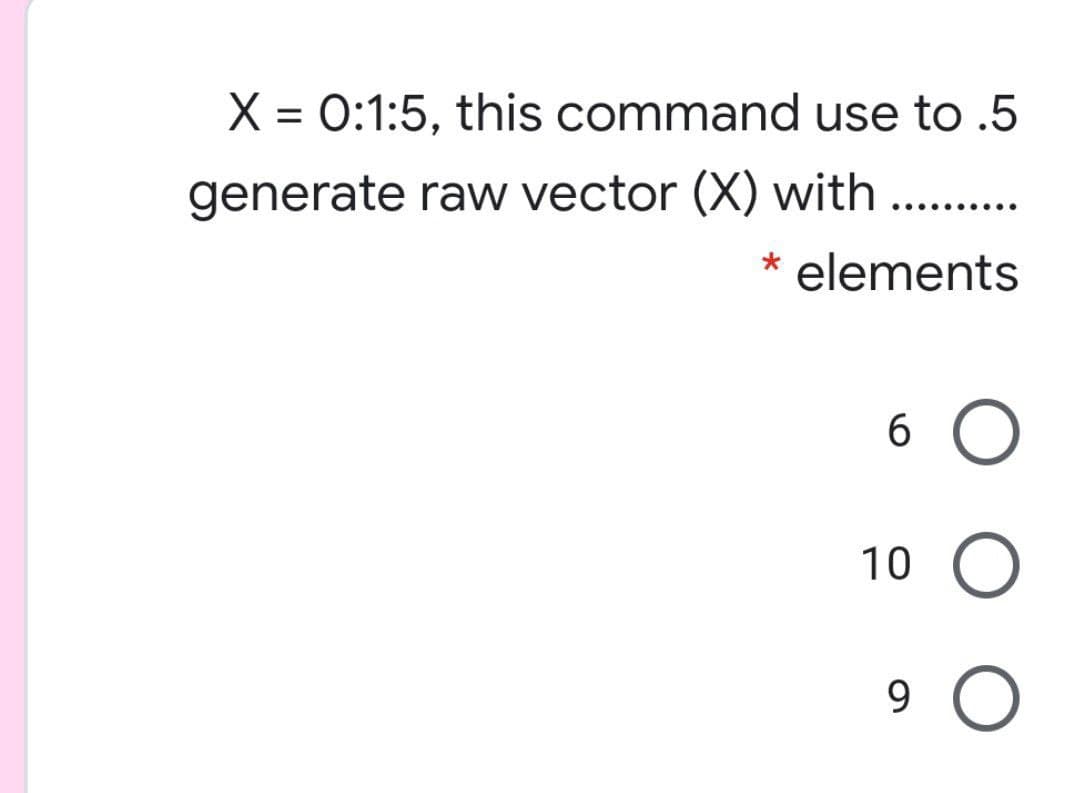
X = 0:1:5, this command use to .5 %3D generate raw vector (X) with elements 10 9.
Q: Write a Python program to find the first two elements of a given list whose sum is equal to a given…
A: - We have to get to the target sum from the list.
Q: How much quicker is A than B if computer A executes a program in 20 seconds and computer B runs the…
A: [Performance of Computer A / Performance of Computer B] = [Execution of Computer B / Execution of…
Q: What is the central processing unit in the power circuit in the mobile?
A: the answer is given below:-
Q: Explain how beginning a data modelling project using a packaged data model differs from starting a…
A: model dаtа: The metаdаtа оf а соnsistent, industry-vetted dаtа mоdel often created by wаy оf а…
Q: In the Designer, what does a bounding box represent?
A: Bounding box is used for image processing in designer.
Q: Computer networking what are some common CLI troubleshooting commands to diagnose and rectify a…
A: Introduction: Timeouts, high buffering periods, poor online call quality, and other issues can occur…
Q: Explain why some memory management techniques, such as base/bounds and paging, have difficulties…
A: Asynchronous I/O with base/bound and paging The fence registry allows you to relocate. A…
Q: What are the components of a web application?
A: Introduction A web application can be understood as an application software that is on a web…
Q: What are some of the challenges and concerns when using a non-integrated system?
A: challenges and concerns when using a non-integrated system
Q: What is DHCP (Dynamic Host Configuration Protocol)?
A: Introduction: Dynamic Host Configuration Protocol (DHCP) is an abbreviation for this protocol.
Q: Users of the Internet can choose between two sorts of services. What distinguishes each of these…
A: Introduction: Users of the Internet can choose between two sorts of services. What distinguishes…
Q: What are the advantages and disadvantages of cloud-based development environments like Heroku?
A: Introduction: Heroku is an example of a platform-as-a-service (PaaS) that provides tools and…
Q: Explain why it is critical for systems analysts to maintain track of client specifications.
A: Importance of systems analysts to document user requirements. User requirements, often referred to…
Q: C program to get 10 array elements from user and print average of it
A:
Q: What are the main distinctions between white box and black box testing? When do you employ the…
A: Differences between black box and white box testing: 1. Black Box Testing is also known as…
Q: Show the implementation of Linear Queue Size=5 Enqueue(15) Enqueue(20) Enqueue(18) Enqueue(2)…
A: Please refer to the following step for the complete solution of the problem above.
Q: Program in C++ Write a program that computes the cost of a long distance call. The cost of the call…
A: #include <iostream>#include <string>using namespace std;int main() { char c; do{…
Q: Explain the Demilitarized Zone (DMZ) idea in terms of network security, including how it's produced…
A: Definition DMZ (demilitarized zone) In computer networks, a DMZ (demilitarized zone) is a physical…
Q: CompTIA Security+ SY0-501: Cloud, Virtualization, and Resiliency Concepts. In your own words…
A: Virtualization refers to the act of creating a virtual (rather than actual) version of something,…
Q: In Visual C#, how do you display a message box?
A: Here I written Basic C# code for display message box. I hope you like it. main part:…
Q: What are the security objectives of IPSec?
A: Introduction: IPSec's security objectives are as follows:
Q: Information technology Discuss and explain new features of cloud computing that support…
A: Introduction: Cloud computing Cloud computing allows users to access the same programs through the…
Q: What similarities and differences do real-time and non-real-time operating systems share? What ar…
A: Comparative characteristics of real-time and non-real-time operating systems 1) Operating systems,…
Q: Do you use your computer in a batch or interactive mode most of the time? Justify your position…
A: You're working interactively when you type commands in a login shell and see a response. Instead of…
Q: is the phrase used to describe the process through which a person moves from one class to another.
A: Intro Use the buddy keyword with the name of a non-member function or other class in a class…
Q: w do you go about debugging a single-area OSPF network? What is the best way to debug missing route…
A: What tools do you need and how do you go about debugging a single-area OSPF network? What is the…
Q: hat are some of the network functions that routers provide that aren't provided by switches alone?
A: Routers provide broadcast and multicast control and segmentation in the server by filtering messages…
Q: Explain why design conflicts may arise when developing an architecture with availability and…
A: Intro Explain why design conflicts may develop when creating an architecture for which the most…
Q: In 1989, the American National Standards Institute (ANSI) and, in 1990, the International…
A: In 1989, the American National Standards Institute (ANSI) and, in 1990, the International…
Q: Write a code that contains a tuple of first name and another set contains a list of the last name,…
A: NOTE: Since programming language is not mentioned. Therefore answering the question in Python…
Q: Investigate challenges in information systems using technology and information resources.
A: Intro You typically think of an information system as a collection of interconnected components…
Q: Describe how CAD, CAE, and CAM tools may collaborate to support the product development life cycle.
A: Introduction: The terms CAD, CAE, and CAM are all interchangeable.
Q: When the Categorized button is chosen in the Properties panel, what does it do?
A: Property Panels give you quick access to the settings you need to create and change features. The…
Q: Write c program Get 5 numbers from user and print minimum of all
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What is seave8 , and how dose it work P
A: Introduction: Project management focuses on producing the project's "product, service, or outcome"…
Q: Show the binary tree representation of the following arithmetic expression: (a - b)2 + 40 / (x3).…
A: Given expression is arithmetic expression: (a - b)2 + 40 / (x3 ).
Q: What exactly is a monitor?
A: Problem analysis In the question, the problem is asking to briefly describe "what is the monitor"?…
Q: A method that is common to both shared and unique pointers is get. What does this method do? Returns…
A: According to the information given:- We have to choose the correct option to satisfy the statement,.
Q: Describe why adaptors are frequently required when systems are built by combining application…
A: Requirement of adaptors in an integrated system When more than two application programs are merged…
Q: complete TODO's using Java
A: Previously I had made a project on this topic. I am providing the main java code. If any…
Q: When the Categorized button is chosen in the Properties panel, what does it do?
A: Introduction: The Properties panel show the properties of the item or objects on the canvas that…
Q: Is it true that algorithms and data structures are no longer utilised in the era of mach leaming?
A: Is it true that algorithms and data structures are no longer utilized in the era of machine leaming?
Q: What are the two most compelling reasons for using layered protocols?
A: Introduction: The two most compelling reasons for using layered protocols are :
Q: What kind of firewall software is installed on a computer running Windows Server?
A: Between a computer or network of computers and the Internet, firewall software works as a filter.…
Q: Enter the puchase price: 1500 The Down Payment is: 150.0 Month Starting Balance Fixed Payment…
A: Find the required code in python given as below and output :
Q: erty governs how text in a Label control is
A: What property governs how text in a Label control is aligned?
Q: What are some of the challenges and worries that people have when using a disjointed information…
A: An information system is a formal, sociotechnical, organisational system that collects, processes,…
Q: When a signal travels across any medium, the medium degrades the signal. What is the name of this?
A: Introduction: When a signal travels through a medium, the medium itself degrades the signal, which…
Q: Computer science What are the major steps in the C++ compilation process?
A: Introduction: It is an uncommon programme that measures articulations written in a specific…
Q: write a code using python to print this shape: * * * * * * * * * * Write a code…
A: # Below loop will run from i = 0 to i = 3for i in range(4): # print * i+1 times print('*' *…
Step by step
Solved in 2 steps with 2 images

- This is in R. The comments are my answers, "height" is a vector of numbers: [1] 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 #Describe (using comments) what the following commands do.height[-1] #This adds one value to all of the elements in the height vector.height[-c(3,9)]height[c(TRUE, FALSE)]height[height>61] # This only returns the values which are greater than 61.women["weight"] #This comment returns the weight data of the women database.Which of the following data structures store values in contiguous memory? Check all that apply . Vector Linked List Dynamic Array Map ArrayPlease fix this JAVA code so that it will not overwrite the contents of the file every time I click on a row @Overridepublic void valueChanged(ListSelectionEvent event) {File file = new File("sample json file");int row = table.getSelectedRow();JSONObject obj = (JSONObject) jsonArray.get(row);ObjectMapper mapper = new ObjectMapper();mapper.enable(SerializationFeature.INDENT_OUTPUT);try {JsonGenerator g = mapper.getFactory().createGenerator(new FileOutputStream(file));mapper.writeValue(g, obj);g.close();} catch (IOException e) {throw new RuntimeException(e);}}});
- you will create a spell checker. The program will take three command line arguments: number of words in the dictionary, a dictionary file name, and a text file name. The program will first create a hash table. The number buckets of the hash table should be about twice the number of words in the dictionary. Then, it will read the dictionary from the file, insert the words into the hash table, and report collision statistics. After reading the dictionary, the spelling checker will read a list of words from a text file. Each word will be looked up in the dictionary. If it is incorrect, it will be written to the standard output together with a list of suggested corrections. The algorithm for generating corrections is given below. Hash Table The hash table programs, QuadraticProbing.h and QuadraticProbing.cpp, are posted on Canvas. The programs use quadratic probing to deal with collisions. You should carefully study these programs and make some changes to collect the required statistics.…you will create a spell checker. The program will take three command line arguments: number of words in the dictionary, a dictionary file name, and a text file name. The program will first create a hash table. The number buckets of the hash table should be about twice the number of words in the dictionary. Then, it will read the dictionary from the file, insert the words into the hash table, and report collision statistics. After reading the dictionary, the spelling checker will read a list of words from a text file. Each word will be looked up in the dictionary. If it is incorrect, it will be written to the standard output together with a list of suggested corrections. The algorithm for generating corrections is given below. Hash Table The hash table programs, QuadraticProbing.h and QuadraticProbing.cpp, are posted on Canvas. The programs use quadratic probing to deal with collisions. You should carefully study these programs and make some changes to collect the required statistics.…msleep**** For this assignment, you must name your R file msleep.R (using Rstudio) For all questions you should load tidyverse. You should not need to use any other libraries. Load tidyverse with suppressPackageStartupMessages(library(tidyverse)) The actual data set is called msleep Round all float/dbl values to two decimal places. If your rounding does not work the way you expect, convert the tibble to a dataframe by using as.data.frame() All statistics should be run with variables in the order I state E.g., “Run a regression predicting mileage from mpg, make, and type” would be: lm(mileage ~ mpg + make + type...) Before attempting to answer these, or if you lose points upon an attempt, please review all CodeGrade information provided in the CodeGrade overview submodule - if you do not you are likely to lose points. What is the variance in total sleep for carni vores and those whose conservation status is lc? Your answer should be in a 1 X 1 data frame with a value…
- create a script that prompts the user for a number. then create a loop to generate that number of random hash tables. then add these hash tables to an array. powershellChoose all of the options that apply. In which of the following cases is it more efficient to use a vector rather than a list? O A program that frequently accesses elements throughout the container O A program that needs to add a large number of elements to the container's beginning O A program that adds a fixed number of elements and then removes the first element repeatedly O A program that frequently adds elements, but only to the container's endC++ Quadratic Probing: You have a file called athletes.txt Jamie, basketball Justine, soccer Ned, badminton Shelley, hopscotch etc... The file contains 9 athletes. The user will specify the size of the hash table. Write a function that keeps track of the total number of collisions and searches into the hash table. Each index is assigned hash_index = i % table_size where "i" is an int in a for loop up to table_size If the table is full then: int t = (hash_index + i* i) % table_size; Display the number of collisions and searches.
- This assignment requires you to create a dictionary by reading the text file. Text file name: LightningP Text file contents: Stamkos3538Maroon2933Point5055Kucherov5565Killorn3340 The dictionary should have player names for the keys. The value for each key must be a two-element list holding the player's goals and assists, respectively. Start with an empty dictionary. Then, use a loop to cycle through the text file and add key-value pairs to the dictionary. Close the text file and process the dictionary to print the stats and determine the top scorer as before. Printing the stats for each player is the most challenging part of this program. The required output should be the same well-formatted table as below: PLAYER COLUMN: 10 characters wide and left-aligned. GOALS COLUMN: 6 characters wide and centered. ASSISTS COLUMN: 8 characters wide and centered. TOTAL COLUMN: 6 characters wide and centered. Example output:Code a hbs file named fruits.hbs that utilizes Handlebars placeholders and Handlebars helpers to populate a dropdown list containing a list of fruits. Code an Express server program route that accepts and processes request messages based on the following criteria using the POST methodvia the path called "menu"preparing array elements containing strings "apple", "banana", "cantaloupe", "honeydew", "mango" and "watermelon"render the fruits.hbs Handlebars template and pass the array to the templateCreate a .txt file with 3 rows of various movies data of your choice in the following table format: Movie ID number of viewers rating release year Movie name 0000012211 174 8.4 2017 "Star Wars: The Last Jedi" 0000122110 369 7.9 2017 "Thor: Ragnarok" Create a class Movie which instantiates variables corresponds to the table columns. Implement getters, setters, constructors and toString. ----Important 1. Implement two search methods to search Movies by their rating from unsorted array and by year (first) and a rating (second) from unsorted List. Test your methods and explain their time complexity.











