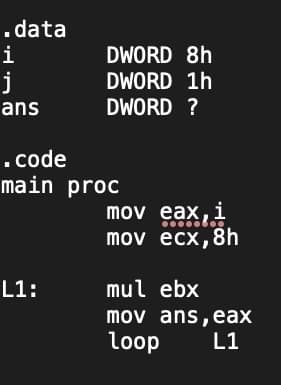
.data i j ans DWORD 8h DWORD 1h DWORD ? . code main proc L1: mov eax, i mov ecx, 8h mul ebx mov ans, eax loop L1
Q: Program below repeatedly accept real numbers until zero is entered. The output of the program is the…
A: Here is the complete java code of above problem. See below step.
Q: In python, write a program that receives an integer, greater than or equal to 2, from the user and…
A: What is Python? Python is a widely used high-level, general-purpose programming language for…
Q: What makes address alignment such a crucial concept in computer science?
A: Introduction: Unaligned memory access is the access of data with a size of N number of bytes from an…
Q: s there a better way to defend against DDOS attacks?
A: One can defend against a DDOS attack: 1) We can adopt a CDN content delivery network Solution, or…
Q: The transport layer requires packetizing from the network layer for a number of reasons. For some…
A: Networking layer: The network layer in the OSI architecture is the layer that permits the host to…
Q: How do logical and linear addresses differ from one another, and how do they connect to one another?
A: Introduction What are logical and linear addresses, and how do they relate to one another?
Q: You found an exciting summer job for five weeks. It pays, say, $15.50 per hour. Suppose that the…
A: I have solved your required logic in C++ and defined comments for each line , kindly check it out ,…
Q: Can I have a flowchart for below C program code please? #include #include #include int…
A: Flowchart for the provided C code is given below:
Q: The solution in its simplest form using C++?? ^^^^^^^^^^^^^^^^^^^^
A: Coded in C++
Q: (c) Design a Turing Machine that accepts all binary strings in the form of a palindrome. (d) Use the…
A: c) Algorithm: If no input is received, proceed to the final state and stop. If the input is "a,"…
Q: Countermeasures should be stated as specific plans of action to manage and reduce risks associated…
A: A way or thing to cancel out or make up for something The most well-known way for a doctor to get…
Q: We'll go over how to create a botnet and use it in a DDoS attack in this article.
A: A network of computers that have been hacked and that may be used to carry out criminal behavior is…
Q: typing the response listed here gives an error. Exited with return code 1. Traceback (most recent…
A: Please find the answer below
Q: . How many syntax errors in the following code: (assume all libraries are ncluded) void showq (queue…
A: Given code lines are all in c++ language.
Q: at are the prevailing computer science network trends to
A: Introduction: Investigate cutting-edge computer science technologies such as artificial…
Q: Describe the operation of Google Dorks and its original purpose.
A: Google Docs Google Docs is a free Web-based application in which reports and calculation sheets can…
Q: How does an XSS attack operate and what is it?
A: An XSS Attack : Attackers often provide a malicious link to a user and get them to click on to start…
Q: Given how important the network is to the users of the firm, do you have three protocols that are…
A: 1)IMAP(Internet Message Access Protocol) 2)POP3(Post Office Protocol 3) 3)DNS(Domain Name System)…
Q: Which kind of routing path—static or dynamic—would you employ for a simple network? What makes you…
A: In the given question Static routes are configured in advance of any network communication. Dynamic…
Q: 14. A rectangular box has the dimensions shown. (a) Determine the angle BAC to the nearest degree.…
A: According to the information given:- We have to follow the instruction in order to get the angle BAC…
Q: If a client and a server are placed far apart, we may see network latency dominating overall…
A: Physical distance plays a very small role in network latency.
Q: Describe the operation of Google Dorks and its original purpose.
A: Introduction: Google dorks: Google Dorks, commonly known as Google Hacking, is an online subculture.…
Q: How many line(s) should be changed/added to make class Res-Visitors a emplate class? nswer: class…
A: Class template which refers to the template that are used to generate the template classes. You…
Q: The process of decomposing a relations into two relations is called: Select one: O Denormalization O…
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: What do you think the definition of the word "computer" is?
A: Introduction: A computer is an electronic device that can be programmed to manipulate data or…
Q: the SPI Firewall working with the FTP
A: Firewall: It is a piece of software used to prevent unauthorized access and access to unauthorized…
Q: Given that the network is heavily relied upon by the users of the company, can you please mention…
A: Rules and criteria for transmitting data are outlined in protocols, Each step and process of…
Q: Describe the relationship between the terms dependability and availability in the context of a…
A: Obsolescence and Depreciation: Depreciation is the a term used to describe the decline in fixed…
Q: Does one person have the ability to plan a distributed denial of service attack?
A: The above question is solved in step 2 :-
Q: DDoS attacks can be started by a single individual, but how do they operate?
A: INTRODUCTION: A DDoS attack is an effort to bring down a network or web server by flooding it with…
Q: In Python, ask user to enter a string,e.g., Today is a good day. Pass the string to a function…
A: First Ask user for string and store it in some variable. Now call function and store function result…
Q: How can a hash value be protected for message authentication? Can a MAC algorithm be broken without…
A: A hash value can be protected for message authentication by using a MAC algorithm. A MAC algorithm…
Q: Include the for loop below in a small program and complete the program. The loop should execute 10…
A: Since there is no language asked in problem. I am using c++ language. See below step for code.
Q: Design Turing Machines using JFLAP to compute the fol lowing function where x is an integer…
A: q0 has 0 remainder q1 has 1 remainder q2 has 2 remainder q3 has 3 remainder q4 has 4 remainder So,…
Q: Describe the topologies and methods used in various network designs. Describe the topologies and…
A: The structure of services and network devices to meet the client devices' connectivity needs is…
Q: Neumann architecture from other types of desi
A: Architecture by Von NeumannThe underlying design that almost all digital computers have been built…
Q: Write a while loop that asks the user for input and stops only when the user types in the string…
A: - Solving the first question only because of guidelines. - We have to write a while loop with…
Q: In what ways do networks get used in schools?
A: networks get used in schools: What kinds of networks are employed in educational institutions? is…
Q: Attacks that cause simultaneous destruction of several services by a single individual are known as…
A: Introduction: The question that has to be answered is how a DDoS assault works. The inquiry is…
Q: What is the output of the below pseudocode? Integer a Set b=1 for(each a from 1 to 3) print b;…
A: We need to find the correct output of the code. See below steps.
Q: List the databases that hold your data. How is each database's data saved, and how often may you…
A: Introduction: The idea of the database for the average personDatabase uses in daily life include: In…
Q: I/O interfaces have a role, but what does it mean specifically?
A: The answer of this question is as follows:
Q: What does it mean for the transport layer to offer the network layer a packetizing service? What is…
A: Packetizing is the process of encapsulating the data received from the upper layers of the…
Q: What makes address alignment such a crucial concept in computer science?
A: Given: Importance of address alignment is questioned.Address alignment: Information saved in memory…
Q: When it comes to operating systems, a mainframe and a laptop are quite unlike. How are they…
A: system analyst A system analyst is someone who gathers and compiles data on the programme. The user…
Q: of service (DDoS) attac
A: Solution - In the given question, we have to explain denial of service (DDoS) attacks and also tell…
Q: Provide the similarities and differences between the following: systems engineering, engineering of…
A: The traditional scope of engineering embraces the conception, design, development, production and…
Q: Assumptions... • Alphabet Σ = {a,b} f(w) = wR o where wΕΣ+ To do in this exercise... Construct a…
A: The Turing Machine is below:
Q: Which kind of routing path-static or dynamic-would you employ for a simple network? What makes you…
A: When using the basic network, static routing is excellent. The greatest solution for users of very…
Q: You found an exciting summer job for five weeks. It pays, say, $15.50 per hour. Suppose that the…
A: C++ Some computer languages are created with a particular objective in mind. Like Java, which was…
Step by step
Solved in 2 steps

- uint16_t data = wiringPiI2CReadReg16(adc, 0x00); low = (data & 0xFF00) >> 8; high = (data & 0x00FF) << 8; value = (high | low)>>4; return value; I know this stables the value some how but how and why Please give explanationQuestion 4 lstBox.Items.Add(FormatNumber(1234.856,1)) Full explain this question and text typing work only thanks"""return the haversine distance between the two locations.The location should be a tuple of (latitude, longitude)https://en.wikipedia.org/wiki/Haversine_formulaIf you use code from a website as the basis for this function, besure to document that website here::param location1::param location2::return: haversine distance between two locations, measured in miles.""" FILES LOOK LIKE THISID,City,State,Latitude,LongitudeA45419E,Plattsburgh,NY,44.704021,-73.471148A19312D,Aiken,SC,33.554433,-81.69588A90172S,Tuscaloosa,AL,33.170238,-87.616169A19394D,Alexandria,VA,38.819853,-77.059645A27218D,Pittsburgh,PA,40.47441,-79.950968A68626D,Meadville,PA,41.611599,-80.114891A17494D,Allentown,PA,40.602658,-75.469236A86034S,Tonawanda,NY,42.99704,-78.878659A45142D,Asheville,NC,35.602711,-82.567281A38298S,Atlanta,GA,33.844371,-84.47405A14497Y,Roswell,GA,34.055198,-84.370475A25954D,Austin,TX,30.326374,-97.771258B46374X,Fairhope,AL,30.480713,-87.861306B52199S,Cedar…
- No plagarism please. Upvote guarenteedI WANT THIS PROGRAM IN JAVA LANGUAGE OOP KINDLY USE GUI eShop Create/View/Edit ProfileAdmin account for notifications/viewable informationview itemscontact seller (chatbox)add to cartview cartcheckoutmake paymentsview purchase historyview product viewing historyreminder to checkoutGroup Members Click for more optionsRegex, APIs, BeautifulSoup: python import requests, refrom pprint import pprintfrom bs4 import BeautifulSoup complete the missing bodies of the functions below: def companies(website):"""Question 6- Acces the table at the provided website:'https://en.wikipedia.org/wiki/Companies_listed_on_the_New_York_Stock_Exchange_(C)'- Parse through it and retrieve the names of all companies in the site that~ Are based in the US~ Have an acronym anywhere in their name~ (Let us define 'acronym' as any two or more consecutive capital letters)Args:string (website)Returns:list (list of company names)>>> web1 ='https://en.wikipedia.org/wiki/Companies_listed_on_the_New_York_Stock_Exchange_(C)'>>> web2 ='https://en.wikipedia.org/wiki/Companies_listed_on_the_New_York_Stock_Exchange_(T)'>>> companies(web1)['CACI','CAI International, Inc.','CARBO Ceramics Inc.',...'CYS Investments, Inc.']>>> len(companies(web1)) 27>>> len(companies(web2))23"""pass…
- 1. Make a WPF Application using C# in Visual Studio and name it as MTYourFirstnameLastname. 2. Design and implement an app having multiple windows that displays and manages information of players of different sports – Ice Hockey, Basketball, and Baseball. 3. The app maintains generic collections of these players. 4. The app can read, add, update, and delete the data. 5. Use LINQ whenever you need to read or fetch data. 6. The app should come preloaded with 5 pieces of data for each collection. 7. The main window should have three buttons (View Ice Hockey Players, View Basketball Players, View Baseball Players) that displays a new window for that particular sports player. 8. Each new window has a ListBox that gets populated with the player names. 9. On selecting a name from the ListBox, display the data in the TextBoxes. Faculty of Applied Science & Technology Page 2 of 3 10. Add buttons to insert/update/delete data for that particular sports player. • Show a message box with an…Please written by computer source 1. Make a WPF Application using C# in Visual Studio and name it as MTYourFirstnameLastname. 2. Design and implement an app having multiple windows that displays and manages information of players of different sports – Ice Hockey, Basketball, and Baseball. 3. The app maintains generic collections of these players. 4. The app can read, add, update, and delete the data. 5. Use LINQ whenever you need to read or fetch data. 6. The app should come preloaded with 5 pieces of data for each collection. 7. The main window should have three buttons (View Ice Hockey Players, View Basketball Players, View Baseball Players) that displays a new window for that particular sports player. 8. Each new window has a ListBox that gets populated with the player names. 9. On selecting a name from the ListBox, display the data in the TextBoxes. Faculty of Applied Science & Technology Page 2 of 3 10. Add buttons to insert/update/delete data for that particular sports…Solve it using viual studio C++ at enrty level please. Thank you
- T or F Number fields store values that represent quantities, measurements, and scores, for example. T or F The introduction should be the principal section of a formal report. T or F The Import Spreadsheet Wizard can help you import data from Excel into a new Access table. Which of the following properties can you set for a Short Text field? Format Decimal Places Default Value Input Mask What type of graphic illustrates changes in data over time? Line chart Flowchart Pie chart Table6 Cell Phone PackagesCell Solutions, a cell phone provider, sells the following packages:300 minutes per month: $45.00 per month800 minutes per month: $65.00 per month1500 minutes per month: $99.00 per monthThe provider sells the following phones (a 6 percent sales tax applies to the sale of a phone):Model 100: $29.95Model 110: $49.95Model 200: $99.95Customers may also select the following options:Voice mail: $5.00 per monthText messaging: $10.00 per monthWrite an application that displays a menu system. The menu system should allow the userto select one package, one phone, and any of the options desired. As the user selects itemsfrom the menu, the application should show the prices of the items selected.def wear_a_jacket(us_zip:str) -> bool: This function should use https://openweathermap.org/ API (user account required) to collect its weather information. The purpose of this function is to inform you if you should wear a jacket or not. It will be given a US zip code. This function should query the API to figure out the current temperature in the region associated with the US zip code. If the temperature is less than 60 degrees Fahrenheit (main.feels_like float: This function should use https://openweathermap.org/ API (user account required) to collect its weather information. This function should retrieve the historical temperature in Fahrenheit at a particular US location. You will be given a number of days, hours, and minutes and a United States zip code. The time values given are the cumulative total time in the past minus the current time, you should retrieve the historical temperature (current.temp). In other words, if the parameter days is 4 hours is 0 and minutes is 5.…



