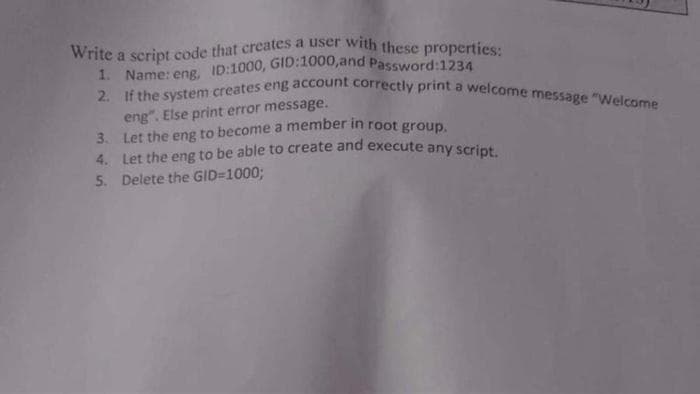
Write a script code that creates a user with these properties: 1. Name: eng, ID:1000, GID:1000,and Password:1234 2. If the system creates eng account correctly print a welcome message "Welcome eng". Else print error message. Let the eng to become a member in root group. 3. 4. Let the eng to be able to create and execute any script. 5. Delete the GID=1000;
Q: Does it usually take a certain length of time before someone interrupts you? How does this relate to…
A: Introduction: The operating system creates an interrupt whenever a hardware event that is not…
Q: What does the term "computer programming" mean? What aspects need to be considered while choosing a…
A: In step 2, I have provided ANSWER WITH BRIEF EXPLANATION-----------
Q: Describe the process that a stateless firewall uses to reject all HTTP requests.
A: Introduction: In the case of a stateless firewall, there is no brain. It contains no memory to…
Q: To what extent can a business be protected from cyber threats like viruses and hackers?
A: A business can never be completely protected from cyber threats like viruses and hackers, but it can…
Q: As the processor returns a chunk of data from the write buffer to main memory, it also sends a…
A: When a processor needs to add a comment, it first checks to see whether the address it needs to…
Q: demonstrates how selection sort works. The operation FIND MINIMUM (L,i,n) picks the smallest element…
A: The operation FIND MINIMUM (L,i,n) picks the smallest element from the array L[i:n] and returns the…
Q: You are given a string s of lower case english alphabets. You can choose any two characters in the…
A: Algorithm : 1: Start2: Create a frequency list with 26 elements and initialize all values to 0.3:…
Q: This section should provide a clear and succinct explanation of the two factors that are often…
A: Operating System: Software makes up the operating system of a computer. An operating system (OS) is…
Q: Give some background on the term "cybersecurity" and what it implies.
A: Cybersecurity is a rapidly growing field in today's technology-driven world. It encompasses a wide…
Q: TODO 10 Now it's your turn to define an entire class. Complete the TODO by creating the…
A: The task asks to define a class called LogTransformer which will implement two methods fit and…
Q: 8. Draw a Java use case diagram for a Library Management System.
A: Commonly known as a behavior diagram, use case diagram is used to describe the actions of all users…
Q: What's the difference between consistent processing and using FIFO?
A: Consistent processing refers to the ability of a system to process data in a way that produces the…
Q: Analyze how well and how often your social skills were put to play throughout the preparation and…
A: INTRODUCTION: Communication skills, speaking, listening, walking, looking, personality, mood, and…
Q: Explain what you mean by "application security."
A: Introduction of Security: Security in terms of computers is the protection of data from unauthorized…
Q: What exactly is meant by the phrase "fine-grained multithreading," and how did it come to be used?
A: Given: What is fine-grained multithreading, exactly? Solution: Multithreading: It is described as…
Q: In this context, it is important to highlight the role that firewalls play in protecting computer…
A: In order to adequately answer the question, we must define network scanning and assessment as a…
Q: Discuss the pros and cons of using pre-made software packages rather than developing in-house…
A: Although constructing a customized vehicle may seem appealing, time and budget constraints will…
Q: this C++ code is pre-existing and cannot be changed or modified. for it to work, the program has to…
A: Solution: Given, #include <iostream>#include <vector>using namespace std; int main() {…
Q: How can employees of a company make sure that knowledge is retained? Let's say your company is…
A: Introduction As a manager, there are several ways that you can ensure that your employees are…
Q: [ Question related to Aws Ec2] When We Host Webserver On Ec2 Linux Instance ,We can access it from…
A: Yes, we can access the AWS Ec2 Linux Instance, using an SSH client called Putty. The ability to…
Q: Please provide me a rundown of the top five vulnerabilities and threats currently facing my system.
A: Introduction: Network security vulnerabilities are faults in the system's code, hardware, or…
Q: Learn about the hacking tests that were performed. Specifically in the field of cyber security?
A: Cybersecurity testing is an important aspect of information security. It is a process that helps…
Q: In a few sentences, describe some of the issues plaguing the world's information systems.
A: Dear Student, The answer to your question is given below -
Q: C++ First, read in an input value for variable numIn. Then, read numIn integers from input and…
A: The provided code takes an integer input 'numIn' from the user and then takes 'numIn' i.e. number of…
Q: There may be a variety of issues and drawbacks brought on by disparate information systems.
A: Disparate information systems refer to a situation where multiple information systems are used in an…
Q: TODO 1 Let's load the forestfires.csv by using Pandas read_csv() function. The read_csv() function…
A: Introduction Pandas: Pandas is just a Library for python to manipulating and analyzing the data. It…
Q: How exactly does one go about describing the Internet layer to another person?
A: The answer is given below step.
Q: how do i zip a folder with code in python?
A: To compress individual files into a ZIP file, create a new ZipFile object and add the files you want…
Q: Is there any value added by a Cyber Security educator?
A: Absolutely. Cybersecurity is a rapidly evolving field, and the need for knowledgeable educators is…
Q: Describe ISA (Instruction Set Architecture) and the many ISA (Instruction Set Architecture) kinds,…
A: ISA: An instruction set architecture is ISA. These instruction sets are combinations of commands…
Q: Talking about metrics in your own words is one way to increase the quality of your network.
A: When it comes to improving the quality of a network, metrics play a crucial role. Metrics are…
Q: Suppose you have a RISC machine with a 2.7 GHz clock (i.e., the clock ticks 2.7 billion times per…
A: Please refer to the following step for the complete solution to the problem above.
Q: How does starting from scratch in computer science compare to starting with a packaged data model on…
A: Introduction Fostering a model for data is perhaps the earliest move toward mapping out the…
Q: It would be helpful to include an explanation of the DHCP lease. How exactly does one go about…
A: A device on a network may receive a temporary IP address assignment through DHCP (Dynamic Host…
Q: Differentiating between users and their respective responsibilities is crucial for effective…
A: Introduction: Computer security access control is a security measure used to protect computer…
Q: It is important for teachers to understand the benefits and limitations of educational information…
A: Introduction : An Educational Information System (EIS) is a computer-based system designed to manage…
Q: Is there a standard firewall design in place at your firm now?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Provide a comprehensive breakdown of the dangers posed to data if the system fails.
A: Dear Student, The answer to your question is given below -
Q: What, precisely, is meant by the term "complexity"?
A: Complexity: When anything is divided into several components that combine in various ways, the term…
Q: Identify two firewalls at the network layer.
A: The following are some firewalls that operates at the network layer (layer-3) are: Border Gateway…
Q: What possible consequences can a breach in cyber security have for a company?
A: When sensitive information that has been stored at an advanced stage is accessed by any unauthorised…
Q: 7. Write an application in Java that creates and starts three threads. a. Each thread is…
A: The java code for the above given question is given below:
Q: Find out how technology and data are used to solve the problems experienced by data systems.
A: Introduction : A data system is a collection of data, hardware, and software components that are…
Q: A typical operating system is made up of a variety of parts, each of which has a distinct function.
A: Introduction The core of an operating system, which is the user interface, is a PC program called a…
Q: What can you do to make sure your model gets all the data it needs? What benefits can problem…
A: In model creation we need correct data to give accurate results.
Q: Customer Number: Customer Name: Customer Address: 1001 Sales Order Number: Sales Order Date: ABC…
A: 3NF: 3NF stands for Third Normal Form, which is a database design principle used in relational…
Q: Question: In computer science, a sorting algorithm is an algorithm that puts elements of a list…
A: Algorithm steps to solve the given problem: Start Set the initial minIndex to the first index in…
Q: There are several methods to combine boolean expressions.
A: The answer for the above question is given in the following step for your reference
Q: Define what a hack or virus is and the measures a company may take to prevent them from entering its…
A: Dear Student, The detailed answer of your question is given below -
Q: What makes software modeling different from software development? Describe the ways in which one…
A: Software Development Methodology: A software development process in software engineering is a method…
Step by step
Solved in 2 steps

- Add to this code & apply in it, hashing for Confidentiality service or Username & password for Authentication service (JAVA code) server side class initializes socket, establishes connection with socket.accept method, read string and close the connection. but this code Doesn't it implement authentication and confidentiality services, so you should ADD IT in this codes below Server class import java.net.*; import java.io.*;public class TestServer {public static void main(String[] args){try{ServerSocket ss=new ServerSocket(8088);Socket s=ss.accept(); DataInputStream DataInput=new DataInputStream(s.getInputStream());String str=(String)DataInput.readUTF();System.out.println("message= "+str);ss.close();}catch(Exception e){System.out.println(e);}}} client class import java.io.*;import java.net.*;public class TestClient {public static void main(String[] args) {try{Socket s=new Socket("localhost",8088);DataOutputStream output=new…Write a server for a client. The client sends loan information (annualinterest rate, number of years, and loan amount) to the server (see Figure a).The server computes monthly payment and total payment, and sends them back tothe client (see Figure b). Name the client Exercise33_01Client and the serverExercise33_01Server.I need help with this: (BMI Server) Write a server for a client. The client sends the weight ( in pounds) and height (in inches) for a person to the server (see Figure 33.18a). The server computes BMI (Body Mass Index), and sends back to the client a string that reports the BMI (see Figure 33.18b). See Section 3.8 for computing BMI. Name the client Exercise33_01Client and the server Exercise33_01Server.
- Explain the following code clientObj.hasOwnProperty("Batman") && (clientObj["Batman"] = "Dormant");Create a simple Client-Server communication via Sockets where Client will send the message in following form → {message, SHA_256_hash_value}. Once the server receives the message it will parse it, calculate the SHA_256 hash value of the message part and compare it with the received hash. If values are matching it will send 'OK' back to Client, else 'Message was compromised'. Use Java GUI to send and receive messages in both parties (client and server).what is access modifier? Access modifier is good? why? We have Public, Default, Private, and Protected access modifiers do yo0u think which access modifier is better? why? Do we need all of them(access modifiers)? if you able to remove one of them which of them will you chose? why?
- An example of session design pattern implementation in a web application could be a loginsession:In this example, the Session class is implemented as a singleton, it has methods for logging in,logging out, checking authentication status and getting the user.The class implements a private constructor, which ensures that only one instance of the classcan be created, and a static method for retrieving the single instance.This way, the session object can be accessed from any part of the application, in order to checkthe user's authentication status, retrieve their user object and maintain their sessionthroughout the application.A client wishes to open a new account at a bank branch. To do so, his instance of class client must first be retrieved from the central bank server. For a new clinet, an instance of client must be created. An instance of BankAccount is then created using the Client Object. A deposit must then immediately follow, to complete the account creation process.ProblemYou know that you will need to create a strong passphrase every time you create anSSH key, and you want to define a policy that spells out what a strong passphrase is.So, what makes a strong passphrase?
- Design a Login interface with python tkinter with the following requirements: Use ttk kit Use a Frame, which is not resizable Ask for a Username and a password Have a button that does "Login", the button has the action (command=) to validate that the password entered is greater than 8 digits and is not "12345678" or "password" The "User" and "Password" labels are aligned to the rightA company is implementing tokenization as an alternative to protecting data without encryption. During this process, the application collects a piece of sensitive data. Which step should occur immediately after this action? A. Data is sent to the tokenization server. B. The tokenization server generates the token. C. The tokenization server returns the token to the application. D. Token data is stored by the application.Implement a new alias command (mandatory for teams of 4 and not required for teams of 3) Add a new built-in alias command that allows you to define a shortcut for commands by essentially defining a new command that substitutes a given string for some command, perhaps with various flags/options. The syntax is as follows: alias alias_name='command'. For example, you can define an alias with alias 5='ls –al', so that the user can then enter 5 at the prompt to execute the ls -al command. Although there is an alias command in bash, you must implement your own version and not make use of the built-in alias bash command. Typically, alias is a built-in command, but since this affects how your shell functions (i.e., you simply cannot just pass an aliased command to the exec family system call as you are managing the execution which would otherwise result in a not found message. Specifying alias with no arguments should display a list of all existing aliases. You may remove a single alias with…



