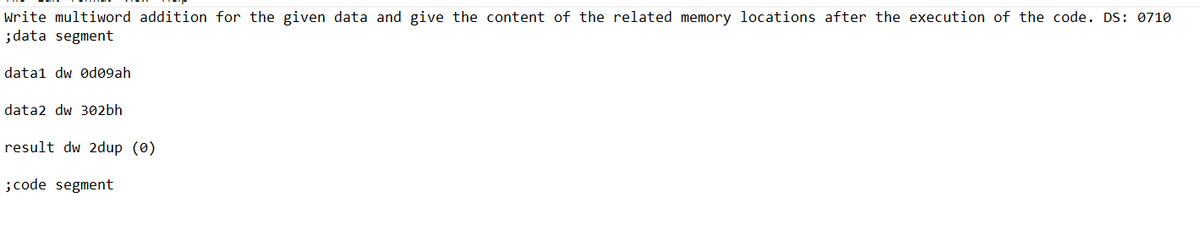
Write multiword addition for the given data and give the content of the related memory locations after the execution of the code. DS: 0710 ;data segment datal dw 0d09ah data2 dw 302bh result dw 2dup (0) ; code segment
Q: Write a program that lets the user play the game of Rock, Paper, Scissors against the computer. The…
A: ALGORITHM : Step 1: StartStep 2: Welcome the player to the game.Step 3: Explain the rules of the…
Q: Write a note on Schema of DTD.
A: A document type definition, or DTD, is one. An XML document's structure, legal components, and…
Q: In the URL "http://www.u.arizona.edu/~wtn", what part of the URL defines the hosting server?…
A: The components of a URL are:- Protocol Host name or hosting server Path Query string
Q: Why is it that the central processing unit (CPU) is the most important part of a computer?
A: Central processing unit (CPU): The most crucial part of a computer system is the Central Processing…
Q: Define What Is Emergency Repair Disk (ERD)?
A:
Q: I did not ask for a the output on a GUI. I need lines
A: I attached your answer above.
Q: Defend the use of firewalls as a means to protect the privacy and security of your network. To…
A: Firewalls : A firewall is a network security system that monitors and controls the incoming and…
Q: Define What is XML.
A: Please check the step 2 for solution
Q: It is essential to have a good understanding of the function that the internet, intranets, and…
A: We need to talk about the role that intranets, extranets, and the internet play in today's…
Q: How has the development of computer security's key components over time shaped the field as it…
A: The protection of computer systems against theft or damage to their hardware, software, and data, as…
Q: if you upload a picture of a handwritten answer, please make sure it's legible. Please only…
A: The Assembly Language for x86 Processor focuses on programming microprocessors compatible with intel…
Q: O Using the Customer database (Customer Database has one table Customer), Create Class Library…
A: Step 1To create a DatabaseTo build the "CoreMvDB Database," open your SQL Server with the following…
Q: Write Features of DTD.
A: The XML Document Type Declaration, commonly known as the DTD, is a way to describe the precisely the…
Q: Which of the following is the full filename that should be used for your EC Hosting assignment in…
A: The name of the file should be always index. Thus, option 2 is wrong. The name of the file should…
Q: This is the code I have, I need to change it to a menu driven option:
A: Description The task is to convert the given program to a menu-driven program containing the…
Q: What is the procedure for an evildirect wireless attack? Do not rely on handwritten notes.
A: EvilDirect may be created by setting a rogue GO to use the same channel, MAC address, and SSID as a…
Q: Write a note on internet and external DTD. Typed answer only
A: The Document Type Definition (DTD) describes the vocabulary and the structure of an XML document.
Q: When creating a website, what factors should be prioritized the most?
A: Website: A website is defined as a collection of web pages and other information that is linked…
Q: Please help me make a a t square fractal using recursion. if you can please also make a sierpenski…
A: According to the information given:- We have to make a a t square fractal using recursion, make a…
Q: Social media has made it possible for people of all ages to keep in touch with loved ones,…
A: Social engineering attacks utilise psychological tricks to trick unwary users or workers into…
Q: In other words, "Could you provide a summary of Classical optimization strategies?"
A: CPU scheduling is a method that lets one process use the CPU while another's execution is put on…
Q: There are several potential methods for launching a denial-of-service attack against regular email.…
A: Introduction: A denial of service (DoS) attack is a kind of cybercrime in which many computers are…
Q: Working with Digital Circuits Consider the function: F(x,y,z) = xy+z'. a. Draw the logical diagram…
A: The question is solved in step2
Q: What exactly is the speed of a computer's clock?
A: - We need to talk about the clock speed of a computer.
Q: 3.3 Let's say we have an array of length X+1. How would we define array[x]? or What is array[x]…
A: given that: we have an array of length x+1 so, index values to access the elements of array are in…
Q: For those who may be unfamiliar, what precisely is an intrusion prevention system?
A: INTRODUCTION: System for preventing intrusion (IPS) A network security system called an intrusion…
Q: How to create a frame in HTML? Explain with example.
A:
Q: E B F A C G ZO J K L M N D H O PR
A: Solution Breadth First Search BFS BFS is a graph traversal algorithm that start traversal from…
Q: Different methods of multithreading are tried out on various OSes (Linux, Windows, Mac, Android,…
A: Multithreading techniques in Linux/Windows/Mac/Android/etc. are contrasted for uniprocessor and…
Q: Discuss the nature of offline password attacks. Specify TWO (2) distinct approaches to launching…
A: Introduction: When a password is generated on a computer, the hash form of the password is saved.…
Q: Practice Assignment Ch. 9-1 1. 2. 3. 4. 5. ➤ > Classroom Sections: Group assignment - break into…
A: Description The following program extends Practice 1 to include two more functions: The two…
Q: Suppose we have a benchmark that executes in 100 seconds of elapsed time, of which 90 seconds is CPU…
A: To find how faster will program run at the end of six years.
Q: ) Suppose I have a system which uses 16-bit virtual addresses and 1Kb pages. How many logical pages…
A: Here in this question we have given two questions and give that virtual address is 16 bit Page size…
Q: What are some of the distinguishing features that set a computer apart from other types of…
A: The question is solved in step2
Q: How does the primary key of a relation relate to the interdependencies among its other attributes…
A: Answer: A primary key-foreign key relationship characterizes a one-to-numerous connection between…
Q: Differentiate between HTML and XML.
A:
Q: The program, however, must have: • Two extra functions besides "main" (or whatever you call it) • At…
A: ALGORITHM OF THE CODE : 1. Start 2. Read in a list of numbers from a file. 3. Sort the list using…
Q: Explain what is Ipsec tunneling, how it works?
A:
Q: In the realm of relational databases, how does Oracle stand out from the crowd?
A: recursive databases: It is based on the relational model, which makes use of set theory in…
Q: Can you explain the inner workings of an IDS?
A: Firewall: An internal network is protected against unauthorised servers and networks using this…
Q: How many steps are required to make a website? Give reasons and explanations for everything you do.
A: How many steps are required to make a website? A website must be designed in seven steps: Goal…
Q: As described by the UofA's Autonomic Computing Lab, which of the following would NOT be commonly…
A: Decision making Decision making would not be considered as being one of the challenges for the…
Q: Give me a definition of the term "intrusion prevention system," please.
A: "intrusion prevention system," An intrusion prevention system (IPS) is a network security tool…
Q: The smallest functional unit of an ATM system is a virtual circuit. How?
A: Introduction: Determine which ATM virtual circuit is the smallest unit. Asynchronous Transfer Mode…
Q: (Python)Fill in the first blank with a Boolean expression so that after the loop executes, the…
A: Here is the explanation regarding the expression:
Q: 3. (Greedy, DP) Consider the 0-1 Knapsack Problem: Given weights and values of n items, put these…
A: Algorithms: START A Dynamic Programming based solution for 0-1 Knapsack problem Create a class…
Q: Tablet computers are distinct from other kinds of computers in a number of important respects.
A: There is a wide variety of ways in which the tablets and the computers are not equivalent to one…
Q: Full explain this question and text typing work only We should answer our question within 2…
A: In step 2, I have provided answer with brief explanation.....
Q: 2. Use case diagram
A: According to bartleby guidelines we are supposed to answer only one question so the 2nd one, use…
Q: demonstrate to you how the insertion sort works. Type up the code and submit the output only.…
A: The answer is given below.
\\
Step by step
Solved in 5 steps with 3 images

- . (True/False): A segment selector points to an entry in a segment descriptor tableARRAY ADDRESSING Determine the address of the given array. char = 1 byte; int = 2 bytes; float 4 bytes; double = 8 bytes. show your solution and explain. thankss struct record{char name[25];int qty;float price;double total;} rec[15];Address of rec[3].qty = 2000Given that X is a double number array starting at location 100, ptr is a pointer to X, and each double is stored in 8 bytes of memory, what location does ptr + 1 point to? 100 101 1004 108
- A pointer that contains the address O is called a(n) ____ pointer .Define an array of ten pointers to floating point numbers. Then read ten numbers into individual locations referenced by pointers. Add all of the numbers and store the result in the pointer-referenced location. Display the contents of all locations.Numbers between 0 and 15 are stored in the memory location starting from physical address B000Fh randomly. Write a program which finds the element order number in the string starting from 0 to 15 and writes to physical address C000Fh. (Eg: "1" is 2nd element in the first string, "2" is 4th element, ....etc)
- C++ ARRAYS 3. Population In the Lithuanian register, the personal identification code data of the population is stored in the format SYYMMDDXXXX. Here: S- Gender: 3 (male, 1900-1999), 4 (female, 1900-1999), 5 (male, 2000-), 6 2000-), YY is the last two digits of the year of birth (00, 01, 02, 03, MM - month of birth number (01, 02, 03, ... 11, 12), DD - number of the date of birth (01.02, 03, ... 30, 31), XXXX - registration number (0001 ... 9999). Make a program that will find the dates of birth of the eldest Lithuanian man and woman and display them on the screen. The first line of the source data file contains the personal codes n (1 <n < 3000). Next, each line contains one code.Multiple key-value pairs, each representing a hotel room number and current temperature, are read from input and added to room_temperatures. In sorted order of the keys, output each key-value pair that has a value less than 70.0. Begin each output with the key followed by the value, separated by a space.Please include steps and comments. Starter Code: title Title of Program (skel.asm) .model small ; one data segment, one code segment.stack 100h ; reserves 256 bytes for the stack.386 ; for 32 bits.data ; start definition of variables ; your variables go here .code ; start code portion of programmain proc ; start of the main procedure mov eax,@data ; load the address of the data segment into eax mov ds,eax ; load the address of the data segment into ds ; the two previous instructions initalize the data segment ; your code goes here ; the following two instructions exit cleanly from the program mov eax,4C00h ; 4C in ah means exit with code 0 (al) (similar to return 0; in C++) int 21h ; exitmain endp ; end procedure end main ; end program
- What does it mean to say that an address variable is a pointer? In what context is it employed? A dynamic array is an array of constant data. A dynamic array has a relationship to pointers in that it can both contain pointers and have pointers as elements.Given the declaration below, if array aData[][] was associated to the memory location 1010 (in decimal), what is the value/address (in decimal) equivalent to aData[5] ? double aData[6][4]; Note that sizeof(double) results to 8, meaning 8 bytes.Why is it important to distinguish between data types having a static length and those with a dynamic length?

