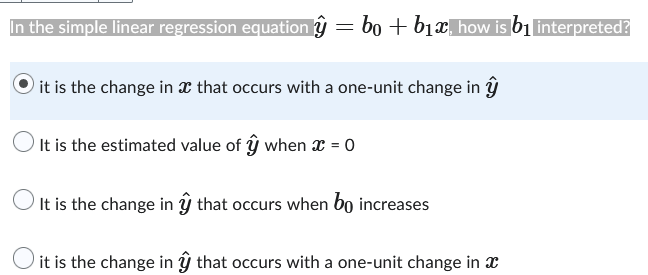
In the simple linear regression equation ŷ = bo + b₁x, how is b₁ interpreted? it is the change in x that occurs with a one-unit change in It is the estimated value of ŷ when x = 0 O It is the change in ŷ that occurs when bo increases it is the change in ŷ that occurs with a one-unit change in x
Q: What are REST web services and why are they so prevalent?
A: About REST web services RESTful web services are designed to work optimally over the Internet. REST…
Q: What is the inorder traversal of this tree? E X H
A: What is a Tree? A tree, a commonly used abstract data type, depicts a hierarchical tree structure…
Q: Five typical network topologies should be distinguishable. Which do you consider to be the most…
A: Types of Network Topology: In a star topology, each device is coupled to a single hub by a wire.…
Q: of Ethics in brief d
A: Solution - In the given question, we have to describe the ACM Code of Ethics in detail.
Q: Is encryption of the connection and data from end to end possible? What is the advantage? Describe a…
A: The above question is solved in step 2 :-
Q: The use of print statements or manual walkthroughs for debugging has both advantages and…
A: Launch: A developer will use "print" statements to instrument their application throughout the…
Q: a) n³+15n+2 is O(nª) b) 2n³ +25m is (n²)
A: Here in this question we have given two asymptomatic equation and we have asked to prove them using…
Q: Describe the many technologies that enable users to transmit vast quantities of data over any…
A: Digital Subscriber Line (DSL): Also known as a digital subscriber loop, DSL is a communication…
Q: What are the speed and cost differences between main and secondary storage?
A: Main storage:It is primary storage, a form of data storage ,typically refers to as Random Access…
Q: This is an example of a ? Choose the most specific answer. of tree graph O digraph O weighted graph…
A: - We have to talk about the structure we are seeing in this picture. - The options :: First…
Q: What alternatives exist to a PKI-based system in the case that he forgets his password?
A: PKI-Based System: A public key infrastructure (PKI) is a system for the production, distribution,…
Q: How can you identify between the many IT project management tools and technologies?
A: Given: Differentiate the technologies and tools that support information technology project…
Q: Define WAP, and explain the model working of it.
A:
Q: As they function, computers create heat. Is there anything more regarding computer cooling systems…
A: Institution: Computers create heat. Discuss computer cooling types and relevance. They manage…
Q: Describe how usability contributes to and enhances the user experience.
A: First let's understand what is usability . Then we can understand the use of it to enhance the…
Q: 2. Analyze the below program segment and find the syntax error. /* Tracing The Error*/ cin >>…
A: In this segment of code, there is problem in the syntax of all three lines.…
Q: What code would you use to display "Good Afternoon" in a message box?
A: A message box is a specialized dialogue box employed to convey specific information to the user. In…
Q: Comparing cypher block chaining to cypher feedback mode in terms of the number of encryption…
A: The DES (Date Encryption Standard) cypher block chaining mode is as follows: It is a sort of cypher…
Q: Q5. The output of the following code is 'tiangong@tiangong.edu.cn'. import re pattern = '[a-zlt ?…
A: Here is the answer below:-
Q: It may be difficult for application proxies to interpret end-to-end encryption due of its…
A: Gateway at the application levelThis kind of device—technically a proxy and sometimes referred to…
Q: Comparing cypher block chaining to cypher feedback mode in terms of the number of encryption…
A: The above question is solved in step 2 :-
Q: Sending a large file requires the usage of cypher block chaining or cypher feedback mode. How much…
A: The DES (Date Encryption Standard) cypher block chaining mode is as follows: To prevent block…
Q: What's the difference between logical and physical data flow diagrams?
A: The data flow diagrams represent the flow of information in a process or system. There are two types…
Q: You are expected to solve the following question with the C++ programming language; 1-Write a…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: Web servers use a range of technologies to generate personalized web pages that cater to the demands…
A: The web servers use the following technologies, in that order, to respond to client requests: It is…
Q: An attacker attempts to change the Tag (the MAC) and the ciphertext while deploying a MAC (message…
A: MAC is likewise called tag. It is an instructive piece utilized by source and recipient for the…
Q: How may block and stream ciphers exchange keys, and why should they be different?
A: Symmetric cryptography ciphers contains 2 main categories: block ciphers and stream ciphers.Block…
Q: Prove that (1+00*1) + (1+00*1) (0+10*1) (0+10*1) = 0*1 (0+10*1) *
A: To prove:- (1 + 00*1) + (1 + 00*1) (0 + 10*1) (0 + 10*1) = 0*1 (0 + 10*1)*
Q: Are alternatives for end-to-end data and connection encryption available? Why is this advantageous?…
A: Data encryption is a technique for keeping information secret from unauthorized third parties. On…
Q: Do you understand the meaning of a "poison packet attack"? Use a few instances to illustrate your…
A: Complete answer is given below:
Q: From a business perspective, describe the advantages of having a data-driven website.
A: A data-driven website is one whose administrators can easily make changes to the website. In…
Q: Based on Don Norman's concept of user issues, explain how formative evaluation may be used to…
A: Answer: Introduction: These evaluations occur throughout the redesign process, and the information…
Q: This is an example of a ? Choose the most specific answer. tree O graph O digraph O weighted graph
A: Complete answer is given below:
Q: Debugging is the process of discovering and correcting bugs. What relevance does this have to…
A: Debugging is the method involved with finding bugs for example mistake in programming or…
Q: What is the inorder traversal of this tree? L M) (Q) E (Z) (A P (J) H G) (K B S (T) (X)
A: Inorder Traversal: An inorder traversal strategy follows the Left Root Right approach. Here, Left…
Q: What software development issues can cause software system failure later on? O Increasing system…
A:
Q: Is encryption of the connection and data from end to end possible? What is the advantage? Describe a…
A: Introduction of Link Encryption A message moving through a network is encrypted and decrypted at…
Q: What happens if an attacker attempts to alter the Tag (the MAC) and ciphertext while the message is…
A: In cryptography a message authentication code (MAC), sometimes known as a tag, is a short piece of…
Q: Consider a design team that want to discover if their suggested prototype design would boost user…
A: Methods of Designing Evaluations are Designed. Pass-fail evaluation, evaluation matrices, and SWOT…
Q: Is it feasible to modify the Tag (the MAC) and the ciphertext using a MAC (message authentication…
A: Institution: The abbreviation for the tag is MAC. It is a fact utilised by both the sender and the…
Q: Examine critically the many uses of the conventional costing technique.
A: Answer: Standard Costing: Standard costing is a variance analysis technique used to manage…
Q: Is connection and data end-to-end encryption possible? What is the value? Describe a scenario in…
A: Introduction: A communication encrypted with a public key can be decrypted using a private key in…
Q: Write a C# code to find the second largest integer in an array using only one loop.
A: The below code snippet is Find the second highest value in an array using C#
Q: please solve with computer no with handwrite What are the major drawbacks of flooding and how…
A: Here in this question we have asked that what are drawback of flooding and how gossiping is…
Q: If you have followed the debugging technique and are still unable to resolve the issue, what are…
A: There is no perfect technique for fixing all issues in your code, however there are some effective…
Q: Q8 Using only R studio programing: Create one function that can convert the number base 10 to number…
A: Here is the r code: See below steps for code and output:
Q: What is a cost model that uses algorithms? What disadvantages does it have in comparison to other…
A: The question has been answered in step2
Q: Differentiate the many types of Web architecture
A: Web architecture is the applied construction of the World Wide Web. The WWW or web is a continually…
Q: Utilizing technology and information resources, investigate health information system-related…
A: Health information system (HIS) A health information system (HIS) is a system designed to handle…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Say that you have the following initial settings for binary logistic regression: x = [1, 1, 3] w = [0, -2, 0.75] b = 0.5 2. Given that x's label is 1, what is the value of w_1, w_2, and w_3 at time t + 1 if the learning rate is 1? For this problem, you may ignore the issue of updating the bias term. 3. What is the value of P(y = 1 | x) given your updated weights from the previous question? 4. Given that x's label is 1, what is the value of the bias term at time t + 1 if the learning rate is 1? 5. What is the value of P(y = 1 | x) given both your updated weights and your updated bias term? 6. Given that x's label is 0, what is the value of P(y = 0| x) at time t + 1 if the learning rate is 0.1? Round your answer to the nearest 1000th as a number [0, 1].What is the code in Stata for this question? Run the linear regression given by wages = β0 +β1education+β2workexp+β3unionmember +β4south+ β5−9occupation + β10female + u where wages=hourly wage in US dollars; education=years of schooling; workexp=years of work experience; unionmember=a dummy variable equal to ”1” if a person is a union member, and ”0” otherwise; south=a dummy variable equal to ”1” if a person lives in the south, and ”0” otherwise; occupation=a categorical variable equal to ”1” if a person’s occupation is ”management”; ”2” if it is ”sales”; ”3” if it is ”clerical”, ”4” if it is ”service”, ”5” if it is ”professional” and ”6” if it is ”other”. Please make sure to use ”other” as the base category; female =a dummy variable equal to ”1” if a person is female, and ”0” if a person is male.You have been hired by the European Space Agency to build a model that predicts the amount of oxygen that an astronaut consumes when performing five minutes of intense physical work. The descriptive features for the model will be the age of the astronaut and their average heart rate throughout the work. The regression model is OXYCON = w[0] + w[1] × AGE + w[2] × HEARTRATE
- Develop a simple linear regression model (univariate model) using gradient descent method for experience-salary datasets as it is shown on the following table. Once you got the model, check how close the predicted values against the ground truth and calculate the total error (mean square error) and the accuracy R^2.Which statements are true about LASSO linear regression? Group of answer choices has embedded variable selection by shrinking the coefficient of some variables to exactly zero. has one hyper-parameter lambda (The regularization coefficient) which needs to be tuned if there are multiple correlated predictors lasso will select all of them adds the L2 norm of the coefficients as penalty to the loss function to penalize larger coefficientsA Ridge Linear Regression adds the sum of the squared values of the coefficients to the loss function to penalize large coefficients. Group of answer choices True False
- ) Develop a simple linear regression model (univariate model) using gradient descent methodfor experience-salary datasets as it is shown on the following table. Once you got the model, checkhow close the predicted values against the ground truth and calculate the total error (mean squareerror) and the accuracy R2.No Experience Salary ($) PredictedTuition($) Applicant Pool Applicant 950 76210 11040 1225 78000 10940 1325 67420 8670 1350 70380 9040 1500 62580 7410 1675 59260 7080 1800 57930 6350 1975 60130 6110 a.develop the multiple regression equation for these data. b. What is the coefficient of determination for this regression equation? c. Determine the forecast for freshman applicants for a tuition rate of $1700 per semester, with a pool of applicants of 63000. CAN YOU SHOW ME ALL THE ANSWER STEP STEP WİTH EXCELLDevelop a simple linear regression model (univariate model) using gradient descent methodfor experience-salary datasets as it is shown on the following table. Once you got the model, checkhow close the predicted values against the ground truth and calculate the total error (mean squareerror) and the accuracy R2.
- The temperature T (in °C) and length L (in mm) of a heated rod is given in the following table, if: L = a + bT where, a and b are constants, find the best value of constants for each data by using linear regression fit. L (mm) 20 30 40 50 60 70 T(°C) 600.1 600.4 600.6 600.7 600.9 601.0I need to plot the data from a simple linear regression with its values x and y with the fitted y values from fitting a logistic regression model. How do I plot the x values with two different y's, y values on the left side with fitted y values on the right? I want to generate the fitted/predicted y values using logistic regression and then create a plot using all those three variables? Here is an example of my SAS code that doesn't work. data coupons;input redeemed discount;cards;100 5147 9176 11211 13244 15277 17310 19343 21;run; ods graphics on;proc logistic data=coupons;model redeemed(event='1') = discount;effectplot;run; It give me this warnings and I do not understand…. NOTE: Option EVENT= is ignored since LINK=CLOGIT. NOTE: PROC LOGISTIC is fitting the cumulative logit model. The probabilities modeled are summed over the responses having the lower Ordered Values in the Response Profile table. Use the response variable option DESCENDING if you want to reverse the assignment of…In R, a logistic regression model’s “response” will produce _________ when applied to a scoring data set using the predict() function. A binary class prediction A confidence percentage for the positive dependent variable outcome Confidence percentages for the positive and negative dependent variable outcomes A binary class prediction and confidence percentages for the positive and negative dependent variable outcomes In R, if the dependent variable is coded using words such as yes/no or true/false, which function will convert the dependent variable to an acceptable form for logistic regression? cast() as.numeric() convert() as.factor()

