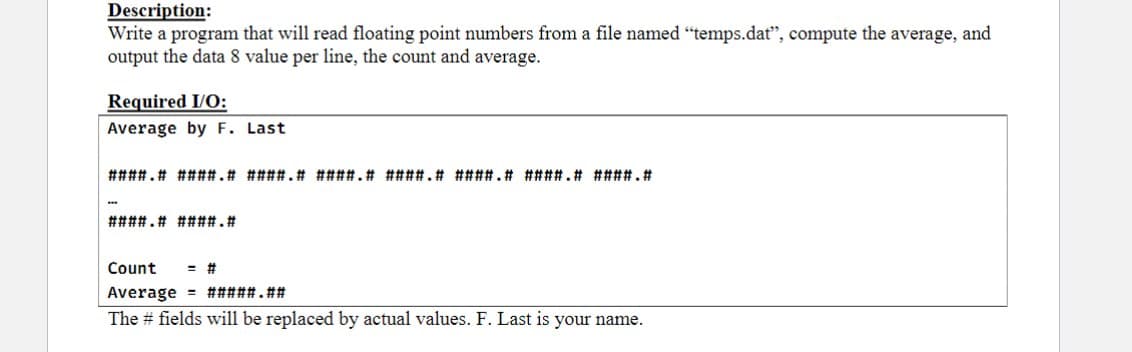
Write a program that will read floating point numbers from a file named "temps.dat", compute the average, and output the data 8 value per line, the count and average.
Q: Discuss and analyze cloud computing and data virtualization in Big Data
A: In the field of Big Data, cloud computing and data virtualization are two significant ideas. Both of…
Q: On Host C, port 80 is available, and it may be used to visit a Web server. Let's say A and B are in…
A: When a client sends a request to a server, a new socket connection is established between the client…
Q: A key team member should be named in system development. Is it feasible for the engineers and other…
A: When done correctly, team development may establish an atmosphere that encourages creativity,…
Q: What safety measures may be performed if the dangers associated with mobile phone use are reduced?
A: Introduction : Mobile phones have become an essential part of our daily lives, but their usage poses…
Q: What are common system development methods? Examine each method's pros and cons.
A: "Waterfall development," "scrum development," and "agile software development" are a few examples of…
Q: Explain firewalls for network security and privacy. Explain the term and provide examples to show…
A: The answer to the question is given below:
Q: umber of permutations and comparisons) of quicksort becomes minimal and justify your claim. Assume…
A: To construct a field of length (2^k) -1 for which the running time of quicksort becomes minimal, we…
Q: Waterfall development phases. What about Agile development?
A: The above question is solved in step 2 :-
Q: Offer cyber security mistakes and answers.
A: Sure! Here are some common cybersecurity mistakes and answers to help you stay secure: Mistake #1:…
Q: In your opinion, which two operating systems stand out above the others, and why?
A: A computer system's operating system is a piece of software that controls computer hardware and…
Q: Explain memberwise assignment briefly.
A: Introduction: The process of planning, creating, testing, and maintaining computer software's source…
Q: Print a single record using PL/SQL (show spool output please)( LEDGER_VIEW is shown in pic) SPOOL…
A: What is spooling: Spooling is just a function which stores the data in a database or later…
Q: I don't want static data members or member functions.
A: Both C and C++ make use of the term "static" in their respective programming languages. The static…
Q: Parsing a few grammars requires many techniques.
A: Please refer to the following step for the complete solution to the problem above.
Q: Create a data type Version that represents a software version number, such as 115.1.1, 115.10.1,…
A: To represent a software version number as a data type, we can create a class called Version that has…
Q: How can you spot fake news on social media?
A: Spotting fake news on social media can be challenging, but here are some tips that can help: Check…
Q: Think about the benefits and drawbacks of using wireless technology. Give the network a choice of no…
A: Introduction : Wireless technology is a term that refers to a broad range of technologies that…
Q: Top-down What projects utilize C++'s binary search trees? able parsing and recursive descent vary.
A: There are many projects that utilize C++ binary search trees. Here are a few examples: Compiler…
Q: Since the phrase "privacy" is vague, what do you mean by it? Is there really a difference? And what…
A: Solution:- The right to one's privacy is the freedom from interruption or attention, and the right…
Q: Firewalls protect computer networks and the internet. Explain the sentence using business examples…
A: Firewalls are a critical component of network security that help protect computer networks and the…
Q: A distributed denial of service attack may be initiated by a single actor, but how would this really…
A: DDoS (Distributed Denial of Service) assaults are malicious cyber-attacks used by hackers or…
Q: What is "critical thinking"? Software development follows this.
A: Critical thinking: Various definitions are available, so you can choose the one you like. But in…
Q: Compare binary and linear search benefits.
A: When conducting a linear search, each item on the list is investigated one at a time, in the order…
Q: The physical platforms can be organized in different ways. For example, we can have an Ethernet LAN…
A: Both the answers are given in the below step
Q: top five things you can do to safeguard your personal data
A: The following are five things that one can do to safeguard your personal data: Use strong and…
Q: NFC (Near Field Communication) protocol including its architecture, communication protocol, and use…
A: Introduction Near Field Communication (NFC) Protocol Near Field Communication (NFC) is a…
Q: In terms of setup, a Windows Service differs from a regular application.
A: Windows Service differs from a regular application in terms of setup in several ways: Ways…
Q: Can cloud-based security jeopardize data? Can this be prevented in the future?
A: Given Can a data breach really compromise cloud data protection? Can anything be done to make sure…
Q: Develop a user-defined MatLab function I =Comptrapez(FunName,a,b) of integrating a function by using…
A: MATLAB which refers to the one it is a proprietary multi-paradigm programming language and numeric…
Q: Your information is likely stored in databases that belong to the IRS, your state's BMV, and the…
A: The answer is given below step.
Q: Make a data type called Version that reflects the version number of a piece of software, like…
A: Algorithm: Step 1 Start. Step 2 Define a class called "Version". Step 3 In the init method, split…
Q: Network security depends on firewalls. Clarify the word and provide business examples
A: The answer to the question is given below:
Q: Please define "static semantics." Please list BNF-difficult static semantics standards. Thanks.
A: Definition of static semantics and BNF-difficult static semantics standards lists has been given…
Q: You've decided to stop using Facebook due to privacy issues with the social networking site. Please…
A: Privacy issues with social networking site: A social network is a social structure made up of a set…
Q: What does the term "firewall" mean in the context of network security, and how is it used in various…
A: A firewall is a network security device that monitors and controls incoming and outgoing network…
Q: Why should students, interns, and company owners learn operations management to succeed in their…
A: Definition: Planning, leading, and keeping tabs on production and manufacturing operations, as well…
Q: Imagine that you've been employed as a software developer to create the patient-control app for a…
A: Introduction The patient-control app being proposed should be designed to provide the hospital with…
Q: discuss non-technical cyberattacks
A: Your answer is given below.
Q: ns tha
A: Sure, here are the steps to outline the regulations that apply to functions with default parameters:
Q: Imagine being asked to facilitate a JAD session. If you ran a JAD session, write 10 rules for…
A: Moderator of the Joint Athletics Directors' Meeting Only the JAD session leader is in charge of…
Q: Customer data has been lost as a consequence of database system compromises at several significant…
A: While designing web-based data, we must differentiate between database security and system security…
Q: Why do computers require RAM and ROM?
A: Computers require both Random Access Memory (RAM) and Read-Only Memory (ROM) because they serve…
Q: What are some advantages of using a feature?
A: Using a software feature can offer several advantages, which may vary depending on the specific…
Q: Use common divisibility. Determine, with Proof, any and all pairs of integers that satisfy the…
A: To solve this equation using common divisibility, we need to find an integer solution (x, y) that…
Q: Examine the similarities and differences between a firewall and the packetized data flow.
A: A firewall and packetized data flow are both related to network security but serve different…
Q: Create a data type Version to represent the number of a software version, such as 115.1.1, 115.10.1,…
A: 1. Create a new class named Version that implements the Comparable interface. 2. Create three…
Q: How does an attack using a DDoS work? Who exactly are the The purpose of a distributed denial of…
A: How does DDoS work? Who plays? DDoS attacks' goal? Cybercriminals exploit normal network…
Q: Discuss the many software system design inputs and outputs.
A: Introduction: Within the context of an information system, the term "input" refers to the…
Q: Just how crucial is it that your computer has an operating system?
A: An operating system (OS) is the program that controls all other application programs in a computer…
Q: There are five distinct kinds of denial-of-service attacks, all of which are listed below.
A: A DoS attack is defined as an attempt to prevent access to a service by overwhelming it with…
please answer with proper explanation and step by step solution.
Solve in c++ please
Trending now
This is a popular solution!
Step by step
Solved in 5 steps with 4 images

- Write a program countfile.c that calculates and prints on screen the number of bytes or number of lines in a file. To print the number of lines in the file myfile.txt, the program is run from the command line with two arguments as follows countfile.exe -l myfile.txt or, to print the number of bytes in the file myfile.txt, it would be run as countfile.exe -b myfile.txt EXAMPLE: Suppose the file myfile.txt contains the following samantha jacob 58 91 Then running countfile.exe -l myfile.txt would print 4 on the screen. And running countfile.exe -b myfile.txt would print 15 on the screen. If as a switch anything other than -l or -b is used, the program should give an error message and exit with code 1. If the file is not found, then it should give a message saying no such file exists, and exit with code 2. If everything runs correctly the program should return 0.It contains data for one movie on each line.Each Movie contains the following data items:Title(String), Year(int-4 digits), Runtime(double). Write Java program(s) to do the following:1) Read the movies.txt Text file and write the data as a Serialized file called movies.ser to the local directory(same as movies.txt).2) Read the movies.ser serialized file and output the data on to the Console in the format shown below. The spacing for the output is: Title(20), Year (8) and Runtime (10.2)Title and Year are left-justified, Runtime is right-justified.(You can use your own text file to test your program) Sample output: Title Year Runtime aaaaaaaaaaa aaaa aa.aa...... ...... ........... ...... .....xxxxxxxx xxxx xx.xxyyyyyyy yyyy yyy.yyWrite a program which reads the content of a file given as input and counts the number of thewords in the file. It is assumed the words are separated by one or multiple of the followingcharacters: ’ ’ ’,’ ’?’ ’!’ ’.’ ’\t’ ’\r’ ’\n’. input: words.txt output: The file contains 17 words. Please write in C programming language.
- Question G .This is a java Write a program that reads a file line by line and print each line with a line number. Line number starts at 1 Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineWrite a program that reads student data from a file, compute their GPA and writes the results to a different file. 1. The user should have the option to either enter their text file that contains the student grades or use the provided text file that contains theinformation. The data in "indata.txt" should look similar to this, Lara_Croft75 70 91 69 89Chris_Redfield68 88 79 85 94Johnny_Cochran69 98 95 77 80Wanda_Maximoff84 86 98 95 92Luke_Skywalker74 96 80 98 97William_Kurt89 52 99 81 58Samuel_Jackson50 96 50 64 95END_OF_FILE This is supposed to be in python. This is what I have so far. I have no experience I apologise. I am trying to finish the GPA calculating program currently but am having trouble finishing it. grade = input("enter grades")points = 0 if grade is 90-99:total_points = 4.0if grade is 80-89:total_points = 3.0if grade is 70-79:total_points = 2.0if grade is 60-69:total_points = 1.0if grade is 50-59:total_points = 0.0gpa = total_points/len(grade)print(gpa,"is gpa")Write a program to create a file named RandomNums.txt if it does not exist. Write 100 integers created randomly into the file using textI/O. Integers are separated by spaces in the file. Read the data back from the file and display the data in increasing order. - Next, add a feature to the existing code that finds the number with the highest number of occurrences. - Write your results to a file. - Print the output to the console for verification and debugging. - Use OOP design. - Use exception handling as necessary. - Use comments accordingly. The program must be OOP in design and implement a test class. use of Collections .frequency() to pull number counts
- Create a text file of names, (3 names per line, 5 lines in total) followed by an age for each name. Go through the file and sum the ages. Create an output file with each persons name followed by age and then a line at the end of the output file that says “sum of all ages is: x”. Simple Java programming. Should include things like bufferedReader, fileReader, printWriter, fileWriter, file close, try-with-resources, Scanner, catch/try, etc. Include Java file and txt file. Thank you.3. Suppose you have a text file called notes.txt. You are provided with this notes.txt file on the blackboard. Write a C++ code to display the word that appears most in the notes.txt file and how many times the word appears. This is called word frequency. Your code should automatically find this word that appears most in the text file and also should automatically calculate how many times this word appears. Your code should be such that when I use it to count words from a file with million words, it should tell me which word appears most, this means I do not need to look at the file to know the word first. Your code should also count the number of characters in the word you found and also convert the word to all CAPS. Your code should also count the total number of words in the file. For example, suppose a text file has the following text: Apple Mango Apple Apple • Your code will be recompiled during marking to see if it gives the output you found. • You are to complete this…Write a program that findsall prime numbers up to 10,000,000,000. There are approximately455,052,511 such prime numbers. Your program should meet the followingrequirements:■■ Your program should store the prime numbers in a binary data file, namedPrimeNumbers.dat. When a new prime number is found, the number isappended to the file.■■ To find whether a new number is prime, your program should load the primenumbers from the file to an array of the long type of size 10000. If nonumber in the array is a divisor for the new number, continue to read thenext 10000 prime numbers from the data file, until a divisor is found or allnumbers in the file are read. If no divisor is found, the new number is prime.■■ Since this program takes a long time to finish, you should run it as a batchjob from a UNIX machine. If the machine is shut down and rebooted, yourprogram should resume by using the prime numbers stored in the binary datafile rather than start over from scratch.
- Please Write a program that reads data from a file containing integers that ends with -999. Output the numbers that are divisible by 7 Output the numbers that are divisible by 11 Output the numbers that are not divisible by 7 or 11. OkWrite program that reads a list of names from a data file and displays the names to the console. The program should prompt the user to enter a filename. Create such a file and check your code. Solve with python. Example of code format: #Prompt the user for file name file_name = input("Enter file name : ") #Open file with open(file_name,"r") as file: #Read file content f = file.readline() #split the contents into numbers numbers = f.split(' ') test_list = [int(i) for i in numbers] res = 1 #Find the product for i in test_list: res*=i #Print result print("Product of numbers in the list :",res)Write a program that reads a student's name followed by five test scores. The program should output the student's name, the five test scores, and the average test score. Output the average test score with two decimal places. The data to be read is stored in a file called test.txt. The output should be stored in a file called testavg.txt. test.txt: A file containing the student names and the five test scores for every student. Andrew Miller 87.50 89 65.75 37 98.50 Green Sheila 91.05 75.88 50.0 65.5 74.30 Sethi Amit 49.82 75 30 74 86.30 testavg.txt: A file containing the student name, the five test scores, and the average of the five test scores for each student.

