Question 6 (see above) Which of the following are equivalent to the statement "No librarians have checked out any books"? Select all that apply. A. Vm E M.b E B.L(m) →¬C(m, b) B. O-3m E M.vb E B.L(m) A C(m, b) C. O Vm E M.b E B.¬C(m, b) → L(m) D. O-3m E M.3b E B.L(m) A C(m, b) E. O Vb E B.¬3m E M.L(m) A C(m, b) F.O Vm E M. E B.C(m, b) → ¬L(m)
Question 6 (see above) Which of the following are equivalent to the statement "No librarians have checked out any books"? Select all that apply. A. Vm E M.b E B.L(m) →¬C(m, b) B. O-3m E M.vb E B.L(m) A C(m, b) C. O Vm E M.b E B.¬C(m, b) → L(m) D. O-3m E M.3b E B.L(m) A C(m, b) E. O Vb E B.¬3m E M.L(m) A C(m, b) F.O Vm E M. E B.C(m, b) → ¬L(m)
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter17: Linked Lists
Section: Chapter Questions
Problem 10PE
Related questions
Question
please do it ASAP... I'll give you up thumb definitely
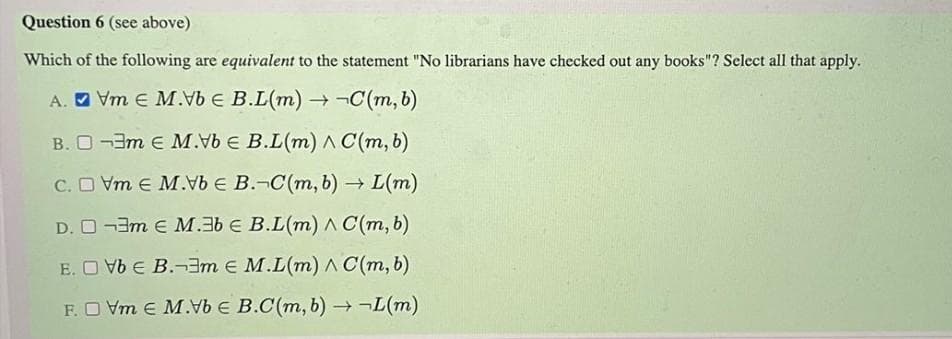
Transcribed Image Text:Question 6 (see above)
Which of the following are equivalent to the statement "No librarians have checked out any books"? Select all that apply.
A. O Vm E M.Vb E B.L(m) ¬C(m, b)
B. O -3m e M.vb E B.L(m) A C(m, b)
C. O Vm e M. E B.-C(m, b) → L(m)
D. O -3m E M.3b € B.L(m) A C(m, b)
E. O Vb E B.¬3m E M.L(m) A C(m, b)
F.O Vm E M.b E B.C(m, b) →¬L(m)
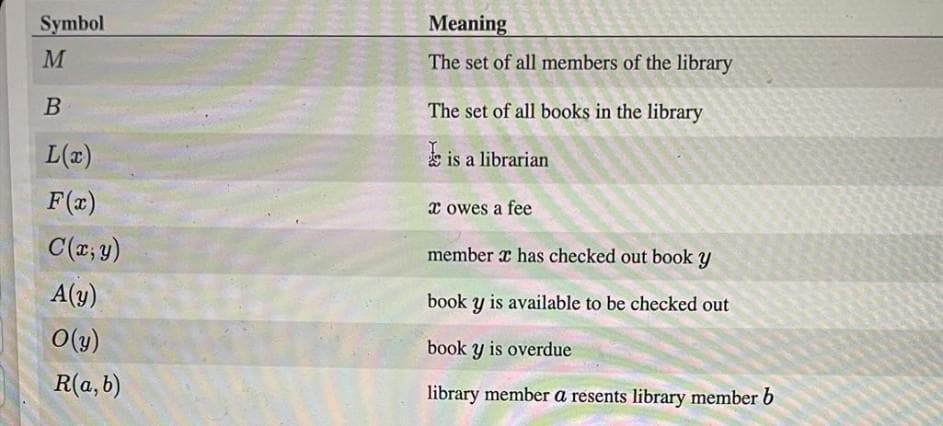
Transcribed Image Text:Symbol
Meaning
M
The set of all members of the library
B
The set of all books in the library
L(x)
s is a librarian
F(x)
x owes a fee
C(; y)
member x has checked out book y
A(y)
book y is available to be checked out
O(y)
book y is overdue
R(a,b)
library member a resents library member b
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L