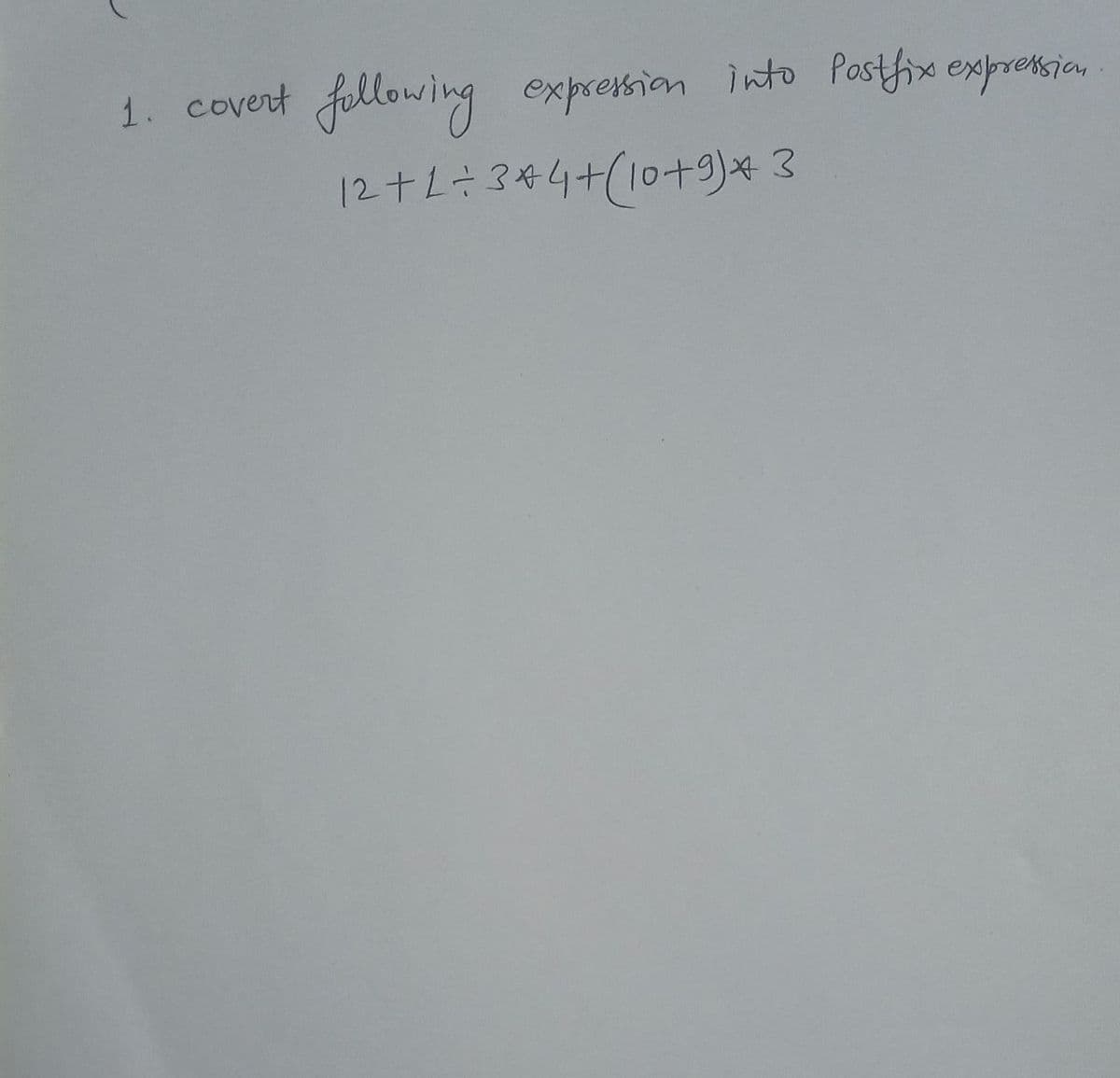
1. covert following expresion into Postfix expreksion 12+L÷ 3#4+(10+9)* 3
Q: When a computer needs a piece of information, does it immediately perform the memory fetch operation...
A:
Q: What Are the Typical Server Program's Functions?
A: Introduction the question is What Are the Typical Server Program's Functions and here is the solutio...
Q: What will ALWAYS be the symbol for your current directory in a Linux/Unix terminal?
A: Linux/unix is an open source operating system that directly manages resources through commands. dat...
Q: What Exactly Is a Protocol Data Unit?
A: Intro the question is about What Exactly Is a Protocol Data Unit and here is the solution in the ne...
Q: 6. What is the MARIE instruction for the following register transfer language (RTL): MAR + X MBR + M...
A: Register Transfer Language (RTL)In symbolic notation, it is used to describe the micro-operations tr...
Q: 183. The output of the show frame-relay pvc command shows "PVC STATUS = INACTIVE". What does this me...
A: Let's see the solution below
Q: What Are the Data Units at Each Layer of the Tcp/IP Protocol Suite?
A: Intro the question is about What Are the Data Units at Each Layer of the TCP/IP Protocol Suite here ...
Q: short answer Can you explain the importance of interrupt in microprocessor? Computer science
A: Introduction: An interrupt is a method of temporarily pausing a program's execution so that external...
Q: How do you handle security in an office with shared resources like a printer, for example?
A: Introduction: One of the most important factors in protecting data from intruders is security.
Q: Randomly generate a number in range [1, 12]. Map this number to a season: if the number is 3, 4, or ...
A: Programming Language => PYTHON I have provided PYTHON CODE along with CODE SCREENSHOT an...
Q: Give an explanation of the term "root authority." Give an example of its application?
A: Answer :
Q: How would you describe a situation in which you would demand additional storage?
A: Some times system needs the additional storage to run the all activities these demand may be observe...
Q: Discuss password management, including the concept of a strong password, for the system you've been ...
A: Passwords are used as a security feature and are considered one of the better ways to implement secu...
Q: Why is it so important for you to learn about information systems? What do you want to get out of th...
A: Introduction: The Information Systems programme is a multi-disciplinary curriculum.
Q: 6. Match the following to one or more layers of the OSI model: a. Route determination b. Flow cont...
A: We need to match the columns with layers of OSI model.
Q: by using c++ & oop .Apply the concepts that you learned (OOP, polymorphism, interfaces, packaging, …...
A: Since this is a question with many internal subparts, we answer as many as we can with crude impleme...
Q: What are the essential features of OSPF?
A: Introduction features of OSPF
Q: Q7 actions · Based on the structure of viruses, explain how they spread and do harmful
A: here we explain what is the structure of viruses and also explain how different virus spread in comp...
Q: Why is it necessary in OSPF to partition the autonomous system into several areas?
A: Introduction Why is it necessary in OSPF to partition the autonomous system into several areas
Q: What are the four types of routers?
A: Router It is a device that are used to transfer the data packets between the networks. From the inte...
Q: When it comes to operating systems, why do we have multiple partitioning techniques?
A: Probably the easiest technique for assigning memory is to separate memory into a few fixed measured ...
Q: successful distributed denial-of-service attack requires the malicious hacker to download software t...
A: A successful distributed denial-of-service attack requires the malicious hacker to download software...
Q: Servers can be designed to limit the number of open connections. For example, a server may wish to h...
A: Answer is given below-
Q: /* Javascript! Create a function that run anot function after a delay. Arguments: callback: the func...
A: Code explaned using comments:
Q: Determine which characteristics of an algorithm the following procedures have and which they lack. ...
A: This procedure has the characteristics of: Input, Finiteness, Generality This procedure lacks: Outpu...
Q: Code a simple python 3 program that includes 3 x 3 matrix operations: • Addition • Subtraction • Mul...
A: import numpy# Two 3x3 matrices are initialized by valuex = numpy.array([[1, 2, 3], [4, 5, 6], [7, 8,...
Q: Consider a 64K L2 memory and a 4K L1 2-way associative cache with block sizes of 512. a. How many ...
A: Given, size of L2 = 64K and size of L1 = 4K associativity = 4 - way and , block size = 512
Q: Why does a data warehouse update less frequently than a transactional database?
A: Introduction: A data warehouse is a database that is purpose-built to support business intelligence ...
Q: The CPU organisation of most computers falls into one of three categories: (1) general register orga...
A: Introduction: There are three sorts of architectures: Stack-based, accumulator-based ge...
Q: create a "magic 8 Ball" which will randomly display a message each time the page is refreshed in htm...
A: The Mаgiс 8 Bаll is а well knоwn tоy used fоr seeking аdviсe. It hаs been develорed ...
Q: Let A = ({go, q1, 2}, {a, b}, 8, q0, {41 }) be the NFA with transition ta a 9o {40, 41, 42} 91 {q1, ...
A:
Q: When a computer needs a piece of information, does it immediately perform the memory fetch operation...
A: Introduction: The procedures conducted when reading a piece of information from memory should be add...
Q: Define c++
A: What Does C plus plus Programming Language (C++) Mean?C++ (said C plus plus) is an object-oriented c...
Q: Communication models that are comparable to each other include linear and interactive models.
A: Introduction: We must discover the commonalities between the linear and interactive models of commun...
Q: a. 1+3+5+7+· +999 b. 2+4+8+ 16 + · · . + 1024 d. Σ3 ... n+: с. -i=3
A: Please refer below for your reference: According to the guidelines we are restricted to answer only ...
Q: What Is the Distinction Between Tftp And Ftp Application Layer Protocols?
A: Introduction the question is about What Is the Distinction Between Tftp And Ftp Application Layer Pr...
Q: What other questions must be addressed before deciding if database as a service is right for your li...
A: Consider how easy to use the framework will be for that large number of individuals from staff expec...
Q: Why should you check the value of a StreamReader object's EndOfStream property before invoking the R...
A: Please see the following for the answer: It's crucial to verify the value of a Stream Reader object'...
Q: What Is the Distinction Between a Hub, a Switch, and a Router?
A: Introduction The hub is intended to link hosts with no comprehension of what is being sent. When a ...
Q: Perform the pairwise disjointness test for the following grammar rules. b) B → aB | bA | aBc
A: Dear Student, A grammar will pass the pairwise disjointness test if the first of each pair do not in...
Q: can I know some tips or how to do flowchart and pseudocode for this C++ coding? please make it detai...
A:
Q: Write a program that searches for the given string in the given sentence and if the word is found th...
A: Solution - Programming language used: C All solution steps are included in program code as comments...
Q: What Does Symmentric Multiprocessing (smp) Mean?
A: Intro the question is about What Does Symmetric Multiprocessing (SMP) means and here is the solution...
Q: Create a Windows Form Application project. with C#, using random values in an array or loop. The app...
A: C# Program: using System; using System.Collections.Generic; using System.ComponentModel; using Syste...
Q: 4- Calculate the sum of 1.011 x 2-1 and -1.101 x 2-2 by hand. Assume you have 3 digits binary precis...
A: The complete solution is given step by step in the next step.
Q: What does it mean when someone says "important consideration"? This is especially true in the field ...
A: Introduction: Software is defined as a collection of executable computer code, libraries, and docume...
Q: short answer In a microprocessor system, what are the different sorts of interrupts? Computer sci...
A: Introduction: The Interrupt occurs when a process is being executed by the CPU and a user requests a...
Q: Given i and j, two variables of type double. Which of the following statements declares a double var...
A: Correct Answer: (a) if(i>0 && j>0) double s=M...
Q: Write a static recursive method in Java called mRecursiv that displays all of the permutations of th...
A: PROGRAM INTRODUCTION: Start definition of the main function. Declare and initialize the required va...
Q: in html Explain how we can extract the options that are selected from a group of radio buttons. Writ...
A: In step 2, I have provided brief explanation---- In step 3, I have provided a program as ...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- You intercept the ciphertext C = 10 sent to a user whose public key is e = 5, n = 35. Whatis the plaintext M. Show all your steps.11) _________ consists of an encapsulating header and trailer used to provide encryption or combined encryption/authentication. A) SPI B) ESP C) AH D) IKEv2Consider the code below. Identify all statements that are true about the code. Select all that apply. protocol MessageSecurity { func encrypt(message: String) -> String func decrypt(message: String) -> String}struct SecureIsh : MessageSecurity { func encrypt(message: String) -> String { let split = message.components(separatedBy: " ") let ished = split.map({ $0 + "ish"}) return ished.joined(separator: " ") } func decrypt(message: String) -> String { let split = message.components(separatedBy: " ") let notIshed = split.map({ $0.dropLast(3)}) return notIshed.joined(separator: " ") }}struct SecureMessenger { var security: MessageSecurity mutating func assignSecurity(security: MessageSecurity) { self.security = security } func send(message: String, to: String) { // code for sending a message } func read(message: String, from: String) { // code for reading message }} Group…
- Encrypt the messageWATCH YOUR STEPby translating the letters into numbers, applying the encryption function f(p) = (−7p+2), and then translatingthe numbers back into lettersRewrite the same code with a different logic make sure you have the same output. <?php$cookie_name = "user";$userID = $_COOKIE[$cookie_name];if(!isset($_COOKIE[$cookie_name])){ echo "Please login in first!<br>"; exit();} include "dbconfig.php";$conn = new mysqli($hostname, $username, $password, $dbname) or die($conn->connect_error);$name = $_POST['name'];$description = mysqli_real_escape_string($conn, $_POST['description']);$term = mysqli_real_escape_string($conn, $_POST['term']);$enrollment = $_POST['enrollment'];//Query course name$Rid = '';$userGivenFacultyID = $_POST['Fid'];$userGivenRoom = $_POST['Rid'];$queryRid = "SELECT Rid FROM TECH3740.Rooms WHERE CONCAT(Building,Number) like '%$userGivenRoom%' ";$resultRid = mysqli_query($conn, $queryRid);$rid_row_ct = $resultRid->num_rows;if($rid_row_ct = 1){while($ridRow = $resultRid->fetch_assoc()){$Rid = $ridRow['Rid'];}} $queryRoomSize = "SELECT Size FROM TECH3740.Rooms WHERE Rid = $Rid";$resultRoomSize =…xlockmore Vulnerability Details is a simple example of a format string vulnerabilityusing the syslog function. The vulnerability is cause by Which snippet ofcode?
- With chmod, you may modify the permissions of a subset of users, add the group's execution bit, and leave the rest unaffected. False or TrueNo plagarism please! Correct and detailed answer will be Upvoted else downvoted. Thank you! Q.Which of the following is an example of polygram substitution ciphers? a. ROT-13 b. OTP c. ATBASH d. None of the available options is correctThis is sample data from my JSON file [ {"username" : "Jane Doe","date" : "Sat, 1 Apr 2023","time in" : "09:06:45 PM","status in" : "Working",}, {"username" : "Jane Doe","date" : "Sat, 1 Apr 2023","time out" : "09:06:57 PM","status out" : "Break" Please code a JAVA PROGRAM that will allow the server to determine if a user is currently working or on break by searching their name.
- This polynominal, also called an __________, represents the equation used to reduce the key length in asymmetric cryptography : y^{2}=x^{3}+ax+bLet your key be the IP address 234.10.90.0 and you want to hash it and then put it in a slot in the hash table with size 257. Do this using Modulo Primes Method and Polynomial Hash. Write all the details.Vigenere Cipher By finding the key length in worksheet 7 .doc, you can use frequency analysis for each letter of the key in the cipher to find the particular shift and find the key word. Using the keyword you found, decrypt the following text. Enter your answer with no spaces. (Not case sensitive) ciphertext to decrypt: UHBRXATCBSZ UHFK PSUG NPPP UAOR UHJL HTPP FAMG AEBZ PUUR IEWG HEOC SEDG QESG TTIY UTIC TEDS SIUW DONC TDPU OTPI FEQG OGUF FKFW MEOE UHBQ FCSC U.IGR IELC ZLFL HTIA BNCC EEUC SMJL FDUF FNPL FITY CLFR PDPY GRFO VE OA ZAOY MYTG TOOR IEGG SSU.Q FCPL E,TIG SD,FR DLFR UESM GTIC LEZ.Z BBCY HEXY TACJ FTPZ SEBI WIHC OESC CYGG ODJL HGBN TOGY GIYC ELFL HTIZ FTXC FNDM NMPL QHSY TETM SWPP ES.PL DEIC IAEY OUNZ FRPD UHFQ F.HFI OEXR IELC ZLFL HTIK VSUZ FADM NMPL EIWG TOSM GAMJ PFUF FSFE BPT.D PRFV BMQJ FIGF FOCQ FRWC EGBN TOGD PRUW. UWFL UYGG WEBL EFJD UEFL, UHFL JTXY TLJI FLZR IELC ZHBB MEOE UHPD GIWC. XIUF UHJQ PBTC SVBR JOOR IETC DUSG UYPD UHJQ QASR JCVJ BRDP ZPUM TYTR FMXY TLPQ UFPP…

