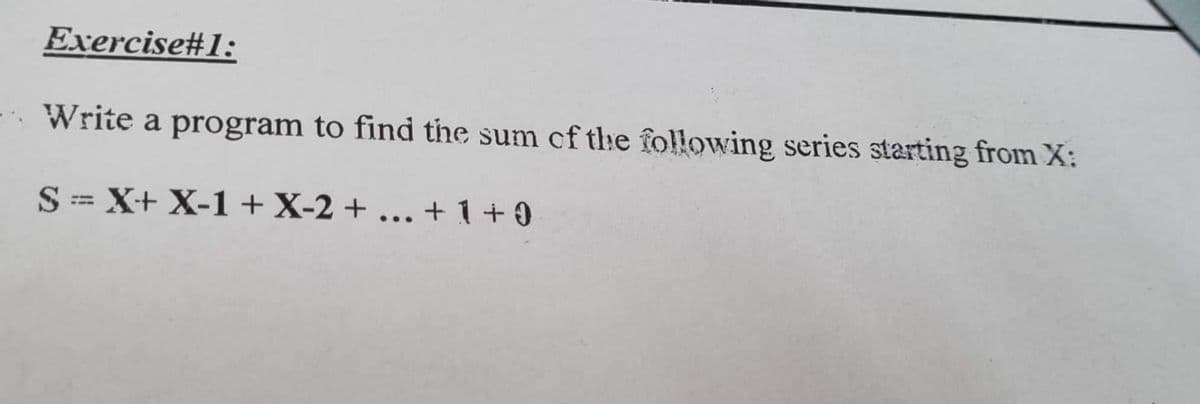
Write a program to find the sum cf the following series starting from X: S = X+ X-1 + X-2 + ... + 1 + 0
Q: When it comes to a processor's access to main memory, the loosely coupled arrangement and symmetric ...
A: Introduction: Contrast the configuration with loose coupling and the design with symmetric multiproc...
Q: Why is understanding Boolean algebra crucial for computer scientists?
A: Boolean algebra is an algebra for manipulating things with only two values, often true and false or ...
Q: Is there a restriction on the use of MST for TSP? How is the temporal complexity of MST calculated?
A: Tree with the Fewest Nodes: A subgraph with minimal weight edges links all vertices in a connected, ...
Q: What distinguishes a thin client from a fat client?
A: Introduction: A thin client is a central computer that runs applications in conjunction with a dista...
Q: What are the benefits of computing with CUDA and graphics processing units (GPUs)?
A: CUDA enjoys a few upper hands over conventional broadly useful calculation on GPUs (GPGPU) utilizing...
Q: Is it feasible to increase the efficiency of cloud computing using autonomous computing?
A: Introduction: Autonomic computing refers to a computer's ability to manage itself spontaneously via ...
Q: According to you, what is the third natural state? How do you go from a two- dimensional to three-di...
A: Introduction: Three-dimensional art items take up real space and may be seen from all directions. Th...
Q: Where is the object's supertype stored?
A: Introduction: The super type entity in the data model is defined, shown, and explained in detail.
Q: What is personalization? Examples of personalized information services that weren't available a few ...
A: Introduction: Personalization (often referred to as customization) is the process of adapting a serv...
Q: Distinguish the three layers of data modeling.
A: - They three steps of data modelling must be highlighted. - The distinctions: - Data modelling is d...
Q: What is the precise distinction between stream ciphers and block ciphers? Kindly mention three disti...
A: INTRODUCTION: CIPHERS: Ciphers, alternatively called encryption algorithms, are data encryption and ...
Q: HTML, CSS, JavaScript Integration This assignment involves integrating HTML, CSS and JavaScript. The...
A: Below is the implementation of program using js,css and html. NOTE: Whenever a button is clicked, th...
Q: Identity theft, in which people steal personal information, continues to be a serious threat for bot...
A: Introduction: Theft - obtaining personal information: The majority of thefts occur in order to get p...
Q: hat steps are involved in creating a software function? Computer science
A: What steps are involved in creating a software function?
Q: Using Java implement the following lab experiment using HashMap. Create a class Product with follow...
A: public class Product { //declaring instance variables private int pid; private String product_name;...
Q: Explain DFD & draw(L-0 and L-1) diagram for booking a ticket for flight through online service.
A: Answer In the Flight Ticket Booking System, the Data Flow Diagram (DFD) shows how the data moves and...
Q: Here are the many file access methods. I'm curious about the pros and cons of using them. What does ...
A: Introduction: The most fundamental mechanism of file access is as follows: File organisation is noth...
Q: EXERCISE No. 2 Mary Jane would like to invest her money amounting 100,000 at the bank. Before invest...
A: The investment amount is considered as P and interest for each type of account is calculated using t...
Q: What was the primary goal of early operating systems in comparison to the goals of modern ones?
A: Objectives of operating systems The operating system acts as an interface between user and hardware...
Q: Consider two-dimensional vector data where the data items do not overlap. Is it possible to convert ...
A: Introduction: Raster data is represented by a regular grid of points. The x and y coordinates for ea...
Q: What is the relationship between PCA and SVD
A: Principal Component Analysis, or PCA, is a dimensionality-reduction method that is often used to red...
Q: What was John von Neumann's residential address?
A: Introduction: A single, shared memory for programmed and data, a single bus for memory access, an ar...
Q: Write a program using recursive function that calculates the sum of the first no elements from harmo...
A: As no programming language is mentioned, it is solved using basic C++
Q: What are Data Analytics? what are the purpose and reason why do we have now data analytics.
A: Data is very useful in businesses to better understand their customers, improve their advertising ca...
Q: What year did the first computer mouse appear?
A: According to the question the mouse trackball and the related pointing device changed into invented ...
Q: In a single statement or a few lines, define and contrast random forest with decision trees. How can...
A: Introduction: A random forest is a collection of decision trees, whereas a decision tree is a collec...
Q: Which component of the computer is capable of preserving data indefinitely even when the machine is ...
A: Persistent storage is long term storage for bytes as files and folders.
Q: How is cloud storage used for data backup?
A: Introduction: Cloud backup is a service that backs up and stores data and apps on a business's serve...
Q: Creating a portfolio highlighting your academic accomplishments may be beneficial throughout the job...
A: Introduction: A career portfolio goes beyond a resume and cover letter to demonstrate your job exper...
Q: What is an NDA and how does it work?
A: What is an NDA? Company should keep working projects, creative ideas, and amazing new products secre...
Q: Provide a short overview of source data automation (SDA), emphasizing at least two (2) of the techno...
A: Let's see the solution what source data automation is
Q: What happens when an array is sorted using a selection sort
A: Introduction: The smallest element in an unsorted array is brought to the front of the selection sor...
Q: Identify and describe the reference model for the Internet of Things (IoT). Fill up the gaps using t...
A: Introduction: The task is to describe the IoT reference model. The Internet of Things (IoT) referenc...
Q: If you wish to rapidly access data in a centralized database, what design considerations are made di...
A: INTRODUCTION: What design decisions are made differently in a centralized database versus a distrib...
Q: Is Morse Code still significant in this modern era? Why or why not?
A: Morse code is still used significantly in this modern era. It has some of the very important impleme...
Q: A local area network has a number of disadvantages, which we will discuss below.
A: LAN or Local Area Network is a wired network spread over a single site like an office, building or m...
Q: Courses(C, T, H, R, S, G) Relation and F={C→T ,HR→C, HT→R, HS→R,CS→G} is given. What is the Norma...
A:
Q: PCA tried to find new basis vectors (axes) that maximize the variance of the instances. Is True or ...
A: Let's see the solution
Q: What does it imply when someone speaks about a 4G or 5G phone network?
A: Find the answer given as below :
Q: Why is it advantageous to utilize NLP (Natural Language Processing) for financial news analysis?
A: Introduction: The field of study that focuses on the interactions between human language and comput...
Q: Provide an overview of online marketing tactics and partnerships, including business-to-business (B2...
A: Marketing tactics Marketing tactics are the strategic actions that direct the promotion of a product...
Q: Was it conceivable for a business to build its own private cloud from scratch? What are the normal s...
A: Introduction: For a number of reasons, many individuals desire to remove their data from the cloud. ...
Q: Submit your ideas on the topic of Using Information and Communications Technology (ICT) in Education...
A: Some ideas of ict in education
Q: How is artificial intelligence going to accomplish its ultimate objective? Please give an overview f...
A: Introduction: The ultimate objective of artificial intelligence is to create computers that can dupl...
Q: Define the words "spatial locality" and "temporal locality," and explain how caches are utilized to ...
A: The software often reuses data and instructions that it has previously utilised. A decent degree of ...
Q: How to add to an existing text file called movies.txt with a movie name and price? Movies.txt The ...
A: Since the question doesn't include which programming language is used to code the solution so I am u...
Q: Compare the header and body of the getBalance method with the header and body of the getPrice method...
A: INTRODUCTION: HEADER: A header is text that is positioned at the top of a page, whereas a footer is ...
Q: Explain how the waterfall system development paradigm controls the modifications that can happen dur...
A: Actually, SDLC stands for Software Development Life Cycle.
Q: Examine the many ways in which different companies use information systems.
A: Introduction: The Executive Support System (ESS), Management Information System (MIS), Decision Supp...
Q: Describe the three fundamental distinctions between industrial and consumer IoT.
A: Given: Describe the three fundamental distinctions between industrial and consumer IoT.
Step by step
Solved in 3 steps with 1 images

- Answer the given question with a proper explanation and step-by-step solution. Write an MIPS program that computes terms of the Fibonacci series, defined as: 1, 1, 2, 3, 5, 8, 13, 21, 34, 55 ... (This is sometimes started with a 0th term: 0, 1, 1, 2, etc.)The first two terms in the series are fixed, and each subsequent term in the series is the sum of the preceding two terms. So, for example, the term 13 is the sum of the terms 5 and 8.Write the program as a counting loop that terminates when the 100th term of the series has been computed. Use a register for the current term and a register for the previous term. Each execution of the loop computes a new current term and then copies the old current term to the previous term register. Count the number of passes to stop after the 100th term. Do not worry about overflow: this will FAR exceed the capacity of a register to hold the value. Stop the program with a syscall with 10 in $v0.(B) Write a program that reads from the user the values of x and h to implement the equation below. -10x + 2h, √x -h, fx = x < 3 x ≥ 3Use C++ to program a system that lets people guess a random number between 506 and 783 twice. The guesser must know if the number is correct. If not, then they must know how much higher or lower their guess is from the randomly selected number.
- Write a program that would compute the sum, difference, product, quotient, and will printthe squared and cube of the first number and second number.Write the robot program using the VAL+ for the following automation case. First draw the problem; then handwrite the VAL+ code. The robot picks up FIVE blocks of size 100x100x100 mm that are stacked at a fixed position and place them at the corners and center of a square table of size 500 x 500 mm. Select the original position on the table on your own.Answer the given question with a proper explanation and step-by-step solution. Qns: Write a Little Man program that adds a column of input values and produces the sum as output. The first input value will contain the number of values that follow as input to be added.
- Evaluate the given Computer Expressions below: Suppose the value of A = 10; B = 15; C = 20.50; D = 15 a. (A + B * C) / 2 + (A + D + B) b. C + (A * B + C) + A – 10 c. [(10 + 5 + A * B) + (B + D – 10 8 2)] + A * B – 10 d. D * 2 + 3 + B * (A + B * C - 40) * A e. [(A + B * 2 + C) * 2 + (B – 10 + C)] + [(40 + A + B) - (10 + 8 + C - D)]write a multithreaded program which sums, two integers variables.Write a program that inputs a sequence of non negative numbers terminated by a negative value and show the sum, average, maximum and minimum of the non negative numbers
- Write a program to solve the following simultaneous equations 5Y+7Z=2X+17 3X-6Y=40-2Z 9X-3Y+8Z-55=0Use C++ language to create a program that will get the length, width and height of a gift box. Afterwards, compute and display its volume.write a program thar reads three numbers and prints the largest one step by step



