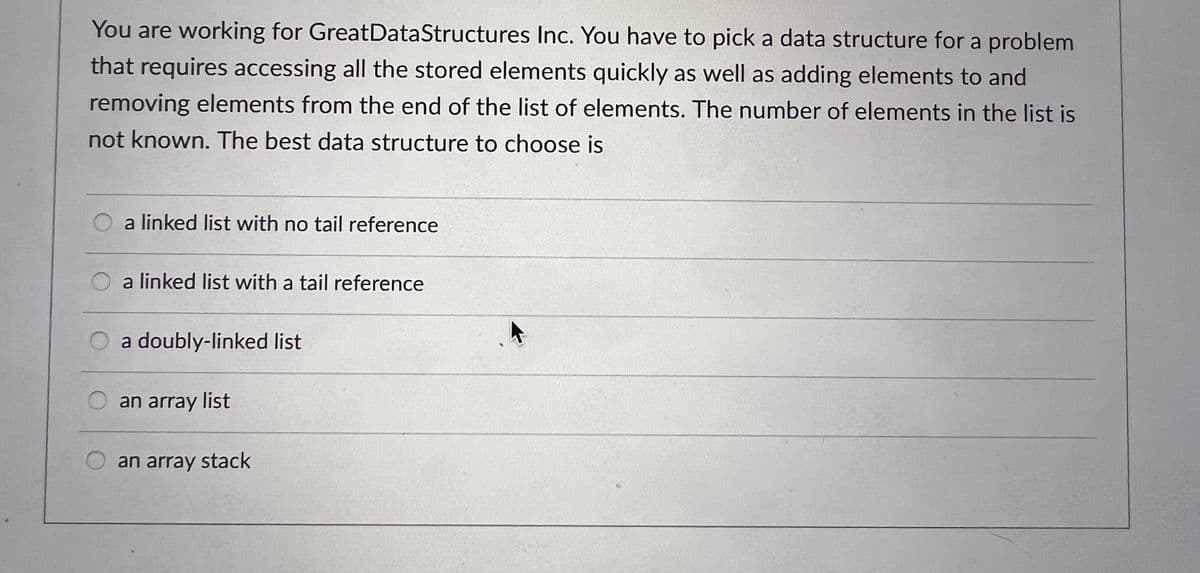
You are working for GreatDataStructures Inc. You have to pick a data structure for a problem that requires accessing all the stored elements quickly as well as adding elements to and removing elements from the end of the list of elements. The number of elements in the list is not known. The best data structure to choose is a linked list with no tail reference a linked list with a tail reference O a doubly-linked list an array list an array stack
Q: You need to develop a ticket-issuing system that can also sell bus tickets, therefore write down the…
A: Activities for the SDLC for the TICKET ISSUING SYSTEM.
Q: Do we refer to two different things when we talk about the Internet and the World Wide Web? Are the…
A: 1) Yes, the terms "Internet" and "World Wide Web" refer to two different things. 2) The Internet is…
Q: a differentiation between frequency multiplexing and temporal multiplexing (According to commuter…
A: Answer: We need to explain the frequency multiplexing and Temporal multiplexing and we will see some…
Q: Design a datapath to solve the following equation: K is the input P=(1+ 102/128) K + 32 Define how…
A: To design a datapath to solve the given equation, we need to break it down into individual…
Q: Write the Python code to find the transitive closure when given zero-one matrix. DO NOT use the…
A: Here, the goal is to mark all nodes that may be reached from each node in the graph by doing a…
Q: Phishing is a type of social engineering attack often used to steal user data, login credentials and…
A: Phishing is a type of cyberattack in which a dishonest person or business sends emails or messages…
Q: Offer methods for locating and warding off intrusions into the system.
A: Locating and preventing breaches into a computer system may be accomplished using a variety of…
Q: mber when a bit is enabled and turned on in respect to the number? What does the state of a bit…
A: In computer science, a bit is the smallest unit of information in a digital system. It is…
Q: PLEASE USE JAVA RMI PROGRAMMING Create a Java GUI program that will allow users to create accounts…
A: Java RMI (Remote Method Invocation) is an API that allows Java objects to invoke methods on objects…
Q: Should an essay be written on why networking is so important in the IT industry?
A: The importance of networking in information technology: Data is the basis for persuasive…
Q: Find out some applications of index numbers
A: Introduction: Index numbers are a useful tool in economics and finance for measuring changes in…
Q: Give the DFAs for the two languages {w| w has exactly two a’s} and {w| w has at least two b’s}. Give…
A: Answer the above question are as follows
Q: What are the three primary frequency bands utilized by wireless communication systems? Help from you…
A: Frequency Band: A frequency band is a collection of frequencies that have been designated for use…
Q: 1. The representation must be on a linear scale (not logarithmic) Linear scale means each year is…
A: Here is an example of a linear scale timeline that meets the requirements you listed:
Q: aspects of an OS are widely regarded as essential
A: The OS Aspects and essential are as follows:
Q: tures. Include ACF, PACF, and manual differencing plots in your submission. Do not use any functions…
A: Time series analysis is a statistical method for analyzing and forecasting time series data, which…
Q: Provides a thorough explanation of what a data warehouse is and how it works. For that matter, what…
A: A data warehouse is a central location where a lot of data may be stored and analysed. Applications…
Q: Given the following incorrect heap:
A: Consider the given data :
Q: Principles and philosophies of early engineering were first taught in military academies and were…
A: Principles and philosophies of early engineering were first taught in military academies and were…
Q: Is it true that applications may provide one of two distinct categories of Internet services? One…
A: No, it is not accurate to say that all internet applications fall into one of two distinct…
Q: Why do most people believe that the Internet represents the pinnacle of today's information and…
A: Definition: The abbreviation "ICT" refers to a set of technological tools and resources that are…
Q: Your task for this lab is to write a program in any language you like(c language) to determine the…
A: We have to create a program which follows the fibonacci rule and by the help of which we have ot…
Q: //Algorithm should: /*NOT destroy any of the originally even-valued node. This means that the…
A: We have to create a function DelOddCopEven based on the given algorithm.
Q: In what ways may the canvas element in HTML5 be helpful?
A: The fifth and latest HTML version, HTML5, is a markup language that facilitates the creation and…
Q: The Internet Explorer Box Model Bug and how it will affect your ability to use Internet Explorer to…
A: A connection-oriented technique connects the sender to the recipient and verifies if a communication…
Q: Provide me with a list of the most vital parts of the operating system. What this boils down to is:
A: An operating system is the program that after being initially loaded into the computer by a boot…
Q: To what extent does Windows take the initiative to solve problems, as opposed to relying on users to…
A: Answer Windows has various built-in features that can take the initiative to solve problems…
Q: design assets disposal topic from CAPS document where you can use micro teaching steps in…
A: Answer Microteaching is a teaching technique that involves practicing and teaching a specific skill…
Q: Consider a linked list whose nodes are objects of the class Node: class Node { public int data;…
A: The statement used to delete the node n2 from a linked list, given that prev references a node n1 in…
Q: Make a table showing the adjacency matrix for the following directed graph with edge costs. 2 2 3 2…
A: - We need to create an adjacency matrix for the directed graph.
Q: As a producer of personal computers, one of your primary objectives s
A: Introduction: As a producer of personal computers, the primary objective is to design and build…
Q: Write a python code to calculate the following: y= ax^3 + b Use the python input function to get…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: What distinguishes the resources that are found in libraries from those that are found in indigenous…
A: The library resources and indigenous media sources differ from one another in terms of purpose. The…
Q: Provide an example of a hierarchical task analysis that was carried out by an interface designer…
A: Interface designers use the hierarchical task analysis (HTA) technique to examine complex tasks and…
Q: What are the six benefits that would result from widespread adoption of the SQL standard?
A: Structured Query Language (SQL) is a powerful and ubiquitous database programming language. SQL…
Q: Are there advantages to using the internet for those who have physical or mental disabilities? What…
A: There are many advantages to using the internet for people with physical or mental disabilities. For…
Q: As you go into the heart of the operating system, start with the simplest activities and work your…
A: Introduction:- The operating system can be simply termed as OS. Resource Management is the process…
Q: How does the advent of new forms of electronic communication affect today's business practices in…
A: How we communicate has entirely altered because of technology in our personal and professional…
Q: a) Write a MATLAB function which takes as input any XM matrix of numbers, append a new row of zeros…
A: Explanation: We first define the function to solve as fun = @(x) log(x) - x^2 + 2;. This is the…
Q: PLEASE USE JAVA RMI AND MAVEN Create a Java GUI program that will allow users to create accounts…
A: Java RMI (Remote Method Invocation) is a Java API that provides a mechanism to create distributed…
Q: Is there a set of guidelines for creating the microkernel that runs an OS? How does this technique…
A: Here is your solution -
Q: Do you realize how many different stages there are involved in the process of establishing a website…
A: Answer is
Q: When applied to a concrete thing, what does the term "operating system" signify? Can you name the…
A: When applied to concrete thing, an operating system generally refers to software that manages…
Q: ply Prims algorithm to the graph below, starting with vertex a. Construct a table that shows the…
A: Prim's Algorithm: It is a greedy algorithm. It is used to find minimum spanning tree from given…
Q: Create a function in python called print_first_last_name that prints first and last name passed to…
A: Accordign to the information given:- We have to follow teh instruction in order to get desired…
Q: Aren't the two most important characteristics of an operating system outlined in this article…
A: An operating system has two main characteristics: resource management and abstraction.
Q: Design the following menu using VB programming: 1) For details, collect employee details and display…
A: Here, I am adding two forms - one for collecting employee details and one for displaying salary…
Q: Your job is to decrypt this intercepted message, CQNTNHRBDWMNACQNVJC, which is believed to reveal…
A: 1. To decrypt the intercepted message NEXYIYECEHTIRISNEHPK, we need to reverse the route cipher.…
Q: Do you know the number of processes that go into designing a website? extensive and in-depth…
A: Do you know the number of processes that go into designing a website?extensive and in-depth…
Q: What sorts of fundamental changes have been brought about in the process of communication as a…
A: The use of voice-to-voice communication and face-to-face communication has been surpassed by the…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- You were tasked to do programs that will illustrate the use of lists implemented using an array. One uses a sorted list, the other an unsorted list. Run the programs separately and answer the following questions. Write a program that will initially create an UNSORTED list containing the following and then run the program: Mitch Diane Jack Robbie Katherine Answer and explain the following questions below: Ifwecheckthememorylocationofeachelementinthelist,whatwoulditbe?What index represent eachelement? What happens if we add Morrie in the list? What will be its indexvalue? Whatdoesthenewlistlooklike?WheredoyouthinkMorrieshouldbeplacedand why? With the same list above (with Morrie added), delete/remove Jack. Answer and explain the following questions below: What is the new list? Identify the elements of the list and itsindex. What happened to the former location occupied byJack? Write a program that will initially create a SORTED list containing the following and then run…You are going to be asked to make a singly-linked list of singly-linked lists. How are you designing your data structure to best facilitate this design? Be sure to explain how the data is internally stored within your linked list of linked lists. (PI 1.1/ABET[1], PI 6.1/ABET[6]) #PythonWrite a C program that reads the dimensions of a 2D array and its contents from a file calledmatrix.txt. The program should construct an array of linked lists where the array represents the rowsand the linked lists represent the elements in a row. The building block of the linked lists will be astruct
- I need a C++ Program which reads the numbers till -5 was entered. After that,program will display the smallest and largest numbers and the numbers between smallestand largest. It is not allowed to use vector or array, you have to use data structures(linked list,sorting,insert item,delete item vs) sample output: Input the numbers: 5 12 53 6 9 4 18 27 88 36 45 54 -5Result: 4 18 27 88 Input the numbers: 23 97 63 15 88 21 36 45 -5Result: 97 63 15 88 21Which of the following statements regarding linked lists and arrays is correct? Group of answer choices: a. A dynamically resizable array makes insertions at the beginning of an array very efficient. b. Using a doubly linked list is more efficient than an array when accessing the ith element of a structure. c. A dynamically resizable array is another name for a linked list. d. Any type of list tends to be better than an array when there are a set number of maximum items known beforehand. e. If many deletions at any place in the structure were common, a linked list implementation would likely be preferable to an arrayANSWER THAT MCQ QUESTION IN 2 MINUTES PLEASE.. The following function reverse() is supposed to reverse a singly linked list. There is one line missing at the end of the function. /* Link list node */ struct node { int data; struct node* next; }; /* head_ref is a double pointer which points to head (or start) pointer of linked list */ static void reverse(struct node** head_ref) { struct node* prev = NULL; struct node* current = *head_ref; struct node* next; while (current != NULL) { next = current->next; current->next = prev; prev = current; current = next; } /*ADD A STATEMENT HERE*/ }
- you need to design, analyze, and implement algorithms to read in a sequence of characters from standard input and maintain the characters in a linked list with no duplicates. When you read in a previously unseen character, insert it at the front of the list. When you read in a duplicate character, delete it from the list and reinsert it at the beginning. The program implements the well-known move-to-front strategy which is useful for caching, data compression, and many other applications where items that have been recently accessed are more likely to be re-accessed. Requirements: The program should read a sequence of characters. The program should insert unseen character at the front of the list. The program should check if the character is not in the list to be inserted at the front of the list. The program should delete a duplicate character and delete it from the list and insert it at the beginning of the list. The program should check if the character is already in the list and…Old MathJax webview Old MathJax webview In Java Some methods of the singly linked list listed below can be implemented efficiently (in different respects) (as opposed to an array or a doubly linked list), others not necessarily which are they and why? b. Implement a function to add an element before the first element. c. Implement a function to add an item after the last one element. d. Implement a function to output an element of the list. e. Implement a function to output the entire list. f. Implement a function to output the number of elements. G. Implement a function to delete an item. H. Implement a function to clear the entire list. I. Implement functionality to search for one or more students by first name, last name, matriculation number or course of study. J. Implement functionality to sort the records of the student, matriculation number and course according to two self-selected sorting methods.Modify the given code to move the string from leftmost side to the rightmost side of the screen (no trails). Given Code: .model small.stack.data strg db 'Mapua$' row db 12 col db 0.codemain proc mov ax,@data mov ds,ax mov ah,6 mov al,0 mov bh,7 mov ch,0 mov cl,0 mov dh,24 mov dl,79 mov cx,40again:push cx mov ah,2 mov bh,0 mov dh,row ;row mov dl,col ;col int 10h mov ah,9 mov dx,offset strg int 21h inc col mov cx,10 push cx mov cx,0ffffhx: loop x pop cx loop y pop cx loop again mov ah,4ch int 21hmain endpend main
- Write a C program that will initially create an UNSORTED list containing the following and then run the program:MitchDianeJackRobbieKatherine Answer and explain the following questions below:a) If we check the memory location of each element in the list, what would it be? What index represent each element?b) What happens if we add Morrie in the list? What will be its index value? c) What does the new list look like? Where do you think Morrie should be placed and why? With the same list above (with Morrie added), delete/remove Jack. Answer and explain the following questions below:a) What is the new list? Identify the elements of the list and its index.b) What happened to the former location occupied by Jack?I need to design, analyze, and implement algorithms to read in a sequence of characters from standard input and maintain the characters in a linked list with no duplicates. When read in a previously unseen character, insert it at the front of the list. When read in a duplicate character, delete it from the list and reinsert it at the beginning. The program implements the well-known move-to-front strategy which is useful for caching, data compression, and many other applications where items that have been recently accessed are more likely to be re-accessed. The program should read a sequence of characters and should insert unseen character at the front of the list. The program should check if the character is not in the list to be inserted at the front of the list. The program should delete a duplicate character and delete it from the list and insert it at the beginning of the list. The program should check if the character is already in the list and delete the character from the list…The following are the operations that you can do using a single linked list. Choose only one operation then create the algorithm and simulate. The attached Rubric will be used in evaluating the activity. 1. Delete a particular node in a single linked list 2. Delete the first node of a single linked list 3. Insertion after a given node of a single linked list 4. Insertion at a given position in a single linked list 5. Insertion before a given node in a single linked list 6. Reverse a single linked list EX: Delete the last node of a single linked list Problem" Deletion of the last node in a single linked list Algorithm" Step 1: if HEAD = NULL Write UNDERFLOW Go to Step 8 Step 2: SET PTR = HEAD Step 3: Repeat Steps 4 and while PTR à NEXT = NULL Step 4: SET PREPPTR = PTR Step 5: SET PTR =PTR à NEXT [End of loop] Step 6: SET PREPTR à NEXT = NULL Step 7: FREE PTR Step 8: EXIT…

