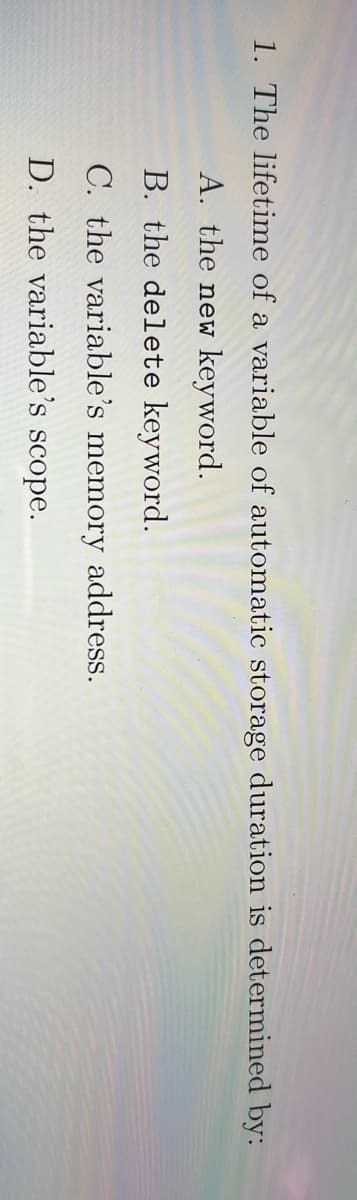
1. The lifetime of a variable of automatic storage duration is determined by: A. the new keyword. B. the delete keyword. C. the variable's memory address. D. the variable's scope.
Q: Can I please have the flow chart for this python code?
A:
Q: Write a script that produces the following report: For each instructor, display one line with Instru...
A: For each instructor, display one line with InstructorID, last name, first name, how many courses the...
Q: Computer Science Assume that you have a 3-class problem, and you have computed the cross-validated a...
A: The answer is given below.
Q: Using C Language, trace the following: (c) #include #include void kar1(char *c, char b, char *a) {...
A:
Q: Describe an algorithm using pseudocode that takes a list of n integers a1, a2, ..., an, and returns ...
A: The answer is given below:-
Q: Distance is a quantity that ____. always needs a reference point is always a vector has mag...
A: 4. has only magnitude.
Q: Consider the following hypothetical situation: An exception is thrown by a function. What are the th...
A: Introduction: An exception is an occurrence in a program that causes the normal flow of the program ...
Q: java programming Create a class called Citizen with the following attributes/variables: a. String c...
A: As per our guidelines we are suppose to answer first three sub question. Kindly repost other questio...
Q: Let, the time complexity of each of the following code snippets be T(n). Find out a tight bound for ...
A: Lets see the solution.
Q: The console output port to display characters The keyboard input port to read characters 1) Please p...
A: There are certain properties of ARC processor: It is designed with a LOAD/STORE architecture, which ...
Q: s the message box that was triggered instantly appear before or after the applicati
A: CreateWindow functionThis function creates a pop-up or child window that is overlapped. It provides ...
Q: Translate the following program to hex and binary, given that the first instruction is at address 0x...
A: 0040004C 0 ==> 8421 ==> 0000 0 ==> 8421 ==> 0000 4 ==> 8421 ==> ...
Q: What feature allows EIGRP to perform unequal-cost load balancing across multiple paths?
A: Answer: The feature allows EIGRP to perform unequal-cost load balancing across multiple paths are as...
Q: Code in go Language with output screenshot Write detailed code for Fibonacci sequence number print i...
A: Logic:- define a function for Fibonacci series display. Set p=0, q=1 and r=q display p, q use for ...
Q: Create a Java program in codiva.io to print the "smallest" and "largest" character in your name. For...
A: public class chegg { // function that return the largest alphabet. static char larg...
Q: You are given an instance of a problem where you have an n x n grid of squares. Each square can be u...
A: That rectangle's smallest quantity: They may do this with the ceil operation, who returns any small...
Q: 2. Simulate the Sort_Arr procedure using the given below and give the output. (Use a space to separa...
A: The given problem is related to C++ programming where the pseudocode is already given to sort those ...
Q: In Python write out the Python Code for the following in Jupiter Lab. Show code and outputs. Use a d...
A: arrow_forward Step 1 In questions with many asks, we must answer first. arrow_forward
Q: Methods Java Write the appropriate method headings using the provided method name for the following ...
A: The program is written in Java. Please find the source code and output in the following steps
Q: Create a shared memory segment of 16 bytes. This segment is shared by two process A & B. Process A i...
A: SUMMARY: - Hence, we discussed all the points.
Q: Wait() system call executed by a parent process has the following format: 'a = wait(&b);. What do th...
A: Wait(): The wait() system call is used to suspends execution of the current process until one of it...
Q: discuss how to creat a non-executable stack and disuss the stack's exploitable wesknesaes
A: Non-executable stack (NX) is a virtual memory insurance instrument to hinder shell code infusion fro...
Q: a=rea zatemaareiyat at Dremier Finenciel Serica yeu ere getting teen station You repert te Mary, the...
A: Please check the step 2 for solution
Q: (A) Write the pseudo code from the given dependency graph of concurrent processes player nconf healt...
A: A) Begin player: par begin resource; ...
Q: Because even though we may not understand them, algorithms can help us solve problems.
A: INTRODUCTION: Computations are carried out by following a set of rules, known as an algorithm. When...
Q: date man date file/ man -k password man-f passwd Man 5 passwd Info dațe Date -help Ls /usr/share/doc...
A: Here are the functions of above commands on Linux :- 1)date:- this command is used to display the sy...
Q: Write a code to decide if Gram-Schmidt Algorithm can be applied to columns of a given matrix A throu...
A: Gram-Schmidt Algorithm The Gram-Schmidt process (or method) is a collection of procedures that conv...
Q: To what is the main downside of using algorithms?
A: Given To know about the main downside of using algorithms
Q: Write a program that asks the user for the hexcode of a color and then displays a turtle that color....
A: According to the information given:- We have to write program to ask user hexcode of a color then di...
Q: Write a program to find the sum for the following series: اكتب برنامج لايجاد المتسلسله التاليه : (1*...
A: Program Explanation: 1) Implementing the header file. 2) Using the integers. 3) Using an if-else sta...
Q: As input, enter two non-negative number sequences in increasing order (the numbers entered are alway...
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------...
Q: A port is where there is only one receiver fixed to it. QUESTION 12 Vhen using buffer, the producer ...
A: Given :- (a.) A port is-------- where there is only one receiver fixed to it. (b.) When using-------...
Q: Compare between the Two Tier Client-Server DBMS Architecture and Three Tier Client-Server DBMS Archi...
A: Compared between the Two-Tier Client-Server DBMS Architecture and Three-Tier Client-Server DBMS Arch...
Q: Given the machine code, identify the instruction line or command line. Use CAPITAL LETTERS . No spac...
A: SUMMARY: - Hence, we discussed all the points
Q: Using VBA Code create a list of 5 expenses amounts and notes. Find the smallest expense. Instead of ...
A:
Q: Code in go Language with output screenshot Write detailed code for Fibonacci sequence number print i...
A: Go program to generate the fibonacci series
Q: 7- Simulation tests all the logic a. Gate speed b. Functions c. Tools 8- EDA test bench creation too...
A: Question 7: Logic simulation is a way of testing a system on a computer before it is turned into har...
Q: Determine the function for the number of steps taken by the algorithm. (FOR EACH FUNCTION) Which Big...
A: INTRODUCTION: The function that represents the number of steps that are going to be taken by the al...
Q: Write a MATLAB function that takes a number as an input argum= checks to see if the number is lucky....
A:
Q: = to classify an object from the test data set which falls in this leaf de (NODE t). Predict this ob...
A: Given 4. Suppose we have used a decision tree algorithm to build a classifi-cation tree model for de...
Q: Create a function that prints converts the light sensor into 3 (equal range) categories based on the...
A: creating a function to 3 equal range category The advantages of simulating real-time events have bee...
Q: In a three-tier design, the intermediate layer between the database and the client servers is referr...
A: n a three-tier design, the intermediate layer between the database and the client servers is referre...
Q: Because even though we may not understand them, algorithms can help us solve problems.
A: Introduction: A pattern for rules for doing calculations is an algorithm, which is short for an algo...
Q: What was my understanding of the Internet before?
A: answer is
Q: Brenda secured her bicycle with a number lock. The problem was she forgot the exact arrangement of t...
A: There will be total 24 combination for code number containing 1,3,4,7. The combination of all types ...
Q: Let's say that an employee's regular pay is rate times hours. If they work more than 40 hours, they ...
A: See the solution below-
Q: Giving the following schema for a supermarket database, specify the domain constrains for each attri...
A: Constraints are the conditions which are applied on table or table domains. Domain is field or colum...
Q: The objective of this assignment is to give you some practice using inheritance, virtual functions, ...
A: Below is the required program in C++. Screenshot of Output is also attached at the end of the progra...
Q: Construct a regular expression that represents the same language as the automaton below, using metho...
A: Hey there I have written the required solution for the above stated question. I am uploading the sn...
Q: What impact has technology had on human behaviour in terms of cyber security?
A: Introduction: Perhaps the most difficult aspect of cyber security is the reality that humans are at ...
Step by step
Solved in 3 steps

- What is the unit of memory measurement? Write at least four multiples of this unit.Select all true statements import java.io.File; import java.util.Scanner; public class DirectorySize { public static void main(String[] args) { // Prompt the user to enter a directory or a file System.out.print("Enter a directory or a file: "); Scanner input = new Scanner(System.in); String directory = input.nextLine(); // Display the size System.out.println(getSize(new File(directory)) + " bytes"); } public static long getSize(File file) { long size = 0; // Store the total size of all files if (file.isDirectory()) { File[] files = file.listFiles(); for (int i = 0; files != null && i < files.length; i++) { size += getSize(files[i]); // Recursive call } } else { // Base case size += file.length(); } return size; } } a. The length() method returns the size of a file. b. The listFiles() method returns an array of File objects and excludes each directory.…If you wanted your variables to be located only on even numbered bytes in memory, what directive would you use? Group of answer choices ALIGN 1 ALIGN 2 OFFSET 4 OFFSET 2
- Hi, I am trying to learn and execute a morse code in this way and by using this format, I already know another way and it works but it will be very helpful to understand this one as well, thanks. def print_intro(): def get_input(): def encode(message): def decode(message): def process_lines(filename, mode): def write_lines(lines): def check_file_exists(filename): def main():PLEASE ASK THE USER IF THEY WOULD LIKE TO WRITE INTO THE FILE IF THEY CHOOSE NOT TO DELETE THE FILE, AND WRITE IT INTO THE FILE Write a complete java program that: asks the user for a filename tests whether the file exists and tells the user if it does exist ask the user whether it should be deleted. Either delete or do not delete the file based on the user input. If they don't delete it, ask them if they would like to write to the file If they want to write, ask what they want to write to the file and write it. Make sure to provide plenty of console output dialog specifying what status/actions are taken at each step.B3- Write a Python program that reads the marks from a file named marks.txt and then increments each mark by 5 and saves the updated marks in a new file called updatedMarks.txt. You can assume that the marks are written on a separate line each in the marks.txt file. Finally, read the new marks from the new file and print them to the output screen.
- Complete the following sentences by filling the right word To check if two string variables string1 and string2 refer to the same memory address we use the command ………How come when I create a binary for a makefile ex. # create binaryprogram: <--- color turns blue to indicate it is a comment after ':' --- Can you show an example of a makefile --- for "program.c" Create binaryCreate object file for program.cCreate if needed object file for programx.c <--- and indicate why theres 2 object filesdelete all of the object files clean:Exercise 2:Write a Java program that allows the user to specify a file name on the command line and prints the number of characters, words, lines, average number of words per line, and average number of characters per word in that file. If the user does not specify any file name, then prompt the user for the name.
- Write program that reads a list of names from a data file and displays the names to the console. The program should prompt the user to enter a filename. Create such a file and check your code. Solve with python. Example of code format: #Prompt the user for file name file_name = input("Enter file name : ") #Open file with open(file_name,"r") as file: #Read file content f = file.readline() #split the contents into numbers numbers = f.split(' ') test_list = [int(i) for i in numbers] res = 1 #Find the product for i in test_list: res*=i #Print result print("Product of numbers in the list :",res)Write the negation of each statement.a. The processor is fast but the printer is slow.b. The processor is fast or else the printer is slow.c. If the processor is fast, then the printer is slow.d. Either the processor is fast and the printer is slow, or else the file is damaged.e. If the file is not damaged and the processor is fast, then the printer is slow.f. The printer is slow only if the file is damaged.True or False ___ 14. A file with .class file name extension is Java’s byte code. ___ 15. A Java method can call other methods. ___ 16. Java compiler converts source code into byte code. ___ 17. Java program can use any file name extension as you would like. ___ 18. Both symbols // and /* and */ are Java comments. ___ 19. In Java, the expression x=x+2; is valid.





