Write a query to delete job with id of 10 from job table
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter3: Database Systems And Applications
Section: Chapter Questions
Problem 3PSE
Related questions
Question
Write a query to delete job with id of 10 from job table
Transcribed Image Text:tables.pdf
1 / 5
80%
+
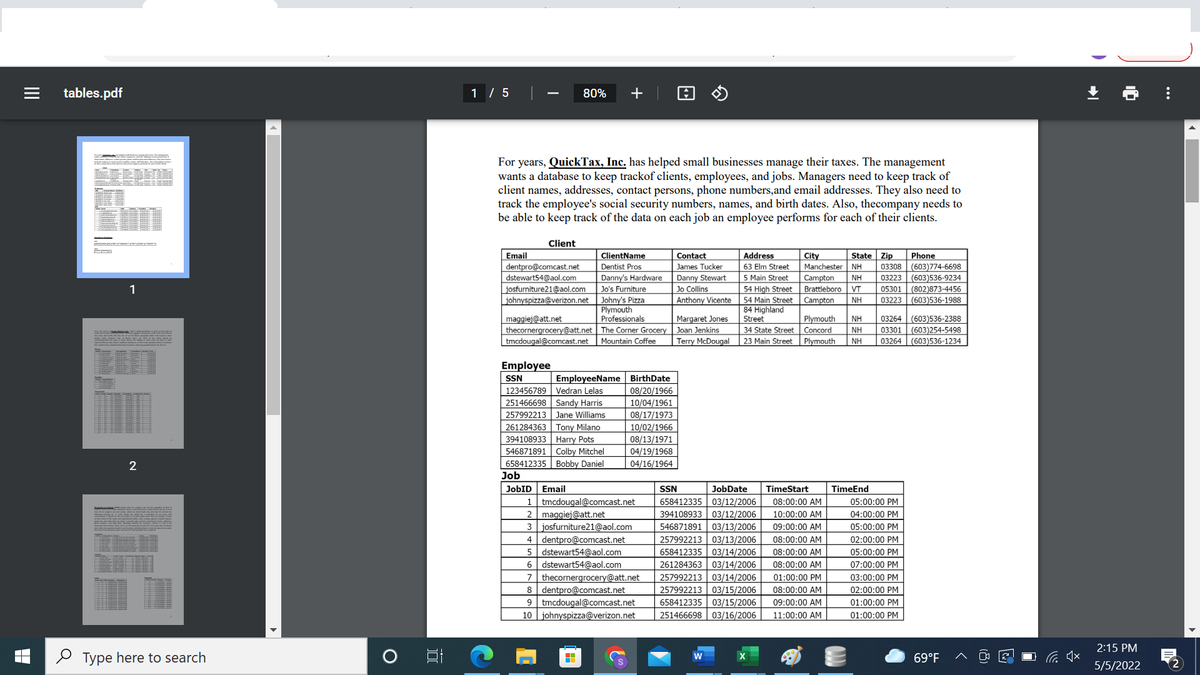
For years, QuickTax, Inc. has helped small businesses manage their taxes. The management
wants a database to keep trackof clients, employees, and jobs. Managers need to keep track of
client names, addresses, contact persons, phone numbers,and email addresses. They also need to
track the employee's social security numbers, names, and birth dates. Also, thecompany needs to
be able to keep track of the data on each job an employee performs for each of their clients.
E
Client
ClientName
Address
State Zip
Phone
(603)774-6698
03223 (603)536-9234
Email
Contact
City
63 Elm Street
dentpro@comcast.net
dstewart54@aol.com
osfurniture21@aol.com
johnyspizza@verizon.net
Dentist Pros
James Tucker
Manchester
NH
03308
Danny Stewart
Jo Collins
Danny's Hardware
5 Main Street
Campton
Brattleboro VT
NH
1
Jo's Furniture
54 High Street
05301
Johny's Pizza
Plymouth
Professionals
Anthony Vicente
54 Main Street
84 Highland
Street
Campton
NH
03223
(603)536-1988
Margaret Jones
Joan Jenkins
03264
03301
Plymouth
maggiej@att.net
thecornergrocery@att.net The Corner Grocery
NH
(603)536-2388
(603)254-5498
(603)536-1234
34 State Street
Concord
NH
tmcdougal@comcast.net
Mountain Coffee
Terry McDougal
23 Main Street
Plymouth
NH
03264
Employee
EmployeeName BirthDate
08/20/1966
10/04/1961
08/17/1973
10/02/1966
08/13/1971
SSN
123456789
Vedran Lelas
251466698 Sandy Harris
257992213 Jane Williams
261284363 Tony Milano
394108933 Harry Pots
546871891 | Colby Mitchel
658412335 | Bobby Daniel
04/19/1968
04/16/1964
Job
JobID
Email
SSN
JobDate
TimeStart
TimeEnd
1 tmcdougal@comcast.net
2 maggiej@att.net
3 josfurniture21@aol.com
dentpro@comcast.net
dstewart54@aol.com
6 dstewart54@aol.com
thecornergrocery@att.net
8 dentpro@comcast.net
9 tmcdougal@comcast.net
10 johnyspizza@verizon.net
658412335 03/12/2006
394108933 03/12/2006
546871891 | 03/13/2006
257992213 03/13/2006
658412335 03/14/2006
261284363 03/14/2006
257992213 03/14/2006
257992213 03/15/2006
658412335 03/15/2006
251466698 03/16/2006
08:00:00 AM
05:00:00 PM
10:00:00 AM
04:00:00 PM
09:00:00 AM
05:00:00 PM
4
08:00:00 AM
02:00:00 PM
08:00:00 AM
05:00:00 PM
08:00:00 AM
07:00:00 PM
7
01:00:00 PM
03:00:00 PM
08:00:00 AM
02:00:00 PM
09:00:00 AM
01:00:00 PM
11:00:00 AM
01:00:00 PM
2:15 PM
2 Type here to search
W
69°F
5/5/2022
2
...
II
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning