X1 + x2 – X3 = –3 бх, + 2х, + 2х, %3D 2 -Зх, + 4х, + хз 31 -3x1 = 1
Q: What is the system catalogue, and how does it work? Please include at least three products for which...
A: Introduction: The system catalog is a set of tables that describe the database's structure. When a d...
Q: What is tha main function of router?
A: Introduction: Routers are computer networking devices used to transport data packets from one networ...
Q: Find a Topological Ordering Consider the following graph: a b. C e f Provide a topological ordering ...
A: Below is the answer to above question. I hope this will be helpful for you....
Q: What kind of SciFi show should be developed and will appeal to Male and Female audiences born after ...
A: SciFi shows creates a lot of buzz among the generation which connect to the scientific principles.
Q: 2. Because it's such an uncommon format, Python does not include a csv module to make reading and wr...
A: 2) False Python contains csv module in Python's standard library. 3) True Syntax is correct
Q: Write properties table for the following form: O Calculater Numbert Number2
A: Create the form and update the Text=Calculator
Q: ite a python program to find the longest words in a text file for example: [general-purpose, interpr...
A: Lets see the solution.
Q: When it comes to database independence, how can you tell the difference between physical and logical...
A: Physical data independence is mostly concerned with how data is saved in the system. whereas logical...
Q: REMINDER: - Every recursive function must have one or more base cases, - The general (recursive) cas...
A: Please refer below for your reference: Recursive algorithm to get maximum element is : int find_max(...
Q: A university professor who works with sensitive medical information exchanges a private file with a ...
A: Introduction: In this scenario, the professor is to blame for sharing a private material with a stud...
Q: Investigate the use of the edge detection approach to image segmentation and segmentation. Why is di...
A: Introduction: Image segmentation is a critical stage in digital image processing. Segmentation is th...
Q: te a program to find the summation of the numbers from 5 to 15
A: ANSWER:
Q: (a) Construct deterministic finite automata accepting the following languages: (i) {w e {0, 1}"| w i...
A:
Q: en: Language L = {w is in {0, 1}* | w ends with a 0} over the alphabet = {0, 1}. Based from the give...
A: Lets see the solution.
Q: Consider the following problem, and determine which aspects listed below are ambiguous (i.e., you ca...
A: Consider the following problem, and determine which aspects listed below are ambiguous (i.e., you ca...
Q: A DDBMS differs from a heterogeneous DDBMS in a number of ways. What could possibly be more difficul...
A: A distributed Database can be classified as homogeneous or heterogeneous. In Homogeneous DDBMS all s...
Q: Computer science Why is scope creep so common in information system design?
A: Introduction: Information System Design will be used to finish the project. A project is a client's ...
Q: Why should you care about the approaches of programme design?
A: Introduction: The stages in programming design are as follows: - Understanding the program and deter...
Q: When surfing online, you get some strange data on an apparently secure website, and you realize you ...
A: The answer is given in the below step-
Q: I'm interested in learning more about how the Big Oh notations in Algorithms are implemented.
A: Introduction: The Big Oh sign is used to represent the upper bound on an algorithm's runtime, and he...
Q: 8. The problem of template matching takes as input two nmatrices I[0 - 1,0 : n - 1] and T[0 m - 1,0:...
A: Proficient calculations for picture format matching on fine grained as well as medium grained MIMD h...
Q: Explain what the Named Entity Recognition software is and what it is meant to do in its first few mi...
A: INTRODUCTION: Employers can use recognition software to reward employees for their health and safety...
Q: Computer science What are some of the most common difficulties that affect software?
A: Introduction: A software bug is a mistake, error, or flaw in computer software that causes it to gen...
Q: 1- A combinational circuit is defined by the following three functions F1= XY +XYZ F2= XY+ XYZ F3= X...
A:
Q: In CSS, explain the difference in using a flex layout, vs using a grid layout. find at least 3 diffe...
A: Given: We have to discuss, In CSS, explain the difference in using a flex layout, vs using a grid ...
Q: What are the benefits of using virtualization on a network environment
A: Introduction: Network Virtualization (NV) is a term that refers to the process of abstracting networ...
Q: а. 10, 20, 30, 40, 50 (in decreasi b. 50, 40, 30, 20, 10 (in decreas: c. H, E, A, P, S, O, R, T (in ...
A: given - Analyze and evaluate the Heapsort algorithms as Transform-and-Conquer technique usea. 10, 20...
Q: Describe how a firewall resembles a data stream that has been divided into packets.
A: According to the question A firewall is a community safety tool that monitors incoming and outgoing ...
Q: /hich of the hen we kno erations:
A: given - Which of the following loops is best when we know the number of iterations:
Q: What technological innovations in the fields of software engineering and computing have occurred bey...
A: Introduction: Software engineering refers to creating computer programs by using engineering princip...
Q: Q3 Devise a context-free grammar that generates L {wiw2 : w1, w2 E {0, 1}* and wi # w2}.
A: Context Free Grammar : - It's a type of formal grammar that generates all conceivable strings in a f...
Q: What are the two most significant benefits of encrypting data stored in a database system?
A: INTRODUCTION: Encryption: It is a technique for protecting your data from outsiders or those you do ...
Q: List at least a couple of items that a process could be awaiting before proceeding.
A: Process: Process is the instance of a computer program that is being executed by one or many thread...
Q: Data leaking should be defined.
A: Introduction: It is the unlawful communication of data from inside an organisation to an external de...
Q: A graph has the following edge-endpoint function table. Edge Edgepoints {v. v3} e2 {v2 vs} {vs, Va} ...
A: Please refer below for your reference: For vertices: V1: 2 V2: 3 V3: 3 V4: 2
Q: numben into convert the given binary decimal number Systm. %3D humber : Rromsa
A: The decimal number of given binary number is (14.375)10
Q: Exercise 5: Write a C++ program which reads from a file inventory records of some items (“inventory....
A: 1)Read the each number from input file 2)And assign it to array 3)Based on the index print to the ...
Q: In what way does a netlist serve a purpose?
A: Typically, the netlist is a list of the electrical connections between components on a circuit board...
Q: Which of the following is an NFA for L = { w∈{0,1}* | w has a substring of 100 }
A: Given: Which of the following is an NFA for L = { w∈{0,1}* | w has a substring of 100 }
Q: Construct the NFA that will accept the string of (dclac)* dc (gg|bb)*dc.
A: Answer is given below-
Q: In Python you indicate exponentiation .1 with
A: In python, exponents are calculated in the following ways: Using the ** operator. To calculate 25 w...
Q: How do i convert a repaeting decimal into a fraction? I seem to understand how to mostly do it on my...
A:
Q: The first index value in string equal to .5
A: Introduction String is a datatype supported by most of the high level programming languages like C+...
Q: Give an explanation of the three integrity rules. Explain why each rule is being enforced and why it...
A: Data integrity is normally enforced in a database system by a series of integrity constraints or rul...
Q: Why were the TPC-D and TPC-R benchmarks introduced in lieu of the TPC-D?
A: Benchmarks like the Transaction Processing Performance Council (TPC) are used to measure a database'...
Q: Create blade template containing a form having the following form controls: case and submit button. ...
A: Answer is given below-
Q: Some of the devices in one of the buildings where your organisation has set up a network have comple...
A: Introduction: Protecting the network is critical today since there are many data breaches. The data ...
Q: a- Write code to find the sum of even number between 1 to 100 for the first 10 numbers , then for th...
A: Find the required code given as below and output: As per company guidelines we are supposed to answe...
Q: 1- A combinational circuit is defined by the following three functions: F1= XY + XYZ F2= XY + XYz F3...
A: Answer the above questions are as follows:
Q: Given the following binary number in 32-bit (single precision) IEEE-754 format, the decimal value cl...
A:
Solve the system using:
1. Simple Gaussian elimination.
2. Removal of Gauss with partial pivoting.
3. Gauss-Jordan method without partial pivoting.
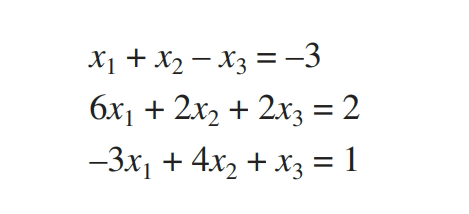
Step by step
Solved in 2 steps with 2 images


