1. Create vector "Sex", "ModeratePA", and "Phone_Hours" based on the table beside.
1. Create vector "Sex", "ModeratePA", and "Phone_Hours" based on the table beside.
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN:9780357392676
Author:FREUND, Steven
Publisher:FREUND, Steven
Chapter11: User Interfaces, Visual Basic For Applications (vba), And Collaboration Features
Section: Chapter Questions
Problem 3EYW
Related questions
Question
Question Khn
.
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
Transcribed Image Text:Create vector "Sex", "ModeratePA", and "Phone_Hours" based on the table
beside.
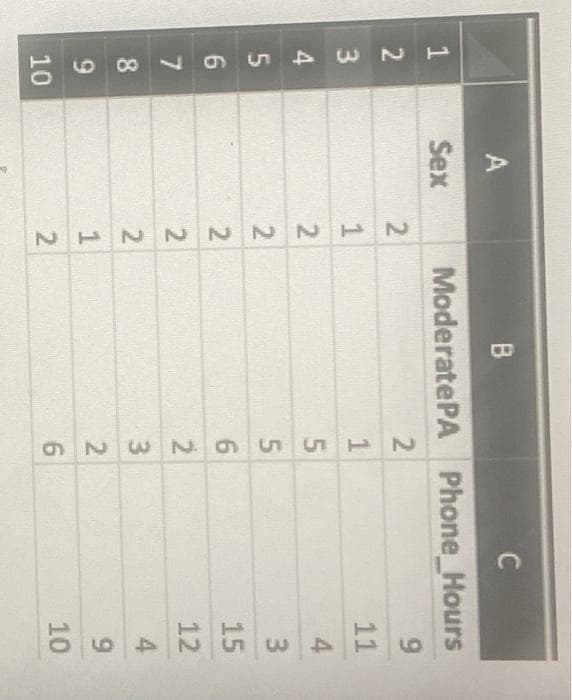
Transcribed Image Text:12
3
4
5
6
7
8
9
10
A
Sex
2
B
Moderate PA
2
2
122~N~1~
1556N326
9
C
Phone_Hours
9
11
4
3
15
12
4
9
10
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning


COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:
9780357392676
Author:
FREUND, Steven
Publisher:
CENGAGE L

New Perspectives on HTML5, CSS3, and JavaScript
Computer Science
ISBN:
9781305503922
Author:
Patrick M. Carey
Publisher:
Cengage Learning


Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage