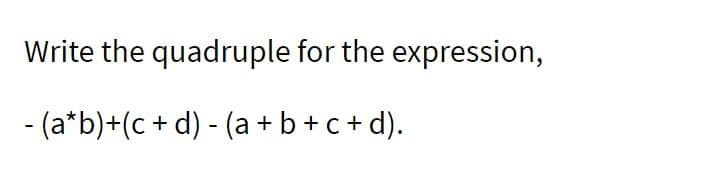
Write the quadruple for the expression, - (a*b)+(c + d) - (a+b+c+d).
Q: It's necessary to recognise and characterise the four main types of disc access caching.
A: Introduction: A disk cache is a system for further developing the time it takes to peruse from or…
Q: Peçe 19 ia Is Write in program to print Fibonacci Series (0112358 413 21 34).
A: Step-1: StartStep-2: Declare variable n, a=0, b=1Step-3: Take input nStep-4: Print a and bStep-5:…
Q: How can I mine cryptocurrency on my laptop?
A: Introduction: The cryptocurrency may be used without being traced. Another cryptocurrency that may…
Q: What is missing from this statement?
A: Introduction: Scanner class in java comes under ‘java.util’ package and gives several methods to…
Q: Find the shortest path between points. 3,1, 4) and (-1,-1,3) on the plane 2 2 2-5 -X-Ý
A: The shortest path between the points on the plane is solved in Step 2.
Q: **The below screenshot has VBA codes in the editor windo 3 subs. The instructions on the expected…
A: According to the information given:- We have to define VBA codes on the basis of instructions…
Q: Project Title: Design of rf based speed control system for vehicles App Name: (Program name)…
A: The vehicle speed control system is designed to control the speed of the vehicle in specific zones…
Q: Create a program that will calculate and print to the screen a sales receipt. Required: 1. First 3…
A:
Q: In a situation of chaos, order and structure cannot be created. What specific examples do you have…
A: It is projected that a wide range of system configurations would experience an intermediate state…
Q: Find out which of the top four web browsers has the most users and the most market share. What…
A: Web browser: Anywhere on the internet is accessible with a web browser. It pulls data from other…
Q: What are the benefits and downsides of dispersed data processing that should be considered while…
A: Given:
Q: Assume function call below will replace the comment in the main(). What should be the actual…
A: Actual parameter if we want to pass the address of the last double stored in aValues:…
Q: 5.(15%) Generate an optimal Huffman code for the following set of characters with frequencies: c:…
A:
Q: Write a complete C program to calculate total pay which includes net salary and bonus. The sample of…
A: Solution code :- #include <stdio.h> // double basicSalary() function to ask user to enter…
Q: The risk that is faced by businesses that are dependent on information technology has either grown…
A: Introduction: Let's start by examining the purpose of information security. By averting security…
Q: I try to download the image that I uploaded in the website using Python Selenium, but I get an error…
A: You can download the image file with src url starting with "blob:http" by
Q: What should be written in Q1? (Adjust nUnits) nUnits = getReverse(nRev); nUnits = 1; nUnits = 0;…
A: B. nUnits = 1
Q: Topic: C Programming - Text Files Please remember that 1KB is equal to 1024 bytes. Type your…
A: End of the File or EOF is the position of the file at which a specific file end. EOF of a file can…
Q: Ques-1 explain The Bagging algorithm and it's steps to perform it. I
A: The ensemble learning technique known as bagging, often referred to as bootstrap aggregation, is…
Q: How is the increased use of smartphones and tablets, with their smaller screen size, affecting user…
A: The Answer for your question is given below clearly step by step: Yes, there are lot of issues that…
Q: What are the best practises for using computer-aided decision-making?
A: Introduction: Computer-aided decision-making innovation, which comes from applications that arrange…
Q: You have been provided with the following elements • Sheunesu • Katlego • Andries • Buhle • Avinash…
A: Step-1: StartStep-2: Declare a variable set of LinkedHashSetStep-3: Add given elements into…
Q: Investigate the four most popular web browsers and their respective market shares. They've grown in…
A: Introduction: We all understand the browser's or program's fundamental usefulness: it connects you…
Q: The purpose and objective of an auditor is to form opinions on whether the operations of an entity…
A: The question has been answered in step2
Q: 1) What are the company's key assets? What do they need to protect? (An asset is an item of property…
A: Careless Employees Your employees are on the frontline of guarding your company’s knowledge assets.…
Q: Write a simple nested loop example that sums the even and odd numbers between 5 and 15 and prints…
A: I give the code in Python along with output and code screenshot
Q: Consider the following instance of relation Sells(book_title, library, price): book_title The grand…
A: Answer: Books sold by more than one library
Q: True/False - Sorting, no explanation a) The worst-case time complexity of HeapSort is O(n log(n)).…
A: Big O notation is a maths notation which helps in describing the limiting behaviour of a given…
Q: 3. (a) (b) How is a doubly linked list more useful than a singly linked list? Write a program/pseudo…
A:
Q: What are the benefits and downsides of dispersed data processing that should be considered while…
A: Dispersion refers to how data has been spread out, for instance where the data set has a large…
Q: Please answer Values 1-5. Complete the following Incomplete LMC program by filling out the vacant…
A: An instruction model of the computer called Little Man Computer. It has simple von Neumann…
Q: 7. SOFTWARE SALES A software company sells a package that retails for $99. Quantity discounts are…
A: #include <iostream> #include <iomanip> using namespace std; int main() {…
Q: Suppose that we have n entries of computers in an electronic store. These computers are of 5…
A: Lower Bound – Let L(n) be the running time of an algorithm A(say), then g(n) is the Lower Bound of A…
Q: Is it feasible for two network interfaces with the same MAC address to communicate with each other?…
A: In a computer network, there is a requirement for communication which is fulfilled by an addressing…
Q: Is there a way to leverage regions and availability zones to increase application resilience,…
A: Application Resilience: Application resilience is an application's capacity to respond to faults in…
Q: make me a simple program with the application of control structures, functions and arrays about the…
A: Structure which is also called as structs are the way to group the several related variables in one…
Q: A lady behaves like a teacher in a classroom, mother or daughter in a home and customer in a market.…
A: The concept used is Polymorphism, In this case. The idea of polymorphism allows for the execution of…
Q: Define, 3 A = 6 2 Find X. Hint: use numpy.linalg.inv and the @operator for matrix multiplication. 5…
A: Python Program: import numpy as np # declare array A A = np.array([[3, 5, 2], [6, 1, 7], [2, 5,…
Q: Assuming a 4-KB page size (4096 bytes), what are the page Numbers and offsets for the following…
A: As per guidelines I can answer only three sub-parts. Thank You. Page size: 4KB : 4096 bytes a) Page…
Q: 2. (a) (b) What do you understand by Time and Space complexity? How is Big-0 notation used for…
A:
Q: What is the signed decimal number that is equivalent to the 8-bit binary number 10101010 given that…
A: A sign magnitude format is the simplest way of representing the signed decimal number in binary…
Q: When it comes to programming, what are the advantages and disadvantages of dynamic programming?
A: Dynamic Programming: In the field of computer programming, the method known as "dynamic programming"…
Q: references, Cite Them Right Harvard style?? and just over half of what was asked
A: Lubuntu - Utilize the LXQt desktop environment instead of GNOME in Ubuntu. Previously billed as…
Q: What does it imply to say that a "operating system" runs a computer? Is it feasible to make the…
A: Given: This question relates to the definition of the word "operating system" and the possibility of…
Q: What are some ways that regions and availability zones may be utilised to increase the resilience of…
A: Introduction: This article explores the usage of regions and availability zones to enhance the…
Q: Provide a schematic and input string for each version of a Turing machine.
A: Turing machine: An abstract machine that manipulates symbols on a strip of tape in accordance with a…
Q: Star University is a private research university that provides an exceptional education for…
A: Class diagram is the static diagram which represents the static view of the application. Class…
Q: Because of their inherent properties, wireless networks face a wide range of issues. Explain in your…
A: Introduction: Wireless networks that are reliable and secure are becoming increasingly important to…
Q: Explain the problems with pointer type design. In many programming languages, pointers may only…
A: Introduction: Levels of pointers is the term for this. Each compiler must include at least 12 layers…
Q: Requested resources are made available to those who have reached a standstill as a result of…
A: Introduction: A deadlock happens when two computer programmes that share the same resource get…
Step by step
Solved in 2 steps

- Simplify the following expressions using Boolean Algebra:Z = (C + D)’ + A’ C D’ + A B’ C’ + A’ B ‘C D + A C D’What does logic expression XB'C'+X'BC look likeGiven an infix expression a*(b+c)-d, its postfix expression is (A) a b c d * + - (B) a b c + * d - (C) a b c * + d - (D) - + * a b c d Which is the right answer and please explain why
- CLEAR AND CORRECT OR DISLIKE Put it in shortest form using boolean algerba (A+B+C+D) (A+B+C+D') (A+B+C')(A+B')Simplify these Boolean expressions as much as possible: a) ((A+D)'(C'+B')'+C)' b) A'B+CA'D+B'+D' c) (A+(AB)'+C(AB)')(A+BA'+B')Draw logic diagram for the following expression F = ( AB + CD) C '

