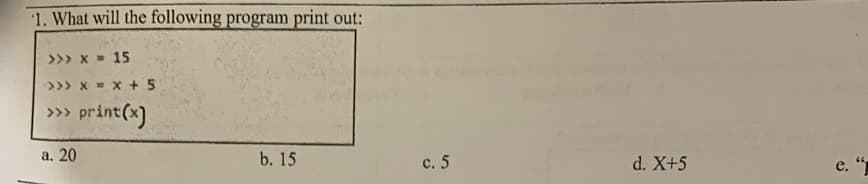
1. What will the following program print out: >>> x - 15 >>> x- x +5 print(*) >>> a. 20 b. 15 с. 5 d. X+5
Q: pared to alternative network security solutions, such as application layer security, what are the…
A: Introduction: Below are the benefits and drawbacks of adopting IPSec
Q: Change this MIPS code to RISC-V Assembly using store-load. Please add comments. Allow running in…
A: This is related to assembly language of RISC-V, code is working in RARS and giving correct result.…
Q: Q2: Insert the following data in the following tables: A. carrier CarrierID CarrierName Phone range…
A: INSERT is the keyword used to insert a row into a table and let's see the statements to insert…
Q: -Problem -2 When you execute your program it should ask user to input any number then check if the…
A: Note: Programming language is not mentioned, so writing code in C++ In this question, we are asked…
Q: Identify at least three of the most recent routing methods. Instead than describing the algorithm,…
A: Routing algorithms with the most popularity: Algorithm of Distance-Vectors.Algorithm of…
Q: The head of the IT group in a company often is called the chief information officer (CIO) or chief…
A: INTRODUCTION: A chief information officer (CIO) is the firm leader in charge of information and…
Q: Research TCP/IP and OSI and how they are related to network security. Network security is aided by…
A: Answer:TCP/IP is a network protocol suite. It creates networks like the internet. The OSI model…
Q: You have to create a program in C language in which the user enters the mass M and length L of a…
A: I give the code in C along with output and code screenshot
Q: ffects people and the tactics used to commit it Do you know what you can do to av
A: Introduction: Below the how you can do to avoid being a victim of cyber-crime?
Q: occurred
A: The most impacted protocol in the network system as a consequence of a cyber attack.
Q: Wireless networks include weaknesses that might create several troubles. What are three of these…
A: Wireless networks: Wi-Fi networks are crucial in today's corporate environment to ensure that…
Q: banks employ what kind of network technology?
A: Network Technology: WAN (Wide Area Network) optimization is critical to financial institution…
Q: 2. Find the ring! by CodeChum Admin Thanks to you, my crush was impressed with my awesome display()…
A: Find the required code given as below and output :
Q: An overview of how secure Internet transport is provided via connection-oriented operations should…
A: The protocols involved in the transport layer manage the end-to-end communication.
Q: Identity theft is a widespread kind of cybercrime. Tell us about the ways in which hackers might…
A: Introduction In today's digital environment, cybercrime is one of the most common crimes. Solution:…
Q: When it comes to transferability, how may the blockchain work?
A: Foundation: The blocks that make up a blockchain are collections of data that each include a set of…
Q: Assume you have three int variables: x = 2, y = 6, and z. Choose the value of z in the following…
A: x=2, y=6 The given is a ternary operator. (Condition)? Case1 : case2 If condition is evaluated to…
Q: What distinguishes a hacktivist from a cyberterrorist in your opinion? Is using hacktivists against…
A: Information security researcher Dorothy Denning defines hacktivism as "the marriage of hacking and…
Q: Any explanation of the DNS should contain iterated and non-iterated requests, root servers,…
A: Introduction: The Domain Name System (DNS) is known as "the phonebook" on the Internet. Domain names…
Q: What is the purpose of ICMP, and how does it work? Is it possible to explain how ICMP traceroute…
A: The acronym ICMP stands for Internet Control Message Protocol. ICMP provides an error control that…
Q: What does RDP stand for? What am I supposed to do with it?
A: RDP software provides access to a desktop or application hosted on a remote host.
Q: Scripting vs. programming languages: what's the difference?
A: Scripting languages convert high-level instructions into machine language.
Q: Big data has two key properties: speed and variety. What do each of these traits look like in…
A: Big data: Massive, difficult-to-manage data quantities – both organized and unstructured – inundate…
Q: owing is NOT a
A: Solution - In the given question, we have to select which operator is not a logical opeator in c++…
Q: IP spoofing is a term for what? Is it possible that IP spoofing is a security flaw?
A: Introduction Spoofing is a kind of cyber-attack in which hackers gain access to computers in order…
Q: 37. Find the CY flag value after cach of the following codes. (a) MOV A, 54H (b) MOV A, #00 (c) MOV…
A: the answers is an given below :
Q: Apex Assignment: Create a apex class called addition and then create a method to add the 2 integer…
A: Apex is a program language which is used to create the salesforce Backend and mostly Salesforce…
Q: So, what exactly is data mining? What are some data mining jobs you can think of?
A: Given: The work of a data mining expert is analysing information in order to discover links, trends,…
Q: QUESTION 5 Suppose you connect your laptop into a university network (either via wired ethernet or…
A: as per the company policy, if multiple questions posted in single picture, then only first 3…
Q: Analyze the King III framework as it relates to IT governance in a typical company. Examine how…
A: King III highlights the role of IT governance and the board's related responsibilities.
Q: What are the many sorts of data structures that are available?
A: Data structures are easy ways of storing and organising data in a computer system so that actions on…
Q: -Problem -2 When you execute your program it should ask user to input any number then check if the…
A: Note: Programming language is not mentioned, so writing code in C++ In this question, we are asked…
Q: What are the benefits and drawbacks of IPSec over alternative network security solutions like…
A: Start: IPsec is a collection of linked protocols used to secure communications at the network or…
Q: Explain how dependability and availability connect in a computer network. Why a network HUB is no…
A: In a computer network, Availability refers to the overall uptime of the computer network or its…
Q: Determine the present network's advantages and drawbacks.
A: (1) Availability: You are rarely out of contact since wireless technology allows you to communicate…
Q: In order to get a digital certificate for a single public key, how do you keep the private key…
A: The fact that RSA is a trapdoor permutation means that you are not required to reveal the private…
Q: MIPS programming write a program in MIPS that will print "Hellow World in reverse order utilizing…
A: An million instructions per second is simply called as MIPS.An MIPS which approximate measure of a…
Q: st out the benefits of biomet uthentication?
A: Introduction Below the benefits of bio-metric authentication
Q: Write a nested loop to extract each digit of n in reverse order and print digit X's per line.
A: Since programming language not mentioned using C++
Q: You've decided to use WPA2 as your wireless security protocol. Give reasons as to why this choice is…
A: WiFi- Protected Access 2 (WPA2): WiFi- Protected Access 2 (WPA2) is an abbreviation for WiFi-…
Q: Because there are so many distinct operatin
A: A partition is an logical division of a hard circle that is treated as a different unit by operating…
Q: Is it possible to explain low-level programming languages?
A: Low level programming language is close to computer hardware which directly interacts with hardware…
Q: Describe the many methods used by law enforcement authorities to investigate computer crimes and…
A: Law Enforcement: Computer technology enables law enforcement agencies to store and access large…
Q: Cross-site scripting (CSS) attacks are referred to as "reflected cross-site scripting attacks."
A: This type of attack, known as cross-site scripting (XSS), occurs when hackers execute malicious…
Q: This is a leftist max-heap. Show 2 get max calls where the maximum is removed
A: Introduction: Max heap tree is the tree which contains the maximum element at the root node Answer…
Q: Q5: Design a PDA for accepting a language (0'1"0" | m, n-1} give the ID form as we explain in the…
A: PDA: PDA stands for Push Down Automata. Push down automata read input string from left to right.…
Q: Sketch Norman’s Cycle of Action, and define each step. Explain both gulf of evaluation and gulf of…
A: Norman's Cycle of Action
Q: If you're a network security administrator, you should think about identifying and defending your…
A: The primary duty of a network and security administrator is to aid in the protection of a company's…
Q: What will happen to a corporation if it suffers a cyber security breach?
A: Foundation: When sensitive information stored at an advanced stage is accessed by unapproved means,…
Q: Theft of one's identity is a regular and growing kind of cybercrime. How may identity fraudsters…
A: Answer: Whether an identity cheat hears you perusing out your credit card number on the telephone,…
Step by step
Solved in 2 steps

- Q1. Write a program to take input for a number, if the number is palindrome, then display its half on the screen, otherwise take input for 2 more numbers, and display their product on the screen. Use minimum two functions including main functionDriving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('%0.2f' % your_value) Ex: If the input is: 20.0 3.1599 the output is: 1.58 7.90 63.20 Your program must define and call the following driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) Your program should call the function three times to determine the gas cost for 10 miles, 50 miles, and 400 miles. Note: This is a lab from a previous chapter that now requires the use of a function.Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('{:.2f}'.format(your_value)) Ex: If the input is: 20.0 3.1599 the output is: 1.58 7.90 63.20 Your program must define and call the following driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) Your program should call the function three times to determine the gas cost for 10 miles, 50 miles, and 400 miles. Note: This is a lab from a previous chapter that now requires the use of a function. def driving_cost(driven_miles, miles_per_gallon,…
- Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('{:.2f}'.format(your_value)) Ex: If the input is: 20.0 3.1599 the output is: 1.58 7.90 63.20 Your program must define and call the following driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) Your program should call the function three times to determine the gas cost for 10 miles, 50 miles, and 400 miles. python # Define your function here. if __name__ == '__main__': # Type your code here.Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('{:.2f}'.format(your_value)) Ex: If the input is: 20.0 3.1599 the output is: 1.58 7.90 63.20 Your program must define and call the following driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) Your program should call the function three times to determine the gas cost for 10 miles, 50 miles, and 400 miles. python use this in answer please # Define your function here. if __name__ == '__main__': # Type your code here.Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both floats) as input, and output the gas cost for 10 miles, 50 miles, and 400 miles. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('{:.2f}'.format(your_value)) Ex: If the input is: 20.0 3.1599 the output is: 1.58 7.90 63.20 Your program must define and call the following driving_cost() function. Given input parameters driven_miles, miles_per_gallon, and dollars_per_gallon, the function returns the dollar cost to drive those miles. Ex: If the function is called with: 50 20.0 3.1599 the function returns: 7.89975 def driving_cost(driven_miles, miles_per_gallon, dollars_per_gallon) # Define your function here. if __name__ == '__main__': # Type your code here.
- 1. Federal law requires that hourly employees be paid “time-and-a-half” for work in excess of 40 hours in a week.For example, if a person’s hourly wage is $12 and he or she works 60 hours in a week, the person’s gross pay shouldbe (40 *12) + (1.5 *12 * (60-40)) = $840.Write a program that requests the floating number of hours a person works in a given week and the person’s hourlywage as input, and then displays the person’s gross pay. Save it as overtimePay.pyProblem 2 Write a program that lets the user enter an integer number and display its equivalent value in text form. The range of input values should be from -99999 to 99999. Example 1 Enter integer in range [-99999, 99999] -> 100 Expected Output Text equivalence: one hundred Example 2 Enter integer in range [-99999, 99999] -> 5 Expected Output Text equivalence: five Example 3 Enter integer in range [-99999, 99999] -> 1812 Expected Output Text equivalence: one thousand eight hundred twelve Example 4 Enter integer in range [-99999, 99999] -> 44040 Expected Output Text equivalence: forty-four thousand forty Example 5 Enter integer in range [-99999, 99999] -> -10 Expected Output Text equivalence: negative ten In [40]:Modify the craps program to allow wagering inside of C#. Initialize variable Balance to 1000 dollars. Prompt the player to enter a wager. Check whether the wager is less than or equal to Balance and, if not, have the user reenter the wager until a valid wager is entered. After a valid wager is entered, run one game of craps. If the player wins, increase Balance by wager, and print the new Balance. If the player loses, decrease Balance by wager, print the new Balance, check whether Balance has become zero and, if so, print the message “Sorry. You busted!” (explain steps as much as possible so I can understand plz).The program to modify has the code listed below:// Craps class simulates the dice game craps.using System; class Craps{// create random-number generator for use in method RollDiceprivate static Random randomNumbers = new Random(); // enumeration with constants that represent the game statusprivate enum Status {Continue, Won, Lost} // enumeration with constants that represent…
- 3)Write a program which prompts the user for their age. If they are 19 or younger inform them that qualify for student discounts. If they are between 20 and 65 inform them that they qualify for no age discounts. If they are 65 or over inform them that they can receive senior discounts. (solution will be Pyhton code,thank you)4)Write a program from decimal to any base, ask the user for a decimal number and convert entered base by user. (Your program should support bases between 2 and 16 .) (solution will be Pyhton code,thank you)Display the first N magic numbers, where N is a positive number that the user provides as input. Here, a magic number is a number whose sum of its digits eventually leads to 1. For example, 1234 is a magic number because 1 + 2 + 3 + 4 = 10 and 1 + 0 = 1, while 1235 is not (1 + 2 + 3 + 5 = 11 and 1 + 1 = 2). Write a program that prints out the first N magic numbers, seven on each line. You are required to use the following function prototype: bool isMagic(int value); // Returns true if value is a magic number The outline of this function will be as follows: Step 1: Calculate the sum of digits of the value Step 2: Repeat Step 1 until we get a single-digit Step 3: If the resulting sum is equal to 1 then it is a magic number, otherwise not Here is the sample output:C++ Programming Exercise: A real estate office handles, say, 50 apartment units. When the rent is, say, $600 per month, all the units are occupied. However, for each, say, $40 increase in rent, one unit becomes vacant. Moreover, each occupied unit requires an average of $27 per month for maintenance. How many units should be rented to maximize the profit? Write a program that prompts the user to enter: a. The total number of of units. b. The rent to occupy all the units. c. The increase in rent that results in a vacant unit. d. Amount to maintain a rented unit. The program then outputs the number of units to be rented to maximize the profit.

