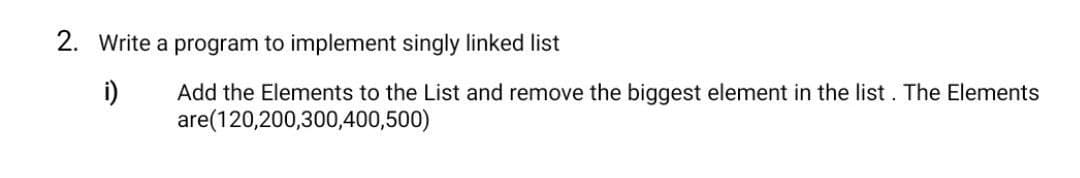
Write a program to implement singly linked list i) Add the Elements to the List and remove the biggest element in the list. The Elements are(120,200,300,400,500)
Q: What are the legal ramifications of the data concerns that are being discussed?
A: Information Property: Because access to and exploitation of Big Data is becoming essential to future…
Q: Explain the differences between interlacing and progressive scan in the context of video signal…
A: Explanation: In the transmission of visual signals, distinguish between interlacing and progressive…
Q: Describe each assessment method in the realm of human-computer interaction in a few words. Testing…
A: Human-Computer Interaction (HCI): Human-computer interaction (HCI) research, a multidisciplinary…
Q: are needed to implement equation F- XYZ+ XYZ + X ent circuit using.
A: F XYZ+XZ XZ(Y+1) XZ
Q: 2. Given F(a,b,c) = a'b' + bc + a'bc'. %3D a. Obtain the truth table of F. b. Express F in sum of…
A:
Q: If 2 LAN devices have the same MAC address, what happens? How would it work? If both PCs connected…
A: If two devices are having same MAC address, then neither of the computer can communicate properly.…
Q: When it comes to session, what are the drawbacks?
A: In session stickiness, also known as session persistence, a load balancer builds an affinity between…
Q: External devices may be connected to the CPU through the expansion bus using interface cards. why?
A: Given that: the extension bus allows for the attachment of additional devices to the CPU through…
Q: Describe how virtual machines lack support for instructions set architectures.
A: Introduction: Virtual machines Computers within computers which are virtualized A virtual machine,…
Q: What's the difference between a cryptographic secret key and a public key?
A: Symmetric, or secret-key, encryption relies on a piece of information or parameter to encrypt and…
Q: What's the difference between what a user wants and what a system wants?
A: The user's world is the basis of the issue while discussing user needs. They explain what the…
Q: Is it possible to classify the four most fundamental features of software development? Please give…
A: Fundamental Features of Software Development: "Software development" is a collection of activities…
Q: Mux, is a device that can be use to O select one from many O many from one O parallel input to…
A: INTRODUCTION: Here we need to tell MUX is a device that can be use to.
Q: the Octal system can be represented in . bits in binary 3 O 5 O 7 O 8
A: Introduction: the Octal system can be represented in ...... bits in binary3 578
Q: Separate user-visible registers from control and status registers, and provide at least one example…
A: An operational framework is a software that facilitates communication between the user and the…
Q: A secret key differs from a public key in cryptography because it is kept hidden.
A: Cryptography: There is a difference between a cryptographic secret key and a cryptographic public…
Q: Create a program that will sort the following words: Example: Will, Mike, Dustin, Lucas, Max, Eleven…
A: The following are steps need to be taken for the given program: Declare the given words as an array…
Q: struct a MATLAB function to appl- value.
A: x = -3:0.1:3; y = x.^4 plot(x,y)
Q: What exactly is the distinction between connotative and denotative meanings?
A: Introduction: Simply expressed, the Extensible Markup Language (XML) sets rules for constructing…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: This question pertains to accessing and utilizing cloud-based services and applications.
Q: Analyze the risks and advantages of cloud security. There are various issues and hazards involved…
A: With the introduction of cloud computing, a new paradigm for offering IT services has arisen, one…
Q: To get your computer to begin searching for operating system boot files on the CD-ROM before looking…
A: CD-ROM stands for compact disc read-only memory, a kind of computer memory that resembles a compact…
Q: how services and apps that are hosted in the cloud may be accessed and utilized.
A: Given: Users can use a browser or an app to access cloud services. They connect to the cloud over…
Q: Describe the factors to consider while selecting the appropriate scanning device for a certain task.…
A: Intro Centralized/De-Centralized ScanningWhether scanning is a centralized or decentralized will,…
Q: Is there a method to classify the four most fundamental characteristics of software development?…
A: Meaning: "Software a development refers to a collection of computer science activities devoted to…
Q: It is easy to convert the hexadecimal to . bits equivalent binary representation O 3 O 2
A: To find solution for "it is easy to convert the hexadecimal to ______ bits equivalent binary…
Q: Thermo Couple is an Analogue .( ). input device True O Plc False O
A: Dear learner , hope you are doing well , i will try my best to answer this question. Thank You !!
Q: Adhoc Network's nodes must be able to tell when the network's structure has changed.
A: When devices connect and interact directly with one another, a spontaneous network, typically one…
Q: Write C++ program to create a base class named Person that includes variables: name and age and then…
A: Your C++ program is given below as you required with an output.
Q: A. What are the basic types of timers in PLC?
A: What are the basic types of timers in PLC?
Q: Find three server options that a local bank may employ.
A: Introduction: It is a bank that operates for business reasons inside a community. It takes deposits,…
Q: What does it mean when you say "new data source"?
A: Introduction: Data collection is the process of acquiring, gathering, extracting, and storing large…
Q: Make a distinction between multiprogramming systems and timesharing environments.
A: It is necessary to distinguish between Multiprogramming and Timesharing Systems. The following is…
Q: What signs could point to a hacked laptop's operating system?
A: What signs could point to a hacked laptop's operating system?
Q: Perform a cost-benefit analysis of deploying NAS (network attached storage) and SAN (network…
A: A NAS is a single storage device that delivers data via Ethernet and is affordable and…
Q: Converting from.. to ., include divide by two, to keep track of the remainder O Binary to Decimal…
A: The conversion of the decimal to binary includes the division by two with keeping track of the…
Q: To shut down the computer, manage processes, and connect to a Remote Desktop session, what…
A: Select Run from the remote computer's Start menu, then type the following command to shut down the…
Q: Describe each assessment method in the realm of human-computer interaction in a few words. Testing…
A: Introduction: Human-computer interaction (HCI) research focuses on human-computer interaction. HCI…
Q: Why may two separate databases be maintained in the same DBMS?
A: As per the question statement, We need to list the scenarios/reason why you should maintain two…
Q: arnough Map ncludes at leas 2 variables
A: Karnough Map can be consideres to includes at least: 2 variables
Q: What are the responsibilities of those who manage data?
A: The complete solution is given below:-
Q: What would you do if you discovered someone was taking your data, based on your expertise…
A: Immediately take action if you have been a victim of identity theft or if you suspect that you have…
Q: How do the nodes of the Adhoc Network know when the topology of the network changes?
A: In wireless Ad hoc network topology, wireless capable devices communicate directly each other…
Q: What are the seven most critical fields to fill out when generating an MS-DOS directory entry?
A: MS-DOS Directory: The Organization of the DOS Directory StructureA directory entry in the Microsoft…
Q: Draw an ERD for below scenario by pen and upload the picture in the upload section below(4 marks):…
A:
Q: What do you mean when you say "network security
A: What do you mean when you say "network security"? Answer: Network security is a set of technologies…
Q: Consider wireless networks in developing countries. Why are firms dumping LANs and cables for…
A: When it comes to linking many computers together, a wireless network, also known as a Wireless Local…
Q: It is the basic building block in VB. Select one: a. none of the choices b. label c. textbox d.…
A: The Form is the primary building block of a Visual Basic 6 application Label is needed to change the…
Q: Oracle Database with code and output on update,delete and insert code of trigger i need it on…
A: Here , CUSTOMERS table we had created : Select * from customers;…
Q: Which of the following is applicable to Dijkstra's algorithm, but not to Prim's algorithm? O a. All…
A: The answer is given in the below step
Step by step
Solved in 2 steps with 1 images

- Which of the following statement is not true about the doubly linked list? A. We can traverse in both the directions. B. It requires extra space C. Implementation of doubly linked list is easier than the singly linked list D. It stores the addresses of the next and the previous nodepython programming Write a function that will insert a new value into the middle of a Linked List. INPUT: The head of the Linked List, the value to insert OUTPUT: Nothing is output RETURNED: Nothing is returned6. Take a input from a user and create a doubly linked list and then find the largest element in a doubly linked list. Use 1 to take more inputs from user else enter another number. Use C language and attach output.
- JAVA CODE PLEASE Linked List Practice ll by CodeChum Admin Write a function printNodes that takes in the head of a linked list and prints all the values of that linked list using a while loop. Print the values separated by a [space]->[space] In the main function, write a program that asks the user to input five integers and assign these values to the nodes. Arrange the nodes in ascending order first before printing them using the printNodes function. Input 1. One line containing an integer 2. One line containing an integer 3. One line containing an integer 4. One line containing an integer 5. One line containing an integer Output Enter·number·1:·1 Enter·number·2:·2 Enter·number·3:·3 Enter·number·4:·4 Enter·number·5:·5 1·->·2·->·3·->·4·->·5read positive numbers from user and create a double linked list. the list should stop expanding the moment the users enters 15 numbers and display it in sorted order. write the program in c or c++.Question : Write a program to remove duplicates from a doubly linked list. e.g (1,2,3,4,5,2) (you will remove the 2nd duplicate) and then swap two data items in a doubly linked list. swap address of node 2 with node 4.
- 1. Write a simple procedure to count the number of elements in a linked list. Please use CConsidering all the elements and its indexes at the right side:Write a sequence of List operations that would result to a LIST that contains ONLY the elements with its respective indexes: {index[00]=104, index[01]=165, index[02]=115, index[03]=384, index[04]=248, index[05]=117}.JAVA CODE PLEASE Linked List Practice l by CodeChum Admin Write a function printNodes that takes in the head of a linked list and prints all the values of that linked list using a while loop. Print the values separated by a [space]->[space] In the main function, write a program that asks the user to input five integers and assign these values to the nodes then print the five nodes using the printNodes function. An initial code is provided for you. Just fill in the blanks. Input 1. One line containing an integer 2. One line containing an integer 3. One line containing an integer 4. One line containing an integer 5. One line containing an integer Output Enter·number·1:·1 Enter·number·2:·2 Enter·number·3:·3 Enter·number·4:·4 Enter·number·5:·5 1·->·2·->·3·->·4·->·5
- _!?8. Problem Title: "Add Two Numb You are given two non-empty linked lists representing two non-negative integers. The digits are stored in reverse order, and each of their nodes contains a single digit. Add the two numbers and return the sum as a linked list. You may assume the two numbers do not contain any leading zero, except the number 0 itself..Write c# code for a circularly linked list is shown in figure.Write the following function that sorts and merges two lists into a new sorted list. The new list contains only even numbers. def myMergeEvenList(list1, list2): Enter list1: 10,5,6,7 Enter list2: 12,8,5,0,1 The merged list is: 0,6,8,10,12

