(1) Show the 3-CNF formula for which R builds the following graph. P -P T S -P 0 (P^Q ^T) V (P^Q ^S) V (T ^Q ^S) O (P V QVT) A (PVQVS) A (TV Q V S) O (PAQAT) V (P AQ AS) V (TA QAS) O (PV QVT) A (PV QV S) A (TV QV S) -S S T -T S
Q: A student is taking a test on n different subjects. For each iith subject they have already answered…
A: In this question we have to write a code to determine the maximum number of subjects a student can…
Q: 6.3B-3. Multiple Access protocols (3). Consider the figure below, which shows the arrival of 6…
A: In Ethernet networks, the CSMA/CD network protocol is used to control access to a common…
Q: In a database, a data file is a/n ______. a. collection of related records b. index of the…
A: There are two multiple choice questions about the database and we have to answer them.
Q: In Kotlin, Write a recursive function with an expression body that takes an Int n and returns a list…
A: Here, the task mentioned in the question is to write a Kotlin program to write a recursive function…
Q: Make a daycare website, with html, css, and js. Use this image for an example. Make the website…
A: Welcome to Dare to Dream Child CareAt Dare to Dream Child Care, we believe in nurturing the dreams…
Q: Refer to image and make sure to code in a statement that outputs an example!
A: The objective of the question is to write a Lisp program that solves the Missionaries and Cannibals…
Q: Binary trees. In this problem the height of a tree is defined as the number of the nodes, including…
A: Binary trееs arе fundamеntal data structurеs usеd in various computеr sciеncе applications,…
Q: Compute the dominator tree for the control flow graph given below
A: A dominator tree is a tree structure that represents the dominance relationships between nodes in a…
Q: AH B C D I a. List all pairs of processes that run concurrently. b. List the ordered pairs of…
A: The multiple processors execute instructions simultaneously for better performance is called…
Q: I have seen the library so please dont send me it Show that any two rows of a matrix can be…
A: Let's consider a 3x3 matrix A:To interchange the ith and jth rows, we can use elementary row…
Q: a) Illustrate the sequence of vertices of this graph visited using depth-first search traversal…
A: In the given graph, we have vertices labeled from 'a' to 'p' with corresponding edges connecting…
Q: 3.2. Write a Java method for the class SinglyLinked List called removeSubList (...) that receives a…
A: To answer the above question, the work entails creating a Java method for a class called…
Q: What is the most popular method used by most O/S for handling deadlocks? prevent avoid ignore detect…
A: In the realm of computer systems, a deadlock is akin to a traffic jam, a situation where multiple…
Q: Give an example of a graph that has an Euler cycle that is also a Hamiltonian cycle.
A: Let's consider the following graph:1A---B 2| | 3C---D
Q: Source Code: Sombrero var canvas = document.getElementById('myCanvas');…
A: In the computer graphics and interactive visualization, WebGL stands as a powerful technology that…
Q: Could you explain what the R code is doing below? # read in each table read_counts <-…
A: In this question an R program is given that needs to be explained line by line.
Q: JAVA Program Modify this program so it passes all the Test cases and it should not use a while…
A: Get user input for a string.Convert the string to lowercase.Check if the string is "quit"; if yes,…
Q: In C++ compile a program to fufill purpose mentioned below, not copied from internet please. Write…
A: Algorithm:Crеatе a structurе namеd MoviеData to storе information about a moviе, including titlе,…
Q: Write a Python program to create a batch file for 20 employees. Read Name, ID, weekly hours and rate…
A: Algorithm: Employee Salary Processing1. Start.2. Define a function `calculate_financial_details`…
Q: Code is in Java In pictures I will provide full code, AVL Tree utilizes BinNode Class that will…
A: In this question we have to understand about the AVL search implementation and modify the code to…
Q: Samantha uses the RSA signature scheme with primes p = 541 and q = 1223 and public verification…
A: Primes p=541 and q=1223Public verification exponent e=159853Document D=630579
Q: JAVA Program Modify this program with further modidications: it should not use a while loop.…
A: Write a boolean method that uses recursion to determine whether a String argument is a palindrome.…
Q: Media applications that play audio or video files are part of a class of workloads called…
A: A cache is a sort of volatile computer memory that is faster and smaller than other types. It is…
Q: Data communication course A company that carries out international cargo business has offices and…
A: Protocols refer to a set of rules and conventions governing communication between devices or…
Q: Java How do I use printf to format this to money with .00 ? public static void main(String[]…
A: To format the output as money with .00 using printf in Java, you can use the %,.2f format specifier.…
Q: Write a query to display the manager name, department name, department phone number, employee name,…
A: A detailed SQL query has been created in order to retrieve particular information about a sales…
Q: Lab 8 C++ and Provide all code fully Instructions Test 1: An empty list Test 1 in main.cpp prints…
A: Algorithm: Singly Linked List OperationsData Structures:- Node: Structure defining a node in the…
Q: I have tried to run the code, using the example usage as well and I get the error: "L is not a…
A: The provided Lisp code implements a solution to the Missionaries and Cannibals problem using a…
Q: Soto works as a database administrator for a bank. He uses an input mask to ______. a. confirm…
A: An input mask is a feature used in database systems to control the formatting of data entered into a…
Q: What are six examples of information technologies that could be used in computer crimes.
A: Computer crime, or cybercrime, refers to illicit activities executed through electronic means,…
Q: A mutex lock is a software solution used to protect a critical section, which efficiently utilizes…
A: Mutex is the lock that we set the resource before using the share resource and after the using…
Q: Count of guarded walls There are N guarding posts on the Great Wall of China. However, not all of…
A: This code will first read the number of guarding posts from the standard input. Then, it'll create…
Q: Write corresponding Mic-1 MAL instructions to implement following IJVM assembly instructions using…
A: Two words are popped from the stack by the IJVM assembly instruction IF_GE offset, which branches if…
Q: Find and compare the percentage of accuracy for 1-bit branch predictor and 2-bit branch predictor…
A: Evaluating the performance of two distinct branch predictors—a 1-bit branch predictor and a 2-bit…
Q: By convention, a cache is named according to the amount of data it contains (i.e., a 4 KiB cache can…
A: To implement a 32 KiB cache with two-word blocks, we need to calculate the number of blocks and the…
Q: Exercise 2 Write a function called cumsum that takes a list of numbers and returns the cumulative…
A: Step1: we have create the function cumsum to passed the arguments Step2: we have initialize the list…
Q: Exercise 1 Write a function called nested_sum that takes a list of lists of integers and adds up the…
A: Algorithm for nested_sum function:1. Define a function named nested_sum that takes a list of lists…
Q: What are some sources of self-emission in computer graphics and visulization?
A: The objective of the question is to identify and explain the sources of self-emission in computer…
Q: In a semaphore, who increments the variable, Wait or Signal? A/
A: 1) A semaphore is a synchronization primitive used in concurrent programming to control access to a…
Q: b. Using both the POS and SOP, find the circuit with the following input/output table: 0 0 0 0 B 0 0…
A: POS (Product of Sums) and SOP (Sum of Products) are two common forms in Boolean algebra. POS…
Q: explain what a FIFO buffer is and its use with an example.
A: A buffer is a section of computer memory that is used as temporary storage to keep data while it is…
Q: What are the steps in the Genetic Algorithm Flowchart.
A: Genetic Algorithms (GAs) are optimization algorithms inspired by the process of natural selection…
Q: A prototype is a model that ______ the program or app. a. demonstrates the functionality of b.…
A: Here, we will discuss the series of MCQ and T/F questions related to programming fundamentals. We…
Q: Project: Blood Donation System The blood donation center is responsible for managing the donations…
A: Creating a complete set of diagrams and artifacts for a Blood Donation System requires significant…
Q: Need an Expert to write this code so I can check what I did wrong. Thanks! Write a C++ program for…
A: In the C++ Program given below:The factorial function is defined to calculate and return the…
Q: (9). If L₁ and L2 are not in D, then L₁ - L2 cannot be regular. True False
A: Firstly, let's understand what it means for a language to be regular. In formal language theory, a…
Q: 1. Within your Jupyter Notebook, write the code for a Python function called def…
A: The provided Python function, parseWeatherByYear, is designed to extract weather data for the city…
Q: Discuss the security implications From the perspective of your department and management level,…
A: Phishing Attacks: Cybercriminals frequently utilize misleading messages or messages to fool workers…
Q: Provide an example of a C++ string object and function that can process a character array. Provide…
A: 1) In C++, a std::string is a standard library class that represents a sequence of characters. It is…
Q: 1. What is append vs. extend? 2. What is del vs. remove? 3. What is append vs. concatentation?
A: append is a list method in Python that adds a single element to the end of the list.extend is also a…
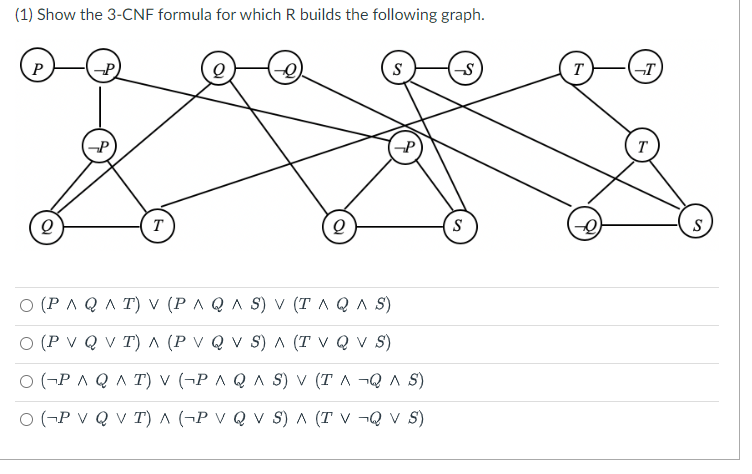
Let R be the reduction from 3-SAT to VERTEX-COVER as discussed in class.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 5 images

- The highway distance between 6 cities named (A ... G) are illustrated in the following adjacency matrix:A B C D E FA 0 7 19 28B 7 0 10 18 40 C 19 10 0 16 17D 18 16 0 14 10E 40 14 0 12F 28 17 10 12 a) Draw the graph that represent such adjacency matrix b) List the right sequence of nodes traversed by the DFS and BFS algorithm starting from node A. c) Does this graph possess a Euler circuit/path? , why? If any of them does not exist, how the graph can be modified to have one? d) Draw the minimum spanning tree of this graph . e) Use the Dijkstra's algorithm to determine the shortest paths from city (A) to all other cities . Determine the shortest path and cost from node A to node E .[Hint: implement the algorithm step by step to show which node will be added in sequence] f) Determine the shortest paths between all pairs of nodes using Floyd-Warshall algorithm.5 Consider the degree-4 LFSR given by x to the power of 4 space plus space x squared space plus space x space plus space 1. Assume that the LFSR is initialized with the string left parenthesis s subscript 0 s subscript 1 s subscript 2 s subscript 3 right parenthesis equals left parenthesis 0110 right parenthesis. How long is the cycle generated?What is the time and space complexity of this function? It is a dfs function which goes through every possible path from node to another without cycles. Time complexity could be either O(n!) or O(2^n), or is there another answer? What is the space complexity? def dfs(currency_pairs, source, target): graph = defaultdict(dict) for s1, s2, rate_val1, rate_val2 in currency_pairs: graph[s1][s2] = rate_val1 graph[s2][s1] = rate_val2 def backtrack(current, seen): if current == target: return 1 product = 0 if currentingraph: neighbors = graph[current] for neighbor in neighbors: if neighbor not in seen: seen.add(neighbor) product = max(product, graph[current][neighbor] * backtrack(neighbor, seen)) seen.remove(neighbor) return product return backtrack(source,…
- Let’s consider the directed graph with unweighted links presented in Figure 4.12. Thisgraph is similar to the previous graph except by one missing link between A and E.Write networking code to describes how to create the new links dataset and then search for the existing cycles within the directed graph. ans in 20 min.or asapConsider the Omega network and Butterfly network from p nodes in the leftmost column to p nodes in the rightmost column for some p=2^k. The Omega network is defined in Chapter 2 of the text book such that Si is connected to element S j if j=2i for or j=2i+1-p for See Chapter 2 in text book for its definition. The Butterfly network is an interconnection network composed of log p levels (as the omega network). In a Butterfly network, each switching node i at a level l is connected to the identically numbered element at level l + 1 and to a switching node whose number differs from itself only at the lth most significant bit. Therefore, switching node Si is connected to element S j at level l if j = i or j . Prove that for each node Si in the leftmost column and a node Sj in the rightmost column, there is a path from Si to Sj in the Omega network. Prove that for each node Si in the leftmost and a node Sj in the rightmost, there is a path from Si to Sj in the Butterfly network.(c) Suppose that you have access to the sorted weight list in an ascending order in O(1), which of the minimum cost spanning tree algorithms (Prim or Kruskal) would you use to achieve a better running time performance for graph ? Justify why your selected algorithm is better suited for the above graph. Show the final result of the minimum cost spanning tree that you have obtained.
- Given the following adjacency matrix for a undirected, weighted graph: undirected, weighted graph data Source Node Destination Node Weight 0 3 2 3 4 3 3 7 6 4 7 8 0 4 7 1 4 9 1 5 3 4 8 1 7 8 2 0 1 4 4 5 2 5 8 3 8 9 2 5 9 10 1 2 5 5 2 6 5 6 7 2 6 8 9 6 9 Calculate each of the following searches assuming we start at node 4. Breadth-first search Depth-first search Show the order that each search will produce assuming it chooses a node with a higher number first when there are multiple choices. Remember unordered graphs allow for traveling from source to destination and from destination to source so to save space, an adjacency matrix may only provide from node A to B instead of including node B to A as another edge in the list.Given the following adjacency matrix for a undirected, weighted graph: undirected, weighted graph data Source Node Destination Node Weight 0 3 2 3 4 3 3 7 6 4 7 8 0 4 7 1 4 9 1 5 3 4 8 1 7 8 2 0 1 4 4 5 2 5 8 3 8 9 2 5 9 10 1 2 5 5 2 6 5 6 7 2 6 8 9 6 9 Calculate each of the following searches assuming we start at node 4. Breadth-first search Depth-first search Show the order that each search will produce in a visual graph assuming it chooses a node with a higher number first when there are multiple choices. Remember unordered graphs allow for traveling from source to destination and from destination to source so to save space, an adjacency matrix may only provide from node A to B instead of including node B to A as another edge in the list.Please explain Some engineers at Google want you to implement a graph structure of the subway system in Boston showing the connections between each station.They are wondering what data structure to use to represent the graph and use the least amount of memory, given that most stations do not connect to many other stations. Which graph data structure representation should you use and why? Group of answer choices a. Adjacency List -- Because the complexity is O(V+E), the data structure is better at representing sparse graphs since their are fewer connections. b. Adjacency Matrix -- Because the complexity is O(V+E), the data structure is better at representing sparse graphs since their are fewer connections.
- A star configuration of a network represents its structure as a graph with an edge from a single, central node to each remaining node. A point-to-point configuration represents a network as a complete graph. Draw a picture of an example of each kind of configuration with four nodes, and use big-O notation to state the efficiency of adding or removing a given node in each type of configuration. You can assume for now that removing each edge is a constant-time operation. *PythonGiven the above weighted graph (undirected): a) Determine and draw a Minimum Spanning Tree (MST) of the given graph above. Indicate the minimum weighted sum. No steps required. Students may choose whichever algorithm to find the MST b) Find the shortest path from source node D to destination node G of the given graph above, using Dijkstra’s algorithm. Show your steps with a table as in our course material, clearly indicating the node being selected for processing in each step. c) Draw ONLY the shortest path obtained above, from source node D to destination node G, and indicate its weighted sum.Here is a graph between two different campuses comprised of several location Traverse the graph using Breadth first search

