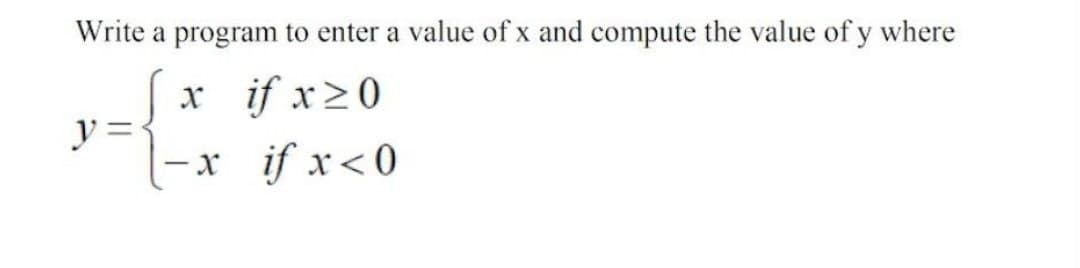
Write a program to enter a value of x and compute the value of y where x if x ≥0 -x if x < 0 y =
Q: A- What is the difference between network layer delivery and transport layer delivery?
A: 1) Network Layer is the third layer of the OSI Model. 2) It’s responsible for source-to-destination…
Q: As a systems analyst, why do you have to be bilingual? What organisations could be engaged in this…
A: Introduction: A systems analyst must act as a translator for non-technical persons, interpreting…
Q: about them, what kinds of privacy issues may they have?
A: The above question is solved in step 2 :-
Q: Certain ports must be blocked if network administrators want to monitor FTP traffic, for example.
A: Intro The File Movement Protocol (FTP) is a common communication protocol used in computer networks…
Q: Computer ethics covers a wide range of topics, including security, cybercrime, personal privacy,…
A: Organizations and individuals that use computers may express their information security and…
Q: In your perspective, will the internet have a positive or negative influence on society in the…
A: Intro According to the information given:- we have to define the is the internet going to have a…
Q: then three distinct types of computing environments are covered in detail.
A: The computer environment should be distinguished to lay out an extent of the product item's ability…
Q: My interest in learning more about multifactor authentication stems from sheer curiosity. How…
A: The above question is answered in step 2 :-
Q: We still don't fully understand how operating systems carry out process implementation.
A: To carry out process implementation the operating systems take use of the Process Model.
Q: How can we figure out which model to establish using Microsoft Access as the platform for our table…
A: Encryption: Database management systems like Microsoft Access are used. The database management…
Q: Write a nested loop to prints n X's for each value from 1 to max inclusive: Example Output (if…
A: 1) Below is C++ Program to print n X's value from 1 to MAX using nested loop In main function of…
Q: When transitioning from a serial processing system to a batch processing system, what is the most…
A: Encryption: Serial processing follows a predetermined sequence and serves one process at a time.…
Q: What are two of the projected effects of virtualization on operating systems?
A: Intro To establish an image deployment process for physical servers, administrators must consider…
Q: Give an explanation of what is meant by the term "cybersecurity," and discuss the significance of…
A: Start: Cyber security is the process of preventing harmful attacks on electronic systems, networks,…
Q: Do the rules that are now on the books do enough to protect children under the age of 16 from being…
A: Given: No, the laws that are now in place do not provide enough protection for children under the…
Q: Give folks the opportunity to discuss how they use tablet computers and cellphones in their…
A: Here are some instances of tablet and smartphone use in the workplace: Information Access Anywhere…
Q: Consider the difficulties you will have when constructing the framework, and after that, analyse the…
A: Introduction: In light of the many benefits it offers, cloud computing has quickly become a popular…
Q: To what extent can one rely on the results of sentiment analyses? In your opinion, what process is…
A: The accuracy as well as the procedure of sentiment analysis: Analysis of sentiment refers to the…
Q: Suppose you have a database of restaurants' x, y coordinates and their names. Assume that just the…
A: The B-Tree index design is preferred in the following scenario since the supplied query is not a…
Q: In educational institutions, what kinds of networks are used? What makes this type different from…
A: Introduction: In school, we use LAN, which stands for local area network, to link computers in a…
Q: Computer ethics covers a wide range of topics, including security, cybercrime, personal privacy,…
A: Organizations and individuals that use computers may express their demands for information security…
Q: Is there a certain kind of system that is more likely to profit from the use of agile development…
A: More flexible strategies: A project management technique used in software development is called an…
Q: If A and B are rectangular matrices as the following: A = (ay)pxq and B = (bij)nxm and AB = BA, then…
A:
Q: The performance of the network might be impacted by a large variety of different circumstances.
A: Explanation: How rapidly data can be sent between devices is what we mean when we speak about a…
Q: An explanation of a real-world SQL database should be provided.
A: Intro A database in SQL Server comprises a collection of tables, each of which contains a unique…
Q: To what extent can one rely on the results of sentiment analyses? In your opinion, what process is…
A: Start: The accuracy as well as the procedure of sentiment analysis. Analysis of sentiment refers to…
Q: How does the concept of ubiquitous computing really work
A: Explanation: Web of Things may be associated with the term "ubiquitous computing," which refers to…
Q: Next, with just your own words, name and explain THREE distinct types of computer environments that…
A: computing environment where different computers are used to process and exchange information to…
Q: According to the ACM code of ethics and conduct, what ethical and professional norms would be…
A: 1.) APPROVAL When 1) registering a private participant in a programme that employs biometric…
Q: Two of the anticipated operating system implications of virtualization should be recognised and…
A: Introduction: Operating system virtualization (OS virtualization): It is a server virtualization…
Q: The stop-and-wait technique is explained in detail. What are the primary drawbacks and drawbacks of…
A: The stop and wait for technique is defined as the fundamental technique which is providing reliable…
Q: a explain Encodiny and Decording with for. AS CH85.
A: though ASCII85 and Base85 are similar, Adobe also developed their own encoding. Adobe PDF files…
Q: Many TCP implementations try to avoid IP fragmentation by setting the MSS to 536. Why does this…
A: The Answer is in step2
Q: the commission of crimes online and the implications these crimes have for society 2) Identify the…
A: Overview: An criminal conduct that involves or is aimed against a computer, computer network, or…
Q: What are some of the advantages and disadvantages of using convolutional neural networks (CNN)?…
A:
Q: Could you elaborate on the four most important advantages that continuous event simulation offers?
A: Integrating in a Constant Manner: Continuous integration (CI) improves the process of developing…
Q: What are your thoughts on the question of whether or not social media platforms like Facebook ought…
A: Facebook: College administrations and law enforcement agencies utilise Facebook, a social…
Q: What exactly does it mean to approach operating system architecture layered? What are the advantages…
A: Intro A working framework can be executed with the assistance of different constructions. The design…
Q: 3. a. Write the HTML code to draw the given table with the following specification. Name Ram Reena…
A: I have provided HTML CODE along with CODE SCREENSHOT and OUTPUT…
Q: You believe that switching from a serial to a batch processing system is the most critical step that…
A: Batch processing: The practice of automating and handling several separate transactions all at once…
Q: Think about the distinction that exists between a cache that is completely associative and one that…
A: The above question is solved in step 2 :-
Q: Is there just one function that an operating system is designed to do, or are there really three?
A: An operating system is responsible for the following three primary functions: (1) oversee the…
Q: The contents of the shell script even_sum.bash is shown below. Write down the output on when you…
A: In the given code the value of the $1 will be set to 10 as while running the statement 10 is passed…
Q: esign for X ideas and applications
A: Design for X or DfX the Design for Excellence, another name for this term, refers to a set of the…
Q: Is it necessary to run a simulation on a computer in order for it to have any value? Explain.
A: Explanation: The management is able to both measure and watch the behaviour of the system via the…
Q: Exercise 7-5 Symbolize the following sentences, using the indicated symbols as abbreviations. Some…
A: “Since you have posted a question with multiple sub-parts, we will solve first three subparts for…
Q: Explain by real-life situation about each VB.net Control List Box Date Time Picker Picture Box MDI…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: Direction: Identify the three key elements of a URL.…
A: Here URL is given, we need to find out what are the important key elements of URL.
Q: Scalability in the cloud: Would you be so kind as to describe and explain it? What aspects of…
A: Starting: Please provide a brief description and explanation of cloud scalability. What factors…
Q: It is important to recognise and discuss two of the anticipated impacts of virtualization for…
A: Introduction: Operating system virtualization (OS virtualization): It is a server virtualization…
Step by step
Solved in 2 steps

- Write a program that prompts the user to enter the minutes (e.g., 1 billion), and displays the number of years and days for the minutes. For simplicity, assume a year has 365 days. Use C++ program.Write a program accepts numerical value x from 0 to 100 as input and computes and displays the corresponding letter grade given by the following tableWrite a program that prompts the user to enter five test scores and then prints the average test score. Indicate the average test score by printing it to the terminal. Average test score is X (Assume that the test scores are decimal numbers)
- Write a program that asks the user to enter a month (1 for January, 2 for February, etc.) and thenprints the number of days in the month. For February, print “28 days”.Enter a month: 530 days(B) Write a program that reads from the user the values of x and h to implement the equation below. -10x + 2h, √x -h, fx = x < 3 x ≥ 3write a program that enters an individual's year of birth and the present year and calculate and return the individual's current age
- Write a program that takes as input the speed of a car e.g 80. If the speed is less than 70, it should print “Ok”. Otherwise, for every 5 km/s above the speed limit (70), it should give the driver one demerit point and print the total number of demerit pointsWrite a program that accepts a number corresponding to a plane figure: Right Triangle Rectangle Circle The program will then ask for the following: base and height – if the previous input is 1 (right triangle) width and length – if the previous input is 2 (rectangle) radius – if the previous input is 3 (circle) (Use c++)Write a program that takes a number as input from the user. Use conditional operator to check if the number is even. Display E if the number is even and O otherwise.



