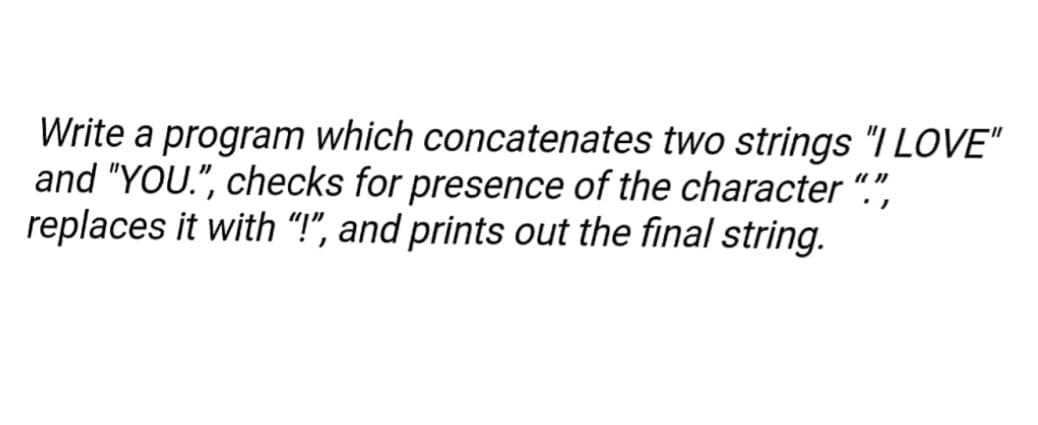
Write a program which concatenates two strings "I LOVE" and "YOU.", checks for presence of the character "." replaces it with "!", and prints out the final string.
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Introduction: The methods in which firewalls may assist in the security of your firm, the advantages…
Q: Contrast command interfaces with menu interfaces in terms of their respective strengths and…
A: Solution: Command Line Interface (CLI) is the abbreviation for Command Line Interface. CLI allows…
Q: Explain how peer-to-peer middleware works. What are their requirements, both functional and…
A: Introduction: To handle the automated placement and addressing of distributed objects, which are…
Q: Concerns have been raised over users' ability to maintain their privacy while utilising social…
A: Since the advent of the first social networking sites in the early 2000's, social networking sites…
Q: The installation of firewalls is an essential component of both the security and privacy of a…
A: Introduction: A firewall filters incoming and outgoing network traffic based on a company's security…
Q: A consumer reporting agency known as Equifax and the Internal Revenue Service (IRS) are likely to…
A: Data collection in each database: The Internal Money Service (IRS) is a federal government…
Q: 9.) A 8255 PPIO circuit is connected to system bus of the 8085 microprocessor. The base address of…
A: Answer:- In this 8085 program initially 8255 is being setup in I/O mode. Then FF hex (i.e. 1111 1111…
Q: 14. How many different ways can a structure var be declared:
A:
Q: You will be responsible for informing your clients of the potential risks involved in the use of…
A: Introduction: You must educate your consumers about the risks of using their credit card information…
Q: The field of computer science. In order to increase the security of your Windows system, you need do…
A: Introduction: Windows is a collection of proprietary graphical operating system families created and…
Q: Be sure that you are well-versed on the major tools and procedures that will be used during the…
A: Introduction: The system development life cycle includes conception, analysis, design,…
Q: There are five main changes between Windows 7 and Windows 10
A: Windows 7 is a significant arrival of the Windows NT working framework created by Microsoft. It was…
Q: 7. Create a 3x3 matrix with values ranging from 10 to 18 8. Create a 4x4 identity matrix 9. Use…
A: Python is a programming language. Python is a high-level general-purpose programming language. It is…
Q: The Linux kernel has included three new functions. The release's safety may be affected in any way…
A: Introduction: The Linux kernel is the operating system's heart. It is a monolithic, modular,…
Q: It is essential, before moving on, to define the role of the firewall in terms of the safety and…
A: Introduction To effectively defend and secure a network, it is imperative to comprehend these…
Q: What are some of the job responsibilities that need Network+ or CCNA certification
A: Jobs that will gain the most from Network+ are: IT jobs 1. Set up computers, printers, scanners,…
Q: Problem Write a program that captures input from the user. Then, swap the letters two at a time in…
A: As per the requirement program is developed. Algorithm: Step 1: Read the input from the user Step 2:…
Q: 6 Consider converting the following NFA to an equivalent DFA. 0 90 91 1 a The number of states in…
A:
Q: Why does DevOps recommend “shift-left” testing principles?
A: The practise of shifting to the "left" side of the DevOps lifecycle involves moving testing,…
Q: It is essential, before moving on, to define the role of the firewall in terms of the safety and…
A: It is essential to have an understanding of these functions of firewalls in order to properly defend…
Q: Web page content can include O text O images audio & video all of the above
A: The answer is given below.
Q: Create a topic proposal for an web-based attendance tracker. Questions: 1. Reasons for the…
A: Note : As per guidelines of the company, we are authorized to answer 1st 3 subparts. Thus answering…
Q: At each step of development, the inputs and outputs of a software system must be thoroughly…
A: Introduction: Input is raw data processed to generate output. Input design must consider PC, MICR,…
Q: According to results above, construct a truth table to implement the logic function on the best time…
A:
Q: Any recommendations for Linux package management systems you've used in the past or are…
A: Linux Package Manager-APT: The Advanced Package Utility (APT) is an open-source tool with a user…
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Encryption: The pros and downsides of using hardware and software firewalls, software tools, and the…
Q: It is essential to provide a case study that indicates how the students were successful in achieving…
A: Abstract: To offer the reader with a complete yet condensed overview of the research and conclusions…
Q: Imagine you're installing a new wireless router at a small business. When providing secure wireless…
A: Given: Which form of wireless authentication offers the most protection against unauthorised access?…
Q: Below are five samples given in the dataset. Note: Visual distance between the points in the image…
A: Answers 1: Option C is CORRECT. Explanation: *) We will choose (n-1) observations for training…
Q: 13. Write code that reproduces the output shown below. In [23]: # Code Here In [17]: # DON'T WRITE…
A: Answer:
Q: Take into account the benefits and drawbacks of using wireless technology. At the very least,…
A: Explanation: This high-speed solution is used to transfer information quickly or develop secure…
Q: In the following program, shown below, the print result is #include void main() {int a=1,b; b=++a;…
A: //lets analyse the given code: #include <iostream.h> void main(){ int a=1,b;//integer…
Q: Please go into as much detail as you think is required on the differences between the three most…
A: Introduction The distinctions between the three main desktop operating systems may be described in…
Q: #include void main() { int i,x; cout> x;
A: Given :
Q: Different components on the motherboard of a PC unit are linked together by sets of parallel…
A: These lines are called Buses. Correct option is B Different components on the motherboard of a PC…
Q: What exactly is meant by the term "critical thinking," and how is it carried out? This guideline is…
A: Given: What exactly does it mean to have "critical thinking"? In the field of software engineering,…
Q: The phrases "complete" and "constant" are sometimes used interchangeably, but what do these words…
A: Given: The requirement analysis step of the software development process is very important since the…
Q: In your perspective, which stage in the process of developing software is the most important, and…
A: Gathering Requirements: This is the most crucial step in the SDLC; nevertheless, most people…
Q: When dealing with data that is dynamic, it is important to describe how the heap works. Why would a…
A: Given: Dynamic allocation creates a "new" data area in C++. Dynamic allocation may be used to build…
Q: Describe the prerequisites for an educational website's functionality.
A: Educational websites are the ones that have different activities and tools for online learning of…
Q: In the process of developing and testing software, what sorts of tools and technologies are…
A: Launch: Software testing is an organisational process for building software that assures…
Q: 25. What's the result of this line of code? string x = "123" + 45 O168 O "168" O "12345" compiler…
A: Given, string x = "123" + 45 we need to provide output for this.
Q: following program, below, the print resu
A: Solution - In the given question, we have to find the output of the given program.
Q: If at all possible, there should be a more in-depth description of the metrics involved in the…
A: The following is the response: In software development, software engineering is one of the most…
Q: Penetration testers have a multitude of reasons for using the technique of aircracking.
A: Introduction: A penetration tester is a security expert who employs various methods to gain access…
Q: Explain the potential risks associated with using a credit card to transmit money over the internet.
A: Introduction: The number is encrypted and masked behind a mathematical code when you add a credit…
Q: Do you think Facebook and other social media platforms should provide law enforcement access to your…
A: Given: Facebook. Facebook, a social media platform, is being utilised by college administrations and…
Q: Describe in as few words as possible what a proxy firewall is. What is a generic proxy (like SOCKS),…
A: According to the question, a sock proxy is an alternative to a VPN and routes packets between the…
Q: Is there anything you can do to enhance your system's design using heuristics?
A: Introduction: Experts utilise heuristic assessment to examine user interface usability in…
Q: Give examples of how Internet and telecommunications technologies (e.g., Interactive Voice Response…
A: Telecommunication is a technology that includes cabling, wireless, switching, media, internet and…
Step by step
Solved in 4 steps with 2 images

- Write a program that takes a string and swap the first character and the last character of that string.Write a program that reads a text (string) and prints the letter that starts the most number ofwords in that stringWrite a program that takes input values as integer, checks the number is not less than 10 (otherwise take input again), and prints the previous 10 numbers i.e. 10, 9, 8, … Concatenate the integer and string values and print as a string
- Write a program that takes a string and creates a new string made of first two characters and last two characters from the given stringwrite a program that allows the input of a string from the user and prints the longest word in that string and its length. If there are multiple words with the same maximum length you must print the first one only.Write a program that reads a character and a string (an entire line, which may include spaces or tabs), and outputs the number of times the character appears in the string. Hint: use getline(cin, mystring) to read the entire line including spaces. Use mystring.length() to know how many characters. But to avoid a glitch when getline gets an empty string following a cin, do the following sequence: cin >> mychar; /* get character. cin leaves the newline in the input buffer*/ cin.ignore(80,'\n'); /* remove newline from the buffer, which getline would see as empty line*/ cout << "Enter a string: "; //prompt for string getline(cin, mystring); Example program run (the user types only the word "Monday" and the letter "a"): Enter character to count: a Enter a string: Monday count = 1 Example program run: Enter character to count: a Enter a string: Today is Monday count = 2 Example program run: Enter character to count: b Enter a string: Today is Monday count = 0 #include…
- Write a program that reads in a string containing three words separated by commasand then outputs that string with each word in a different line.Write a program that accepts as input a sentence in which all of the words are run together but the first character of each word is uppercase. Convert the sentence to a string in which the words are separated by spaces and only the first word starts with an uppercase letter. For example the string “StopAndSmellTheRoses.” would be converted to “Stop and smell the roses.”Write a program that asks the user to enter a word that contains the letter a. The programshould then print the following two lines: On the first line should be the part of the string upto and including the first a, and on the second line should be the rest of the string. Sampleoutput is shown below:Enter a word: buffalobuffalo
- Write a program which reads string and rewrite it in alphabetical order. For example, the word STRING should be written as GINRST.Write a program that gets a string containing a person’s first, middle, and last names, and then display their first, middle, and last initials. For example, if the user enters John William Smith the program should display J. W. S.Write a program that reads a string from the user containing a date in the form mm/dd/yyyy. It should print the date in the form March 12, 2014.

