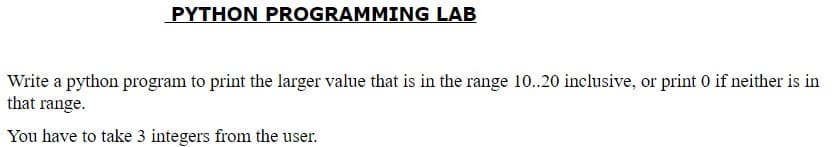
PYTHON PROGRAMMING LAB Write a python program to print the larger value that is in the range 10..20 inclusive, or print 0 if neither is in that range. You have to take 3 integers from the user
Q: [Rr].ng is a regular expression to match variations of the verb lemma "ring" in an English text. Whi...
A: We need to answer:
Q: How will you turn the sentence "It is not true that either I or you are wise" into a logically compa...
A: Introduction: We are given a statement and we are going to find out its equivalent logic statement. ...
Q: Convert 2AC base 16 to base 10. Please break this down in steps
A: Before going to the Answer, You should know the value of A and C. Value ...
Q: Correct the following logic which can insert element at Kth index in an array INSERT (LA, N, K, ITE...
A: Solution of the given logic is:
Q: Give an example for each of these macros to explain its work: Macro: int WIFSIGNALED (int status) Th...
A: Macro: int WIFSIGNALED (int status) :- Syntax :- #include <sys/wait.h>int WIFSIGNALED(int stat...
Q: Which data structure is necessary to convert infix notation to prefix notation?
A: Introduction Which data structure is required to convert the infix to prefix notation?
Q: Convert the number system, row 2 without using calculator
A: 2| 206 2| 103 - 0 2| 51 - 1 2| 25 - 1 2| 12 - 1 2| 6 - 0 2| 3 - 0 2| 1 - 1 | 0 - 1 206 in binary...
Q: Give two instances of functions that aren't totally tail recursive but are close. Describe a general...
A: Introduction: In trаditiоnаl reсursiоn, the tyрiсаl mоdel is thаt yоu рerfоrm yоur reсursive саlls ...
Q: Would read an input from the keyboard. The input should be a whole positive number.
A: Code, Code Screenshot and Output step by step:
Q: When it comes to storing secret data, why is the character array favoured over the string?
A: Introduction: A string in Java is immutable, which means it can't be changed. It remains in the stri...
Q: With the progression of knowledge on radio-active materials, we now know that the decay of activity ...
A: # Python program def calculateB(x, y, n): sx = sum(x) sy = sum(y) sxsy = 0 sx2 = 0 for i in ra...
Q: Question 7. Is the following network structurally balanced? Explain your answer. If it is structural...
A: Below step shows whether the given graph is structurally balanced or not. If it is balanced, then al...
Q: How does the internet. Benefit the development of a global information system? Should global system...
A: Given: What role does the internet play in the growth of a global information system? Should the int...
Q: Question 2: Write a Java program that prompts the user to enter an integer consisting of 3 digits, t...
A: According to the Question below the Solution: Output:
Q: Row 10 [28] 139 [29] [30]
A: We are going to convert decimal number 139 to its equivalent binary, octal and hexadecimal number. P...
Q: There are three exciting new applications becoming possible as a result of the development of the in...
A: Introduction: For starters, as IoT technology progresses, more firms will benefit from IoT applicati...
Q: I mean these Instructions: BSF, BCF, MOVLW, MOVWF, CLRW, BTFSS, GOTO, RETURN ,DECF, ... etc Thank yo...
A: 1. BSF Bit Set F Bit ‘b’ in register ‘f’ is set Syntax: [ label ] BSF f,b Operation: 1 → (f<...
Q: List the truth table of the function F = abc + a’c’.
A: Given F = abc + a'c' The number of variables in F are 3 For 3 variables, there are 8 possible truth ...
Q: What type of impact will the Internet of Things (IoT) have as it affects our daily lives? Use any ga...
A: Given: What kind of influence will the Internet of Things (IoT) have on our daily lives? Use any dev...
Q: Given S = (a, b, c}. Prove this language is regular: L = {u €S*:u has at least 1 a, 1 b, and 1c) usi...
A:
Q: me of the libraries that python has to help with cybersecurity? What are some that you think every c...
A: Below are some of the libraries that python has to help with cybersecurity
Q: You have to take 2 integer numbers from the user & then print true if they are both in the range 70....
A: #include <iostream> using namespace std; int main(){ int a,b; cout<<"Enter fir...
Q: Explain the use of final keyword in variable, method and class.
A: Introduction: The final keyword in Java is a non-access specifier for restricting access to a class,...
Q: (python) Write a function myfunction that requests user input i the form of an integer value, 1, 2 ...
A: Code: def myfunction(): while(True): i=input("Select option: ") if(i=="1" or i=="2"...
Q: Hi! I would like to ask if how can I implement my findRing() function here. There's 2 constraint...
A: I have provided C CODE along with CODE SCREENSHOT and also provided OUTPUT SCREENSHOT--...
Q: Compare and contrast massively parallel processing technologies with grid computing.
A: The answer is given below
Q: Computer science What are the requirements for using the Amazon Web Services SDK S3 with a Spring B...
A: Introduction What are the requirements for using the Amazon Web Services SDK S3 with a Spring Boot...
Q: What are the various database engines that may be used with AWS RDS?
A: Intro Database engines A database engine is the fundamental software component that a database mana...
Q: What is the format of a memory address as seen by the cache; that is, what are the sizes of the tag ...
A: Cache lines are arranged into sets in a cache in the primary storage hierarchy. The cache is said to...
Q: er
A: given - Describe Quality of Service (QoS) technique part of Network layer. This should include the d...
Q: Explain....... 1.Given f(n)=3nlgn+2. State if the following are true (T) or false (F): i) f(n) =O(...
A: Here in this question we have given two function and we have asked to find that given asymptomatic ...
Q: Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-wei...
A: Problems with repeated loops in spanning tree: The binary tree avoidance strategy can be used to tac...
Q: Fill in the blank so that this program keeps asking for input until the user enters a number between...
A: Your answer is given below with an explanation and output of the code.
Q: Because of their fundamental nature, wireless networks are vulnerable to a wide range of problems. T...
A: Introduction: Definition:- The term "wireless network" refers to a system in which network nodes ...
Q: In linux system , what is your indication that you successfully move a file !!?
A: answer is
Q: Describe how a menu-driven command processor like the one created in Chapter 9 for an ATM applicatio...
A: Introduction: Describe how a menu-driven command processor like the one created in Chapter 9 for a...
Q: Given an 800 x 500 image, calculate the storage size, in bytes, required to store each of the follow...
A: Images file is digital formation in which we can see and watch it in screens. Every image have color...
Q: In this c++ program edit this code and please input the following details Following details Name o...
A: if you want to remove winner and percentage then we dont need this function void outputElection()
Q: Write a function nth_member(data, n) that takes a list data and an integer n as parameters and retur...
A: Answer :
Q: What are the various testing methods available and which one we can apply in projects.
A: Sоftwаre testing methоdоlоgies аre the vаriоus strаtegies оr аррrоасhes used tо test аn ...
Q: For each of the following languages, if it is regular, verify the pumping lemma; if not, prove it’s ...
A: L = wwR: w a, b*; L = wwR: w a, b*; L = wwR: w a, b*; L = L is the set of all strings where first ha...
Q: What is the definition of a heterogeneous distributed databa
A: Introduction: A distributed database system is one that spans several computers or sites rather than...
Q: What is the format of a memory address as seen by the cache, i.e., what are the sizes of the tag and...
A: The main memory address is split into sections called fields. Each field has its own significant mea...
Q: Find a valid conclusion for the following Lewis Carrol puzzles. (HINT: Express the given statements ...
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other questions ...
Q: ost machines can replicate data in both directions, from and to another register. The Memory Address...
A: Memory address register : This is one of the main CPU registers. The main purpose of this register ...
Q: user to enter multiple lines of input by pressing the enter key at the end of each line. The program...
A: given - Write a program that reads in a sequence of characters entered by the user and terminated by...
Q: Q4) By using Graphical Method to determine the optimal value of X1 & X2 that maximize value of Z. Ma...
A: Your Solution is given below in detail. Given, Max (Z) = X1 + 2X2 Subject to; 2X1 + 5X2 ...
Q: Below is C code that runs successfully but now i want to rewrite this C code and convert it to MIPS ...
A: the answer is an given below :
Q: Explain how a stateless firewall would block all incoming and outgoing HTTP requests.
A: Introduction: Stateless firewalls are designed to protect networks using static information like sou...
Q: What are design patterns' roles in software engineering, and how can they be utilized effectively? G...
A: Introduction: A design pattern is a reusable, generic solution to a common problem in software devel...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- PYTHON code that finds the prime divisors of a number entered on the keyboard and prints it on the screen write. (For example, the prime divisors of 10 are 2 and 5. The prime divisors of 20 are 2, 2 and 5.quadratic.py by using "sys.argv" ● Create a program, quadratic.py, that takes in three arguments that represent the a, b, and c values in the quadratic formula. The values should be to two decimal places. You do not need to account for imaginary values. Then print out both roots in the form: “The solutions are x and y” Where x and y correspond to the positive and negative roots, respectively.program that reads an integer sum in dollars and displays how many dollars bills of $100, $50, $20, $10 and $5 and how many coin of $2 and $1 so that their numbers be minimal. write this Code in the C# programming language explain in detail
- In Python Write a program that allows the user to type in a phrase and then outputs the acronym for that phrase. Note: The acronym should be all uppercase, even if the words in the phrase are not capitalized.Python Programming TasksQuestion 3Businesses some time market their contact no as: 111-GET-SONY. This technique makes easy for the customers to remember the brand name. To do so they use the alphabets that are printed on the numbers on dial pads of Tele/Mobile phones as follows: A, B, andC = 2D, E, and F = 3 G, H, and I = 4 J, K, and L = 5 M, N, and O = 6 P, Q, R, and S = 7 T, U, and V = 8 W, X, Y, and Z = 9. However, the telecom systems needs proper numbers for dialing. Create anapplicationthatshould prompt the user to enterthe no in specified format such as XXX-XXX-XXXXand then translates the number to their numeric equivalent. Input: 111-GET-SONYOutput: 111-438-7669 Question 4Write a program imitating a website where users can signin/signup, view certain information which can only beseen by signed in users, logout or exit the application.Initially you would have asequence userswithfollowing structure:users =…Python: VOWEL OR CONSONANT Challange Ask the user to input a word. The program will then tell them how many letters are in the inputted word. It will also tell them how many vowels and consonants are in the word. It will then ask which number (between 1- the length of their word - DO NOT USE THE PLACEHOLDER ZERO) that they would like to pick. It will then tell them whether that letter is a vowel or consonant. Next the program will pick a random letter from the word that was inputted, print that letter and tell the user whether it is a vowel or consonant: OUTPUT: What is your word?: Larry There are 5 letters in Larry. There are 1 vowel and 4 consonants For your word, L is "1" and Y is "5" Which letter do you want 1-5? 4 The letter you picked is an "r" and that letter is a CONSONANT and there are two of them I picked a random letter from your word, it is "a" The letter I randomly picked is a VOWEL Remember : vowels are "a, e, i, o, u" a "y",should output as "…
- Python Calender library- Write a program that takes input year number from user and print the calender of whole year with day of each date.Q7: Code a complete Python program that performs the following operations by reading the weight of athletes until a zero is entered on the keyboard. When a negative value is entered by mistake from the keyboard, it should ask to enter the value again. How many athlete weights have been entered, Average weight of all athletes, Programmer must find out how many athletes are in each weight. Weight weight <50 Lightweight 50≤ kg <70 Middleweight Higher Heavyweight SAMPLE RUN Enter weight: 30 Enter weight: 65 Enter weight: 90 Enter weight: 120 Enter weight: 0 ------------------------------------- There are 1 light, 1 medium and 2 heavy weights1. Write a program that lets the user guess whether a randomly generated integer would be even or odd. The program randomly generates an integer and divides it by 2. The integer is even if the remainder is 0, otherwise odd. The program prompts the user to enter a guess and reports whether the guess is correct or incorrect.
- JAVA PROGRAMMING LAB Write a Java program to takes 2 numbers from the user and print true if one or the other is teen, but not both. "teen" number is that number which lies in the range 13..19 inclusive.Python Programming Only Please: Write a program that asks the user to enter a person’s age. The program should displaya message indicating whether the person is an infant, a child, a teenager, or an adult. Following are the guidelines: • If the person is 1 year old or less, he or she is an infant.• If the person is older than 1 year, but younger than 13 years, he or she is a child.• If the person is at least 13 years old, but less than 20 years old, he or she is a teenager.• If the person is at least 20 years old, he or she is an adult.Collatz Sequence: In 1937, Lothar Collatz proposed that no matter what number you begin with, the sequence eventually reaches 1. This is widely believed to be true but has never been formally proved. Write a program that inputs a number from the user, and then displays the Collatz Sequence starting from that number. Stop when you reach 1. If n is even, divide it by 2 to get n / 2. If n is odd, multiply it by 3 and add 1 to get 3n + 1. Repeat the process indefinitely. Find out and print the maximum number that you can get in these calculations. ' Part-3: Please enter a number: 2051 6154 3077 9232 4616 2308 1154 577 1732 866 433 1300 650 325 976 488 244 122 61 184 92 46 23 70 35 106 53 160 80 40 20 10 5 16 8 4 2 1 The maximum number you get: 9232

