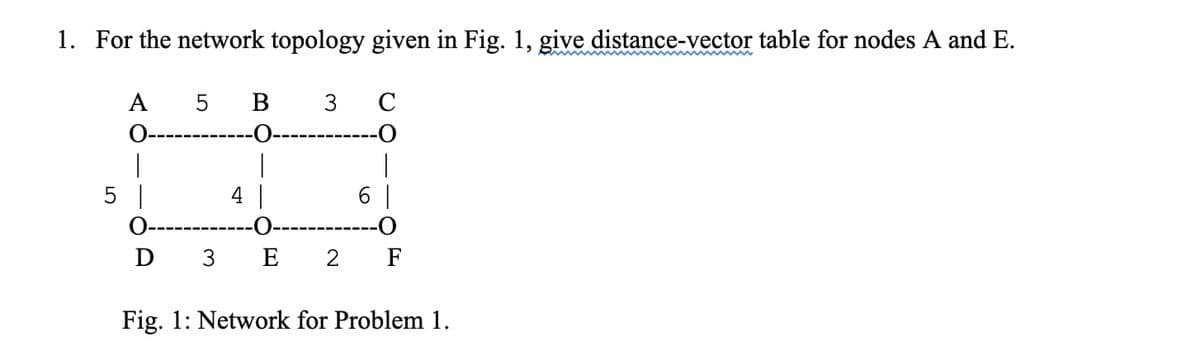
1. For the network topology given in Fig. 1, give distance-vector table for nodes A and E. A O- | 5 | D 5 B 1 4 | 3 E 3 6 C O | 2 F Fig. 1: Network for Problem 1.
Q: at "hardware" and "software" refer to speci
A: Summary A computing system is divided into two categories: Hardware and Software. Hardware refers to…
Q: The operating system and the user application view this virtual machine differently. Compare and…
A: Introduction: You get the impression that another computer is running alongside your primary one…
Q: What relationship exists between cohesion and coupling in software design and development?
A: Introduction: In this question, we are asked to give the relationship between cohesion and coupling…
Q: What is the difference between entering the value 5 into cell number 6 and copying the contents of…
A: Given: Various stages, such as fetching the opcode, reading and writing to memory, are necessary to…
Q: hat's the difference between SSL and TLS? Exists a distinction between these terms?
A: SSL: Included in the Secure Sockets Layer security technology are the domain name and browser. A…
Q: Suppose that your replacement policy (in a paged system) is to examine each page regularly and to…
A:
Q: Describe in your own words the meaning of the following problems: a. The differences among…
A: Sequential access is accessing data in a specific linear sequence.
Q: What is the difference between a client and a server when it comes to computers?
A: Client A client is a user application that connects to a server to get the right of entry to…
Q: Explain why implementing synchronization primitives by disabling interrupts is not appropriate in a…
A: In a single - process system ,eliminating interrupts is not the best way to provide synchronisation…
Q: he number of companies with a Web site has grown explosively in recent years. As a result, thousands…
A:
Q: Symbian, Android, and iPhone all utilize the same file deletion mechanism, but how does this effect…
A: Here's the solution:
Q: What does the operating system imply when it refers to "threads"?
A: The operating system serves as a bridge between hardware and software.
Q: How about a brief overview of the compiler and an examination of the testability hint?
A: Introduction: Testability refers to the ability to undertake an experiment to examine a hypothesis…
Q: ASSU - a1 = a2, b1 b2, c1 = c2 and d1=d2 - al State the resulting sequence. What property do we see…
A: Correct Solution is : <a1,a2,b1,b2,c1,c2,c1,c2> Algorithm for Inserting Sorts In order to rank…
Q: Which paradigm is more complex for compilers to handle, VLIW or superscalar? Why?
A: Introduction: The term "VLIW" is an abbreviation for "Very Long Instruction Word." It's a variety…
Q: Write a letter outlining software testing's principles, difficulties, and approaches.
A: Introduction: Software testing a techniques are the procedures used to check the programme being…
Q: What kind of measurements support software maintenance?
A: Software Maintenance: Software maintenance is the process of the changing, modifying, and updating…
Q: Enumerate the features of intelligent behavior that Artificial Intelligence (AI) seeks to replicate.…
A: Artificial intelligence - (AI) is the ability of a computer or a robot controlled by a computer to…
Q: Describe in your own words the meaning of the following problems: a. The differences among…
A: Answer : 1) Sequential access : In a file when computer system read and write information step by…
Q: What is the explicit expression that represents how many
A:
Q: What are the advantages and disadvantages of recording the name of the creating program with the…
A:
Q: A network must satisfy three conditions in order to be successful and efficient. Please explain in…
A: Answer:
Q: What are the advantages and disadvantages of recording the name of the creating program with the…
A: That kind of attribute must be supported by your filesystem, which not all do. It's useful for…
Q: There are two compelling reasons why layered protocols should be established. Your argument must be…
A: A layered protocol architecture offers a conceptual framework for simplifying the hard job of…
Q: Product support is impacted by the number of identified bugs in a software at the time of release.
A: Sometimes these flaws are still known, but they don't show up: For example, it's very unlikely that…
Q: The diversion of malicious traffic from one VLAN to another is one method for infiltrating a…
A: Network attacks known as "VLAN hopping" allow users on one VLAN to see communications on another…
Q: Explain why implementing synchronization primitives by disabling in- terrupts is not appropriate in…
A: Please find the answer below :
Q: A compiler that is both efficient and accurate must take a lot of factors into account. Explain.
A: Enhancing the compiler: A computer programme known as an optimising compiler aims to minimize or…
Q: iv) If the address of head node of a linked list is 100, the address of the next node after head…
A: Given: Address of the head node of a linked list is 100. Requirement: Choose correct option about…
Q: 1. The figure shown is the density curve of a distribution. Seven values are marked on the density…
A: The area under a density curve from point A to G represents probability. And we know that the sum of…
Q: w and why does a system upgrade oc
A: Introduction: The process of replacing a product with a newer version of the same product is known…
Q: Exist professional certification or licensure requirements for software developers working on…
A: Definition: Because advanced software users are empowered and enabled by certification, customer…
Q: Is the usage of user-level threads superior than kernel-level threads? What is the difference…
A: Definition: What advantages do user-level threads have over kernel-level threads? They are…
Q: Can a shared key be used to encrypt an AES key? Justify your answerHash function is compared to…
A: Advancement in Encryption Standard: The United States government selected the Advanced Encryption…
Q: Describe in your own words the meaning of the following problems: a. The differences among…
A:
Q: What precisely does it mean to speak about "distributed computing"?
A: The question has been answered in step2
Q: significance of software security in the software development process.
A: Software security is that the method of planning, building and testing software system for security.…
Q: Most systems allow programs to allocate more memory to its address space during execution. Data…
A:
Q: Which of the following is a Visual Radiator? Choose the best option t) and post on colleagues' hall…
A: Definition: Burn down charts, task boards, planning boards, narrative boards, handwritten charts,…
Q: What is the root cause of bugs? How can a software bug enter a program? Provide a few examples.
A: A bug is a defect in a computer program or system that produces undesired or incorrect results.…
Q: What distinguishes a rigid disc drive from other types of storage devices?
A: Answer:
Q: If you do not know the location of the update.txt file on your computer, print a copy.
A: Here we have given complete solution to know the location of update.txt file and print the text…
Q: Explain why implementing synchronization primitives by disabling in- terrupts is not appropriate in…
A: Answer:-
Q: One way of detecting errors is to transmit data as a block of n rows of k bits per row and adding…
A: Introduction Yes. There will also be three mistakes found. They will be caught if they are in…
Q: Do policies exist within the Linux workstation or server environment? If so, what are they? Are…
A: Yes, there are policies in place for Linux workstations and servers.
Q: Examine the components of a backup plan. What is the difference between a smartphone backup plan and…
A: Given To know about the backup plan and the difference between a smartphone backup plan and a PC…
Q: The number of encryption operations required to transmit a big file is comparable for block chaining…
A: DES's cypher block chaining mode: All cypher blocks are chained to prevent replacement. In this…
Q: Explain why implementing synchronization primitives by disabling in- terrupts is not appropriate in…
A: answer is
Q: Employee, Customer, Product, and Department are the four firm entities. a) For any three entities,…
A: A company is a system with multiple subsystems that work together to achieve the company's goals and…
Q: Do you know the most essential Compiler Phases components
A: A compiler is a program that transforms source code written in a programming language into another…
Step by step
Solved in 2 steps with 2 images

- If P ≠ NP then there does not exist a minimal-time solution to FSSP for the network topology introduced below as Variation the direct three-dimensional analogue of Kobayashi’s Variation.Subject: DLD Simplify the following function using K-map F(W,X,Y,Z) = (1,2,4,6,8,9,10,11,14,15) G(W,X,Y,Z) = Product(2,3,6,8)+d(1,4,7,10,12,13,15)Construct an undirected network diagram using the given set of nodes and arcs, also find the shortest path and distance from node A to node E using Dijkstra’s algorithm. Nodes {A, B, C, D, E} Arcs {(AB)=2, (AC)=3, (BC)=2, (CD)=1, (DB)=2, (DE)=1, (CE)=6}
- i. How can a mixed network be converted into a directed network? ii. Distinguish between the various types of arcs in network model iii. In one sentence carefully distinguish between feasible solution and optimal solutionQuestion 18 .The following weighted graph corresponds to a railway network, determine the shortest way from station a to zGiven the following nodes from A to G as shown in the diagram, determine the shortest path network from node A to all other nodes in the given cost network graph.
- Consider the Omega network and Butterfly network from p nodes in the leftmost column to p nodes in the rightmost column for some p=2^k. The Omega network is defined in Chapter 2 of the text book such that Si is connected to element S j if j=2i for or j=2i+1-p for See Chapter 2 in text book for its definition. The Butterfly network is an interconnection network composed of log p levels (as the omega network). In a Butterfly network, each switching node i at a level l is connected to the identically numbered element at level l + 1 and to a switching node whose number differs from itself only at the lth most significant bit. Therefore, switching node Si is connected to element S j at level l if j = i or j . Prove that for each node Si in the leftmost column and a node Sj in the rightmost column, there is a path from Si to Sj in the Omega network. Prove that for each node Si in the leftmost and a node Sj in the rightmost, there is a path from Si to Sj in the Butterfly network.Consider the following network: a.) Find the shortest path from node 1 to node 8 using Dijkstra’s algorithm. Write the length of the shortest path as well as the edges that compose it. b.) Write an integer programming formulation to find the second-shortest path from 1 to 8 in this network. (Hint: if the shortest path is not available, the second-shortest path becomes the shortest path.)Describe how to construct an incremental network in the Ford-Fulkerson algorithm in order to find the maximal flow through a network flow model with minimal overall cost.
- Network Routing Analysis - Algorithms Consider the following network. With the indicated link costs, use Dijkstra’sshortest-path algorithm to compute the shortest path from x to all network nodes.Show how the algorithm works by computing a table similar to Table 4.3.Computer Science Hand-execute the Ford-Fulkerson algorithm on the transport network. Find the maximum flow through the network. Identify the cut whose capacity equals the maximum flow. Your answer should include all the details of the execution clearly.As we all know, heuristic or approximation algorithms may not always provide the best solution to a problem, but they are very efficient in terms of polynomial time. (a) Propose an approximation method for the travelling salesman problem (TSP) and analyze the time complexity and limitations of the proposed approach. (2) Provide two examples of inputs for which the method in (a) produces the best and not-the best answers, respectively. (3) There should be between six and eight nodes in each network.

