have capacitance values.
A: The capacitance values of all UTP, STP and COAXIAL CABLES are as follows: Capacitance in cables is…
Q: TCP's control plane serves what primary function?
A: TCP's control: TCP is an acronym for Transmission Control Protocol, a network communication protocol…
Q: ssible to copy and paste this code into Visual Basi
A: Is it possible to copy and paste this code into Visual Basics
Q: List at least five benefits of using Cascading Style Sheets in your document.
A: Cascading Style Sheets(CSS) is used to design the web pages along with the HTML code. We are having…
Q: What is it about a file that is so powerful, despite its simplicity and beauty?
A: If you want to save information on your computer, you'll need a file format. It explains how to…
Q: What is the status of the literature review on rumors on social media?
A: Let us see the answer:- Introduction:- Research on the factors involved in the dissemination of fake…
Q: "Divide and conquer" is one of the key ideas that should constantly be emphasized in software…
A: Split and Conquer is an algorithmic pattern.Algorithmically, the architecture is meant to take an…
Q: Mpho is convinced about the implementation of an information system. He has also realised that he…
A: According to the information given:- we have to follow the instruction to investigate the cost of…
Q: What is port forwarding and how can I comprehend it? Also, what is the best way for me to learn how…
A: PORT FORWARDING: Tunneling is another term for port forwarding in a computer network. It intercepts…
Q: Propose your own SDN analysis, exploratory or research-question oriented, with these subsections:…
A: 1. Software-described networking (SDN) technology is a public administration system that allows for…
Q: What is the complete form of the URL?
A: Given: A URL (Uniform Resource Locator) is a web address that points to a specific piece of online…
Q: Do you want to talk about Big Data and how it's being used by organisations today, and why?
A: Big data refers to large, complex, organized and unstructured data collections that are generated…
Q: Explain the formal description of a Turing Machine by explaining each component of the formal…
A: Definition. A Turing Machine (TM) is mathematical model consisting of an endless tape separated…
Q: Write a function that takes two lists of integer values and compares them to see whether they are…
A: Python code for the aforementioned need is as follows: def num(x,y):#list comparison function…
Q: Explain what pair programming and refactoring mean
A: The Answer is in step2
Q: Explain the distinctions between variables and properties in three pages of writing
A: Given: Variables Properties
Q: Describe how you utilise databases or programmes that utilise databases on a regular basis in your…
A: Databases: A database is a logically organised collection of structured data kept electronically in…
Q: Write a program that takes a singular form of a noun and produces the plural form. For most nouns,…
A: Please find the answer below :
Q: Discuss the meaning of the phrase encryption, as well as its benefits and drawbacks.
A: Encryption is a means of securing data by encoding it mathematically such that it can only be read…
Q: Explain how the star schema uses facts, dimensions, and characteristics.
A: Given: A basic data mart format that is used to create data warehouses and dimensional data sets.…
Q: What is the difference between the architecture of a computer and the structure of the computer?
A: It is the functional description of requirements and design implementation for the many components…
Q: Describe how inline style sheets supersede the style of the HTML document in which they are used.
A: Style Sheet: This Style Sheet is a collection of style rules that informs a browser how the…
Q: Demonstrate your understanding of how Cascading Style Sheets function.
A: How cascading style sheets function
Q: Create a list of and explain the five primary areas/fields involved with internet governance, as…
A: Governance Models for the Internet: Institutional economics, which outlines three major kinds of…
Q: computer science is a term that is used to describe the study of computers.
A: Let's see the solution in the next steps
Q: Explain how Cascading Style Sheets (CSS) function.
A: CSS functions and defines the style of your document—layouts, colours, and font pages are defined by…
Q: All varieties of UTP, STP, and COAXIAL CABLES have capacitance values.
A: Answer Capacitance values of all types of UTP, STP and COAXIAL CABLES The unit units on the ropes…
Q: A master file with practically indestructible data is useless.
A: Master File: The Master File is designed to provide tax authorities an overview of an MNE's…
Q: What is the simplified logical expression of ¬(¬p ∨ ¬q)?
A: To simplify logical expression.
Q: Create a java program that generates elements (randomly from 10 - 75) of a 2-dimensional array (5x5)…
A: import java.util.Random;//to generate random numbers public class Main{ //method to check given…
Q: Logic and physical data flow diagrams differ, but how can that be said to be true?
A: In this question we have discuss how the Logic and Physical Data Flow Diagram differ from each other…
Q: Is it possible to copy and paste this code into Visual Basics?
A: Yes, Similar to the worksheet function in excel, we can also copy-paste data or set of values in…
Q: #include using namespace std; int main() { int N,Prime,i=1,n; cout>"%d",&N; do { Prime=0; n=1; do {…
A: The program is written in C++. Check the program screenshot for the correct indentation. Please…
Q: Why should you study software engineering ideas if you already know how to program
A: Please find the answer in below step.
Q: A military academy accepts candidates according to the following height and weight requirements…
A: Solution: Descriptiom: We have 4 functions and a main function for validating Height and Weight,…
Q: We now know where the file space's hierarchical structure came from.
A: ANSWER:- Hierarchical Structure:- Larger firms and organizations often have a hierarchical…
Q: Write the equations in MATLAB language y=x^3-2x^2+x-4 -4≤x≤4
A: % set the x from -4 to 4 with step of 0.1 x = -4:0.1:4; % create y by writing the expression y = x…
Q: What is the notion of greedy perimeter stateless routing and how does it work?
A: GPSR - (Greedy Perimeter Stateless Routing) is a responsive and efficient routing algorithm designed…
Q: Create an Access Matrix for the following scenario based on the Protection Mechanism in an Operating…
A:
Q: Give an explanation of the distinctions between system and application software. Compare mobile…
A: Distinction between system and application software is that system software establishes a connection…
Q: Why should you study software engineering ideas if you already know how to program?
A: Software Engineering: Software engineering is a method to software development that is based on a…
Q: Create a list of and explain the five primary areas/fields involved with internet governance, as…
A: Today's businesses rely on a plethora of regulations governing the security of aggregated data,…
Q: Describe data networking in a brief introduction.
A: Data networking
Q: What is the difference between computer architecture and computer management?
A: Computer Architecture is concerned with the way hardware components are connected together to form a…
Q: An investigation has been conducted to determine the origins of the file space's hierarchical…
A: INITIATION: Starting with senior management and executives and ending with lower-level employees, a…
Q: In the context of computers, what is the difference between architecture and organisation?
A: Given: We have to discuss In the context of computers, what is the difference between architecture…
Step by step
Solved in 4 steps with 5 images

- What is encapsulation?Clarify with help of example?Write a method getTopLevelDomain that accepts URL in String format then returns the top level domain. Write in java and use test case examples as result.Implement a toString method for the following class that returns a string containing the class name and the names and values of all instance variables.
- examine how to use the major elementsthat make up regular expressions. We start with character classes, which allowus to specify a pattern based on a series of characters.Using the output from the previous activity. Discuss in at least 100 words yourfindings in the previous activity.Implement the following JavaScript function (SEE ATTACHED PHOTO FOR THE PROBLEM)

