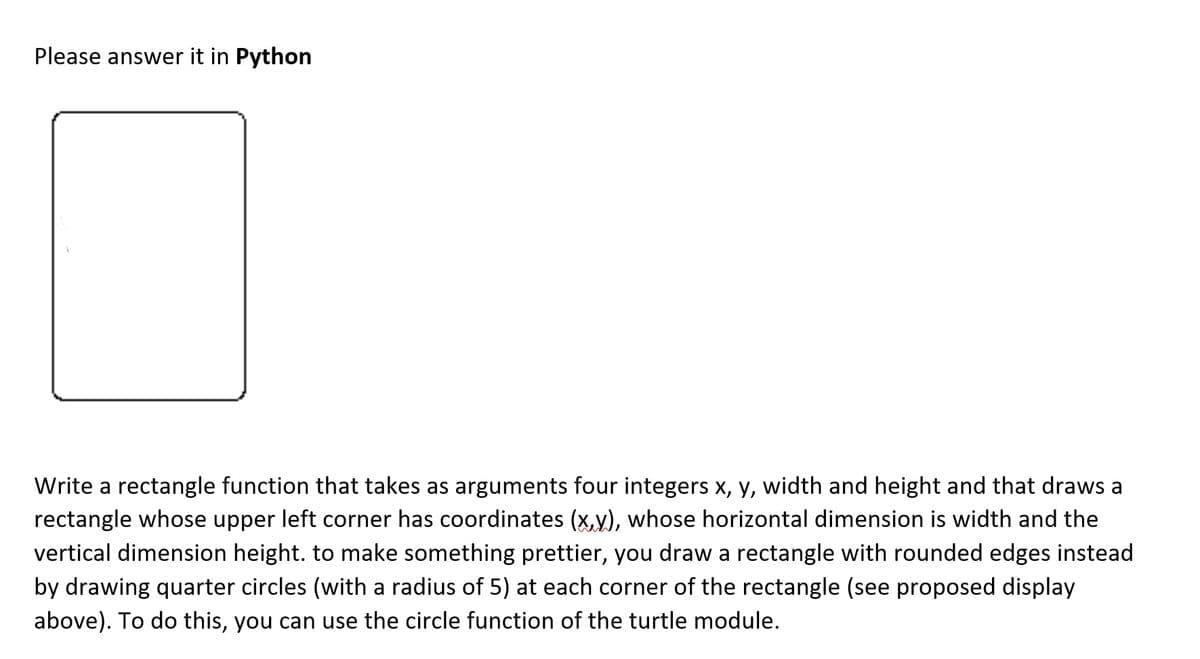
Write a rectangle function that takes as arguments four integers x, y, width and height and that draws a rectangle whose upper left corner has coordinates (x,y), whose horizontal dimension is width and the vertical dimension height. to make something prettier, you draw a rectangle with rounded edges instead by drawing quarter circles (with a radius of 5) at each corner of the rectangle (see proposed display above). To do this, you can use the circle function of the turtle module.
Write a rectangle function that takes as arguments four integers x, y, width and height and that draws a rectangle whose upper left corner has coordinates (x,y), whose horizontal dimension is width and the vertical dimension height. to make something prettier, you draw a rectangle with rounded edges instead by drawing quarter circles (with a radius of 5) at each corner of the rectangle (see proposed display above). To do this, you can use the circle function of the turtle module.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter5: Control Structures Ii (repetition)
Section: Chapter Questions
Problem 14PE
Related questions
Question
Transcribed Image Text:Please answer it in Python
Write a rectangle function that takes as arguments four integers x, y, width and height and that draws a
rectangle whose upper left corner has coordinates (x,y), whose horizontal dimension is width and the
vertical dimension height. to make something prettier, you draw a rectangle with rounded edges instead
by drawing quarter circles (with a radius of 5) at each corner of the rectangle (see proposed display
above). To do this, you can use the circle function of the turtle module.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning