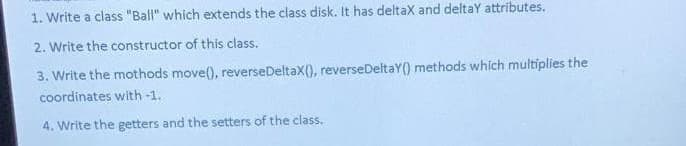
1. Write a class "Ball" which extends the class disk. It has deltax and deltay attributes. 2. Write the constructor of this class. 3. Write the mothods move(), reverse DeltaX(), reverseDeltaY() methods which multiplies the coordinates with -1. 4. Write the getters and the setters of the class.
Q: Describe not just the positive aspects but also the negative aspects that are associated with the…
A:
Q: How challenging was it to construct a network that would be applicable throughout the whole of the…
A: Introduction A network that traverses the association might connect PCs arranged in different…
Q: Describe what is meant by the term "multiprocessing," which is another name for the notion of…
A: "Multiprocessing: As a broad word, "multiprocessing" may refer either the dynamic assignment of a…
Q: Is the issue with the computer's hardware or its software when you power on the computer for the…
A: Introduction: When a computer is powered on, the Basic Input/ Output System (BIOS) initiates the…
Q: Demonstrate how the ownership of a trademark might come into direct conflict with the right to…
A: Introduction: A trademark is a distinguishing sign, design, or phrase that identifies a product or…
Q: Express the solution in big-O terms for the following recurrence relation: T(n) = 9*T(n/3) + n^3;…
A: After that, let's start working through the recurrence relation step by step:
Q: What precisely is the purpose of a firewall system, particularly one that is regarded as being of…
A: Specify the objective of the firewall system. NOTE: Because you have posed many inquiries, we will…
Q: First, in a few sentences, describe what a technique is, and then go on to discussing the method's…
A: Method You want things to have a function once you've created them. Methods can help with this. In…
Q: A name fined in file/namespace scope. It can be referenced by name only thin the same translation…
A: In computing the namespace which refers to the set of signs that are usually used to identify and in…
Q: Both read-only memory (ROM) and random access memory (RAM) are included in a personal computer's…
A: INTRODUCTION Computer memory is of two fundamental sorts - Primary memory(RAM and ROM) and…
Q: Convert the following notation to CNF -((-M-N)^(-N-O))
A:
Q: Describe the several ways in which a business may stand to benefit from the installation of physical…
A: A physical firewall is also known as a hardware firewall. A hardware firewall is a network security…
Q: We respectfully request that you limit your comments to no more than three or four at the absolute…
A: Introduction: Human rights are necessary to defend and uphold each person's inherent value as a…
Q: Why is it so important for people to have a working knowledge of spreadsheets in the current…
A: A spreadsheet program allows storing the data in the tabular format i.e. in rows and column…
Q: ds Used to Avoiding Deadlock and the Meth
A: Introduction: Below describe the Methods Used to Avoiding Deadlock and the Methods Used to Prevent…
Q: You have to create a program in C language in which the user enters the mass m and radius of a…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: Write python program that reads from the user an integer number in the range [1,6] and raise a user…
A: Here is the python code. The code is working fine. See below steps.
Q: What additional options are there for authenticating messages than just sending them?
A: The correct answer for the above question is given in the below steps
Q: Project 6: You have to create a program in C language in which the user enters the mass mand radius…
A: Algorithm: 1. Read mass, m. 2. Read radius, r. 3. moment_of_inertia = (m * r * r) / 2. 4. Print…
Q: When designing an open hash table that has acceptable functionality, the following should be taken…
A: Tableau hash When data is hashed, a hash table represents it as an array where each item carries a…
Q: the most effective linkedlist has? Which one takes the longest time to complete?
A: A linked list is a special data structure where each component (called a node) has two elements: the…
Q: What is an access control technology that protects copyrighted digital content? DEMI DRM CEA DEBIF…
A: What is an access control technology that protects copyrighted digital content The correct option…
Q: What happens to employees not following the security policy? An employee found to have violated this…
A: Introduction to security policy An organization's security policy is a written document that…
Q: In the context of wifi, what precisely does it imply when someone refers to something as a "Access…
A: "Access Point" as it relates to Wi-Fi Simply put, an access point is a location that offers wireless…
Q: Please describe what a cassette drive is and how it differs from a regular tape recorder that is…
A: Introduction: (2) Definition of recorded data. — For the purposes of clause (1), "recorded…
Q: 1. Reduce the following SAT instance to a 3SAT instance. -((a^b^c^d) V-(av (b^c)))
A: Given: Reduce the following SAT instance to a 3SAT instance. ¬((a∧b∧c∧d) ∨¬(a∨(b∧c)))
Q: When someone discusses their WiFi connection, they may refer to themselves as having a "Access…
A: A device that connects users to the internet is known as a wireless "access point." All of the…
Q: Have you ever seen someone being harassed or bullied by someone else over the internet? When you…
A: Have you ever seen someone being harassed or bullied by someone else over the internet? When you…
Q: In comparison to a traditional phone network, what do you believe to be some of the most important…
A: Encryption: The internet is mostly responsible for our daily activities, communication, and…
Q: The relative speeds of the many different storage devices that may be found on a computer system…
A: the solid state drives Solid state drives, or SSDs, are among of the quickest drives available right…
Q: Using the Hamming code algorithm (7, 4), convert a data message (0101) using 7bit. Inject an error…
A:
Q: Create a MATLAB program to read input the length of the side of a cube(in cm) and then it displays…
A: In this question we have to write a MATLAB program in which read input as side of cube in cm and…
Q: It is important to differentiate between a cache that is completely associative and one that is…
A: Definition: In a full associative cache mapping, every block in main memory can be assigned to any…
Q: Figure 3 shows a LAN topology. Assume that no port security implemented on both switches. The…
A: Below I have provided the answer to the given LAN Topology.
Q: When a user calls the help desk and says, "My computer won't boot," a knowledgeable help desk…
A: Definition: Immediately after restarting your computer, continuously press the f11 key. Select…
Q: e law is it permissible to make use of a particular piece of work
A: Introduction: Many images you find in print or online are copyright-protected. There are educational…
Q: It is advised that passwords be hashed rather than encrypted when they are saved in a file for a…
A: It is advised that passwords be hashed rather than encrypted when they are saved in a file for a…
Q: a) Refer to the number list below, explain how selection sort algorithm re-arrange all values in the…
A: Below I have provided the answer to the given values in the number lists.
Q: Write a program that prompts the user to enter a password and validates the password. • The program…
A: Below I have provided Java Programming. Also, I have attached the screenshot of the code and output…
Q: Could you perhaps elaborate on what you mean by the term "principle of non-repudiation"? Thank you…
A: Non-Repudiation Principle: A statement's non-repudiation ensures that you won't be able to challenge…
Q: You have to create a program in C language in which the user enters the mass mand radius R of a…
A: Introduction: A physical quantity that quantifies a body's resistance to having its speed of…
Q: Look at the effects that wireless networks have on countries that are still in the development…
A: Because they don't have many other choices, creating a wireless network is frequently simpler in…
Q: What are the key advantages of reusing application system components as opposed to developing…
A: We will first familiarize ourselves with both ideas: 1. Application System Reuse - Assume you…
Q: If these three needs aren't met, there's no way a network can be successful and live up to the full…
A: Relationships: That are successful in networking display a genuine interest in their connections and…
Q: What use do device drivers serve if the BIOS already has the code that enables the operating system…
A: Traditional x86 BIOS difficulties: During system startup, the BIOS only includes code that enables…
Q: Application Programming Software may be purchased from the following vendors: We would appreciate it…
A: An application programming software performs a specific task directly to the convenience of the end…
Q: QUESTION 5 A differentiated services router distinguishes between packet flows by using the packets'…
A: Question 5 option B is correct Markings Explanation: Using the type of service (TOS) field in the…
Q: Is it feasible to differentiate between the phrases "Internet" and "World Wide Web" in any…
A: Internet is used to link several computer networks at once. Since the internet is a public network,…
Q: Analyze the Python codes given below and write the output result of the program after executed the…
A: Class in python A user-defined class serves as a base or prototype from which entities can be built.…
Q: What types of safety measures can you take to prevent unexpected surges in the power that your…
A: Any computer needs constant stream of power supply. The computer relies on such constant power…
Step by step
Solved in 2 steps with 2 images

- Consider this scenario, a mehtod in some class needs to access a data field in another class, here are two possible implementations: public class Process { /* * Check if student qualifies for financial help */ void check(Student student) { //.... } /* * Check if student qualifies for financial help */ void check(double studentGPA) { //.... }} In class Process, which check method you think is better, why? In other words, should we pass the object to the method or just the data member it needs? Disucuss the Pros and Cons of each approach (if any). Assume class Student has a mehod called getGPA( ).Implement a class Season that represents a season during a specified year. For purposes of thisproblem, assume that the seasons in each year are, in order, 'Winter', 'Spring', 'Summer', 'Autumn' .__init__, __repr__A Season object is created by calling the constructor and supplying two optional arguments:1. season, defaults to 'Winter'2. calendar year, an int , defaults to 2023For the __repr__ , see the usage below: The next and prev methods modify a Season object by changing it to the next season or previousseason in sequence, respectively. Note that the seasons can "roll over" or "roll back" and that this maychange the year by +/-1. 1. During each year, the seasons occur in this sequence: 'Winter', 'Spring', 'Summer', 'Autumn' 2. next - change to next season, if the current season is Autumn then year will increase by 1 3. prev - change to previous season, if Winter then year will decrease by 1 Implement the == operator ( __eq__ method) to compare two Season…This question concerns writing a Student class to model a student's name, composed of a first name, middle name and last name. The Student class should meet the following specification:Class StudentA Student object represents a student. A student has a first name, middle name and last name.Methodspublic void setNames(String first, String middle, String last)// Set the first, middle and last names of this Student object.public String getFullName()// Obtain the full name of this Student with the middle name converted to an initial only.2Thinking of the problem in terms of testing, there are three requirements that must be met:1. The setNames() method sets the names stored in the object i.e. the values of firstName, middleName, lastName.2. The getFullName() method obtains the name of the student with the middle name converted to an initial only.3. The getFullName() method does not change anything – i.e. it does not modify the values of firstName, middleName, lastNameHINT: To start your…
- Write a class Point with instance variables as: xCoordinate(int) and yCoordinate(int). Write public instance methods (getters & setters) for each instance variable. Now, write a class Circle with private instance variables as radius and Pi (value is 3.14). Write public setter, getter for radius, Area method for calculating Area, Draw method for radius. Formula for calculating area=pi*r^2 Formula for calculating radius= Math.sqrt (xCordinate^2+yCordinate^2) a. Extend a Circle class from Point class such as Class Circle extends Pointb. Write a Default constructor in Circle class that sets radius, xCoordinate & yCoordinate to some default value e.g. -1;c. Write a Parameterized constructor in Circle class which takes xCoordinate, yCoordinate and radius as a parameter.Now write a ColoredCirlce class with private instance variable as color (String) and public setter & getters. Extend the ColoredCircle from Circle and do the following operations.d. Write a default constructor…Answer the given question with a proper explanation and step-by-step solution. The base class Pet has protected fields petName, and petAge. The derived class Cat extends the Pet class and includes a private field for catBreed. Complete main() to: create a generic pet and print information using printInfo(). create a Cat pet, use printInfo() to print information, and add a statement to print the cat's breed using the getBreed() method.Write a class Point with instance variables as: xCoordinate(int) and yCoordinate(int). Write public instance methods (getters & setters) for each instance variable. Now, write a class Circle with private instance variables as radius and Pi (value is 3.14). Write public setter, getter for radius, Area method for calculating Area, Draw method for radius. Formula for calculating area=pi*r^2 Formula for calculating radius= sqrt (xCordinate^2+yCordinate^2) Extend a Circle class from Point class such as Class Circle extends Point Write a Default constructor in Circle class that sets radius, xCoordinate & yCoordinate to some default value e.g. -1; Write a Parameterized constructor in Circle class which takes xCoordinate, yCoordinate and radius as a parameter. E.g. Circle (int xCoordinate, int yCoordinate, double radius) { this.xCoordinate= xCoordinate; this.yCoordinate= yCoordinate;…
- Write in java an abstract class Student that includes the following hidden attributes: id(int), name(String), major(String) and grade(double), then create setter and getter for each of them. Write two classes that inherited from Student: ItStudent and ArtStudent. The grade for ItStudent is calculated as: grade = mid*0.30 + project*0.30 + final*40 and the grade for ArtStudent is calculated as: grade = mid*0.40 + report*0.10 + final*50. Crate main class that achieve the following:a. Create an array of some Student objects from both ItStudent and ArtStudent classes.b. Sort the Student objects by grade in descending order using functions.c. Save the sorted objects into file.Implement the following class and write a driver classImplement a new class Contact :public Person I provided person.h you don't have to touch person.h just need help on contact.h class public person and private person please help me
- Create a parent class Person with one attribute age and one method greet() that prints out "Hello, world!". By default, the age is 20. Then create a subclass CollegeStudent that inherits from Person and has its own attributes School_Name and Major. Then create an object (a college student, his name is Harry, age is 21, School_Name is "Felician University", and Major is "Computer Science"), then let Harry say"Hello World!".1/ Write a BankAccountTester class whose main method constructs a bank account, deposits $1,000, withdraws $500, withdraws another $400, and then prints the remaining balance. Also print the expected result 2/ Implement a class Employee. An employee has a name (a string) and a salary (a double). Provide a constructor with two arguments public Employee(String employeeName, double currentSalary) and methods public String getName() public double getSalary() public void raiseSalary(double byPercent) These methods return the name and salary, and raise the employee's salary by a certain percentage. Sample usage: Employee harry = new Employee("Hacker, Harry", 50000); harry.raiseSalary(10); // Harry gets a 10 percent raise Supply an EmployeeTester class that tests all methods. 3/Implement a class Car with the following properties. A car has a certain fuel efficiency (measured in miles/gallon or liters/km—pick one) and a certain amount of fuel in the gas tank. The efficiency is specified in…*using java* Create a class AnimalCreate a class Cat, and a class Dog, and a class Bearded Dragon which extend Animal. Add to your Animal class: Member: name Methods: Public Animal(String name) //constructor public void makesSound()with the implementation printing out a generic animal sound. Next, override (add) the makesSound()method to your Cat and Dog class, with the implementation specific to each animal (i.e, cat says purr..). Do not override the makesSound() for your Dragon (bearded dragons don’t make sounds!)Note, you’ll also need a constructor in each of your subclasses which calls super(name) to initialize the common ‘name’ member of Animal. --- Next (in your test harness) create a List of different Animals ( a couple cats, a dog, a dragon... ) and add these Animals to your list. Iterate through your list & call makeSound on each. ( you should observe the implementation of the makeSound() method called will be: cat -> from Cat class, dog-> from Dog class,…











