1) Here is a numerical expression in C: x << 1 containing an unknown number x. If the value of the whole expression x << 1 ) is 42, what is the value of x?
1) Here is a numerical expression in C: x << 1 containing an unknown number x. If the value of the whole expression x << 1 ) is 42, what is the value of x?
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.6: A Case Study: Radar Speed Traps
Problem 3E
Related questions
Question
These are bitwise operations using C syntax
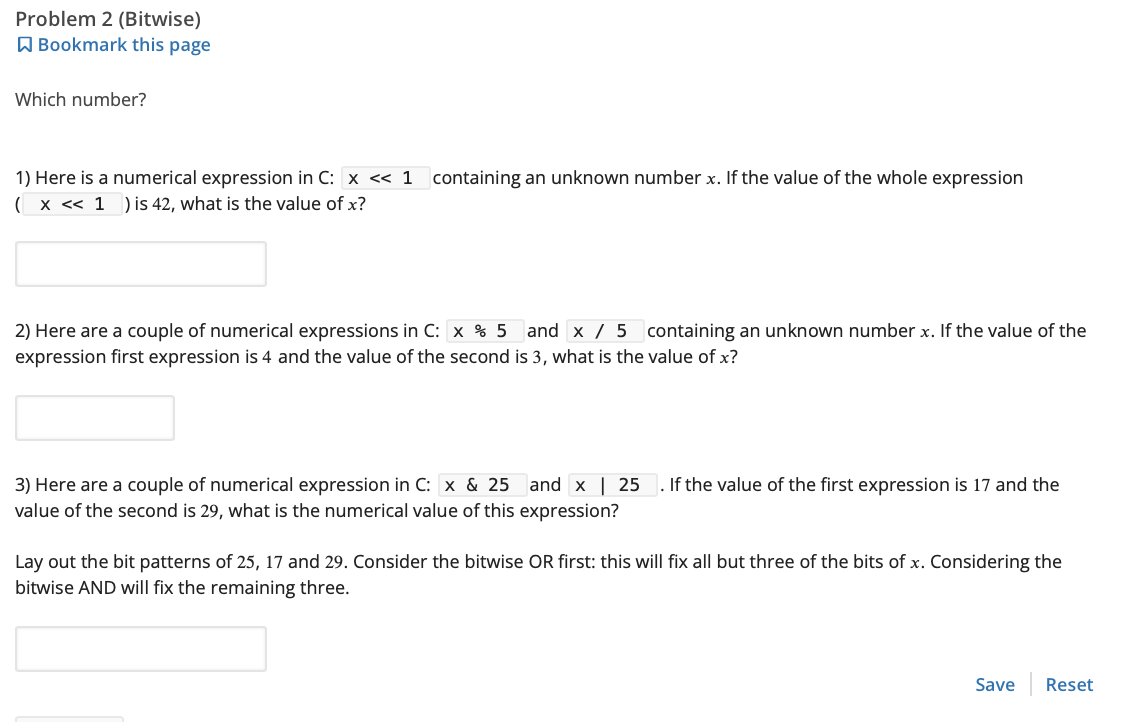
Transcribed Image Text:Problem 2 (Bitwise)
Bookmark this page
Which number?
1) Here is a numerical expression in C: x << 1 containing an unknown number x. If the value of the whole expression
( x << 1 ) is 42, what is the value of x?
2) Here are a couple of numerical expressions in C: x % 5 and x 5 containing an unknown number x. If the value of the
expression first expression is 4 and the value of the second is 3, what is the value of x?
3) Here are a couple of numerical expression in C: x & 25
value of the second is 29, what is the numerical value of this expression?
and x | 25 . If the value of the first expression is 17 and the
Lay out the bit patterns of 25, 17 and 29. Consider the bitwise OR first: this will fix all but three of the bits of x. Considering the
bitwise AND will fix the remaining three.
Save Reset
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr