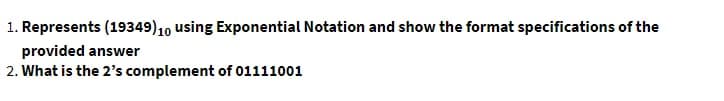
1. Represents (19349) 10 using Exponential Notation and show the format specifications of the provided answer 2. What is the 2's complement of 01111001
Q: computer science - How can a process data flow diagram be used to explain and evaluate a technique?
A: Introduction: In computer science, DFD, also known as a data Flow Diagram, is a typical approach for…
Q: Describe SCRUM and why it is so important in the software development process
A: Introduction: SCRUM is the most important approach in software development since it assists in the…
Q: Internet apps provide consumers with two sorts of Internet services. Is there anything that sets one…
A: Intro Consumers have access to two distinct categories of online services via the use of internet…
Q: In the future, what role will machine learning play? What artificial intelligence applications are…
A: Introduction: In the manufacturing business, machine learning techniques may be used to monitor…
Q: . Do the following without using a cal- culator or a computer, but check your answers with a…
A: Do the following without using a calculator or a computer but check your answers with a calculator…
Q: After a specific amount of time has passed, an initial block statement can no longer be utilised.
A: Intro Initial block: An initial block cannot be synthesized or turned into a hardware schematic with…
Q: 3. Consider the following network address: 212.15.6.0/29 a. How many subnets are there in this…
A: ANSWER:
Q: [CLO-5] What is the value of the variable ss after the following code is executed? int x[ 7 ] =…
A: What is value of variables ss after the following code is executed???
Q: Companies like Amazon and Facebook and Google are so dominant that they really have very little…
A: Employees are said to be truly motivated to achieve their goals via healthy competition in the…
Q: Your home network consisting of 1 desktop computer, 1 wireless laptop, 1 network printer, 1 wireless…
A: Given that, the network consists of total 3 hosts and 1 router. The router is wireless and there are…
Q: 1. Write a shell script to perform either multiplication or division operations on the two numbers…
A:
Q: What functions does a memory management unit (MMU) perform?
A: Introduction: The memory management unit (MMU) on a computer is the hardware responsible for…
Q: Objective To provide you with your first experience programming in C. We'll try to give you a solid…
A: According to the information given:- We have to print diamond pattern in c program.
Q: Which view in EnCase allows you to see the device with the sectors or clusters for each file?
A: Which view in EnCase allows you to see the device with the sectors or clusters for each file? The…
Q: Qno 2: Normalize the following Customer-Order Relation up to 3rd Normal Form, but step by step show…
A:
Q: List out any two practical examples of Closed-loop control systems and explain anyone in detail with…
A: Two practical examples of Closed Loop Control Systems in real-world applications: Voltage…
Q: Discuss appropriate technology briefly. Determine and explain how a specific piece of relevant…
A: Introduction: Appropriate technology is any thing, idea, method, or practise that improves human…
Q: Check whether the following gramm is LX (0) or not. E>E+T\T\ T>TF/F F> (E)lid
A: Dear Student, Given grammar is not LR(0) grammar. The Proof and explanation has been given below.
Q: Determine the time complexity function of the program snippet below, int f1(int n) { if (n = 1)…
A: A) Let the original time complexity be T(n) Here recursion is used where in each iteration we reduce…
Q: 1-How can the CPU recognize the device requesting an interrupt? 2-Since different devices are likely…
A: The answer for the questions is given in the following steps for your reference.
Q: How is routing accomplished in a wide area network?
A: Introduction: A wide area network can connect many NANs to collect data from them and then transfer…
Q: Explain the differences between Abstract Classes and Interfaces in Java.
A: Explain the differences between Abstract Classes and Interfaces in Java.
Q: What is the difference between EPROM, EEPROM, and Flash Memory, and why should you care?
A: Introduction: Flash employs NAND memory, EEPROM NOR. Flash may be erased block-by-block, not EEPROM…
Q: How does the Internet Explorer Box Model Bug effect you, and what is it?
A: The Internet Explorer box model issue is a well-known vulnerability in an implementation of the web…
Q: T F F T L F FL A T T T T LL F LL F F F 9 F Jº T F T F T F T TI F r pvr T T T LL F T T T F W F F F T…
A:
Q: Find a closed form representation for the function defined recursively by f(0) = 5 and…
A: We have to find the solution of the given recurrence relation and prove the solution using induction…
Q: Write a complete method to create a modified ArrayList. Method Specifications The method takes in an…
A: Here I have defined the function named modifyArrayList(). In this function, I have used a loop to…
Q: How many characters can be represented by Unicode?
A: Introduction: Unicode is the concept in the JAVA programming language where every character has a…
Q: List out any two practical examples of Closed-loop control systems and explain anyone in detail with…
A: According to the question we have to list out any two practical of the close loop control system and…
Q: Name three crucial testing categories that developers typically avoid performing and explain why.
A: Introduction: Software Testing is a method to check whether the actual software product matches…
Q: package assignment; public class A4PassFailDriver ( public static void main(String[] args) { //NOTE:…
A: Please do like it will encourage me a lot,
Q: Enter an integer n from the keyboard 1. Check if n is divisible by 3 then print the content "n is a…
A: The code for given problem is solved using C programming language below. Algorithm: The algorithm…
Q: So, in a telecommunications network, what precisely is a protocol and how does it work?
A: Definition: A communication protocol is a system of rules that allows two or more entities of a…
Q: Explain the instruction (fliplr) with example? Your answer
A: The answer is given in the below step
Q: Please help... C++ Basic Arithmetic You are a cook in a restaurant. You need exactly 3 crabs to cook…
A: PROGRAM INTRODUCTION: Include the required header files. Start definition of the main function.…
Q: What is the Internet's mechanism?
A: Introduction: The internet is a global computer network that transmits data and media across a…
Q: Determine the three most common challenges faced with concurrent transaction processing. In your…
A: Intro Controlling concurrency: Concurrency control is the practice of coordinating the simultaneous…
Q: process Allocation max ABC 562 Be PO P1 Pz P3 P4 ABC 322 01 0 111 323 211 210 561 996 324 Avaliable…
A: A resource allocation that is use to avoid deadlock is called Banker’s algorithm. A 1-D matrix is…
Q: What are any more applications for Excel that I haven't considered? Please expand on each of the…
A: Introduction: Microsoft Excel is the most widely used spreadsheet program in practically all…
Q: Explain the instruction (fliplr) with example? Your answer
A: The answer is given in the below step
Q: What is the output of the following code if the value of the variable A is equal to 80: if (A > 90 )…
A: Hello Student This is very simple explaination
Q: What is the definition of routing? Describe in detail the main components of a router and the…
A: Introduction: Routing: Routing is simply the act of finding a path across several networks, which…
Q: hello, i need a python code language for doing electricity cutoffs in lebanon using the meta…
A: According to the question we have to write Python code for doing electricity cutoffs using meta…
Q: Determine whether or not the following statement is a tautology or not and give reasoning. If you…
A:
Q: What is the size of my ROM if I want a maximum output of 6 bits? draw a diagram
A: The answer of the question is given below
Q: Two hosts simultaneously send data through the network with a capacity of 1 Mpbs. Host A uses UDP…
A: The reason why UDP is faster than TCP is due to the absence of an acknowledgement packet (ACK) that…
Q: Consider the following scenario: A school wants to automate their attendance taking. Attendance will…
A: We have a different solutions of the scenario those are And we provide two different Reasons.
Q: For Problem # 1-5 Solve the equations using binary values in signed integer register "R" of size…
A: We have the register "R" of size four (4) 1) 2+3 = ? Binary values representation in signed…
Q: What is the point of performing a vulnerability assessment?
A: Intro Vulnerability assessment is a systematic view of security weaknesses in the information…
Q: Let P and V are two atomic operations P represents wait and V represents signal operation. Counting…
A: Although I have provided the appropriate response, it would be wonderful if you were to become…
Step by step
Solved in 2 steps with 2 images

- What would the word WUUB be deciphered to if it was encoded as (15P + 18) mod 26 (Hint use results of (e) to find the inverse of 15.Perform the Infix - Postfix notation and Postfix - Infix notation. Show your solutions.Convert the following equations from infix to postfix: 2^3^3+5*1 233^^51*+ 11 + 2 - 1 * 3 / 3 + 2 ^ 2 / 3 11 + 1 3 * 3 / - 2 2 ^ 3 / +
- Draw the SD of the Moore and mealy binary sequence detector w/ the ff sequences a) 10110 b) 00110 c) 011Assume numbers are represented in 8-bit twos complement representation. Show the calculation of 11000011 - 11101000. It's 195 minus 232, but I don't get how to solve it when the second number is a higher value than the first. How do I subtract this?Draw the time domain representation of ASK, FSKand PSK of the binary data 110001010111
- What is the 5-digit hexadecimal representation of -24, -31, -1, +25, +35?For the weighted codes (a) 3,3,2,1 and (b) 4, 4, 3, -2 for the decimal digits, determine all possibletables so that the 9’s complement of each decimal digit is obtained by changing 1’s to 0’s and 0’s to1’sCreate a Hamming code (k, n) = (7,4) for the detection and correction of errors in word codes
- Find the Gray code sequence of 12 code words.& 8.The maximal value of num = 16..Questions from previous year's practice exams the professor did not give answers for (a) Perform the following conversions: (i) -1810 to 6 bit 2’s complement. (ii) ABC16 to base 2. (iii) 0.510 to base 2. (b) Give a logic equation in sum-of-products form for the logic function F specified by the following truth table. Simplify your logic equation to the maximum extent possible. (first image) (c) Consider the addition of 4 bit values a3a2a1a0 and b3b2b1b0. Give a logic function for the “carry-in” to the most significant bit position, using quantities gi = ai · bi , pi = ai + bi , and the “carry-in” to the least significant bit position CarryIn0.(d) Give a truth table for a 2 data input, 1 selector input multiplexor. (e) The IEEE 754 floating point standard allows some numbers to be represented in unnormalized form (called denormalized numbers, or “denorms”). Why?

