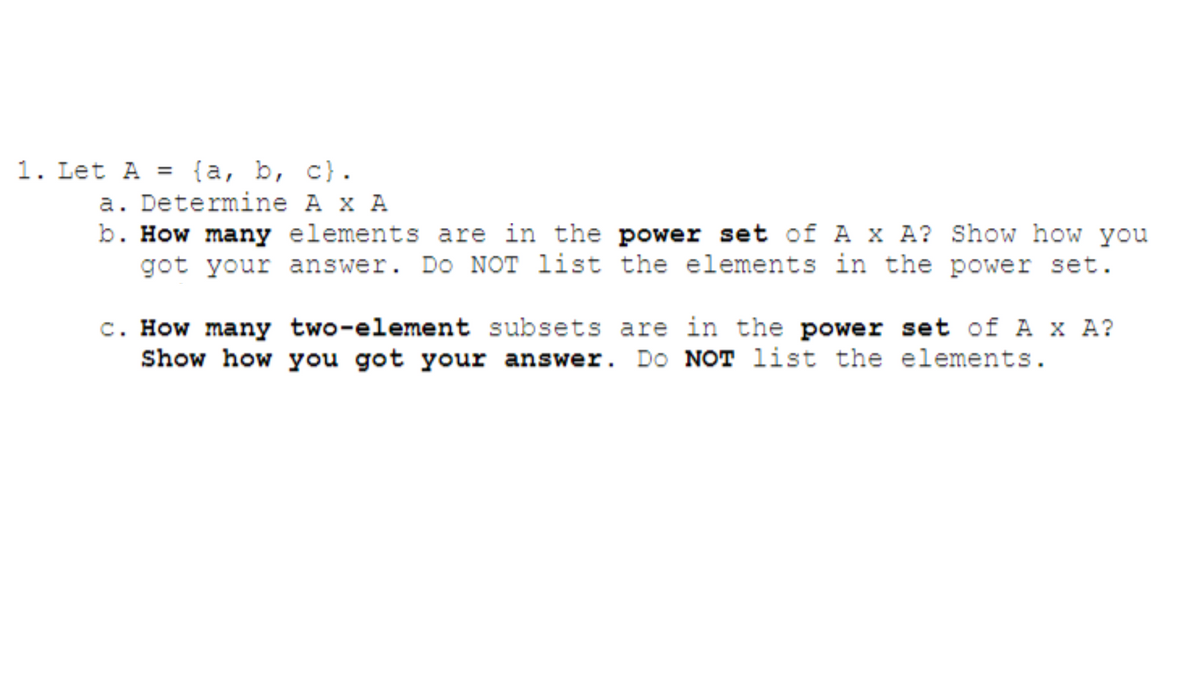
1. Let A = {a, b, c). a. Determine A x A b. How many elements are in the power set of A x A? Show how you got your answer. Do NOT list the elements in the power set. c. How many two-element subsets are in the power set of A x A? Show how you got your answer. Do NOT list the elements.
Q: 8- Determine if each of the following recursive definition is a valid recursive definition of a…
A: Recursive Function: In mathematics and computer science, a recursive function is one that defines…
Q: b. Show the result of normalizing the Airport KLX Table to 2NF
A: The question asks to normalize the Airport KLX Table to achieve 2NF and 3NF. The process involves…
Q: The tree below resulted from inserting 9 numbers into an initially empty tree. No deletes were ever…
A: This is a BST (binary serach tree).An element collection can be arranged and managed using a Binary…
Q: Write a function getNeighbors which will accept an integer array, size of the array and an index as…
A: An integer array, its size, and an index are sent to the C++ function getNeighbors, which returns a…
Q: Suppose the following words were inserted into a compressed alphabet trie, using the symbol $ to…
A: Trie is a tree like structure used for efficient search operations of keys. It is commonly used in…
Q: Illustrate that the nodes of any AVL tree T can be colored “red” and “black” so that T becomes a…
A: The relationship between AVL trees and red-black trees is a significant concept in the realm of…
Q: Options are: a. 3 b. 2 c. 5 d. 0
A: In step 2, I have provided brief answer---------------
Q: Instructions Redo Programming Exercise 6 of Chapter 8 using dynamic arrays. The instructions have…
A: In this question we have to understand and correct the code for the actual output in C++ for the…
Q: True or false? Every binary search tree is a max-heap True False
A: Each node in a Binary Search Tree (BST) data structure contains a maximum of two child nodes, which…
Q: Give a big-Oh characterization, in terms of n, of the running time of the following method.
A: The Big O notation specifies an algorithm's upper bound. It is a common mathematical notation that…
Q: analyze the time complexity and space complexity of the following algorithm
A: Time Complexity:It is a measure of how the running time of an algorithm grows as the size of input…
Q: JAVA PROGRAM Modify this program with further modifications as follows: The test case must pass…
A: Start.Initialize two ArrayLists, girlsNames and boysNames, to store the names of girls and boys…
Q: Contrast the stack data structure with other data structures, such as queues or linked lists. What…
A: Of course, let's compare stack data with two other commonly used data types: queue and linked…
Q: No program required Find a path between the two points. Make a copy of page and draw the path on the…
A: Below is the complete solution with explanation in detail for the given question about finding the…
Q: 5.01-1. Dijkstra's Algorithm (1, part 1). Consider the network shown below, and Dijkstra's link-…
A: Dijkstra's algorithm is used to find shortest path between two vertices and it is a greedy…
Q: Question 8: Consider the following array: #(59 65 72 97 75 80) a. b. Use the Selection sort…
A: Selection sort is a sorting technique which takes the smallest element in unsorted array and brings…
Q: Understand the running order of 7 functions O(1), O(n log n), O(n), O(n2 ), O(n3 ), O(log n), O(an…
A: The asymptotic upper bound of a function, often denoted using "big-Oh" notation (O()), can be…
Q: Please help draw memory diagrams for points one, two and three in the program below. I dont know how…
A: The solution is given in te below step.
Q: 2. Use the master theorem to find the following in O-notation: 1. T(n) = 4T(n/2) + n 2. T(n) =…
A: Dear Student, you have uploaded a question that has multiple sub-parts in it. As per our guidelines,…
Q: trate the following for undirected networks: a) A 3-regular graph must have an even number of…
A: This discipline, a subset of discrete mathematics, explores the relationships and properties of…
Q: the five asymptotic notations are big oh big omega theta small oh small omega please follow…
A: The table is filled and given below with detailed explanation
Q: How does insertion of a new element vary between arrays and linked lists?
A: Arrays and linked lists are fundamental data structures used in computer science to store and manage…
Q: Suppose the number 42 is inserted into the 2-3 tree pictured below. Select all the statements below…
A: After inserting the 42. in the given 2-3 tree. look like in the given below tree . and based on the…
Q: In terms of implementation, how does a doubly linked list differ from a regular (singly) linked list…
A: Data structures play a crucial role in computer science and programming, allowing efficient storage…
Q: Java source code writing - a recursive algorithm. Please use non-recursive and recursive ways to…
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT-----------------
Q: Lines 1- neg = false; 2- if (n0 O(?)
A: Big-Oh notation is the worst case time complexity of the program. It is the tightest upper bound of…
Q: Write the instruction STR R2, [R3] in hexadecimal (using 2 bytes).
A: Thе imagе shows a block diagram of a computеr systеm, with the following componеnts:Addrеss bus…
Q: Task 2 - Use the Dijkstra algorithm on the provided network for node A. Mark the order of nodes…
A: As per our company guidelines, only 3 sub parts will be answered. So, please repost the remaining…
Q: ow does microchip security work, and what measures are taken to protect against vulnerabilities and…
A: IntroductionMicrochip security is a critical aspect of modern electronic systems, ensuring the…
Q: Explain the difference between static and dynamic data structures.
A: Static data structures and dynamic data structures are two key ideas in computer science describe…
Q: in java Revers an Array of n integers Reversing an Array 1. Describe the definition of recursive…
A: Step-1: StartStep-2: Declare an array and initialize with {4, 3, 6, 2, 7, 8, 9, 5}Step-3: Declare a…
Q: Array = [10, 100, 10000, 1, 100000, 1000000, 100, 1000, 10000, 10000000, 1000000000, 100000000,…
A: Here is your solution - ( HERE NO SPECIFIC LANGUAGE IS MENTIONED SO I AM USNG JAVA )
Q: In a company called BCCD engineers are charged of developing different types of applications. Each…
A: In this ERD diagram , it shows the entities involved and their reationship.
Q: seven are located in China, including the world's largest container port in the world in Shanghai.…
A: Answer is explained below in detail
Q: Select the correct claims below. Observe that the first cases are about the big-O notation but the…
A: In computer science, particularly in algorithm analysis, Big-O notation and Big-Theta notation are…
Q: For the AVL Tree insert the value 18. What type of imbalance does it cause? Show the result after…
A: AVL tree is the self balancing binary search tree (BST) where a difference between the height of the…
Q: Describe how the Greedy algorithm works to solve the Leap Line problem. Talk about jumping,…
A: In this question we have to describe on how the greedy algorithm works for Leap Line problem.Let's…
Q: Discuss the time complexity of basic operations in a stack.
A: A stack is a data structure that follows a Last in First Out (LIFO) order.This means that the last…
Q: Given a jungle matrix N*M: jungle = [ [1, 0, 0, 0], [1, 1, 0, 1], [0, 1, 0, 0], [1, 1, 1, 1,] ]…
A: Python program with output snapshot and explanation is given below
Q: i need help with this can you please show pictures of each step on how to find the array of 26, can…
A: Step1: if the given array and searching element equal then element to be found Step2: else if the…
Q: 1. BFS (Breadth First Search) and DFS (Depth First Search) algorithms on graphs. a. Represent the…
A: Algorithm for Breadth First Search (BFS) :1. Create a queue and enqueue the source node.2. Create a…
Q: (DecBin2) Write a program that will accept a number in decimal and display the number in binary. In…
A: StartDeclare necessary variablesRead the decimal number from userConvert it to binary numberDisplay…
Q: a) What is a hash function? b) What is a collision? Which are the characteristies to address…
A: A hash function is a mathematical function that takes an input (or 'message') and returns a…
Q: 2. Minimum Spanning Tree (MST) algorithms. 10 8 2 9 B 12 5 E 6 4 a. Apply Kruskal's algorithm to the…
A: In a weighted graph, Dijkstra's algorithm is a greedy graph traversal technique that finds the…
Q: Java source code writing - a recursive algorithm. Please use non-recursive and recursive ways to…
A: In this question we have to write a java program for a recursive plaindrome problem.Let's understand…
Q: Consider the following undirected graph: His h If you traverse the graph using the Breath First…
A: It is the most common search strategy for traversing a tree or graph.This algorithm searches breadth…
Q: , Is there are other functional dependencies? If so, what are they? If not, why not? Do you believe…
A: The question asks to identify functional dependencies in a dataset of pet records and consider…
Q: Using the diagram provided, assume the node P is the goal node and that the search will end when the…
A: BFS stands for "Breadth-First Search," and it is a fundamental graph traversal algorithm used in…
Q: Consider a Binary Search Tree (BST) and its operations. Which of the following algorithms would take…
A: A Binary Search Tree (or BST) is a type of tree with a list of organized nodes. Each node has two…
Q: Let f(n) = (0.1)^5 n^2-7n + 2 n^4 + 16 n^(3.5) + 100. Which of the following statements is true?…
A: We are given a function f(n) and we are asked which option is fit for this function.We can check…
Step by step
Solved in 4 steps with 3 images
