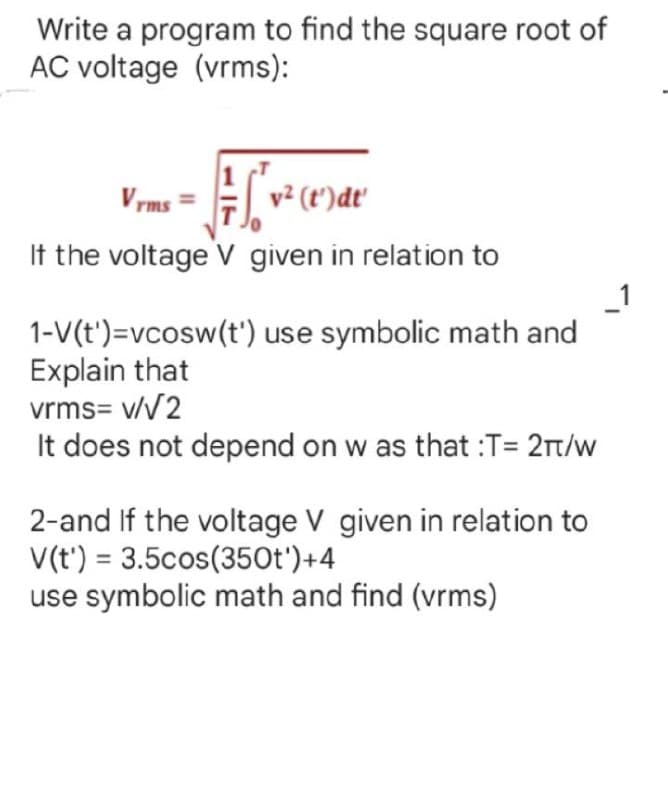
Write a program to find the square root of AC voltage (vrms): Vrms # = √ v² (t')dt' If the voltage V given in relation to 1
Q: Define a repository and explain its importance in the development of a computer system.
A: REPOSITORY A centralized location which holds all the data and information is called a repository. A…
Q: Q2: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements) And Then write…
A: Find the required code in matlab given as below and output :
Q: lementing mobile technology? How much money will I sa
A: Introduction: Below are the challenges of implementing mobile technology?
Q: In terms of network perimeter security, a VPN is an obvious option. Do they also safeguard mobile…
A: VPN is crucial for network security, and the following are a few reasons why VPN is the best…
Q: Provide some examples of the positive and negative impacts that the information and communications…
A: Introduction: Science's influence on learning is one way it has had a long-term impact on society.…
Q: In wireless networking, difficulties may arise when two or more stations are visible at the same…
A: wireless network: A wireless network is one in which data is transferred from one host to another…
Q: It is necessary to elaborate on the concept of application virtualization.
A: Answer is given below-
Q: Which aspects of the information system are considered to be its organizational, managerial, and…
A: Solution: Organizational, administrative, and technical factors all have a role. Senior managers…
Q: How much of an impact have computer technologies and the uses of those technology had on the world…
A: Let's have a look at the solution. There has been a revolution in computers and communications over…
Q: Living in France is hard work O a mess fast asleep O O O
A: The role is to complete the sentence.
Q: Draw the following diagrams to depict the scenario towards the development of the sysye iii. Entity…
A: Your Question says to draw the diagrams for the development of the system. but which system to…
Q: As a network student, how do you understand the concept of enabling users to access software or even…
A: Network: A remote access system allows companies to hire the finest talent regardless of location,…
Q: explain why the Work Breakdown Structure (WBS) is important Managing a normal software project…
A: GIVEN: explain why the Work Breakdown Structure (WBS) is important When managing a normal software…
Q: What is the significance of the fact that object function is more important than constraints in…
A: Linear Programming:The term was coined in 1950 to refer to training plans or schedules, provision of…
Q: Describe the development of wireless LAN standards in brief.
A: Introduction: The task is to outline the development of wireless LAN standards in a few words.…
Q: Prove the following by using induction: 1(1!) + 2(2!) + 3(3!) +...... + n(n!) = (n + 1)! - 1, for n…
A:
Q: Execute the scripts in Scilab and allow me to copy the runnable scripts because my keyboard has…
A: Answer: Scilab Source Code: x = int(100*rand(1,100));xclass = [0:10:100];[m n] = size(x);[m nB] =…
Q: Q1/ Answer the following question (A) What is the difference between checkbox and option button? (B)…
A: "Since you have asked multiple questions I am solving the first one for you if you want an answer to…
Q: It's possible that using structured English will be beneficial for discussing processes that don't…
A: Given: You are going to learn how to use structured English to explain processes that are not…
Q: The addition of additional programs may hinder an operating system in what ways?
A: Given: Introduce the problems that arise when an operating system includes third-party software. The…
Q: Make a case for why the WBS is necessary. Is it necessary to manage a traditional software project…
A: SOLUTION: We must explain why the Work Breakdown Structure is vital in this section. Is it necessary…
Q: Why is studying ICT important in today's society?
A: Introduction: ICT (information and communication technologies) are important in all sectors of…
Q: Methods are functions which are declared inside a class. True False
A: Function: It is a block of code which we can reuse anywhere in our program. Method: Method is very…
Q: Using a least recently used page replacement method instead of a first-in-first-out approach has…
A: Here in this question we have asked that Using a least recently used page replacement method instead…
Q: A sequential circuit counts from 0 to 255 using JK flip-flop. If the propagation delay of each flip…
A: The above question is solved in step 2 :-
Q: If we don't include, C++ will provide a default constructor. True False
A: True
Q: Q3/Answer the following questions. A) Answer with True or False (5 only) (1) 1. The Shape is a tool,…
A: "Since you have asked multiple question i am aswering first 2 for you if want answer for a specific…
Q: Methodologies and the SDLC are clearly separate. Software development life cycle (SDLC) and how it…
A: Software Development Methodology: SDL (Software Development Lifecycle) efficiently handles a…
Q: When it comes to computers, architecture and computer-based organization are two quite distinct…
A: Start: The process of putting together a computer system is known as architectural design. This…
Q: What is the impetus behind the development of an operating system's microkernel? Is this distinct…
A: What is the guiding notion in the creation of a microkernel for an operating system? What is its…
Q: Do you have any recommendations for particular approaches that might be used to capture the flow of…
A: A data flow diagram, often known as - DFD, is a diagram that represents the flow of data through a…
Q: Define a repository and explain its importance in the development of a computer system.
A: introduction of repository and its importance in the development of a computer system.
Q: What is the significance of the object function being more important than the constraints in linear…
A: Given: Give an example of why the object function is more significant than the restrictions in…
Q: (C PROGRAM ONLY) 4. Secret Division by CodeChum Admin You're just in time! I'm now on a…
A: The above question is solved in step 2 :-
Q: What are the several ways that one might come up with new ideas? Give an explanation as to why you…
A: 1) The Method of Storyboarding 2) How to Make a Mind Map (with Pictures): 1) The Method of…
Q: Q2: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements) And Then write…
A: Find the required code given as below and output :
Q: Q2: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements) And Then write…
A: Required Matlab Code for : Generate Row Vector At Range (0-5) with 11 Elements Find the Transpose…
Q: We have no idea how operating systems do their functions. What exactly does it mean to speak about…
A: operating system: An operating system (OS) connects the user of a computer to its hardware. Files,…
Q: If BL=XXH and make CMP BL,BL the sign and zero flags will be SF=1, ZF=0 depend on the value on the…
A: I will give both answes with explaination.
Q: We propose that Flynn's taxonomy be expanded by one level. What makes computers at this level…
A: Flynn's taxonomy: The taxonomy of Flynn is a classification of parallel computer architectures.…
Q: Q4: answer the following questions. (A) Define the following (answer 5 only) ( Vector, Matrix,…
A: We need to define the given terms related to Matlab.
Q: What are the benefits of using a sequential search algorithm as opposed to a binary search…
A: In reality, developing an algorithm is a systematic procedure. Instructions for working through a…
Q: Think about creating a self-driving cab using PAGE; the goal is the O a. Stop b. Get to your…
A: An autonomous vehicle - (AV), often known as a driverless car or robo-car, is a vehicle that can…
Q: What is the function of design patterns in software engineering? Describe three design patterns and…
A: Design Patterns A design pattern is an approach to solving recurring problems that we encounter as…
Q: sn ------Write a C++ program to read elements in two matrices and find the difference of two…
A: The question is to write C++ code for the given problem.
Q: The Ubuntu Server Operating System stands out from other server operating systems due to the…
A: Ubuntu Server is a server operating system: Canonical's Ubuntu Server is a server operating system…
Q: Q2: Write A Matlab Code To Generate Row Vector At Range (0-5) With (11 Elements) And Then write…
A: The Matlab code for this question by making use of standard vector operations in Matlab has been…
Q: A program used to detect overall system malfunction is (A) System diagnostics (B) Utilities (C)…
A: Answer: A program used to detect overall system malfunction is System diagnostics.
Q: Q3/Answer the following questions. A) Answer with True or False 1. The Shape is a tool, which has no…
A: True False, MsgBox and InputBox are 2 methods of input. False, it is used to store a text.
Q: (B) What are the differences between M-file script and M-file function?
A: Please find the answer below :
Step by step
Solved in 2 steps

- Write a C-program to read marks in the Programming and DataStructure Laboratory (out of 100) for N (to be read before) students.Consider the interval of marks 0-5, 6-10, 11-15, and so on. Note thatthe first interval contains 6 numbers, and other intervals are of 5numbers. Find the interval of marks having maximum number ofstudents in the class and compute the difference between its centerpoint from the mean of the distribution of marks.Provide results for the following inputs:1. N=2045, 56, 60, 15, 80, 90, 12, 85, 35, 58,63, 73, 52, 78, 47, 23, 14, 58, 18, 962. N=3054, 65, 6, 51, 8, 9, 21, 58, 53, 85,36, 37, 25, 87, 19, 93, 44, 85, 17, 69,40, 0, 3, 33, 16, 63, 95, 69, 74, 38Let Q(x) be the statement “x hasn’t developed a program in JAVA”, where the domain consist of the students in ICS. Express each quantifications in English statement. 1.) ƎxQ(x) 2.) ¬ƎxQ(x) 3.) Ǝx¬Q(x)(Program) Write a program that tests the effectiveness of the rand() library function. Start by initializing 10 counters, such as zerocount, onecount, twocount, and so forth, to 0. Then generate a large number of pseudorandom integers between 0 and 9. Each time 0 occurs, increment zerocount; when 1 occurs, increment onecount; and so on. Finally, display the number of 0s, 1s, 2s, and so on that occurred and the percentage of time they occurred.
- The language we are using here is in Racket. Please try tying each of the following (car '(11 12 13 14)) (car '(a b c d)) (cdr '(11 12 13 14)) (cdr '(a b c d)) (car (11 12 13 14)) (cdr (a b c d)) What do car and cdr do? That last line of the above should cause an error. Explain why the single quote necessary and what it does.Write a program in C to find out a fuzzy set B in Y using the extension principle for r >= 3 You may extend to: r = 3, and the function is the sum of 3 squares.For any program P that takes as input a string, can P ever solve a language other than Y(P)? If your answer is yes, give an example. If your answer is no, briefly justify your answer
- A finite sequence of symbols from a given alphabet will be called a string over the alphabet. A string that consists of a sequence a1, a2, a3, a4, … … … … , an of symbols will be denoted by the juxtaposition a1 a2 a3 a4 … … … … an. Given the strings: u = a2bab2and v = bab2, Evaluate the following operations for strings: (i) ԑu(ii) u + v(iii) u(u| v)(iv) v | (v | u)create a 2 tape Turing machine (use JFLAP) that has on tape 1 the alphabet of a,b,null, on tape 2 the alphabet is 0,1,2,3, null. Tape 1 has initial content of (a+b)*, Tape 2 has initial content of (0+1)* Begin by processing tape 1, if the substring aa is found on tape 1, search tape 2 for the first 00 substring and replace it with 22 if the substring bb is found on tape 1, search tape 2 for the first 11 substring and replace it with 33. If at anytime aa does not have a matching 00 reject if at anytime bb does not have a matching 11 reject else accept after all of tape 1 has been processed.Define a recursive function (rem r b) that, given a regular expression r and a bool b, returns a new regular expression r′ that matches exactly the set of all strings s such that string bs is matched by r. We will call r′ the remainder of r after division by b. For example, if r matches {T,FF T,TFF} and b = T, then r′ can be any regular expression that matches exactly the set {ε,FF} (because T and TFF are the only strings matched by r that begin with b = T, and their remainders are ε and FF, respectively). Here are some examples of what your function could output (but these are not the only answers!): • rem (false(false+true)∗) false = (false+true)∗ • rem (false(false+true)∗) true = ∅• rem (false∗ + true∗) true = true∗• rem ((false∗)(true∗)) true = true∗ Your implementation need not output these exact regular expressions as long as it always outputs an equivalent regular expression (i.e., one that matches the same set of strings as the given answer). These are also not the only test…
- Extend the JML definition of Peano from the lecture with a function computing the minimum of two numbers.Hint 1: This is Peano, and you cannot check something like '<' yet.Hint 2: You could define ≤ (geq) as follows: (a) geq(0,x) = true, (b) geq(s(x),0) = false, (c) geq(s(x),s(y))=geq(x,y).Hint 3: You could define min as follows: (a) min(0,x) = 0, (b) min(x,0) = 0, (c) min(s(x),s(y))=s(min(x,y)).Computer Science Suppose L ⊆{a, b}∗ is defined as follows: Λ∈L; for every x and y in L, the strings axb, bxa, and x yare in L. Show that L =AEqB , the language of all strings x in {a, b}∗ satisfying n_a (x) =n_b (x).for C++ write a progam for the greatest common divisor of integers x and y is the largest integer that evenly divides both x and y. Write a recursive function gcd that returns the greatest common divisor of x and y. The gcd of x and y is defined recursively as follows. If y is 0 the answer is x; otherwise gcd(x, y) is gcd(y, x%y).

