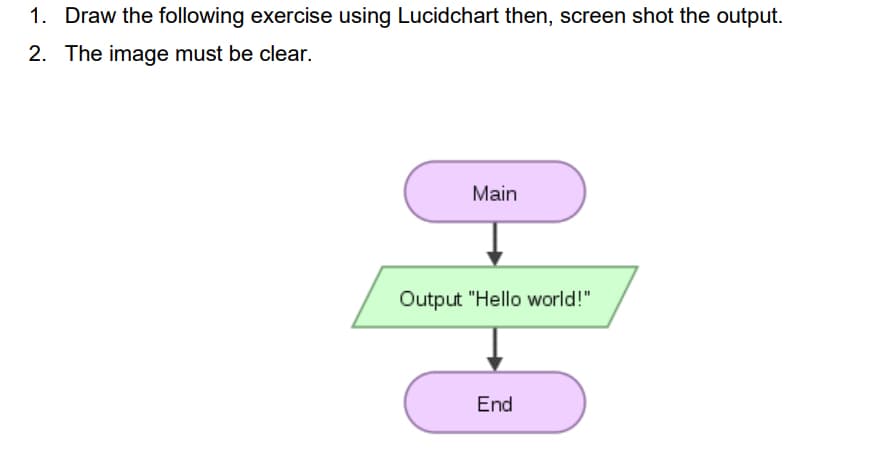
1. Draw the following exercise using Lucidchart then, screen shot the output. 2. The image must be clear. Main Output "Hello world!" End
Q: An example of this would be the term "gigabyte."
A: An example of this would be the term "gigabyte."
Q: Write an if -else statement that assigns True to fever if temperature is greater than 98.6; otherwis...
A: Given requirement, Write an if-else statement that assigns True to fever if the temperature is great...
Q: Create the Kmaps and then simplify for the following functions (leave in sum-of-products form): a) F...
A: Let's see the solution in the next steps
Q: Provide me with the MATLAB code to swap the first and last row of the matrix given below, mat = 1111...
A: The statement mat([1 size(mat,1)],:) will fetch the first and last rows of the matrix and the follo...
Q: a) Write a C+ program that inputs a three digits number from the user and display it in reverse orde...
A: Program using c ++ input value from user and display in reverse order.
Q: What are the four most common types of database failures?
A: Introduction: Memory faults, disc crashes, faulty disc sectors, and discs full of mistakes are examp...
Q: Consider the following edge-weighted graph G with 9 vertices and 16 edges: 40 <- 60 90 50 70 30 80 1...
A: According to the information given:- We have to follow the Kruskal algo and find the MST edges.
Q: Where are the system journals saved by default?
A: Introduction: With the "auto" option, Journal will be configured to save journal log data in the /va...
Q: One advantage of a ROUTER is that it can choose the "best" route between networks when there is a ch...
A: Introduction: Here we are required to mention that whether the given statement is true or false.
Q: Question 6 (see above) Which of the following are equivalent to the statement "No librarians have ch...
A: Here is the explanation about the statements:
Q: is to write a program that allows an input of a sequence of numbers from the user and prints the num...
A: According to the Question below the Solution: As per our guidelines we are supposed to answer only...
Q: What is Automata? List the applications of finite automata. Discuss why to study the concept of auto...
A: The Answer is in below Steps
Q: ee different data plans for its customers: PLAN A: For $19.99 per month, 2 gigabytes are provi...
A: #include <iostream>using namespace std; int main(){ const float MonthlyBillA = 19.99, Monthly...
Q: Question 1 What are two of the allowed modes for opening a file?
A: A file is Collection of stored data which is used for different purposes like read, write,append etc...
Q: The code for DI/BH is DI/BH.
A: Introduction : DI and BH registrations: DI, or Destination Index, is a 16-bit index register that se...
Q: OOP Homework Inheritance (PYTHON) 1. Given two classes as described in Customer.py (attached) Revise...
A: class Sender: # Representing Sender and Recipient #Attributes nameSender = "" addr...
Q: Is it possible for two network interfaces to have the same MAC address? Why do you think that is? Is...
A: Introduction: A network interface is when a computer connects to a private or public network. A netw...
Q: write a java program to print the mirror image of right angled in x-direction after taking number of...
A: In the above question , assuming the right angled triangle to be made up of star patter now original...
Q: Create a mind map with the word Information Technology as the center
A: The figure of mind map is given in second step.
Q: Provide a brief description of four potential vulnerabilities that may be exploited by the enemy. Wh...
A: Sources of Intelligence about Vulnerabilities Vendors of Security Software Providers Governmental a...
Q: 2. Create a mind map with the word Information Technology as the center
A: 2. Create a mind map with the word Information Technology as the center
Q: How to build a Pseudocode for Caesar Cipher
A: The Caesar Cipher technique is one of the earliest and simplest method of encryption technique. It’s...
Q: What influence does data mining have on personal security and privacy?
A: Introduction: Data extraction from data sets can be done using privacy-protected data mining (PPDM) ...
Q: Prove the following laws of logical equivalence using truth tables
A: p q r p->q q->r (p->q)->r p->(q->r) F F F T T F T F F T T T T T F T F T F F ...
Q: NW Q3) IP addressing operates at the network layer (Layer 3) of OSI, IP addresses must be able to id...
A: the answer is given below:-
Q: can you tell me the manage mode of adobe?
A: can you tell me the manage mode of adobe?
Q: t is the median of the following list of numbers? [11, 20, 8, 2, 7, 3, 19, 16, 1
A: Arrange the data in ascending order( from smaller to the larger number) 2,3,7,8,11,13,16,17,19,20 Th...
Q: What is the total delay of the new packet in arriving at Router B, i.e., how long does it take the ...
A: Given: Length of packet (L)=15,000 Transmission rate (R)= 0.05 mbps Number of packet per wave (N)= 1...
Q: PYTHON. Write a program that displays the first and last words of a sentence input by the user. Assu...
A:
Q: 2. Define another characteristic of Data Communication 3. Give an advantage of half duplex over ful...
A: Question 2: Characteristics of Data Communication are: Delivery: Main task of data communication is...
Q: Briefly characterize Amdahl’s law.? Briefly characterize Little’s law?
A:
Q: . Draw state diagrams of the control software for: A telephone answering system that records inco...
A: According to the information given:- We have to draw a state diagram of the mentioned instruction.
Q: Develop a java program to print a receipt for the tuition fee payment. Define a class TuitionFee wit...
A: I give the code in Java along with output and code screenshot
Q: What actions are taken to identify a suitable model for the system?
A: Introduction: What actions are taken to identify a suitable model for the system?
Q: Write a Java programme that reverses a string without utilising the built-in String reverse function...
A: Introduction: Write a Java program that reverses a string without utilizing the built-in String reve...
Q: I am trying to figure out why the sum at the end of my Java code is not working correctly. It keeps ...
A: the answer is given below:-
Q: How do you find out what kind of motherboard you have in order to fix it?
A: Introduction: Motherboards: It is a term used in computer science to describe a computer's primary c...
Q: Draw the logic diagram and construct the truth table for each of the fllowing expressions: (i) X = A...
A: Part 1. X=A+B+(CD)' Logic Diagram Truth Table
Q: Your program needs to read in two words on a single line. If the pair of words are Super Anagrams of...
A: Here, I have to provide a python solution to the above question.
Q: e) Find the moment of inertia of a hollow cylinder about the axis of the cylinder using a JAVA progr...
A: To write java code to find the moment of inertia of a hollow cylinder about its axis.
Q: What Is A Nondeterministic Finite Automaton (nfa) And What Does It Mean
A: Introduction: A non-deterministic algorithm is the execution of concurrent algorithms with race cond...
Q: Please convert to 3rd Normal Form
A: Third Normal Form is a form that is already in First Normal Form as well as Second Normal Form and t...
Q: Please explain the code below line by line in detail. The code is finished, I just need the explanat...
A: answer is
Q: What is a heuristic, and how does it differ from an algorithm?
A: Heuristic - It is used to find the best way according to the heuristic value/Heuristic function. It ...
Q: 2. For this problem consider the Average problem stated below. Average Input: A sequence of n intege...
A: Given The answer is given below. Answer:- a)Algorithm to solve average problem using the 'For' loop ...
Q: Which instruction compares two floating-point numbers before the P6 family?
A: In processors prior to the P6 family FCOM, or FCOMP instruction compares two floating-point values.
Q: Your company is trying to implement a new rewards program for employee moral. Create an INTERRELATIO...
A: To give a reward in the organization is the best practice that is performed in an organization and i...
Q: A year in the modern Gregorian Calendar consists of 365 days. In reality, the earth takes longer to ...
A: Step-1: StartStep-2: Declare a variable and take input from user as yearStep-3: If year is completel...
Q: What argument values are necessary when calling Function 716Ch to read a binary array from a file th...
A: Introduction: This function reads binary data from a file and returns it as data. The format of the...
Q: What are necessary conditions which can lead to a deadlock situation in a system?
A: 1.Mutual Exclusion: When two people meet in the landings, they can't just walk through because there...
Step by step
Solved in 2 steps with 1 images

- 7. The faster the frames are displayed, : a. the rougher the video appears b. the smoother the video appears c. it gets blurry d. none of the mentionedEXERCISE 2 Based on the image attached, solve the following questions.Expand on the concept of Black Box in regards to computer graphics. Please and thank you
- Can you walk me through the steps of making a screenshot on my computer?Java Programming Problem 2 – Characters Around a Circle 1) Create user interface using Scene, Pane and Stage. 2) Use Font class correctly to set up font style and size. 3) Use for loop correctly to scan through each character of the string. 4) Use methods of Text class to set font and rotate characters. 5) The output for Characters Around Circle is correct and looks like the sample screen.Create a simple menu-like JAVA program that will act like a virtual classroom. The program should allow users to add and delete subjects as well as update their calendars and to-do lists.
- Create a JavaFX application that shows the side view of a spaceship when it moves the mouse. When the mouse button is pushed, a laser beam should blast from the front of the ship (a single continuous beam, not a moving projectile) until the mouse button is released. Create a new class to define the spacecraft.Can you please check what is wrong with my project. I am trying to do a convolution on the following picture, but the error is connected with bounds. Please correct my code. import javax.imageio.ImageIO;import javax.swing.*;import java.awt.*;import java.awt.image.BufferedImage;import java.io.File;import java.io.IOException;import java.util.Scanner;import java.awt.Color;import java.awt.FlowLayout;import java.awt.image.BufferedImage;import java.io.File;import java.io.IOException;import javax.imageio.ImageIO;import javax.swing.ImageIcon;import javax.swing.JFrame;import javax.swing.JLabel;public class project {public static void main(String[] args) throws IOException {String imagePath = "C:\\Users\\hasib\\Downloads\\11″ TUFTEX BLACK.jpg";int[][] matrix = {{1,0,-1},{2,0,-2},{1,0,-1}}; //edge detectionBufferedImage image = ImageIO.read(new File(imagePath));JFrame frame = new JFrame();frame.setDefaultCloseOperation(JFrame.EXIT_ON_CLOSE);frame.setLayout(new…Study the following attached picture and answer the question that follows: Write a Java program in NetBeans that will output the pattern of the attached Image.
- Computer Science */ JAVA Compile and run the ImageGen01 application. Experiment with alternate formulas for the value of c. Add two more int variables so that you can separately set the RGB values of color and experiment some more. Share your most interesting re- sults with your classmates.These are some of the activities you can perform a. Load images b. Display image types, size of the image c. Cropping images d. Resizing Images e. Rotating & Flipping images f. Any other image processing activities that you learned by yourself You must explain the steps / methods you used in these activities - You should use Pillow for this project - Use PyCharm for the IDEHI, I have written the code, but I get the wrong inputs over and over. I have attached the question as an image, please can anyone help? Thank you. //<My_Code> import java.util.Scanner;public class Submission {public static void main(String[] args){//Input of the number of rows & columns//Creating a grid to map out the recoursesScanner input = new Scanner(System.in);int n = input.nextInt();int[][] grid = new int[n][n];for(int i = 0; i < n; i++) {for (int j = 0; j < n; j++) {grid[i][j] = input.nextInt();}}//2D integer arrays of max[num][value] collects from position//'num' and 'value'int[][] max = new int[n][n];for(int j = 0; j < n; j++){max[n -1][j] = grid[n - 1][j];}for(int i = n - 2; i >= 0; i--){/**** Inside the for-loop we insert an if statement to see* whether they can move downwards towards right and left.** Inside the two 'Else-if' we see whether they it can move only left,* or only right respectively*/for(int j = 0; j < n; j++){if(j - 1 >=0…

