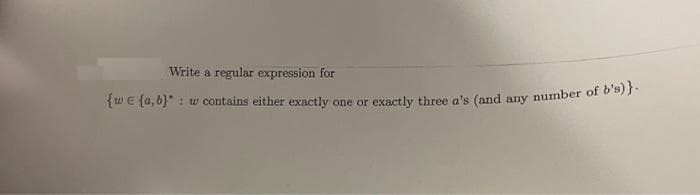
Write a regular expression for {wE {a, 6}" : w contains either exnctly one or exactly three a's (and any number of o B)
Q: Compute the edit distance (using insertion cost 1, deletion cost 1, substitution cost 1) of "beat" t...
A: The edit distance is a way of measuring of how related two strings are. This is defined as the small...
Q: dont dont post existing one strict warning skip if not known A new architecture, with N layers, is p...
A: We have a total of N layers..The message generated at the top layer is M bytesSo the message have to...
Q: Determine whether the following array declarations are valid. If a declaration is valid, write VALID...
A: An Array is one of the data structure in Java. The array is a container object that can store a pred...
Q: Software that runs on the internet is known as web-based application software.
A: yes, software that run on the internet is known as web-based application software.
Q: write c++ program to input three int greatest
A: Below the c++ program to input three integers and to display the largest one. greatest
Q: 10 30 36 The link fields are not shown. The above tree should be in-place converted to following Dou...
A: //Note: I have given the answer as asked in the question //Solution: class db_li_node// storing node...
Q: user_hashes.txt -/labl Open Save userl:saMNhdbYqwtng user2:$1$saltsaltsuf4ZS8mOUI3KOJVGdwOGg/ user3:...
A: Each self-regarding pentester ought to have a strong secret phrase saltine in their toolbox, and Joh...
Q: Look into one intriguing data or text mining application and explain it.
A: Text mining: Text mining, also known as text data mining, is the technique of extracting high-qualit...
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: Approach: The isinstance() function in Python takes the object and the class as the parameters and r...
Q: Discuss the Life cycle activities of Prototyping model in detail with diagram.
A: Prototyping Model is a type of model which is used in software development where prototype that mean...
Q: What's the difference between Stored Procedures and Scripts? What is the purpose of each? Howv does ...
A: Introduction: A stored procedure (also known as a proc, storp, sproc, StoPro, StoredProc, StoreProc,...
Q: 1. Explain the tone of email. 2. Explain think of length of email.
A: 1. Explain the tone of email. Ans:- The writer's emotional condition toward the reader or subject ma...
Q: A MAC computer can be acquired easily by __________ Imaging RDP Connection to anot...
A: The Remote Desktop Protocol can be used in acquiring the MAC easily.
Q: You've been requested to construct a customer-performance scorecard for your company's toy business ...
A: The three measures that might be included are-(1) percentage of new customers to average number of...
Q: There are 4 paths as follows: Path 1: Start → 1 → 4 → 5 → 6 → 7 → 8 → 9 → 10 → End ...
A: SOLUTION:- 1.1 Activity/event a c b Mean Variance Start 1 5 15 30 16.6666667 158.333333 2 5...
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Information, consumers, and organizations must be protected against data theft, business disruption,...
Q: In JAVA language, write a program to input an integer p from the user and then print the count of di...
A: In JAVA language, write a program to input an integer p from the user and then print the count of di...
Q: What is the mantissa and exponent for 6.75 in 8-bit binary floating point?
A: Let's see the solution in the next steps
Q: BARBODHARUP
A: BARBODHARUP
Q: Explain what the statement below means and provide an example of such a situation in no more than 30...
A: Explain what the statement below means and provide an example of such a situation in no more than 30...
Q: Assume you're working on a new word processor with more functionality than any of your rivals. What ...
A: Actually there are different way to remember the all type of commands. I will discuss the some impor...
Q: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let Bob’...
A: The answer is
Q: Microsoft Word 2016 has a number of new and improved features. Which feature in Word 2016 do you thi...
A: Introduction: Microsoft Word 2016 has a number of new and improved features. Which feature in Word 2...
Q: Explain the phrase "balanced scorecard" in just a few words. What role does it play in the operation...
A: What you measure up is what you get. Senior executives understand that their organization's rating s...
Q: post an excel spreadsheet than can be used to compute imputed interest and taxable social security b...
A: FICA is among the most prevalent fundamental taxes that people have to pay. The Federal Insurance Co...
Q: What exactly was "Networking"?
A: Networking: It is the exchange of information, data and ideas among different people with a common p...
Q: What part does database technology play in an organization's data management?
A: Introduction: What part does database technology play in an organization's data management?
Q: Two types of computer incidents occur. One is when a computer is used to commit the crime and the ot...
A: In case of the victim using someones computer, then it is considered as crime.
Q: What is the difference between hardware and software interrupts, and when do they come into play?
A:
Q: The MBR is not present on which of the following? Hard drive Bootable floppy disk ...
A: Answer-:Option(b)
Q: Write an assembly language program using GNUSIM8085 i have 30 mins to devliver please slove faster i...
A: Given se faster, Write an assembly language program using GNUSim8085 i have 30 mins to devliver plea...
Q: Assume you wish to solve a maximum flow issue using parallel arcs, but you don't have any maximum fl...
A: Given The answer is given below. Answer: Parallel Arcs: Parallel arc shortcomings happen between two...
Q: Let's try to add dynamically property of an object and the property must be function and variable in...
A: We can able to add the dynamically property of an object and the required property must be function ...
Q: Similarly, the Windows server OS can run regular workstation applications such as MS Office or Adobe...
A: It affects the system speed.Here, windows server OS can run the regular workstation applications lik...
Q: Instruction: Identify if the following is UNIQUE IDENTIFIER or NOT. Promotion ID File Upload
A: "Promotion ID" is UNIQUE IDENTIFIER because user A's promotion ID will be different from User B's pr...
Q: When utilizing a logic programming language such as Prolog to tackle computing problems, what are th...
A: INTRODUCTION: Logic programming is a type of computer programming in which program statements expla...
Q: How do you make sure each machine utilises its own private key pair while using IPsec?
A: IPsec repository for group of protocols that are used together to set up encrypted connections betwe...
Q: Discuss the various scheduling strategies in terms of (a) waiting time, (b) hunger, (c) turnaround t...
A: The process of determining which process will have exclusive use of the CPU while another is paused ...
Q: True or false? An organization should periodically conduct an inspection of its systems and practice...
A: Introduction: True or false? An organization should periodically conduct an inspection of its system...
Q: In Windows 2016, what are the different types of "flavours?"
A: In Windows 2016, what are the different types of "flavours?"
Q: Describe a cloud storage application and explain how it differs from a standard client storage progr...
A: Lets see the solution in the next steps
Q: Discuss the various scheduling strategies in terms of (a) waiting time, (b) hunger, (c) turnaround t...
A: Algorithm for Scheduling There are several scheduling algorithms in use today, and they are used to ...
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: Introduction: The memory capacity is determined by various factors, including the number of address ...
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms prop...
A: Your solution is here given below.
Q: Suppose you are given with a ROM chip of size 1024*8 and 5 RAM chips of size 512*8. Show diagrammati...
A: The formula for calculating RAM devices: This chip has eight bits. Because one byte requires eight b...
Q: Microsoft Word 2016 has a number of new and improved features. 2016 do you think is the most useful?...
A: Below square measure the listed features:1. sanctio-native the coauthoring: completely different use...
Q: What exactly does the following code display to the screen? print (' ',end ='') for i in range (1...
A: i compiled your code and given output what it displayed on a screen
Q: In a computer with a 32-bit data-bus, how many 4-bit wide memory components are used? the answer to ...
A: The answeris given below:-
Q: Suppose memory access takes 100 ns and register access takes 1 ns (or less), calculate and compare t...
A:
Q: Software that runs on the internet is known as web-based application software.
A: answer is
Step by step
Solved in 2 steps

- Find a regular expression R so that L(R) = L(D) where D is the following DFA:Evaluate the following postfix expressions:a. 12 18 - 30 + 2 * 3 / =b. 28 5 / 3 + 5 4 * - 8 + =c. 13 18 10 17 2 20 + - + / * =d. 7 3 6 2 + - + 2 * 8 + =e. 29 3 / 6 + 12 - 3 4 * + =Write a computer program in C++ to find solution of the following systems of equations using Gauss Elimination Method. 2x+y+z=10, 3x+2y+3z=18, X+4y+9z=16
- Evaluate the following postfix expressions: 82 + 3 * 16 4 / + = 12 25 5 1 / / * 8 7 - - = 70 14 4 5 15 3 / * - - * 6 + = 3 5 6 * + 13 - 18 2 * + =Write a C line to represent the following equationFor each of the following regular expressions over Σ = {a, b}, state 5 strings that are in the language of the regular expression, and 5 strings that are not. 1. (a∗b)∗|a∗2. (Σ∗aaΣ∗)|(Σ∗bbΣ∗)|(ab)∗|(ba)∗|a|b
- write a program in c++ that converts Celsius to Fahrenheit according to the following equation: F=9/5 C+32 by using function.Write a program to display the sum of digits of every palindromic number from m to n. Input of m and n should be given by user write the program in c language without using functionsWrite a program in c ++to calculate the following function f (x) for( n) that is give by the user
- Write a program that prompts for and reads the radius and the height of a cylinder (in centimeters). It then computes its volume by using pass by reference and pass by value.Note: pie=3.14159 Using pointers C++ programmingConstruct triples of the expressionsI am needing assistance with the following problem. Write a C++ program that reads a set of integers and then finds and prints the sum of the even and odd integers.

