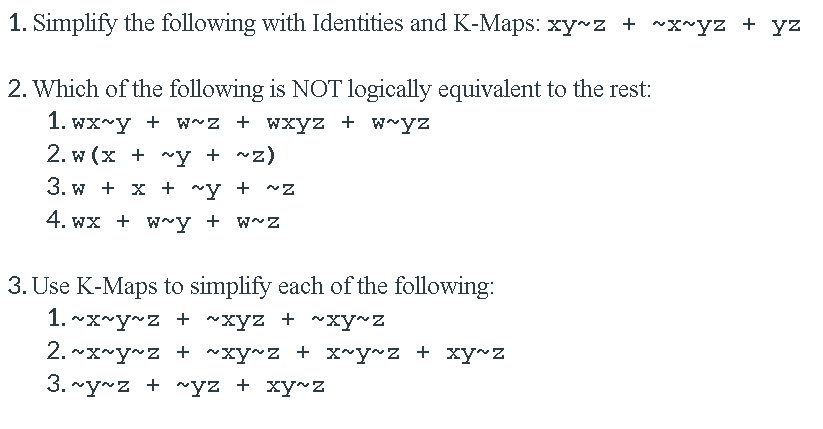
1. Simplify the following with Identities and K-Maps: xy z + ~x~yz + yz 2. Which of the following is NOT logically equivalent to the rest: 1. wx~y + w~z + wxyz + w~yz 2. w (x + ~y + ~z) 3. w + x + ~y + ^Z 4. wx + w~y + w~z 3. Use K-Maps to simplify each of the following: 1. ~x~y~z + ~xyz + ~xy~z 2. ~x~y~z + ~xy~z + x~y~z + xy~z 3. ~y~z + ~yz + xy~Z
Q: Draw the Resource Graph and determine if there is a deadlock. • PA holds R and requests to S PB…
A: A resource allocation graph is a graph which has two kinds of nodes. A node each for all processes.…
Q: Make a complete list of parameters and performance metrics metrics to compare and explain in short…
A: Exceeds standards and creates exceptional experiences for customers for customers and meet minimum…
Q: P7. Consider the network fragment shown below. x has only two attached neighbors, w and y. w has a…
A: a) From the given diagram it is clear that: Minimum cost path from node w to node u=5. Minimum cost…
Q: 3. (10) Convert the following EBNF into BNF: A := CB [x] B ::= C (xly|z) D C:= y {y D} z D:= x | y|…
A: The Answer is in given below steps
Q: Let the relation R, over the set of 8-bit unsigned integers (0 to 255), be defined as R = {(a,b)|a ^…
A: Operations Results 0^0 0 1^0 1 0^1…
Q: A buddy system allocates memory from a fixed-size segment consisting of physically contiguous pages…
A: Defined the memory request/release using the buddy system and international fragmentation
Q: 5.01-3. Dijkstra's Algorithm (1, part 3). Consider the network shown below, and Dijkstra's…
A:
Q: Consider the below EIGRP topology and answer the following questions accordingly. R1 10.1.2.x BW…
A: Answer is: Min bandwidth is in kbps. See below steps
Q: Q3//An ISP is granted a block of addresses starting with 190.100.0.0/16 (65,536 addresses). The ISP…
A: ISP is granted a block of addresses starting with 190.100.0.0/16 (65,536 addresses). The ISP needs…
Q: Question#2: Suppose an ISP in Cincinnati is granted a block of address starting with 155.155.0.0/19.…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: An ISP is granted a block of addresses starting with 160.40.0.0/16. The ISP wants to distribute…
A: In a pair of locations, what was the node: That block's access point is the starting point. Any…
Q: Based on the following graph, describe the four-way handshake in IEEE 802.1X. 802.11 AP MAC…
A: The 4-way handshake is the process of exchanging 4 messages between an access point (authenticator)…
Q: Create Kmap and then simplify the functions: F(x, y, z) = x′y′z′ + x′yz + x′yz′
A: Kmap was introduced by Maurice Karnaugh in 1953. Kamp is a method that is used to solve boolean…
Q: Q) An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute…
A: Q) An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute…
Q: What is an IP address exactly? Is it true that mnemonic addresses are that easy to remember? How…
A: An IP address is an interesting location that distinguishes a gadget on the web or a local network .…
Q: ind the class of find the class of 1011 1110. 0110 0100. 0110 0011. 0010 1000-2 191.100.100.40 C…
A: let us see the answer:- " since you have asked multiple question i am solving first 2 for you if you…
Q: What is the encoding of the data sample [1.4,2]^T that is obtained using the spanning vector…
A: Lets see the solution.
Q: BR main ;******* main () vector: .EQUATE 2 .EQUATE O 10,i 0,i j,s 4,i ;local variable #2d4a ;local…
A: True statements: the code allocates space for a local variable and a local array the code utilizes…
Q: Suppose you have an input volume of dimension nH x nW x nC. Which of the following statement(s) is…
A: Input value of dimension nH*nW* nC is option B i.e. You can use a pooling layer to reduce nH, nW but…
Q: P7. Consider the network fragment shown below. x has only two attached neighbors, w and y. w has a…
A:
Q: An ISP is granted a block of addresses starting with 160.40.0.0/16. The ISP wants to distribute…
A: Gievn: An ISP is granted a block of addresses starting with 160.40.0.0/16. The ISP wants to…
Q: WSNs are a type of communication network. WSNs use sensor nodes to transmit data between each other…
A: EXPLANATION AND ANSWER: If we talk about wireless sensor networks, small devices called sensor nodes…
Q: def mystery (1st): for idx in range(1, len(1st)); tmp = 1st[idx) idx2 = idx while 1dx2 > 9 and…
A: def mystery(lst): # this is selection sort for idx in range(1,len(lst)): tmp = lst[idx] # select…
Q: Suppose you are at home and type cust.edu.pk in your web browser. Explain step by step (with the…
A: First, we will see briefly what is DNS and how it works? DNS stands for Domain Name System. It is…
Q: Q3//An ISP is granted a block of addresses starting with 190.100.0.0/16 (65,536 addresses). The ISP…
A: Find the answers attached.
Q: An ISP is granted a block of addresses starting with 10.100.10.0/16. The ISP needs to distribute…
A: For First Group: Given that each customer needed 128 addresses, So the suffix length is 27=128 i.e…
Q: 7.) The following table of radio stations vs. nearby stations close enough to interfere with their…
A: Solution :: Given data is ::
Q: Example: P₁ Request (1,0,2) • First, we Check that Request≤ Available (that is, (1,0,2) ≤ (3,3,2) ⇒…
A:
Q: Consider this data: "0 - 1" "1 - 1" "1 - 1" "1 - 0" "0 - 0" "1 - 0" "1 - 1" "1 - 1" "1 - 0" "0 - 1"…
A: We need to form 4 columns out of X: A,B,C,D in R language.
Q: Consider the following system specification: R= {R1, R2, R3, R4} P= {P1, P2, P3, P4} E= {R1-->P1,…
A: Provided the solution for Resource allocation graph and whether system is in a deadlock state or not…
Q: Q4 (a) The network in Figure Q4(a) represents a communication network and the values next to its…
A: Given graph contains 6 vertices A, B, C, D, E, R. It contains weighted edges between the vertices.…
Q: 8, 5, 1, 2, 5, 3, 5, 6, 2, 6 Assuming that all frames are initially empty, indicate the contents of…
A: In optimal page replacement algorithm, pages which will be not referred for longest time in future…
Q: 5.01-4 Dijkstra's Algorithm (1, part 4). Consider the network shown below, and Dijkstra's link-state…
A:
Q: WSNS are a type of communication network. WSNS use sensor nodes to transmit data between each other…
A: Introduction: The Wireless Sensor Network - (WSN) is a wireless network that does not require any…
Q: An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute…
A: a.) For 128 Addresses, we will use the /25 mask. (32 - 7 = 25) We need 128 addresses for 60 Medium…
Q: each I from 1 to k: track down such j (1≤j≤k, j≠i), for which (bi⊕bj) is the littlest among all such…
A: Here have to determine about the Xor Tree programming problem statement.
Q: Consider the block of three-address code…
A: Rules for finding leaders: The first three-address instruction of the intermediate code is a…
Q: An ISP is granted a block of addresses starting with 150.80.0.0/16. The ISP wants to distribute…
A: A) There are 200 medium-sized businesses in the group. Because 25 is the following number in such a…
Q: Question 3 Design the network defined by a) N = {A,B,C,D,E) A = {(A,B), (A,D), (B,D), (A,E), (B,E),…
A:
Q: Consider the following histories. Draw their serialization graphs and identify wh one of them is…
A:
Q: An ISP (Internet Service Provider) is granted a block of addresses starting with 190.100.0.0/ 22.…
A: Address: 190.100.0.0 10111110.01100100.000000 00.00000000Netmask: 255.255.252.0 = 22…
Q: 3. Consider the M/M/1 queue discussed in class. Assume that packets arrive to a queue with average…
A: As per guidlines we are allowed to answer only first question.For more answer please post them…
Q: 5.01-2. Dijkstra's Algorithm (1, part 2). Consider the network shown below, and Dijkstra's…
A: Below is the detailed and simplified answer to the above listed problem statement:
Q: Create Kmap and then simplify the functions: F(x, y, z) = y′z′ + y′z + xyz′
A: The Karnaugh map is a technique for improving Boolean variable based math articulations. It lessens…
Q: Consider the following three-node topology, with link costs c(x,y)=2, c(y,z)=3, c(z,x)=6. Compute…
A:
Q: 5. For the following problem, draw a network Activity A B C DE F G H I J Immediate B. A,B A,B B.…
A: ACTIVITY NETWORK DIAGRAM: Activity network diagram is basically the tool that is used for the…
Q: Consider the following schedules: (i) S1: r1 (X), r2 (Z), r2 (Z), r3 (X), r3 (Y), w1 (X), w2 (Y), r2…
A:
Q: ) A paging scheme with THREE (3) frames initially empty are considered. Trace the allocation of…
A: The given problem is related to CPU scheduling where the page references are given and the…
Q: Generalized forwarding: specifying a flow table entry (b). Consider the three-node network below,…
A: It is defined as a group of computers linked to each other that enables the computer to communicate…
Q: 5.01-1. Dijkstra's Algorithm (1, part 1). Consider the network shown below, and Dijkstra's…
A: Given network is
1, 2, 3
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 4 images

- 5.01-1. Dijkstra's Algorithm (1, part 1). Consider the network shown below, and Dijkstra’s link-state algorithm to find the least cost path from source node U to all other destinations. Using the algorithm statement and its visual representation used in the textbook, complete the first row in the table below showing the link state algorithm’s execution by matching the table entries (a), (b), (c), and (d) with their values.5.01-2. Dijkstra's Algorithm (1, part 2). Consider the network shown below, and Dijkstra’s link-state algorithm to find the least cost path from source node U to all other destinations. Using the algorithm statement and its visual representation used in the textbook, complete the second row in the table below showing the link state algorithm’s execution by matching the table entries (a), (b), (c), (d) and (e) with their values.Create Kmap and then simplify the functions: F(x, y, z) = x′y′z′ + x′yz′ + xy′z′ + xyz′
- Consider a computer with 128 MB of main memory, 64 KB of cache, and 4 bytes per memory block. Find out how to split the address (s-r, r, w) so that it can be used for direct mapping.Find out how to split the address into two parts (s and w) for associative mapping.Find out how to split the address into three parts (s-d, d, and w) for set associative mapping. Assume that each cache set has two lines.4. (a) Suppose the encoding matrix is1−3 − 3 − 40 1 14 3 43Use the encoding matrix above to encode the messageGOOD LUCKUsing 1 for the letter A, 2 for B,….26 for Z and 27 for space.(b) Decode the encoded message(-19, -61, 83, -34, -111, 136, -35, -101, 119,-29,-83,84)using the following decoding matrix10 1 15 − 3 − 1−3 2 13What does the message say?Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. Think about a diagram on k hubs, with numbers from b1 to bk composed on them. For each I from 1 to k: track down such j (1≤j≤k, j≠i), for which (bi⊕bj) is the littlest among all such j, where ⊕ indicates the activity of bitwise XOR (https://en.wikipedia.org/wiki/Bitwise_operation#XOR). Then, draw an undirected edge between vertices with numbers bi and bj in this chart. We say that the succession is acceptable if and provided that the subsequent diagram frames a tree (is associated and doesn't have any straightforward cycles). It is conceivable that for certain numbers bi and bj, you will attempt to add the edge between them twice. All things considered, you will add this edge just a single time. You can track down a model underneath (the image comparing to the main experiment). Succession (0,1,5,2,6) isn't great as we can't arrive at 1 from 5. Notwithstanding,…
- 5.14. SDN implementation of Dijkstra’s algorithm. Consider the implementation of Dijkstra’s algorithm in an SDN framework. Which of the following statements are true? (Hint: more than one statement is true.) Group of answer choices a. When executing, Dijkstra’s algorithm will need to send messages to all of the routers to gather their link costs. b. When executing, Dijkstra’s algorithm will use the link-state database that is maintained within the SDN controller. c. When executing, Dijkstra’s algorithm will execute within the operating system of the SDN controller d. When executing, Dijkstra’s algorithm will run as a network control application “on top” on the SDN controller. e. If a router’s forwarding table should be changed as a result of running Dijkstra’s algorithm, the new flow table for that router will be updated by the SDN controller via the southbound API using the Openflow protocol. f. If a router’s forwarding table should be changed as a result of running Dijkstra’s…Description please. Suppose the economies of the world use a set of currencies C1, . . . , Cn; think of these as dollars, pounds, Bitcoin, etc. Your bank allows you to trade each currency Ci for any other currency Cj, and finds some way to charge you for this service. Suppose that for each ordered pair of currencies (Ci, Cj ), the bank charges a flat fee of fij > 0 dollars to exchange Ci for Cj (regardless of the quantity of currency being exchanged). Describe an algorithm which, given a starting currency Cs, a target currency Ct, and a list of fees fij for all i, j ∈ {1, . . . , n}, computes the cheapest way (that is, incurring the least in fees) to exchange all of our currency in Cs into currency Ct. Also, justify the its runtime. [We are expecting a description of the algorithm, as well as a brief justification of its runtime.]Create Kmap and then simplify the functions: F(x, y, z) = y′z′ + y′z + xyz′
- 6.4-6. Self Learning Switches (c). Consider the network below with six nodes, star-connected into an Ethernet switch. Suppose that A sends a frame to A', A’ replies to A, then B sends a message to B’ and B’ replies to B, and then A sends to B and B replies to A. In this sequence of frame transmissions, how many frames have appeared at the interface at C'? Assume that the switch's table is initially empty. [Note: You can find more examples of problems similar to this here.]Mapping is a process in which data is transformed between main memory and cache memory. Consider a computer with main memory capable of storing 1024 K words, each word in memory is 64 bits. The computer has cache memory capable of storing 2048 words, each word is of size 64 bits. Discuss with suitable diagram how associative mapping method can be used to transform data between main memory and cache memory?Please refer to this textbook: “A. Silberschatz, P. B. Galvin and G. Gagne, “Operating System Principles,”7th Edition, John Wiley & Sons Inc., 2006.” And answer the following questions: Question7: A practical way to handle network partitioning is to: (a) Have each process start an election. (b) Elect a leader only if a majority of nodes can be reached. (c) Run a normal election and multicast the result to the subset of processes that can be reached. (d) Divide and conquer: elect multiple coordinators.

