Your goal is to translate the following C function to assembly by filling in the missing code below. To begin, first run this program-it will fall to return the required data to the test code. Next, write code based on the instructions below until running it produces correct. 1 void accessing memory ex 1(void) { 2 memory address 0x10040x5678; 3) Data This allocates space for data at address Ox1004 To make it testable, it's also given a name section bss address(ec1004) memory address ex1004: space 2 global memory address 0x3004 Code accessing nenory_ex_11 -global accessing y Witte a short snippet of assembly code places the value Ox5678 in memory location Ox1004, then returns to the calling test function
Your goal is to translate the following C function to assembly by filling in the missing code below. To begin, first run this program-it will fall to return the required data to the test code. Next, write code based on the instructions below until running it produces correct. 1 void accessing memory ex 1(void) { 2 memory address 0x10040x5678; 3) Data This allocates space for data at address Ox1004 To make it testable, it's also given a name section bss address(ec1004) memory address ex1004: space 2 global memory address 0x3004 Code accessing nenory_ex_11 -global accessing y Witte a short snippet of assembly code places the value Ox5678 in memory location Ox1004, then returns to the calling test function
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.5: Variables And Declaration Statements
Problem 10E
Related questions
Question
C coding
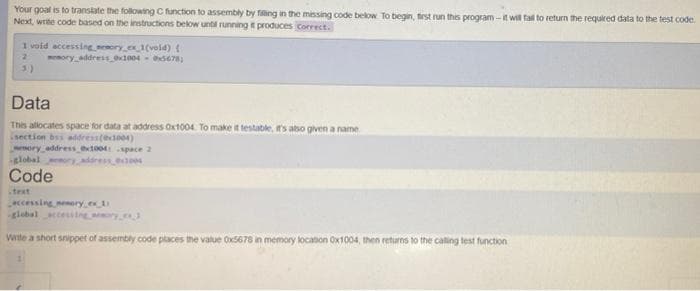
Transcribed Image Text:Your goal is to translate the following C function to assembly by filling in the missing code below. To begin, first run this program-it will fall to return the required data to the test code
Next, write code based on the instructions below until running it produces correct.
1 void accessing memory ex 1(void) {
2
memory address 0x10040x5678;
3)
Data
This allocates space for data at address Ox1004 To make it testable, it's also given a name
section bss address(ec1004)
memory address ex1004: space 2
global
y
0x3004
Code
accessing nesory ex 11
-global accessing y
Witte a short snippet of assembly code places the value Ox5678 in memory location Ox1004, then returns to the calling test function
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr