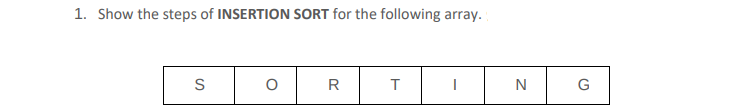
1. Show the steps of INSERTION SORT for the following array. S 0 R T I N G
Q: Is Data Model a positive or negative attribute?
A: Response to the posed query: The data model has various drawbacks, but the two most significant ones…
Q: Given a main program that reads the number of one word names followed by the list of names, complete…
A: Below I have provided C++ Programming. Also, I have attached the screenshot of the code and output…
Q: Object-oriented ideas such as encapsulation and polymorphism are linked with object models.
A: EncapsulationThis is a style of programming where implementation details are hidden. It…
Q: of Ethics in brief d
A: Solution - In the given question, we have to describe the ACM Code of Ethics in detail.
Q: Consider the impact of Human-Centered Design (HCD) concepts on User Experience Design (UXD)…
A: A collection of programs or a set of instructions designed to carry out a specific function is…
Q: Describe the risk posed by the loss or theft of mobile devices and media.
A: In this question we need to explain the risk factors if someone's mobile device or media is lost or…
Q: Write notes on mobile code and agents, and the main characteristics of mobile agent and its host.
A: Let's discuss the following terms one by one 1. Mobile Code 2. Mobile Agents and it's hosts
Q: Compare the main memory organization schemes of contiguous-memory allocation, pure segmentation, and…
A: Please find the answers in the following steps.
Q: the programming expression "resisting the impulse to code" mean?
A: Introduction: According to the old saying in programming, what does it mean to "fight the impulse…
Q: What disadvantages does symmetric encryption's key management have?
A: INTRODUCTION: Symmetric encryption employments a single key to scramble and decode. In the event…
Q: This is an example of a? Choose the most specific answer. 20 100 O graph 23 O weighted graph O tree…
A: In this we have to tell what the given mentioned picture represents .
Q: It is essential to provide a list of the most common network topologies. Which do you consider to be…
A: Topology is a term that refers to a graphical depiction of how the computers are linked to one…
Q: How is the hash value of a message protected? Does it function without the secret key?
A: Message authentication is an additional kind of security. Data secrecy is guaranteed by the message…
Q: What does it mean to host content on the Internet?
A: Introduction: The reliable and safe storage space web hosting services provider is how they work.…
Q: using python create an Employee class that inherits from the Person class and stores employee…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: Compare the main memory organization schemes of contiguous-memory allocation, pure segmentation, and…
A: Contiguous memory allocation means the data is allocated continuously in the main memory. Pure…
Q: Question 9 options: It is the process of organizing observations into distinct groups based on a…
A: Given: Which statement best describes k-means cluster analysis?
Q: Describe how usability contributes to and enhances the user experience.
A: The Answer is in given below steps
Q: Five typical network topologies should be distinguishable. Which do you consider to be the most…
A: Types of Network Topology: In a star topology, each device is coupled to a single hub by a wire.…
Q: Can a shared key be used to encrypt an AES key? Justify your answerHash function is compared to…
A: Advancement in Encryption Standard: The United States government selected the Advanced Encryption…
Q: This is an example of a ? Choose the most specific answer. of tree graph O digraph O weighted graph…
A: - We have to talk about the structure we are seeing in this picture. - The options :: First…
Q: Q7. The output of the following code is 'University. import re pattern 'University' "Tiengeng…
A: Given python program contains a string variable pattern which stores the string University. Then…
Q: Convert the following grammar to Chomsky normal form. SASA | A | E A → aa | E Show that the language…
A:
Q: What use does "debugging" serve?
A: The process of locating and resolving problems is called debugging. problems in software code that…
Q: n modern encryption, plaintext is encoded in binary form. Each bit in a bit stream is encrypted into…
A: Introduction: Plaintext digits are linked with a stream of pseudorandom figure digits to create a…
Q: The diversion of malicious traffic from one VLAN to another is one method for infiltrating a…
A: Network attacks known as "VLAN hopping" allow users on one VLAN to see communications on another…
Q: Write a program that reads integers from the user and stores them in a list. Your program…
A: Note: In-order to run the code successfully, use the proper indentation as made in the program…
Q: A decision support system (DSS) is an information system that aids a business in making…
A: See how the aforementioned issue is resolved next. The following are various parts of the DSS…
Q: What happens if an attacker attempts to alter the Tag (the MAC) and ciphertext while the message is…
A: Introduction: Although MAC characteristics are similar to cryptographic hash features, there are…
Q: In other words, process modeling should not be limited to the creation of information technology…
A: Process Modelling: The visual portrayal of business tasks or exercises is known as interaction…
Q: What are the distinctions between relational, conceptual, and conceptual data modeling?
A: The above question is solved in step 2 :-
Q: Consider the importance of wireless networks in developing countries today. Physical connections and…
A: Launch: Think of how crucial wireless networks are in the emerging nations of today. LANs and…
Q: Are alternatives advantageous? Provide an instance when encryption is advantageous. for end-to-end…
A: Link encryption is a type of communication authentication in which all data on both ends of a…
Q: List and describe the qualities of the perfect cryptographic hash function.
A: Hash function for cryptography The term "cryptographic hash function" refers to a hashing algorithm…
Q: Is there a certain network architecture that you believe is optimal for this circumstance?
A: The physical or conceptual layout of a network is its topology. It describes how nodes are…
Q: Q8. The output of the following code is [] (no match). import re cess string, pattern = '_ \ $'…
A: Explanation:
Q: Do you understand the meaning of a "poison packet attack"? Use a few instances to illustrate your…
A: The Poison packet triggers a bug in the system's network handling software, causing it to crash and…
Q: Why are segmentation and paging sometimes combined into one scheme=
A:
Q: Why does a private communication between Alice and Bob use the shared symmetric key instead than…
A: Solution: For private communication between Alice and Bob use the shared symmetric key instead than…
Q: What are the pros and cons of a database management system? (database administration software
A: A database is a type of computer program that talks to end users, other computer programs, and other…
Q: SEARCH IN MATRIX You are give a matrix (a list of lists) of DISTINCT integers and a target number.…
A: Below I have provided Python Programming . Also, I have attached the screenshot of the code and…
Q: How is polymorphism implemented?
A: The ability to interpret data in several formats is known as polymorphism. Poly signifies many,…
Q: 2. 25 Show the steps of SELECTION SORT for the following array of elements in ascending order. 35 65…
A: The answer is given below. Algorithm:
Q: Explain why implementing synchronization primitives by disabling in- terrupts is not appropriate in…
A: Single processor system A single processor system contains just a single processor. So just a…
Q: An attacker attempts to change the Tag (the MAC) and the ciphertext while deploying a MAC (message…
A: MAC is likewise called tag. It is an instructive piece utilized by source and recipient for the…
Q: What is so challenging about a game that just employs run-length encodings?
A: RLE (Run-length encoding) RLE is a type of lossless data compression where runs of data (sequences…
Q: What is the meaning of the word "debugging?"
A: Debugging is the procedure for locating and correcting problems. problems in software code that…
Q: In the simple linear regression equation ŷ = bo + b₁x, how is b₁ interpreted? it is the change in x…
A: The solution is provided below.
Q: Justification for why you consider a web server to be the ultimate system
A: A computer specifically intended for the operation of websites is known as a web server. Web pages…
Q: Q7. The output of the following code is 'University'. import re pattern University' seekerking =…
A: re standa for regular expression. It is helpful in checking if a string or a sub string of a string…
Step by step
Solved in 2 steps with 1 images

- Using selection sort, Sort the following array from greatest to least write down what the array AA and the sortedsorted array will look like at each step.Show steps of insertion sort for the given array. You may need to add more rows to the table.Sort the array (D, G, J, F, A, C) using selection sort (show the array after each step).
- 1. Sorting• Begin by filling an array with random numbers:import numpy as npnp.random.seed(1012)DATASIZE = 1000MAX_VALUE = 10000000data = np.random.randint(0, MAX_VALUE, size=DATASIZE)• Write a function that is passed a numpy array. The function should walkthrough the array element-by-element, comparing the current element tothe next element. Swap if the next is smaller than the current – sortingthese two elements.• Write a second function that calls the above function n times, where n isthe number of elements (size) of the array. Pass the same numpy arrayeach time. 2. Bubble Sort• The sort from part 1 can be improved. If the data passed to be sorted isalready sorted, it still performs all of the work, as if the array was notsorted.Make two improvements:• Change the first function (the one that does the comparisons), so that it returns aboolean that states whether the array is sorted. Make use of that boolean to stopcalling the first function if the array is sorted.• Consider…1. Sorting• Begin by filling an array with random numbers:import numpy as npnp.random.seed(1012)DATASIZE = 1000MAX_VALUE = 10000000data = np.random.randint(0, MAX_VALUE, size=DATASIZE)• Write a function that is passed a numpy array. The function should walkthrough the array element-by-element, comparing the current element tothe next element. Swap if the next is smaller than the current – sortingthese two elements.• Write a second function that calls the above function n times, where n isthe number of elements (size) of the array. Pass the same numpy arrayeach time.Binary Search in descending order We have learned and practiced the implementation of the binary search approach that works on an array in ascending order. Now let’s think about how to modify the above code to make it work on an array in descending order.
- Please Help me with This Question We are given two sorted arrays (all elements are in ascending order. We need to merge these two arrayssuch that the initial numbers (after complete sorting) are in the first array and the remaining numbers are inthe second array.3. Selection Sort• The idea in a selection sort is that you locate the largest item out of a set ofunsorted items, and move it into position at the end of the unsorted items. Asorted region grows one item at a time, while an unsorted region shrinks.• As done in Part 1, fill an array with random numbers.• Write a function that locates the largest element in the portion of the arraybeginning at the start of the array, up to a given index, and swaps the largestitem with the item at the given index.• E.g. If searching a[0] to a[7] locates the largest item at a[4], a[4] and a[7] would beswapped.• Write a second function that calls the first function repeatedly, until the entirearray is sorted. (Each time the first function is called, it will search one fewerelement)Consider the algorithm for insertion sort shown below. The input to this algorithm is an array A. You must assume that indexing begins at 1. Follow this algorithm for A[1..4] =< 7, 9, 6, 8 >. Specifically, please indicate the contents of the array after each iteration of the outer for loop.
- Q.No.1. In computer science, binary search, also known as half-interval search, is a search that finds the position of a target value within a sorted array. Binary search compares the target value to the middle element of the array. Develop the pseudo code that takes any number from user and performs Binary Search.Given the following set: {b, f, g, h, a, c} You are required to write a C++ programming code that will perform the following operations on the given elements. Write an array code in C++ that will: • Print the first and the last "sorted" character. [5] • Add character "z" in the given array, then print the new set array. [5]Consider the algorithm for insertion sort shown below. The input to this algorithm is an array A. You must assume that indexing begins at 1.





