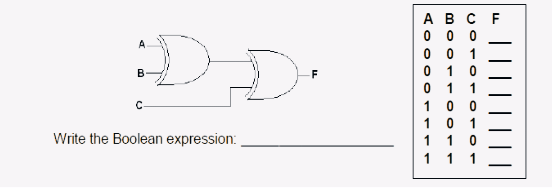
Write the Boolean expression:
Q: To what end does issuing the tracert command lead? Why is it helpful to utilize the trace route…
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: How many rows are there in a truth table with 4 variables
A: Here, we have to calculate how many rows are there in a truth table with 4 variables. Let's solve…
Q: What exactly is a ForkJoinTask? Just how dissimilar are RecursiveAction and RecursiveTask?
A: ForkJoinPool-specific base class for assignments. ForkJoinTask are lightweight strings. Few…
Q: List and briefly discuss the many approaches that enable an operating system to consider multiple…
A: In this question we have to briefly understand multiple approaches that will enable OS to have…
Q: explain the various mapping algorithms used for caching data?
A: Can you explain the various mapping algorithms used for caching data?
Q: In what ways has "street view" on Google Maps been put to use in the business world?
A: Google Street View has been put to use in various ways in the business world. Some of the…
Q: In this screenshot, a Windows 10 user is using the File Explorer to move a file from the C:data…
A: Windows supports FAT32 and NTFS file systems. To manage access to folders and files, NTFS allows…
Q: Analyze the repercussions that game-changing web applications have on our culture.
A: Web applications that change the game have extensive and intricate effects on our culture. On the…
Q: The instruction to "brush your hair five times" most closely resembles which of the following…
A: Dear Student, The detailed answer to your question is given below -
Q: function in C using nested for loops?
A: #include <stdio.h> #include <stdlib.h> void clearScreen() { // implementation of…
Q: What are the four most important record kinds to check for when dealing with SSL protocols? Where do…
A: The SSL protocols provide four distinct kinds of records: HTTPS record protocol. Handshake customs.…
Q: How would you define strings?
A: In computer programming, a string is a sequence of characters. Characters can include letters,…
Q: Create an ordered list-using variant of the ProgramOfStudy software. Place the classes in ascending…
A: In this modified version of the software, we define a Class struct that contains fields for the…
Q: applied disreet maths if |A| = n and f: A--->B is injective, what is |f(A)|?
A: What is injective: In discrete math, a function f: A → B is said to be injective (or one-to-one) if…
Q: Create a GUI application named OddNumsGUI displays all the odd numbers from 1 through 99 when the…
A: Programming Approach: Choose a programming language and GUI framework/library: You can choose any…
Q: Please provide a succinct summary of each method used to evaluate HCI. Usability testing Formative…
A: HCI means Human Computer Interaction. Human-machine interaction (HCI) is the design and research of…
Q: Can a MAC address be shared by several network interfaces? So why is this happening, or why isn't…
A: The answer to this query depends on the IP address and network interfaces of the machine. Let's…
Q: The basic concepts and workings of mobile phones, as well as their various iterations and…
A: Cellular phone basics includeRepetition Access methodsSpeech coding Mobility Ciphering Network…
Q: DNS poisoning attacks need to use spoofed source IP addresses for the forged DNS responses sent to…
A: Dear Student, The answer to your question with detailed explanation is given below -
Q: How does k-means clustering work in RapidMiner (RM) and how does it work in Tableau?
A: According to the information given:- We have to define how does k-means clustering work in…
Q: Analyze the repercussions that game-changing web applications have on our culture.
A: In this question we have to Let's understand and hope this helps if you have any queries utilize…
Q: What does Open Daylight's service abstraction layer provide for in its SDN controller?
A: Open Daylight SDN controller: The Open Daylight controller is an open-source and free project that…
Q: Where can you get the software required to set up IPsec between two computers?
A: IPsec can be configured with Windows Firewall between two computers if they both have it installed.
Q: The DiskPart application is unfamiliar to me, so please walk me through its usage.
A: Introduction to command line: The command line, also referred to as the command-line interface,…
Q: In functional programming languages, list use is commonplace. For what reason is this happening?
A: In functional programming languages, list use is commonplace because lists are a fundamental data…
Q: eral users are having login issues after the password change. This issue has been reported to a…
A: The term "Domain Controller" refers to a specific kind of server machine that is hosted by…
Q: The question is, in what way are data structures like arrays, lists, stacks, queues, and trees…
A: In this question we have to understand about the ways data structures (arrays, list, stacks, trees…
Q: You're the Systems Administrator at AngloGold Ashanti. Your server's performance has been lagging…
A: As a Systems Administrator at a company, one should understand the importance of ensuring that…
Q: The information systems project manager is at a loss as to which system development approach to use.…
A: This is a computer science question related to software development methodologies. As a project…
Q: In this screenshot, a Windows 10 user is using the File Explorer to move a file from the C:data…
A: Both the FAT32 and NTFS file systems are supported by the Windows operating system. Access to…
Q: When I turn on the router, what do I need to do?
A: The following is the router boot-up procedure: Activate the router's power. From the ROM, the…
Q: Scenario window writing ability? Or Tell me your method for testing the application's login…
A: Scenario window writing ability and method for testing the application's login functionality or how…
Q: Tell me the difference between Scenario and Use Case and Test Case? Or difference between Scenario…
A: Introduction: Both scenarios and use cases are general representations of a system's operation. A…
Q: Identify, describe, and define the six parts of an information system you just learned about.
A: Information Technology (IT): The term "information system" refers to any system that is used to…
Q: 1. Evaluate the postfix expression using stacks. 7 4 -3 * 1 5 + / *
A: “Since you have posted multiple questions, we will provide the solution only to the first question…
Q: Please provide a succinct summary of each method used to evaluate HCI. Usability testing Formative…
A: HCI: Human-Computer Interaction (HCI) is the study of how people interact with computers and other…
Q: What are the four most important record kinds to check for when dealing with SSL protocols? Where do…
A: Answer is
Q: By using the routing protocol, how many new networks have been found?
A: In order to make routing choices, routers rely on routing protocols, which facilitate the…
Q: Which technologies are used to set up a VPN, and what exactly is a VPN?
A: Private Network: A private network is a computer network that is restricted to a…
Q: Which one of the following domains is the most effective one when the Ox20 method is applied?…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: What precisely does it mean to "choose numbers at random," though?
A: The term "random" is used to represent the selection of an item, number, amount, or other attribute…
Q: cript please mat
A: The question asks to write a script in MATLAB that will print a multiplication table. Specifically,…
Q: (a) Describe the structure of a complete binary tree of height h with maximum number of nodes.…
A: (a) A complete binary tree of height h has the maximum number of nodes when all levels are…
Q: Please name and describe two (2) critical functions served by routers in today's computer networks.
A: One or more packet-switched networks or subnetworks can be connected using a router. By sending data…
Q: 3. Create a script that will find the average of {-100, 97, 83, 21, -50, 20, 101, 30}. [THE USER…
A: In this script, we first prompt the user to enter the size of the array and store it in the size…
Q: 4. Select all that apply: given str is a variable containning a literal string, which of the…
A: The above questions cover various aspects of working with strings in Python. They involve string…
Q: Identify, describe, and define the six parts of an information system you just learned about.
A: What is Information system: An information system is a combination of hardware, software, data,…
Q: In depth system failure explanation needed for computer security risks.
A: System failure refers to any situation in which a computer system is unable to perform its intended…
Q: In this paper, we will examine Disney World's usage of MagicBands and how they fit into a larger…
A: Here is your solution -
Q: What does a router do in a network setting? Give at least four key distinctions from a switch.
A: Routers send data streams based on their IDs. They're used for Internet access, network linking,…
Problem solve:-.
Step by step
Solved in 2 steps with 4 images

- Simplify the Boolean expression F = C(B + C)(A + B + C).The given algebraic expression is written in prefix notation. ∕ − ↑ −a × 7 c 3 4 × 3 b a. Write the expression in postfix notation.b. Write the expression in infix notation.Minimize the following expression using Boolean rules: F=XY+X(Y+Z)+Y(Y+Z)
- the simplified form of following boolean expression is F=(x'+y).(x'(x+y)) a-a.x'y b-0 c-x'y' d-xySimplify the following expressions using Boolean Algebra:Z = (C + D)’ + A’ C D’ + A B’ C’ + A’ B ‘C D + A C D’The simplification of the Boolean expression (A’BC’)’ +(AB’C)’is (A) 0 (B) 1 (C) A (D) BC Note the A’ indicates Not A

