- Your task is to read a file containing arithmetic instructions such as 3+4 4 - 10 7 11 Each instruction contains an integer, an operator (+, -, or *), and another integer. Return a list of the results. If there is any error, raise an IOError. arithmetic.py 1 ## 2 # Reads a file containing arithmetic expressions and returns a list of 3 # the results after computing each expression. 4 # @param filename the file name 5 # @return a list of results 6 # 7 def read(filename) : 8 9
- Your task is to read a file containing arithmetic instructions such as 3+4 4 - 10 7 11 Each instruction contains an integer, an operator (+, -, or *), and another integer. Return a list of the results. If there is any error, raise an IOError. arithmetic.py 1 ## 2 # Reads a file containing arithmetic expressions and returns a list of 3 # the results after computing each expression. 4 # @param filename the file name 5 # @return a list of results 6 # 7 def read(filename) : 8 9
Chapter14: Files And Streams
Section: Chapter Questions
Problem 2E: Create a program named FileComparison that compares two files. First, use a text editor such as...
Related questions
Question
Attached The contents of input.txt file:
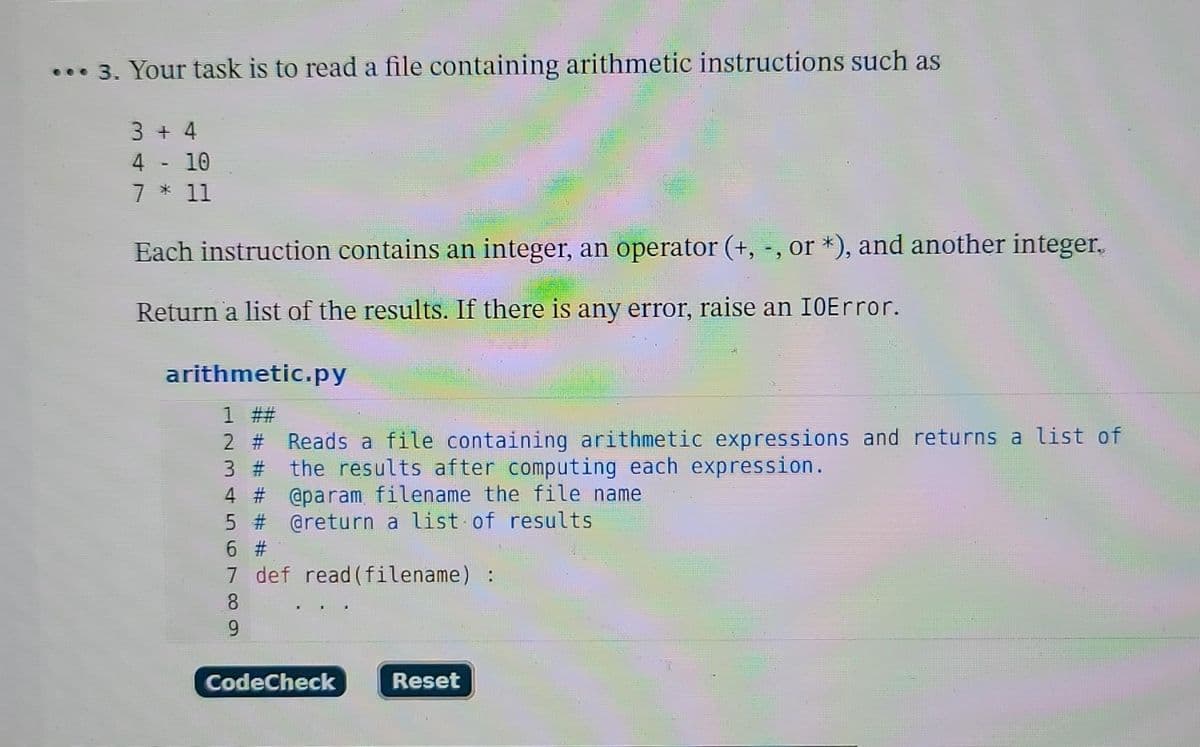
Transcribed Image Text:3. Your task is to read a file containing arithmetic instructions such as
3 + 4
4 - 10
7 * 11
Each instruction contains an integer, an operator (+, -, or *), and another integer.
Return a list of the results. If there is any error, raise an IOError.
arithmetic.py
1 ##
2 # Reads a file containing arithmetic expressions and returns a list of
3 # the results after computing each expression.
4 # @param filename the file name
5 # @return a list of results
6 #1
7
def read(filename) :
8
9
CodeCheck
Reset
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr