Write the status of the Carry (C), Zero (Z), Negative/Sign (N), and Overflow (V) flags after an 8-bit ALU performs an ADD operation on the following 8-bit arguments and b): Hint: Remember that the ALU just sees bits and does not know if the numbers represent signed or unsigned numbers. a. uint8_t a = 122, uint8_t b = 44 b. int8_t a = 32, int8_t b = -22 Please don't write the answer only. kindly show the solution how you get the answer. You can solve it on paper and upload it.
Write the status of the Carry (C), Zero (Z), Negative/Sign (N), and Overflow (V) flags after an 8-bit ALU performs an ADD operation on the following 8-bit arguments and b): Hint: Remember that the ALU just sees bits and does not know if the numbers represent signed or unsigned numbers. a. uint8_t a = 122, uint8_t b = 44 b. int8_t a = 32, int8_t b = -22 Please don't write the answer only. kindly show the solution how you get the answer. You can solve it on paper and upload it.
Chapter8: Data And Network Communication Technology
Section: Chapter Questions
Problem 31VE
Related questions
Question
...........
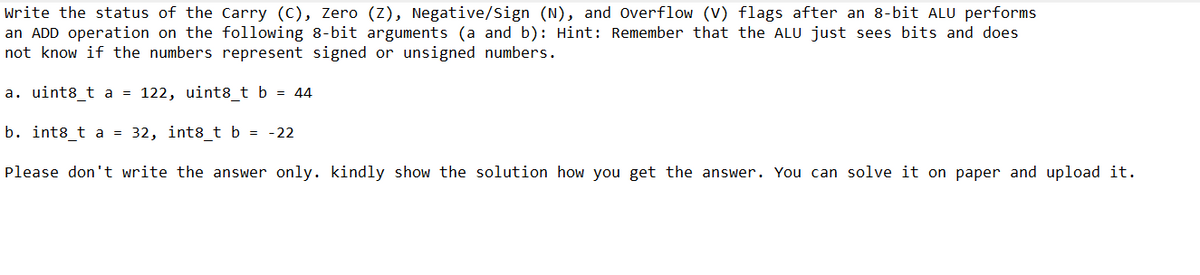
Transcribed Image Text:write the status of the Carry (C), Zero (Z), Negative/Sign (N), and Overflow (V) flags after an 8-bit ALU performs
an ADD operation on the following 8-bit arguments (a and b): Hint: Remember that the ALU just sees bits and does
not know if the numbers represent signed or unsigned numbers.
a. uint8_t a = 122, uint8_t b = 44
b. int8_t a = 32, int8_t b = -22
Please don't write the answer only. kindly show the solution how you get the answer. You can solve it on paper and upload it.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning