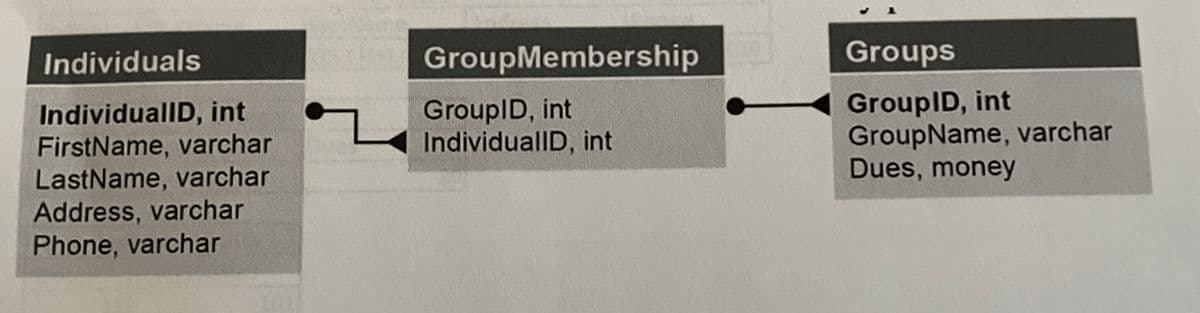
Write CREATE TABLE statements to implement the following design. Include foreign key constraints. Define the individualID, and GroupID as identity columns. Decide which columns should allow null values, if any. Define Dues column with a default of zero and check constraints to allow only positive values.
Q: ne nonal 15. Draw the nated logic diagram for the following Boolean expressions. You may use XOR…
A: Boolean Expressions: Boolean expressions are expressions that use logical operators and return…
Q: Defend the inclusion of GPS receivers in mobile phones and give some examples of their usefulness.
A: Positioning and Navigational System ReceiverThe initials "GPS" stand for "Global Positioning…
Q: Do not copy from other websites Q. Explain creating desired colors for a specific pixel on LCD…
A: The pixel is a word created from picture component is the fundamental unit of programmable variety…
Q: Clear explanation and examples of how to use the ACTION and METHOD elements in both form design and…
A: The purposes of the properties ACTION and METHOD as they are used in forms When a form is submitted,…
Q: Create the GET_CREDIT_LIMIT procedure to obtain the full name and credit limit of the customer whose…
A: From the above given question we have to write an SQL query that take the Customer ID as input and…
Q: Write SQL statement that prints the intitials (first letter of first name and first lettter or last…
A: Write SQL statement that prints the intitials (first letter of first name and first lettter or…
Q: Database Management Concepts Exercise - BITS Corporation You've explained replication to management,…
A: Database Management Systems (DBMS) are software systems used to store, retrieve, and run queries on…
Q: Discuss the benefits of incorporating technology into the classroom. The impact of IT on college…
A: Information technology helps professors and students with new methods of education. And also,…
Q: Define and explain the functions of firewalls, IDSs, and IPSs. I'm interested in hearing your…
A: The function of firewalls: A firewall is a "network security device" capable of monitoring (or…
Q: @@@2 Federal enterprise architecture framework(FEAF) vs EA3 cube framework. Compare and contrast…
A: An enterprise architecture framework is a system. It helps to reverse the bigger problems facing IT…
Q: What is the distinction between a packet-filtering router and a stateful inspection firewall when it…
A: Packet filters analyze outgoing and incoming packets to regulate network access. It allows or blocks…
Q: Figure 3 shows a class diagram that consists of three classes, class Shape, class Circle, and class…
A: a. The type of relationship which exists between class Shape and class Circle is generalization. As,…
Q: To clarify, what is the distinction between the IPA and.am file extensions on iOS?
A: iOS IPA vs..am: iOS binary.ipa file. This format packages and distributes iOS applications. The.ipa…
Q: Put Linux and its features into your own words and explain what makes it special. It would be…
A: Linux is an open source operating system like Windows and MacOS. It is not only limited to an…
Q: To learn more about the AES, search online for "Announcing the Advanced Encryption Standard." Please…
A: Let's see the answer
Q: Which of the many possible network topologies do you propose using?
A: Introduction: Protocols are rules and procedures that outline how two entities should transfer…
Q: Which image support's image layers? A. JPG B.GIF C. BMP D.PNG
A: GIF layer support the image layer not the other one.
Q: Where can I find out more about Assembler and why it might be useful to me?
A: Assembler is defined as the software program that is converting all the instructions of low-level…
Q: To what end does Linux's repquota command serve? Explain. Where does this instruction diverge from…
A: The answer to the question is given below:
Q: standpoint, deep access is preferable to shallow access, rather than focusing solely on performance
A: Dear Student, The answer to your question is given below -
Q: Complete the TODO by finishing the accuracy() function. 1. Compute the total number of correct…
A: Complete the TODO by finishing the accuracy() function.1. Compute the total number of correct…
Q: Ubuntu is the best Linux distribution when compared to other popular options like Red Hat and SUSE.…
A: Introduction: Ubuntu is a Linux operating system that is a part of the Debian Linux distribution.…
Q: Java - Polymorphism Create a class named “Shape” that has the abstract methods getArea() and…
A: Class Shape: package com.bartleby; public abstract class Shape { public abstract double getArea();…
Q: is secure while it's being sent and stored? Which of the following approaches is the best at…
A: Do you think it's important to ensure data is secure while it's being sent and stored? Which of…
Q: When comparing CSFs and KPIs, what are the primary distinctions?
A: The main distinction between CSF and KPI is that the former is what leads to success, whilst the…
Q: malised channel access rate G, and the normalised success rate S (also sometimes called throughput)?…
A: Pure ALOHA is used in a network with Poisson distributed traffic. The success probability, as…
Q: Give some examples of both purely technical and purely sociotechnical software systems, and…
A: Software systems that distinguish between technical and socio-technical bases are listed below:…
Q: Don't just cite performance gains when arguing in favor of deep access over shallow access; instead,…
A: Introduction: From the standpoint of a programmer, provide a defences for using deep access as…
Q: Do you understand how a computer works after reading it? Then we can go on to the hardware of…
A: The architecture of a computer is heavily influenced by both the hardware and the software. It is a…
Q: In what ways are password protection and other forms of access control useful for enforcing rules?
A: Access controls limit access to information and information processing systems. When implemented…
Q: How severe is the digital divide in the United States compared to other parts of the world?
A: Digital Inequality A digital divide is any unequal distribution in the access to, use of, or impact…
Q: As founder of a startup company with a new mobile technology, you decide to draft a checklist…
A: Let's see the answer:
Q: Comparatively to the previous generation, the fourth generation of networks (4G) supports both voice…
A: Explanation: Mobile network spectral efficiency refers to the rate at which information may be sent…
Q: Create the DELETE_INVOICE procedure to delete the invoice whose number is stored in I_INVOICE_NUM
A: Introduction An organized collection of one or perhaps more pre-compiled SQL statements is referred…
Q: Java - Access Specifiers Create a class named Circle that has attributes radius, area, and…
A: formulas to calculate the circumference and area: c = 2πr and A = πr² .
Q: Although you are not required to abide by this request, you are free to do so if you are capable of…
A: Let's see the answer:
Q: You need to provide a thorough explanation of how they will learn about possible values. There is a…
A: A spacecraft that orbits or revolves around a bigger object is called a satellite. An artificial…
Q: 1) Create a class to create a sudoku cell and print it out to the screen. Follow the rules: . . . .…
A: The JAVA code is given below with output screenshot
Q: Write a C++ code that compare the times to traverse a list (containing a large number of elements)…
A: Introduction A linked list is a group of randomly stored items in memory, conjointly referred to as…
Q: If the CFO signs documentation that indicates you should be given permission to delete sensitive…
A: Security is very important to restrict illegal user within a system. Once a user gets right to login…
Q: When trying to test the Firebase app on iOS, what are some of the challenges you face?
A: Explanation The primary source for other useful materials for controlling the applications together…
Q: ll" apply to computer systems design and
A: Introduction: A general-purpose PowerPC core with modest performance is combined with optimised…
Q: In what ways did the rise of cheap microcomputers hasten the spread of software distribution? Who or…
A: The word "microcomputer" refers to a structure that has, at the very least, a microchip, program…
Q: Please help me what is the image below illustrating
A: Fractal Code which refers to the one it is the data that makes up a Digimon and can be obtained when…
Q: Correct and detailed answer will be Upvoted Construct a context free grammar for all binary…
A: A CFG is a grammar which is used to generate all the possible patterns of strings in a given formal…
Q: Some members of the IT security team believe that companies should hire people who have engaged in…
A: A cyber-attack is an assault by hackers using numerous computers against many computers or networks.…
Q: A computer virus is a malicious programme that replicates itself rapidly across computers,…
A: Definition: A computer virus is a piece of malicious software that spreads across computer systems…
Q: What kind of permissions does the Protected Access specifier grant?
A: Access specifier: This element defines whether the field, class, or function Object() { [native…
Q: To what extent can a computer network system be modified to prevent virus infection?
A: The above question that is To what extent can a computer network system be modified to prevent virus…
Q: OVLW 33H; MOVWF 8H; MOVWF 11H; ADDWF 8, 0; ADDWF 11, 1; Questions: What is…
A: Dear Student, The answer to your question is given below -
Write CREATE TABLE statements to implement the following design. Include foreign key constraints. Define the individualID, and GroupID as identity columns. Decide which columns should allow null values, if any. Define Dues column with a default of zero and check constraints to allow only positive values.
Step by step
Solved in 2 steps with 1 images

- Software Engineering: Classes and associations are below the attach picture. I need to draw the Sequence diagram according the steps below: (showing: Message exchanges, Method calls and lifelines of the participating objects) User Registration and Login Sequence: User -> WebApplication: Request to register a new account WebApplication -> User: Prompt for account details (username, email, password) User -> WebApplication: Provide account details WebApplication -> UserAccount: Create a new UserAccount object WebApplication -> UserAccount: Set account details (account_id, email) WebApplication -> User: Notify successful registration User -> WebApplication: Request to login WebApplication -> User: Prompt for login credentials (username, password) User -> WebApplication: Provide login credentials WebApplication -> UserAccount: Validate login credentials UserAccount --> WebApplication: Login status (successful/failed) WebApplication -> User: Notify login…Rule(s) -AGENT can serve multiple CUSTOMERS. AGENT specifically assists CUSTOMERS who are in the same AREA. Given the business rule(s) you wrote , create the basic Crow’s Foot ERD.( that i can visualize, use draw.io or any to illustrate)Sequence diagram Create a UML sequence diagram that will show your clients how the system’s classes will interact when customers are buying their flight tickets on the booking website. How to create your assignment Review the code responsible for adding a new item. Make a sequence diagram that captures the interactions of objects in the app when a new item is added. Your sequence diagram should contain the following classes: AddItemActivity ItemList Dimensions Item And contain calls of the following methods: onCreate() loadItems() saveItem() Dimensions constructor Item constructor addItem() saveItems() Lastly, the activation of AddItemActivity should start with the call to “onCreate()”
- Employee Module a) Timecards (allow recording the attendance and departure of employees). b) Mission and Permission Request. c) Page to approve / disapprove mission and permission request. d) Leave types (Record Types of Vacations) e) Leave Request. with oop javaJob portal system: This system allows the students to search and apply for jobs etc. online. The manager can use the system for posting and deleting job offers etc. 1.Create your own case study (problem statement) for the above application 2.Draw the use case diagram 3.Class diagram with at least 4 classes and explain all the relationshipsSubject : Object Orieted Programming Language Java Netbeans Q: You have been approached by a client to automate inter college event management. The main purpose of this project is to simplify the process of handling each event by providing a web interface for admin, teacher and students. The admin part consists of multiple modules where admin or the authorized person needs to register the college name to create the event by adding the type of event (indoor or outdoor). System allows admin to add teachers who will conduct the particular event activity, which is allotted by the admin itself, also can view the student registration for a particular event and lastly, viewing the results of all events held in college. The teacher part has come up with handling all the event related activity assigned by the admin. Teacher performs various task such as taking the attendance of the students who are registered for a particular event, viewing the list of students to mark the winner of each…
- # Lab 2 ## Scenario Code&Code is a small company dedicated to Software Development. Their engineering team, to which you belong, is working on writing a Web Application as an MVP for a new customer. The code name for this App is “Loggy”, which is meant to offer functionality for a personal journal where users can log their daily activities through text, voice and video. The first step will be to write the main functionality, which is essentially a Microblogging System where all the posts are automatically annotated with voice, video or text. As an initial step, you must create the skeleton of the back-end service for performing the automatic closed captioning under these assumptions: - The closed captioning is performed through an external service (AWS or GCloud). - There should be an internal controller that: - Receives the recordings to be processed from a requester - Sends the recordings to the external service - Receives its response - Updates the recoding with the resulting…Build an organizational chart that accurately reflects the following scenario's data: "The main application calls the getDetails(), calculateFees(), and register() methods (). The calculateFees() module calls the courses() module's course() and courseCost() modules (). Print proof is invoked by the register() module through the printProof() module.1.To find every cell that satisfies the criteria you enter in the Fine and Replace dialog box, you click the Find Next button. Group of answer choices True False 2. Ian has a PivotTable that includes a Product Name column and wants to filter a PivotTable so it shows only product names containing the word "Double." He should apply a Value filter. Group of answer choices False True 3. In the Scenario Manager dialog box, the changing values are the cells that change in the worksheet to show the effect of the scenario. Group of answer choices False True
- Create the Lucky Number application, shown in the “Activity 15 Possible Implementation.” Your project can calculate Lucky Numbers any way you wish, but must include the following features: Two forms, minimum. Each form should have a different title. A programmatically populated control. A control populated based on the selected item in another control. An event that launches the second form. A screenshot of your program running with successful output.Computer Science Pls help me to create the package diagram (uml) for cinema ticket booking system(online and offline) Super Admin: Responsible for adding new movies and their shows, cancelling any movie or show, blocking/unblocking customers, and so on. Admin: Manage all online booking records Ticket counter: Can book tickets. Customer/ Registered member: Can view movie schedules, book, and cancel tickets. Guest: All guests can search movies but to book seats they have to become registered members. System: Mainly responsible for sending notifications for new movies, bookings, cancellations, etc.Scenario: Mr. X works in a large consulting company with multiple operations. Mr. X is a Software engineer who has recently developed an application which helps users keep track of medical information, doctor’s appointments, and prescriptions. Information about the user is stored in this application, including what prescriptions they are taking and how frequently they schedule doctor’s appointments. As the developers of the application, X and his software development team have access to this information. The application is in use by thousands of users. The marketing department of X’s company requests that X supplies them with customer-specific information so they can better target advertisements and other application suggestions to the users. X understands that he is part of a company, but also feels that the privacy of the application users should be protected. Additionally, X feels that as a software engineer, he should be responsible to those who use his technology. Analyze the…

