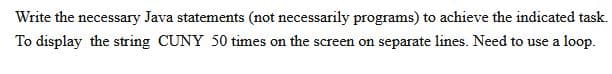
Write the necessary Java statements (not necessarily programs) to achieve the indicated task. To display the string CUNY 50 times on the screen on separate lines. Need to use a loop.
Q: Create a table that differentiates between the functional and non-functional needs of the…
A: The answer is that any information system must pass two types of tests. There are two distinct…
Q: Which two wireless technologies are most common?
A: Different technologies are used every day. Wireless technology is one of the ones that is used the…
Q: Cite importance of converting a value from one number system to another.
A: We communicate with each other in a particular language made of letters or words. We normally type…
Q: Firewalls have several advantages.
A: Launch: You may already be doing some of the following safe computer and internet habits: You never…
Q: My laptop's BIOS was updated, but there is still no display, despite the fact that all of the…
A: According to the facts provided, we must identify the cause of the display problem. There are…
Q: Give three reasons why the spiral model is better than the waterfall model
A: Your answer is given below. Introduction :- It is possible to return to previous phases using the…
Q: Performing more than one instruction at once would waste a computer processor's computing cycles.…
A: Answer is given below-
Q: What is the definition of logical addressing?
A: Logical Addressing: A logical address is the address where an object (memory cell, storage element,…
Q: Computer systems are made up of a variety of components. Explain?
A: Computer system components include: The three fundamental components of every computer system are:…
Q: Write the precondition & postcondition for each method.
A: We are required to trace the code for the given values and define the pre and post conditions for…
Q: Provide an evaluation of whether Nestle is an open or a close system and how a change in one…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. A quality…
Q: How does the widespread availability of digital technology make it possible for nearly anybody to…
A: Launch: We must discuss how digital technology allows everyone to produce multimedia. People may now…
Q: One aspect of a simulated annealing cooling schedule is the temperature. i. Explain the effect of…
A: Answer
Q: A firewall system's primary job is to keep outside threats out. What are the rules of thumb for…
A: Data is transmitted over internet in forms of small chunk of packets .There are two types of…
Q: A super wing-ding diagnostic tool is performed on your personal computer, and the results indicate…
A: Given: Assume you run a super wing-ding diagnostic tool on your PC, and it says that your hard disc,…
Q: How does a Demilitarized Zone, often known as a DMZ, function in terms of the security of a network?…
A: How does a Demilitarized Zone, often known as a DMZ A DMZ, short for demilitarized zone, is a…
Q: Employee is a class with a function to set the details of the employee such as the emp_id, Name,…
A: You have not mentioned programming language so I am going to write code in c++. #include…
Q: Should we connect the CPU to the RAM via an asynchronous or synchronous bus? Please include an…
A: A bus is a type of communication link that uses a collection of wires to connect multiple…
Q: What steps can we take to ensure the success of our projects? What exactly does it mean when a…
A: To guarantee that our project succeeds, there are a few critical steps to take. Ensure that the…
Q: What will be the output of the following C++ code? #include #include using namespace std; int…
A: The output will be l Explanation:- In this line char str[] = "Hello World"; the character array are…
Q: Iterative-and-incremental and the waterfall approach have a lot of similarities, but how do they…
A: The waterfall model is one of the most common and straightforward models used in software…
Q: What other types of firewalls are there except the ones that are based on a network?
A: Network firewalls: Firewalls limit illegal access to private, Internet-connected networks, such as…
Q: Which architecture is the one that has become the de facto standard for the installation of a…
A: which architecture the one has become de facto standard for installation of firewall todays business
Q: Describe what happens when a student views www.google.com while their laptop is connected to the…
A: The answer is given in the below step
Q: Explain in three points why the spiral model is preferable than the waterfall model. Describe how…
A: Introduction: The SDLC methodology really introduces spiral and waterfall models. A project is…
Q: What are the advantages and disadvantages of each successive generation of networking technology?
A: Generation of Networking Technology: Each Generation is characterized by a collection of telephone…
Q: Which three requirements must be satisfied by a network in order for it to function in a manner that…
A: Introduction: Here we are required to explain three requirements that must be satisfied by a network…
Q: What Makes Up a Computer System's Components? Give a short summary of what you're trying to…
A: According to the information given:- We have to define the Makes Up a Computer System's Components…
Q: The cold extrusion products have bad surface finish Select one: O True False
A: Cold work improves the surface finish attainable
Q: What is digital audio? How digital audio is produced from analog sound waves?
A: Digital audio: The reproduction and transmission of sound in a digital format is digital audio.…
Q: What is a mantrap? A fake network set up to lure in and catch a hacker A trap…
A: According to the information given:- we have to choose the correct option to satisfy the statement.
Q: Explain any two Operating System Service structures.
A: The structure of an operating system determines how it is defined and how it runs. Monolithic…
Q: Concerns and issues of a wide variety are brought about by information systems that are not…
A: It is a well-known fact that various systems give rise to many problems and complications. Losses…
Q: = Binary data is transmitted over an AWGN channel at a rate of 1 Mbps. The required average…
A: Answer
Q: Discuss how firewalls can protect your business. How do software and hardware firewalls compare? How…
A: What are the pros and cons of using a software or hardware firewall? What software do you use to…
Q: What factors contribute to the evolution of an information system's overall scope?
A: let us see the answer:- Introduction:- (information systems for corporate management) has been and…
Q: What is the purpose of the contactors' auxiliary contacts? Give an illustration or use case.
A: An auxiliary contactor allows one switch to control another switch.
Q: How do we go about analyzing and developing system infrastructures and architectures while working…
A: Analyzing and Developing System: Analyze and design the system infrastructure and architecture in a…
Q: w may a firewall be used to pro
A: Introduction: Below how a firewall be used to protect your data
Q: What are the advantages and disadvantages of each successive generation of networking technology?
A: 1G Technology: 1G stands for first-generation. It may be used as a different carrier in mobile…
Q: Testing at the unit level, testing at the integration level, and testing at the system level are all…
A: Explanation: Unit testing:Imagine you're a software engineer. Software development is multi-step.…
Q: What kinds of network topologies can really be implemented, and which do you think are the best?
A: The physical network topology refers to the actual connections of how the network is arranged.
Q: How can one guarantee the evolution of old systems?
A: Reverse Engineering and Re-engineering ensure that legacy systems continue to develop in their…
Q: Consider how important wireless networks are in poor countries. Why do some companies choose…
A: Families with many electronic devices, such as PCs, laptops, and other mobile devices, are…
Q: Prove that 2n = o(22n).
A:
Q: What does the term "Access Point" mean? What's the underlying mechanism?
A: Access Point for Wireless Networks (WLAN): You can establish a wireless local area network (WLAN)…
Q: Provide a minimum of three advantages that the Spiral model has over the Waterfall approach. Please…
A: For Software Development Life Cycle risk management, the spiral model is one of the essential…
Q: What are the key advantages of application system reuse in contrast to the construction of software…
A: Construction of Software: Software development is a subject of software engineering. Through a mix…
Q: Can you please write C program that will act as a shell interface that should accept and execute a…
A: Answer
Q: fashion. (3-5 paragrap
A: Fast fashion is conceivable as a result of retailer store network the executives headways. Low costs…
15
Step by step
Solved in 3 steps with 2 images

- this is a java program Complete the given task and give the code here and screenshot of the outputCan you please help me modify this program as in the instructions in the red circle? This is a java program. I need the output to be the same as in the example picture (same picture with the red circle)write a code using java to run the program below
- It's common to print a rotating, increasing list of single-digit numbers at the start of a program's output as a visual guide to number the columns of the output to follow. With this in mind, write nested for loops in Java to produce the following output, with each line 60 characters wide:Write a program in java to get the number from user and then check whether all digits in that number are same or not.this is a java program give me the output with explanation in simple words only so that I can understand
- Please help repeat this Java programming using the text method of input or outputCreate a Java program that loops around getting two fractions from the user,output their sum, and state whether or not they are equal. Keep looping untilthe first fraction entered is a zero fraction.Fix the Java code below, You must have a Boolean variable or return value somewhere in the program. Sample Output is in the picture
- For Java Make a program that makes a triangle. It will be a seven-line pattern, like the one in the figure. Using your knowledge of loops, make the program so that it contains no more than three output statements.Write a Java code and initialize the following variables: title, last name, first name, student number, age and address. After that, display all the values.Manually trace the execution of the following Java code segment: (e) a=1, b=2; if (!(a>b)) { System.out.print(b); } else { System.out.print(a); }

