1. Convex Programming Prove that the following mathematical program is a convex program. You may use without proof any facts claimed about convex functions and sets in the lecture slides. min max(1/1₁, 1/₂) 21.-22 F1, F₂ > 0 x²+x≤1
1. Convex Programming Prove that the following mathematical program is a convex program. You may use without proof any facts claimed about convex functions and sets in the lecture slides. min max(1/1₁, 1/₂) 21.-22 F1, F₂ > 0 x²+x≤1
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter18: Deterministic Dynamic Programming
Section: Chapter Questions
Problem 10RP
Related questions
Question
question 2
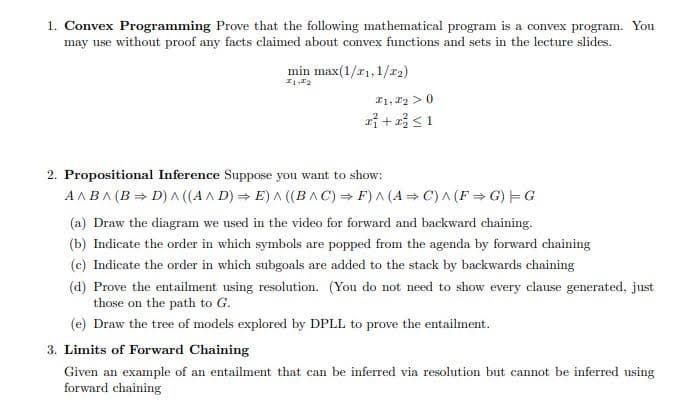
Transcribed Image Text:1. Convex Programming Prove that the following mathematical program is a convex program. You
may use without proof any facts claimed about convex functions and sets in the lecture slides.
min max(1/₁, 1/₂)
1,2
F1, F₂ > 0
x² + x² ≤ 1
2. Propositional Inference Suppose you want to show:
A^B^ (B⇒D) ^ ((A^D) E) ^ ((BAC) ⇒F) ^ (A⇒C) ^ (F⇒G) G
(a) Draw the diagram we used in the video for forward and backward chaining.
(b) Indicate the order in which symbols are popped from the agenda by forward chaining
(c) Indicate the order in which subgoals are added to the stack by backwards chaining
(d) Prove the entailment using resolution. (You do not need to show every clause generated, just
those on the path to G.
(e) Draw the tree of models explored by DPLL to prove the entailment.
3. Limits of Forward Chaining
Given an example of an entailment that can be inferred via resolution but cannot be inferred using
forward chaining
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole