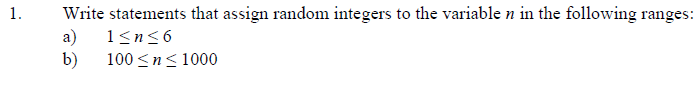
Write statements that assign random integers to the variable n in the following ranges:
Q: Write a program that asks a user to input the height of triangle and draw a triangle thát has the To...
A: According to the Question below the Solution: Output:
Q: One among several diagram supported by UML is Use Case Diagram. Please mention and explain other dia...
A: We are attaching images of the UML diagrams for both marketplace system ticketing system
Q: How do you make sure that each computer using IPsec has its own private key pair?
A: Digital Certificates allow us to verify that any machine connected to the Internet has its own uniqu...
Q: Users may use shared memory on multiprocessor systems. In clusters and grids, these types of operati...
A: Introduction: The relative time it takes for their processors to access the shared memory blocks dis...
Q: Explain the Enterprise Resource Planning life cycle in detail?
A: Lets see the solution.
Q: atn -3m b) x(t) -6 -3 -2 3 4 6 9.
A: Matlab code for Fourier Seriesclear allclose all%Question a.%function for which Fourier series have ...
Q: We have 100 critics who have rated the top movie of the year: Enchantio! Write a C++ program that l...
A: Given ratings 99, 76, 54, 67, 91, 86, 92, 94, 53, 93, 91, 98, 67, 93, 90, 64, 51, 56, 62, 56, 71, 80...
Q: The cloud is protected by using the shared responsibility model and managing identity access (IAM).
A: Cloud security contrasts in light of the classification of distributed computing being utilized. The...
Q: is this statement true? When outliers are important then it is important not to change the current m...
A: answer is
Q: Describe benefits of REST over SOAP.
A: Ans : The benefits of REST over SOAP IS: 1) REST allows a best variety of data formats where as SOA...
Q: List all possible relations on the set {0,1} and determine which of these relations are (a) reflexiv...
A: To list all possible relation on set {0,1} and determine reflexive, symmetric, antisymmetric and tra...
Q: What exactly is a random access technique, and which two protocols come within it?
A: Intro Random Access technique: Random access technique is otherwise called dispute strategies where...
Q: computer science -What are your knowledge about Pro/Engineer software and its applications in Mechan...
A: Introduction: Professional/Engineering software: PTC Creo, formerly known as Pro/ENGINEER, is 3D mod...
Q: Q2: The signal-to-noise ratio in decibels. SNR = 36 and the channel bandwidth is 4 MHz. Compute The ...
A: 2. It is given that the signal to noise ratio in decibels. Bandwidth = 4 MHz = 4 * 10 6 Hz SNR dB = ...
Q: Default value of for loop range function start is 0? Select one: O True O False
A: INTRODUCTION: Here we need to tell the default value of for loop range function start is 0.
Q: List and explain four (4) or more reasons why the online payment method is important.
A: Online payment allows for cashless payments for goods and services through cards, mobile phones or t...
Q: Provide at least five rules for the knowledge base and one fact for working memory in a topic where ...
A: Introduction: The data received from the user during the expert system session is stored in working ...
Q: Describe five different types of network topologies. Which one do you believe is the most trustworth...
A: Intro It is the manner in which computer systems or network devices are linked to one another that i...
Q: create tauth table and X-map. F(x) Y,Z) =XY+Z
A:
Q: b) x(t) -6 3 4 6 . -3 -2
A: Matlab code for Fourier Seriesclear allclose all%Question a.%function for which Fourier series have ...
Q: What advantages does a file system website have over a website that uses the http protocol?
A: Introduction: This query is based on a comparison between the file system and the http protocol. The...
Q: Design and create the needed tables (minimum four) with suitable constraints.
A:
Q: What other issues are linked with the nondatabase method to data processing besides redundancy?
A: Introduction: If the file system or any non-database strategy is utilised to store the data instead ...
Q: Discuss the five most critical security characteristics of a software-as-a-service-based business mo...
A: Introduction: A business model based on software-as-a-service: Software as a Service (SaaS), often k...
Q: In the array declaration 'i' denotes that integer values will be stored in the variables. Select one...
A: in the array declaration i denotes that integer values will be stored in the variables explain below
Q: Write the structure of the tables used in the database from the website (Customers, Categories, Empl...
A: I am just giving the sample values in the table. Query for creating Table:- CREATE TABLE Customers( ...
Q: Is it allowed to use a virtual address A?
A: -The services provided by a virtual address are available for any individual or a registered busines...
Q: Discuss some of the ways through which green computing can be achieved.
A: Green Computing Green computing is the use of computers and their resources in an environmentally s...
Q: For an optimization problem which of the following is/are the property/properties that must hold for...
A: For an optimization problem for a greedy algorithm to work there are two conditions. 1. Greedy - cho...
Q: In networking, what are the three types of autonomous systems ?
A: Introduction: Autonomous systems are classified into three types:
Q: In a memory block, what does address space imply?
A: Introduction: The memory block comprises the block of addresses requested by the process, as well as...
Q: WHERE CAN I FIND A WEB DATABASE APPLICATION?
A: Intro Web Database Application A Web database is a database that can be administered and accessed v...
Q: Which of the following statements about the Vigenère cipher are TRUE? Select all the answers you thi...
A: Vigenere Cipher is a ploy alphabetic substitution cipher where we have a key repeating for making th...
Q: What other variables may be changed to keep the page size the same (and so avoid software rewrite)? ...
A: Introduction: To maintain the same page size, the following factors were altered:
Q: The cloud is protected by implementing a shared responsibity model and implementing identity access ...
A: Introduction: We use cloud technology to the access virtual space and the internet. Some people mis...
Q: How have media and technology been used in the classroom?
A: Introduction: The widespread availability of student databases that can track individual progress, t...
Q: Distinguish between application virtualization and virtualization of applications.
A: Introduction: Virtualization, as the name implies, is a programme that enables several operating sys...
Q: // This main method provides code to run tests on the play() method. // You are free to add c...
A: import java.util.LinkedList;import java.util.ListIterator; public class WordGamePlay { public sta...
Q: When you open a photo and then resize the frame, what happens? What if you resize the frame first, t...
A: Introduction: To resize an image file or its output. This may or may not include altering the file...
Q: What is the status of technology now, as well as the many types of technical systems?
A: Introduction: We live in the twenty-first century, and technology is at its pinnacle. New artificial...
Q: What words would you use to describe the router's boot-up procedure?
A: Introduction: A router is a piece of networking equipment that links two or more packet-switched net...
Q: Ethernet has remained the most used LAN technology. What are the four (4) Ethernet features?
A: Introduction of Ethernet: Ethernet is the wired technology of computer networking and it was standar...
Q: What exactly does the term "Speech Recognition" mean?
A: Introduction: We can express what we can accomplish by speaking solely to our gadgets thanks to spee...
Q: Write a Scheme function that computes the mean of a simple list of integers. For example, the functi...
A: In this question we have to write a scheme functions to find the mean of the list of integers. For m...
Q: What exactly is the meaning of an adapter class?
A: Introduction: Adapter class Adapter classes offer the default implementation of listener interfaces ...
Q: Consider the following set of processes, wit given in milliseconds: Process Burst Time Priority P1 7...
A: We are going to use priority based scheduling for scheduling the jobs, for ex. Process 3 has the hig...
Q: How to encode a TM in binary
A:
Q: Suppose you are transferring 1000 from account A to B and the current balance of A is 3000 and B is...
A: Introduction Suppose you are transferring 1000 from account A to B and the current balance of A is...
Q: What is the output of the following program? void display(int n) {if (n<10) {display(n+2); cout ...
A: Here there is a void function called display having integer as parameter. According to the given que...
Q: What is a multidimensional array and how does it work?
A: Introduction: Rows and columns represent the two dimensions in a matrix. The row index and the colum...
In C
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Show the value of x after each of the following statements is performed:a) x = fabs(7.5);b) x = floor(7.5);c) x = fabs(0.0);d) x = ceil(0.0);e) x = fabs(-6.4);f) x = ceil(-6.4);g) x = ceil(-fabs(-8 + floor(-5.5)));Write statements that assign random integers to the variable n in the following ranges:a) 1 ≤n ≤2b) 1 ≤n ≤100c) 0 ≤n ≤9d) 1000 ≤n ≤1112e) –1 ≤n ≤1f) –3 ≤n ≤11If int x = 10;, int y = 7;, double z = 4.5;, and double w = 2.5;, evaluate each of the following statements, if possible. If it is not possible, state the reason. (3, 4) (x + y) % x x % y + w (z - y) / w (y + z) % x (x % y) * z x % y % 2 (x + y) % z (x % y + z) / w
- 2- Number of basic operations of the following statement is equal to : for ( int i = 0 ; i< = 1 ; ++i) System.out.println( "X+1"+"Y"); A- 5 B- 6 C- 7 D- NoneTell if the statements are true or false. Let p: 2 + 1 = 3; q: 16 − 9 = 7. (a) ~p ∨ q TrueFalse (b) ~p ∧ ~q TrueFalse (c) ~(p ∧ q) TrueFalseWrite C++ statements that accomplish the following. Declare int variables x and y. Initialize x to 25 and y to 18. Declare and initialize an int variable temp to 10 and a char variable ch to 'A'. Declare and initialize a double variable payRate to 12.50 Copy the value of an int variable firstNum into an int variable tempNum Declare int variables to store four integers.
- Given the following statements:int num;int *numPtr;write C++ statements that use the variable numPtr to increment the value of the variable num.30 Suppose a, b, and sum are int variables and c is a double variable. What value is assigned to each variable after each statement executes? Suppose a = 6, b = 3, and c = 2.2. (14) a b c sum sum = static_cast<int>(a + b + c); __ __ __ __ b += c * a; __ __ __ __ c -= a; __ __ __ __ a *= 2 * b - c; __ __ __ __State whether true or false. The following code will throw an error: double a = 2; double b = 3; int c = a * b;

