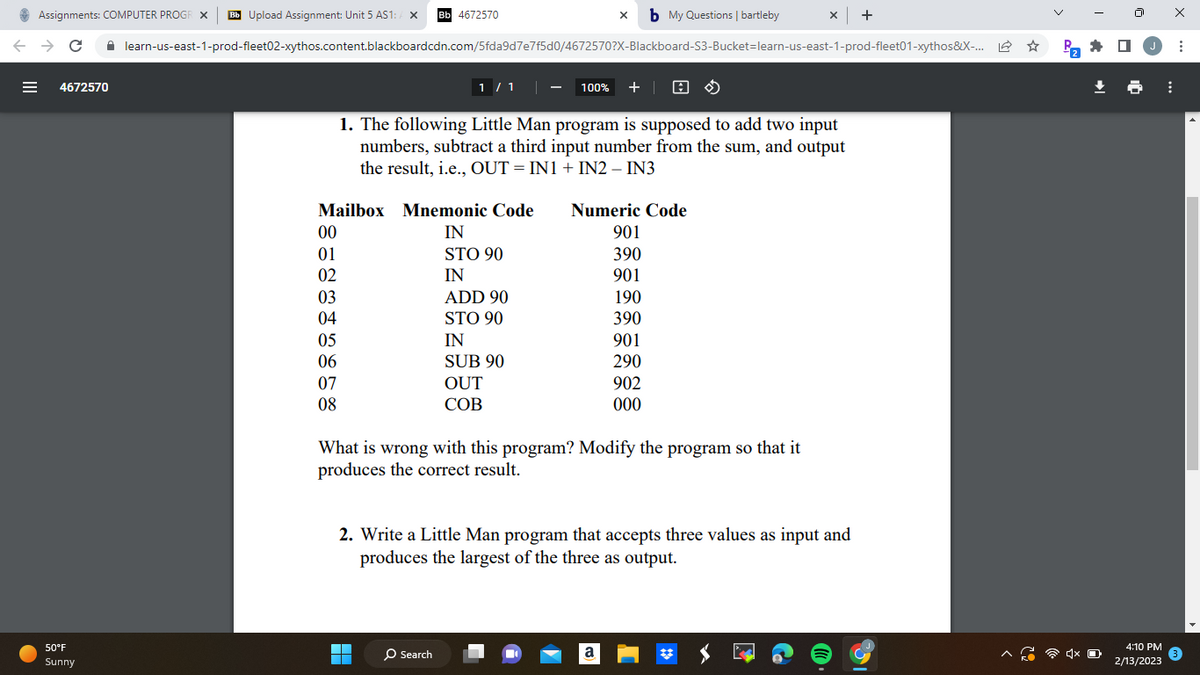
1. The following Little Man program is supposed to add two input numbers, subtract a third input number from the sum, and output the result, i.e., OUT = IN1 + IN2 - IN3 Mailbox Mnemonic Code IN STO 90 IN ADD 90 STO 90 00 01 02 03 04 05 06 07 08 IN SUB 90 OUT COB Numeric Code 901 390 901 190 390 901 290 902 000 What is wrong with this program? Modify the program so that it produces the correct result. 2. Write a Little Man program that accepts three values as input and produces the largest of the three as output.
1. The following Little Man program is supposed to add two input numbers, subtract a third input number from the sum, and output the result, i.e., OUT = IN1 + IN2 - IN3 Mailbox Mnemonic Code IN STO 90 IN ADD 90 STO 90 00 01 02 03 04 05 06 07 08 IN SUB 90 OUT COB Numeric Code 901 390 901 190 390 901 290 902 000 What is wrong with this program? Modify the program so that it produces the correct result. 2. Write a Little Man program that accepts three values as input and produces the largest of the three as output.
Chapter7: Working With The Bash Shell
Section: Chapter Questions
Problem 7DE
Related questions
Question
The following Little Man
numbers, subtract a third input number from the sum, and output
the result, i.e., OUT = IN1 + IN2 – IN3
Mailbox Mnemonic Code Numeric Code
00 IN 901
01 STO 90 390
02 IN 901
03 ADD 90 190
04 STO 90 390
05 IN 901
06 SUB 90 290
07 OUT 902
08 COB 000
What is wrong with this program? Modify the program so that it
produces the correct result.
2. Write a Little Man program that accepts three values as input and
produces the largest of the three as output.
Transcribed Image Text:Assignments: COMPUTER PROGR X Bb Upload Assignment: Unit 5 AS1: A X Bb 4672570
← → C ☐ learn-us-east-1-prod-fleet02-xythos.content.blackboardcdn.com/5fda9d7e7f5d0/4672570?X-Blackboard-S3-Bucket-learn-us-east-1-prod-fleet01-xythos&X-... L
4672570
50°F
Sunny
00
01
02
03
04
Mailbox Mnemonic Code
IN
STO 90
IN
05
06
07
08
1 / 1
100% + A
1. The following Little Man program is supposed to add two input
numbers, subtract a third input number from the sum, and output
the result, i.e., OUT = IN1 + IN2 - IN3
▬▬
ADD 90
STO 90
O Search
IN
SUB 90
OUT
COB
x b My Questions | bartleby
What is wrong with this program? Modify the program so that it
produces the correct result.
Numeric Code
901
390
901
190
390
901
290
902
000
2. Write a Little Man program that accepts three values as input and
produces the largest of the three as output.
x | +
a
P₂
4:10 PM
2/13/2023
⠀
X
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L