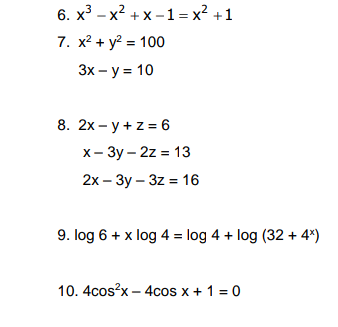
x³x²+x-1= x² +1 6. 7. x² + y² = 100 3x - y = 10 8. 2x-y + z = 6 x-3y-2z = 13 2x-3y-3z = 16 9. log 6 + x log 4 = log 4 + log (32 + 4x) 10.4cos²x - 4cos x + 1 = 0
Q: What distinguishes open source software from closed source software? compile a list of every GIS…
A: A geographic information system (GIS) is a PC system for catching, putting away, checking, and…
Q: What is the definition of database security? Which two database security methods would you mention?
A: Database Security:- Database security refers to the collective measures used to protect and secure a…
Q: 16. NULL can be assigned to a void pointer. O True O False
A: Pointer variables are used for reference purposes.
Q: How were the objectives for the evaluation's user experience and usability divided?
A: User experience refers to an individual's emotional sentiments and mentalities about utilizing a…
Q: What kind of malware are there, and how can you protect yourself from them
A: Malware is malicious software that damages your device and data if it gains access. There are…
Q: What factors need to be considered while creating database field standardization?
A: Answer: We need to write the what factor considered while creating the databases for standardization…
Q: Smith explores problems using information gleaned from tales and traditional wisdom. What makes one…
A: Vital Thinking: The act of choosing what to believe or do requires critical thinking, which is…
Q: Choose three smartphone applications that might be helpful in your present or future employment.…
A: Application programs are computer programs designed to perform specific tasks independently of the…
Q: Please explain the scenario in your own words. Islamic law protects the protection of personal data.
A: Given: Given are Islamic beliefs with relation to the confidentiality of personal information.…
Q: How precisely does multifactor authentication operate? What function does it serve in protecting…
A: Please locate the solution in the following: Answer A security method referred to as multifactor…
Q: Describe four crucial qualities that help systems of systems to differ from one another.
A: Encryption: Based on the operational independence of component systems and the management…
Q: How were the objectives for the evaluation's user experience and usability divided?
A: --> Usability is concerned with the “effectiveness, efficiency and satisfaction with…
Q: Give a brief explanation of how you would use security engineering approaches to examine this DDoS…
A: Considering the information provided: We must outline the security engineering techniques you would…
Q: What is a monitor exactly? What distinguishes semaphores from monitor condition variables?
A: Basics A low level object is a semaphore. It is a variable with a non-negative number. Its value…
Q: What kind of operating system does interrupt-driven I/O use
A: Introduction Operating systems that use interrupt-driven I/O typically rely on interrupts to keep…
Q: Define function pointer?
A: In computer science, in many programming languages, pointers are objects that store memory…
Q: How is technology a mode of revealing? topic: "Technology as a Way of Revealing" and viewing "The…
A: Answer:
Q: Why should you avoid using homonyms and synonyms while creating a database?
A: Homonyms are fields of data in a database that have different values but the same name.The attribute…
Q: What function does the internet, in your opinion, serve in the lives of those who are disabled? •…
A: The internet has always been a powerful tool. It has been used by people with disabilities to…
Q: Difference between global and static variable?
A: Difference between global variable and static variable
Q: What is null pointer?
A: Answer:
Q: Describe the meaning of "inversion of control" as it relates to application frameworks. Describe how…
A: The response to the question can be found in step 2. Inversion of control is an abstract notion that…
Q: What a router does when it gets a packet with an unknown destination network address is described in…
A: Given: What takes place when a router gets a packet destined for a network that isn't mentioned in…
Q: Differentiate between the RISC and CISC instruction sets and architectures using concrete examples.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Examples of…
Q: Do IT professionals need to be familiar with the binary numbering system? Consider five more…
A: Binary number A binary number system comprises information portrayal utilizing 1 and 0. Despite the…
Q: Is it harder to understand how computers operate because they save information in binary? What…
A: No, it is not more difficult to grasp how computers work since binary is a means of describing data…
Q: Explain New classes of descriptive attributes?
A: Lets see the solution.
Q: What component of business intelligence is the most crucial? What, for instance, are the differences…
A: We have to explain what component of business intelligence is the most crucial. And, the difference…
Q: What security methods or procedures may be used to vehicular communications or vehicle-to-vehicle…
A: Answer is in next step.
Q: How do you utilize an Internet of Things wireless protocol to sync data from a wristwatch, bike…
A: Introduction: Today, the Internet has reached nearly every corner of the globe, having an…
Q: Distinguish between short and long jumps on the 8051 microcontroller. Describe five conditional jump…
A: Given:- Explain the differences between short jumps and large leaps on the 8051 microcontroller.…
Q: What is null pointer?
A: Here in this question we have asked that what is null pointer.
Q: What distinguishes conventional on-premises data centers from cloud IT security implementations, and…
A: Given: What distinguishes conventional on-premises data centres from cloud IT security…
Q: Question-7 What are the features of inkjet printers?
A:
Q: What do you mean by #include?
A: A header file is a file containing C declarations and macro definitions (see Macros) intended to be…
Q: "Security" broadly speaking relates to a. immunity from all except direct actions Reverse attack…
A: Introduction: The actions necessary to protect a person or item of property from harm can be…
Q: What function does the internet, in your opinion, serve in the lives of those who are disabled? •…
A: Physically or Mentally Disabled: Anyone who has a physical or mental impairment that significantly…
Q: Describe green computing and how it may improve the quality of life for the environment.
A: Under the concept of "Green Computing," computing has also accepted its promise to help contribute…
Q: What is the difference between creating a "file upload" functionality using PHP native and using the…
A: Given: A physical DFD is concerned with how a system is built, while a logical DFD is focused on the…
Q: What steps are involved in putting finite-state machine control into practice
A: Introduction FSM (Finite-State Machine): A Finite State Machine (FSM) is a computing paradigm based…
Q: What are the differences, for instance, between business intelligence and data
A: Summary Business Intelligence is the process of collecting, integrating, analyzing, and presenting…
Q: What factors should you take into account while considering the advantages and disadvantages of…
A: In distributed data processing, every department processes its transactions locally on its local…
Q: What does it mean to be someone's complement?
A: One's complement: In order to obtain the one's complement of a binary number, one must first convert…
Q: Difference between global and static variable?
A: Introduction In this question, we are asked about the difference between the global and static…
Q: What is De-normalization
A: Lets see the solution.
Q: Specify the elements that make up an information system. How significant is the individual inside…
A: The answer is given in the below step
Q: For mobile networks, packet switching is preferable than circuit switching.
A: Packet switching doesn't require the use of a dedicated channel, in contrast to circuit switching. A…
Q: explain the value of a data model in the context of a standard strength prediction.
A: Answer is in next step.
Q: Can the definition of an operating system be given?
A: A software programme known as an operating system acts as a bridge between physical devices and end…
Q: 9. Where the fu used?
A: Pointers In C, a pointer is a variable that contains the address of another variable. This variable…
Step by step
Solved in 3 steps with 1 images

- 1. Compact discs record two channels (left and right) of music at a sampling frequency of ??=44.1kHz for each channel. If each sample is encoded with 16 bits, and one byte is 8 bits, how many bytes are required to store 48.1 seconds of music? 2. Consider a system that uses 8-bit ASCII codes to encode letters. How long (in microseconds) will it take to transmit the bit sequence encoding Hello-World! if we use a bit time of 4 samples per bit, and transmit samples at a rate of 1MHz? 3. The ASCII table below gives the ASCII codes for common alphanumeric characters and symbols listed from MSB to LSB. What is the bit sequence encoding the message 113? Assume that we transmit the codes of each character in sequence with the LSB first.Consider a telegraph source having two symbols, dot and dash. The dot duration is 0.2 second. The dash duration is three times the dot duration. The probability of the dot’s occurring is twice that of the dash, and the time between symbols is 0.2 second. Assume n = 2 ( 2nd extension of the code), pdash = S0 and pdot = S11. Determine the equivalent codeword for each symbol using Shannon Code. Supersymbol Code S0 S0 S0 S1 S1 S0 S1 S1 2. Determine the coding efficiency.Assuming that XTAL = 11.0592 MHz. a) Find the frequency of the square wave generated on pin P2.3 in the following program b) Find the smallest frequency achievable in this program, and the TH value to do that MOV TMOD, #20H ; MOV TH1, #5; SETB TR1;BACK: JNB TF1 ,BACK ; CPL P2.3 ; CLR TF1 ; SJMP BACK ;
- The latest super-duper supercomputer has memory locations that are 64-bits wide. What is the largest unsigned integer that can be stored in one memory location? Suppose that we use sign-magnitude for storing negative numbers and dedicate one bit for a sign bit. What would be the largest POSITIVE integer that can be stored in a memory location.55. Suppose a digitized voice channel is made by digitizing 8 kHz bandwidth analog voice signal. It is required to sample the signal at twice the highest frequency (two samples per hertz). What is the bit rate required, if it is assumed that each sample requires 8 bits? a. 32 kbps b. 64 kbps c. 128 kbps d. 256 kbps5.1 Evaluate rdx(64,10,4) 0064 5.2 Evaluate rdx(64,8,4) 0100 5.3 Evaluate rdx(64,2,0) 1000000 5.4 Convert denary 47 into hexadecimal. 0x2f 5.5 Evaluate rdx(64,16,4) 0040 5.6 Convert z=0o1235 into rdx(z,2,12) 0b001010011101 5.7 Let a be 0o37, and let b be 0x10. Let c=a+b. Convert c into octal. In denary a=31, b=16 , c=47 i.e. c=0o57 5.8 Which of the two unsigned integers is larger? 0b11111111 or 0x101? 0x101 is larger (0b11111111 is 255; 0x101 is 257.) 5.9 With reference to slide 46 of Subject 0 available around page 53, convert M[ 536 ] into hexadecimal. 0x2a 5.10 With reference to slide 46 of Subject 0, convert M[ 536] into octal. 0o52 can you explain each one how to get answers, bold fonts are answers just need to explain step by step please.
- If you need to design a system for transmitting the output of a minicomputer to a line printer operating at a speed of 30 lines/sec over a voice grade telephone line with a bandwidth of 3 kHz. Assume that the line printer needs 16 bits of data per character and prints out 50 characters per line. What should be the minimum S/N to proceed this transmission?a) Compute the even parity bits for the data bits: 1 1 0 1 0 1 1 1 and 1 0 0 0 1 0 1 0 b) Compute the odd parity bits for the data bits: 1 1 0 1 0 1 1 1 and 1 0 0 0 1 0 1 0 c) Transform the following bit string (D) into a 3 x 8 matrix and compute the two-dimensionaleven parity EDC bits. D = 1 1 0 1 0 0 1 0 1 1 1 0 0 0 1 1 0 0 1 1 1 0 1 1 d) Assume that a sender transmits <D, EDC> as shown and computed in c). Next, assume that thereceiver receives D’ and EDC’ as follows:D’ = 1 1 0 1 0 0 1 0 1 1 1 1 0 0 1 1 0 0 1 1 1 0 1 1; EDC’ = EDC, Does the received bit streamhave errors? If yes, how does the receiver detect or correct the errors and how many errors can bedetected or corrected?3).Let X=−123, n=8 (including 2 sign bit), then the complement of X is_______ .
- 1024 bytes X 1 kilobyte is equal toL={w∈{0,1}* | w starts with 1 and ends with 0}. Its complement L’={w∈{0,1}* | ________ } w starts with 0 and ends with 1 w has length 0 or 1 or starts with 0 or ends with 1 w starts with 1 or ends with 0 w has length 0 and 1 and starts with 1 and ends with 0Simplify and express the answer wi (x^((1)/(4))y^(-(1)/(8)))(x^((8)/(7))y^((1)/(5)))

