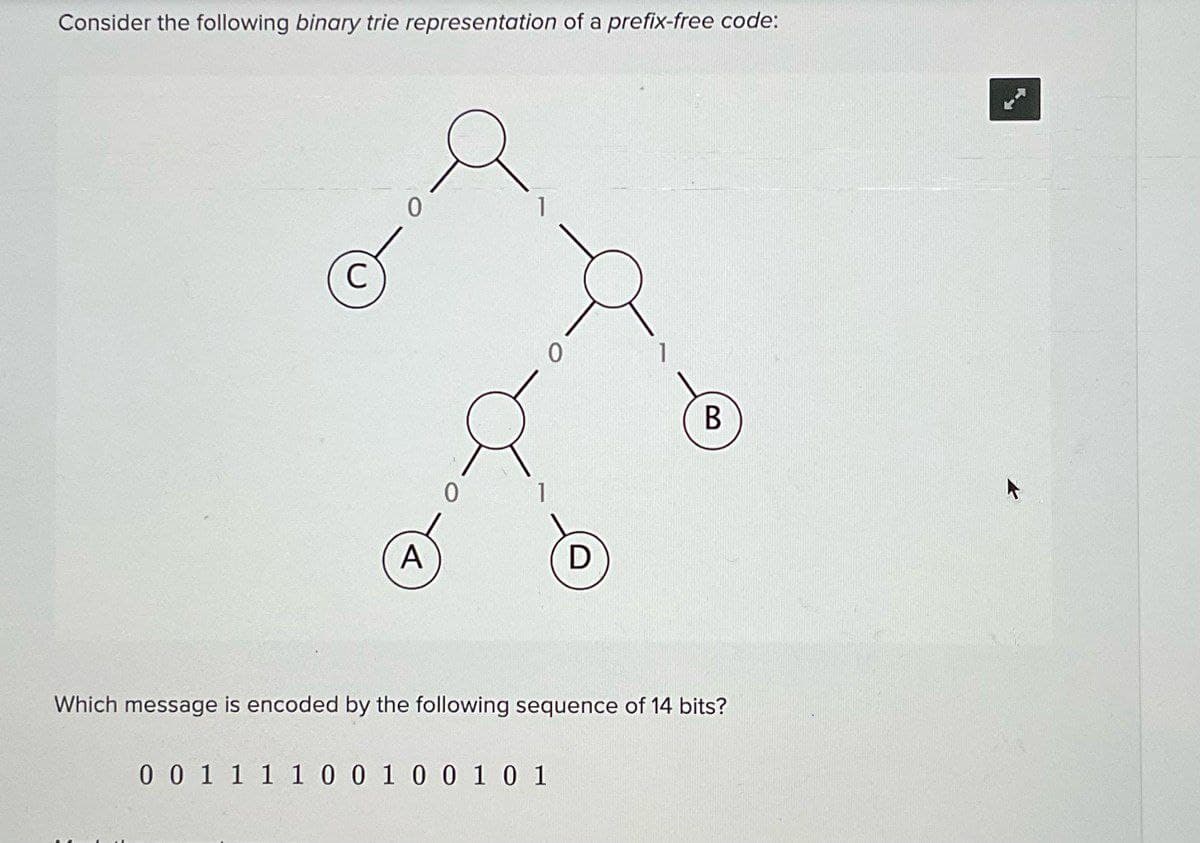
0 A 0 0 D 0 0 1 1 1 1 0 0 1 0 0 1 0 1 B Which message is encoded by the following sequence of 14 bits?
Q: What are the relative advantages of flat staffing versus gradual staffing?
A:
Q: 29. The number of combinations Chr of taking r objects out of n objects is given by: n! r!(n-r)! Cnr…
A: To find the number of combinations(C59,5 * C35,10 in the powerball lottery. Factorial(n) is a…
Q: Advanced Question: Write the following code segment in MARES' assembly language Sol. If x>1 then z =…
A: Introduction: Below output the following code segment in MARS' assembly language Machine code is…
Q: What is the difference between status meetings and decision meetings? Should they always be kept…
A: Status meetings are periodically scheduled events at different levels in which information relating…
Q: Briefly describe the issues involved in using ATM technology in LANS.
A: ATM stands for Asynchronous Transfer Mode. To transfer data from source to destination, it uses ATM…
Q: Discuss the functions of each SONET layer.
A:
Q: What does ESP add to the IP packet?
A: Since utilizing encryption without authentication is risky to any data as we all know .…
Q: During Eid, it is a tradition for every father to give his children money to spend on entertainment.…
A: The above question is solved in step 2 :-
Q: Convert the following decimal fractions to binary with a maximum of six places to the right of the…
A: Note: As per our company policy, the answers of the first three subparts are given in this solution.…
Q: Briefly describe the services provided by the data link layer.
A:
Q: This assignment is a review of loops. Do not use anything more advanced than a loop, such as…
A: c++ code #include<iostream> /* for cout, cin */ #include <stdlib.h> /* srand, rand…
Q: (Coin Tossing) Write a program that simulates coin tossing. For each toss of the coin theprogram…
A: (Coin Tossing) Write a program that simulates coin tossing. For each toss of the coin theprogram…
Q: Can the system under consideration be represented as an actor? Justify your answer.
A: Answer : No , system under consideration not be represented as an actor.
Q: 10. Two trigonometric identities are given by: (a) cos²x-sin²x=1−2 sin² x (b) tan x sin x-2 tan x…
A: ANSWER:-
Q: 9. What is the difference between a session and a connection in SSL?
A:
Q: class Solution { public: }; char repeated Character(string s) { } unordered_set u; char ans;…
A: Introduction The given code snippet is a class in which we are finding the repeated character of…
Q: rite a program that asks the user to enter an integer consisting of 4 digits only, and check w many…
A: Code is given below #include <iostream>using namespace std;int main() { int num,…
Q: ion needed code in java Priority: I/P: Process names, burst times, priority values O/P: Process…
A: Introduction: Below the java program Priority: I/P: Process names, burst times, priority values…
Q: A message is made of 10 numbers between 00 and 99. A hash algorithm creates a digest out of this…
A:
Q: 3. For the RSA algorithm with a large n, explain why Bob can calculate d from n, but Eve cannot.
A:
Q: There are three major differences between software products and other industrial products. 1.…
A: Question 1. 1. Software products are intangible, while other industrial products are tangible. 2.…
Q: mov edx,1 mov eax,7FFFh cmp eax,8000h
A: The answer is
Q: Write a 32-bit assembly program and flowchart that clears the screen, locates the cursor near the…
A: CODE SEGMENT START: ASSUME CS:CODE MOV AX,0600H ;06 TO SCROLL & 00 FOR FULLJ SCREEN MOV…
Q: Q6/ If XY'+Y=X+Y the correct answer O None of them OX'Y'Z+XY=Z+XY XYZ+X'+Y=Z+XY O XY'Z'+Y+Z=X+Y+Z…
A: Option A none of them is correct
Q: 8. Given the following MIPS assembly fragment: $s0, $s2, Exit $s0, $s1, Process $s2, $s3, Exit add…
A: Hello student Answer will be given as per my best of knowledge
Q: hen I tried to do it on my Visual Studio 2022 of what I did on my program code it gave me about 105…
A: JAVA PROGRAM
Q: There are three major differences between software products and other industrial products. 1.…
A: ANSWER:-
Q: It is clear that a software development project carried out by a software house for a specific…
A: Software development It alludes to a bunch of software engineering exercises committed to the most…
Q: Consider a dynamic partitioning scheme. Show that, on half as many holes as segments. average, the…
A:
Q: A F₁ = xy + xy B. F₂ = xyz + xy + xyz F₂ = C. xyw+x(wz+wz)
A: As per our guidelines, we are supposed to answer only 1st three parts. kindly repost the remaining…
Q: Write a function that returns True if two arrays, when combined, form a consecutive sequence. A…
A: Algorithm - Take input from the user. Now use the below logic - c = a + b x,y =…
Q: When setting permissions on a file, we can give an individual user ownership of a file using which…
A: in linux, When setting permissions on a file, we can give an individual user ownership of a file…
Q: Directories can be implemented either as "special files" that can only be accessed in limited ways,…
A: Introduction Directories are the areas utilized for putting away the files in the PC system.
Q: The caret, when found at the start of a character set, is the equivalent to "not" in RegEx. The…
A: In this problem, we need to design the code in the Python programming language. Input - String…
Q: What is the maximum number of callers in each cell in an IS-95 system?
A: Interim Standard 95 (IS-95): It is a 2nd generation (2G) mobile telecommunications standard based…
Q: What is the difference between status meetings and decision meetings? Should they always be kept…
A:
Q: Provided the problem statement below, which of the following algorithms will solve the problem? A…
A: Option (a) is incorrect since the algorithm is not passing any arguments to the CalcAve and…
Q: In the tablet media query, create a new style rule for the article element that sets the width to…
A:
Q: (a) How should the description in Problem 5.30 (a) be written to have the same behavior when the…
A: In verilog, (<=) operator is termed as non-blocking assignment operator.In this,the assignment…
Q: Show how STS-9's can be multiplexed to create an STS-36. Is there any extra overhead involved in…
A: Introduction In this question, we are asked to show how STS 9 s can be multiplexed to create an STS…
Q: Define random access and list three protocols in this category.
A:
Q: Find out which of the following statements are TURE or FALSE: 1. In the addition of two signed…
A: A signed integer is a 32-cycle datum that encodes an integer in the reach [-2147483648 to…
Q: Describe how testing activities can be initiated well before implementation activities. Explain why…
A: Testing: We ought to check out at this in extraordinarily more direct words for better awareness.…
Q: Compare and contrast byte-oriented and bit-oriented protocols. Which category has been popular in…
A:
Q: How does IPSec create a set of security parameters?
A:
Q: Write Massey's Algorithm for Binary BCH Decoding
A: Massey's Algorithm for Binary BCH Decoding is:-
Q: Please attach a picture,I need downloadable images as an answer. The RL can be implemented without…
A:
Q: 1.10 LAB: Warm up: Basic output with variables This zyLab activity prepares a student for a full…
A: Here I have taken input from the user and stored it into a variable. Next, I have printed the number…
Q: Make a brief (4-7 sentence) argument for or against starting a cyber forensics division at a real…
A: The above question is solved in step 2 :-
Q: What is the difference between connectionless and connection-oriented services? Which type of…
A: Introduction: Both Connection-oriented service and Connectionless service are utilized for the…
Step by step
Solved in 2 steps with 1 images

- A bit stream 010011101 is transmitted using the standard CRC method. The generator polynomial is x ^ 3 + x . What is the actual bit string transmitted?Suppose a binary message word is to encoded using a repetition code where every bit is to be repeated thrice. Which of the ff received word is free of any error 1. 101 101 101 101 2. 111 001 000 111 3. 111 101 111 000 4. 111 000 111 000A bit stream 11011001 is transmitted using the standard CRC method. The generator polynomial is x^3+x. (A.) Compute for R or the CRC code; (B.) Determine M and show solutions.
- In an 8-bit binary number, which is the most significant bit (MSB)? What is the decimal representation of each of the following unsigned binary integers? 00110101 b. 10010110 c. 11001100 What is the sum of each pair of binary integers? 10101111 + 11011011 10010111 + 11111111 01110101 + 10101100 Calculate binary 00001101 minus 00000111. How many bits are used by each of the following data types? word doubleword quadword double quadword What is the minimum number of binary bits needed to represent each of the following unsigned decimal integers? 4095 65534 42319 What is the hexadecimal representation of each of the following binary numbers? 0011 0101 1101 1010 1100 1110 1010 0011 1111 1110 1101 1011 What is the binary representation of the following hexadecimal numbers? 0126F9D4 6ACDFA95 F69BDC2A Whatistheunsigneddecimalrepresentationofeachofthefollowinghexadecimalintegers? 3A 1BF 1001…Use Huffman code to demonstrate that a variable length encoding scheme can be used to compress the following message: rammer_jammer_yellow_hammer_give_them_h_alabama How many bits were saved over a MINIMAL FIXED LENGTH encoding scheme?Consider the following message M=1010001101. The cyclic redundancy check (CRC) for this message using the divisor polynomial x5 + x4 + x² + 1 is?
- Generator polynomial G(x) = X5+X3+X+1 Message Polynomial M(x) = X9+X7+X6+X2+1 how to find total number of transmitted bit and Message bit for M(x) (n-k)Consider a (7,4) code with generator matrixG=[1 1 0 1 0 0 00 1 1 0 1 0 01 1 1 0 0 1 01 0 1 0 0 0 1 ] , Encode the messages 1110, 1010, 0001.How many bit strings of length 10 contain a) exactly four 1s? b) at most four 1s? c) at least four 1s?
- Given the dataword 11100101 and the divisor 11011a. Show the generation of the codeword at the sender side (Using Binary Division).b. Show the checking of the codeword at the receiver side (assume no error)What are the CRC bits (R) associated with the payload containing first four bit 1101 and last four bit is the last digit of your reg number (i.e. 5, payload = 1101 0101). Suppose that the 4-bit generator (G) is 0101, and r = 3A bit stream 10011101 is transmitted using CRC method. The generator polynomial is x^3 + 1. Show the actual bit string transmitted. Suppose the third bit from the left is inverted during transmission. Show that this error is detected at the receivers end.

