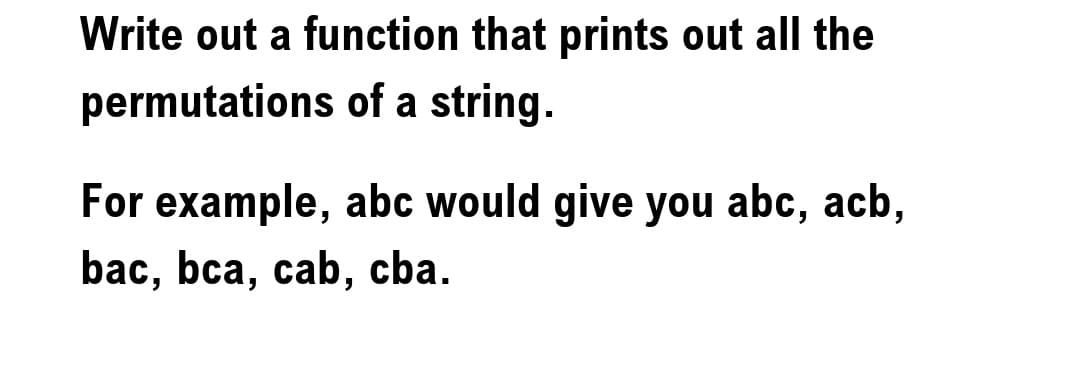
Write out a function that prints out all the permutations of a string. For example, abc would give you abc, acb, bac, bca, cab, cba.
Q: What stages are involved in modelling completely distributed systems?
A: Introduction:Here we need to give the steps involve in the fully distributed system modeling.
Q: What are the most important tasks that an operating system must do on your behalf computer?
A: The above question is answered in step 2 :-
Q: A very successful cinema director named "Chef" decided to solve the problem. When a customer wants…
A: Input - Output Defination: Input begins with an integer T: the number of test cases.Each test case…
Q: identify, characterize, and discuss non-technical cyberattacks
A: Non-technical cybersecurity assaults are defined and explained: Non-technical attacks do not need a…
Q: What are the three tools used for system development in system analytics?
A: Introduction: The evaluation of a system or its components to establish its aims is known as system…
Q: In what ways does cloud computing have an edge over on-premises solutions? What are the cloud…
A: The following are some advantages of using cloud computing: 1. A decrease in the expenses of IT.2.…
Q: You've been given the duty of reviewing an online reservation and ticketing system for trains. What…
A: Introduction: The system development life cycle is a method of project management that lays out the…
Q: Why are chrome Extensions not appearing on a device?
A: Introduction: The number of extensions available in Google Chrome is one of the reasons it is the…
Q: What are the numerous inputs and outputs of the software system design process that should be…
A: System design is the most common way of designing the elements of a framework, for example, the…
Q: Not-OR Statement s1 && s2 && s3 s1 || s2 || s3 ! (s1 && s2 && s3) ! (s1 || s2 || s3)
A: The correct answer for the above question is 4. ! (s1 || s2 || s3)
Q: What kind of long-term effects does a data breach have on the security provided by the cloud? In…
A: The Answer is in given below steps
Q: The only way to start debugging was to hit "F5" or click the "Start Debugging" button. Visual Studio…
A: Introduction: In order to debug, you will need to start your application using the debugger that is…
Q: Assume that you are using the fixed route, and then attempt to send a packet to a host using it. a…
A: Interdiction: When we talk about delays, we're referring to the amount of time that passes before a…
Q: mmarise the Waterfall Systems Development paradigm as follows: What is the difference between this…
A: Introduction: Below describe the difference between Waterfall Systems Development and the Agile…
Q: - Computer science : How does the system detect thrashing? Once it detects thrashing, what can…
A:
Q: Ques, exxplain Gomaric nic class with multiple type parameter by a jane programe?
A: A generic class is a class with items and functions that can be generalized by T parameter that…
Q: What controls, integrates, and manages the physical components of a computer?
A: Introduction: When we talk about the actual physical components of a computer, we are referring to…
Q: Consider the topic of infrastructure sharing in mobile telecommunications networks briefly.
A: Answer: Infrastructure Sharing Among Mobile Telecommunication Networks: Mobile telephony has been…
Q: What affected your choice to quit Facebook because of its huge privacy issue?
A: Introduction: Your Facebook games and apps are not as harmless as you may believe. Facebook permits…
Q: What type of implications may a data breach have for the safety of information stored in the cloud?…
A: Given: Database corruption, leaking of confidential information, intellectual property theft, and…
Q: Is there a relationship between the system life cycle and the system development methodology?
A: System Life Cycle and System Development Methodology: The systems development life cycle (SDLC) is a…
Q: The daily demand for interior paint cannot exceed that for exterior pain the maximum daily demand…
A: Given that, Raw material- exterior- 6,1 Raw materia- Interior- 4,2 Profit- 5,4 Availability- 24,6
Q: The incoming and outgoing traffic, the database, the rules, and the authentication of domain logins…
A: Deification: One of your computers functions as a domain controller if you utilise Windows Server…
Q: What kind of goal(s) do you have in mind when it comes to putting Excel's features to use?
A: Answer: MS Excel is an ordinarily utilized Microsoft Office application. It is a bookkeeping sheet…
Q: Are there any benefits to using pure functions, and if so, how?
A: Given: An important benefit of pure works is that they don't have any negative side effects. When…
Q: The static data members and static member functions aren't quite what I'm going for in this…
A: Explanation: Both C and C++ make use of the term "static" in their respective programming languages.…
Q: When designing a software system, what are the unique inputs and outputs of the process?
A: The answer of the question is given below
Q: LANs and physical cabling
A: Given :- In the above question, the statement is mention in the above given question Need to write…
Q: A fingerprint reader, rather than a username and password, is the new way that your organization…
A: A fingerprint reader is a device that identifies a person's fingerprint and can be used as an…
Q: What kinds of equations call for the use of numerical approximation as a solution?
A: Answer: As computer capabilities have risen, the application of realistic mathematical models in…
Q: wo strings "ABNJKLYUOP" and "ABTRLYIGP", What is the length of long
A: Lets see the solution.
Q: Useful when you need to identify yourself but don't want to use a credit card or an ATM. The…
A: Several steps are taken to safeguard your safety at the ATM. The following are precautions to take…
Q: A very successful cinema director named "Chef" decided to solve the problem. When a customer wants…
A: Process for the code: Firstly we will take input for the number of test cases. After that we will…
Q: Only one-third of IBM's sample of 585 mobile app developers and managers were successful in meeting…
A: Explanation: The deadlines are very important for a team to fulfil in order to maintain the spending…
Q: What is cyber security's purpose?
A: Introduction: The end goal of any cybersecurity effort should be to prevent the loss of data or its…
Q: A fingerprint reader, rather than a username and password, is the new way that your organization…
A: Reader of fingerprints: Instead of typing a user name and password, a fingerprint scanner is a…
Q: What exactly is the purpose of possessing them?
A: Answer: A function is a collection of instructions that must be followed in order to successfully…
Q: Do research on the iOS and Android Operating system. From that research, share the similarities and…
A: Similarities 1. Simple Application Installation It is exceptionally simple to introduce an…
Q: 1. Name the advantages of optical fiber over twisted-pair and coaxial cable.…
A: Below are the advantages of optical fiber over twisted pair and coaxial cable:- Speed Optical fibres…
Q: What is type casting? Explain implicit and explicit type conversion with example.
A: Given Question: Explain type conversion and differentiate between implicit and explicit type…
Q: network has
A: Answer ) LAN option c
Q: A for-loop can have multiple index values. O O
A: A loop is the sequence of the instructions that can be repeated continuously until the condition is…
Q: 2. Write a program that determines the class of a ship depending on its class ID. Class ID Ship…
A: The C program to determine the class of a ship depending on it's class ID is as follows.
Q: Why don't you write a letter on how you feel about the software testing that has been done?
A: Launch: Software development takes place in many stages, but the programme testing step that follows…
Q: Define the instance and local variables.
A: A variable is a name given to a memory area. It is the essential unit of capacity in a program.…
Q: What kinds of equations call for the use of numerical approximation as a solution?
A: Explanation: As computing power has risen, so too has the necessity for more precise numerical…
Q: Could you kindly describe what occurred during the data breach that was recently made public using…
A: Introduction Data breach: A data breach occurs when a hacker gains unauthorized access to and…
Q: To what degree is it feasible to define a digital signature, and if this is the case, how does the…
A: Given: Digital signatures are electronic "fingerprints" that securely connect a signer with a…
Q: computer science - Six characteristics determine the quality of data.
A: Introduction: The Quality Of The Data Is:
Q: A: write a C++ program that read the number and compute its factorial, Use while statement to create…
A: the factorial of a non-negative integer n, denoted by n!, is the product of all positive integers…
Step by step
Solved in 2 steps with 1 images

- Write a function to find out longest palindrome in a given string?Write a function that replaces a substring with a new string. Example: >>> replace('The quick brown fox jumps over the lazy dog', 'quick', 'slow') The slow brown fox jumps over the lazy dog The first parameter is the string, second is the substring to be replaced and the third is the string to replace the substring. If there are more than one occurrence of a substring, replace it all.write a program in C++, to read a string (M[10]) ,send it to a function (My F()) that finds: 1."NL" number of lowercase letters. 2."NU" number of uppercase letters. 3.Change lowercase letters to uppercase letters. 4.Change uppercase letters to lowercase letters. In the same function. (NOTE: using Pointer).
- Write a function that takes a string representing the binary representation of a number, computes the number in decimal and returns this value. The string consists of "." and "-" characters, where "." represents 1 and "-" represents 0. For example, ".--.." corresponds to 10011, which is equal to 1 * 16 + 0 * 8 + 0 * 4 + 1 * 2 + 1 * 1 = 19. So the function returns 19 for an input of ".--..". """Write just the function separate(String s) and write it in JAVAWrite a function in Python that determines if any string of any length is a palindrome. Be as efficient as you can.
- Write the code in python to define a function has_repeat(mystr), which takes a string parameter and returns a boolean result. - If mystr has a character that is repeated (count is more than 1 for that character), return True - Otherwise, return False Hint: You can solve this problem by iterating over the characters in mystr and comparing each character's count with 1. For example: Test Result print(has_repeat("Happy")) True print(has_repeat("sad")) False print(has_repeat("salmons")) True print(has_repeat("Trouts")) FalseWrite a function for a simple game for two players that will generate a random 4 digit number (not greater than 4 digit not less then).Write a Python function that takes a sequence of characters and determines if there are any pairs of characters that are not adjacent to each other by returning True if there are any pairs, or False Example: The string “abbot” would return False because the two b’s are adjacent to each other while the string “abba” would return True because, even though the two b’s are adjacent to each other, the two a’s are not.
- Implement the following function which accepts a string as parameter and reverses it, without using any function from the string library. void strReverse(char *str)Write a function that takes 2 strings, word1 and word2 as parameters. The function must return if,starting from word1, by only deleting some characters you can get word2.Write a function hasBothCases that takes a a c-string and determines if it contains both the upper and lowercase forms of a letter, returning 11 if both the upper and lowercase form of a letter are part of the string and returning 00 if no such letter exists. For example, hasBothCases should return 11 for the strings "Nine", "Lowell", and "o_O", but should return 00 for "nine", "Massachusetts", and "zyBooks". HINTS: You can make use of either the following: (1) Assume that the <ctype.h> library has already been #included. 2) Upper case letter A starts at 65 and Upper case Z is 90 in ASCII code, while lower case a starts at 97 and z is 122. NOTE: You only need to write the function. In C programming

