10, 153, 34, 90, that order at a reading from c numbered from head movemer
Q: Include all of the gadgets that make up an internet connection in your explanation?
A: Components and Uses of Internet Connection Modem for DSL Broadband/DSL Filter NAT Router with a…
Q: What is the "Hybrid Approach" in data warehousing?
A: The first several data marts are created at the same time. An company backfills a data warehouse…
Q: What are the key distinctions between these two phrases when it comes to the world of computers?
A: Computer Organization vs. Architecture: Computer organisation studies the behavior and structure of…
Q: The dining philosopher problem is a classic problem in deadlock management. The problem can be…
A: ANSWER IS GIVEN BELOW:
Q: What exactly does it mean when we talk about a "Access Point" in the context of a wireless network?…
A: Explanation: WAPs are a more practical, safe, and economical alternative to cables and connections…
Q: Wireless networks have a lower bandwidth capacity than conventional networks.
A: Bandwidth is the frequency spread within the certain frequency range while transmitting a signal.…
Q: How might the four organizational frameworks be used to a prospective project that includes the…
A: Model with four frames: The Four Frame Model is a conceptualization that splits every organization…
Q: Become familiar with the assembler, the compiler, and the interpreter, as well as the similarities…
A: Introduction: Compilers are used to translate code written in high-level programming languages into…
Q: What is source data automation (SDA), and name at least two (2) advantages of using this technology…
A: Source data automation:- The process of gathering data at their point of beginning in advanced…
Q: Only one form of memory may be improved, so which one would you choose and why? The three types of…
A: Memory refers to the psychological of the acquiring , storing, retaining and later retrieving the…
Q: (1) How many 2-permutations of the set (a, b, c, d, e} are there? List them all. (2) Compute these…
A:
Q: Write a function definition for a function name Accept a string as an input parameter. Return the…
A: We are asked , to write a function definition for a function named getLast () : Given that:- a)…
Q: Question 4: Ted wants to view two sections of this workbook simultaneously and be able to scroll…
A: answer for both mcq given below.
Q: In this piece, we'll take a deep dive into the distinctions between assemblers, compilers, and…
A: Given: One sort of software is known as a compiler, and its primary function is to translate code…
Q: Given the code: double value = 95.35; Write a single line of code to print the the decimal portion…
A: Introduction: In this question, we are asked to write a C++ program to print the decimal portion of…
Q: What exactly is meant by the term "user-defined data types"?
A: A data type that was derived from an existing data type is known as a user-defined data type (UDT).…
Q: Alice and Bob use the ElGamal scheme with a common prime q=131 and a primitive root a=6. Let Bob's…
A: Key generation Common prime q=131 primary root = 6 Bob's public key =3 Random integer chosen k= 4…
Q: What sets the Oracle database apart from other types of databases, namely relational databases?
A: Relational databases: Based on the relational paradigm that uses set theory, it stores data as a…
Q: Star topology is a computer network architecture in which the user connects each network node to a…
A: Answer:
Q: Generate all permutations of {3, 8, 2} using the Johnson-Trotter algorithm. Show the steps.
A: Initialize the first permutation with <1 <2 ... <nwhile there exists a mobile integer find…
Q: Please provide an example of one method that an engineer who is responsible for generating a system…
A: Given: Give an example of one way in which an engineer who is responsible for developing a system…
Q: Please describe how an engineer who is responsible for generating a system requirements…
A: Given: Describe how a system requirements engineer may keep track of the relationships between…
Q: Describe the Assembly Registers and elaborate on the significance of their use throughout the…
A: Register of the assembly: When working with assembly, the register is sent to the processor so it…
Q: Compare Binary Search with AVL Trees. Can we discuss business efficiency?
A: Start: A binary search tree is a kind of binary tree in which the tree's left child includes a value…
Q: Explain the word "network," as well as its pros and disadvantages.
A: network - A network consists of two or more computers that are linked in order to share resources…
Q: Create a Shell Script: Write a program which performs two functions: add…
A: Given We know about the programming language and subtraction and addition function.
Q: True or False: Separating the parking lot from the facilities building is a proactive security…
A: True
Q: When it comes to the construction of a system, what makes the position of systems analyst so…
A: System analyst: System analyst is responsible for specifying the transforms implied by both source…
Q: S.no Name 17 Hades 99 James 1001 Robert 500 John 400 Michael 11 David 45 William Job.id dept.man…
A: The question has been answered in step2
Q: What opportunities does data modeling offer up?
A: Data modelling is the method of creating a visual representation of an information system for…
Q: Differentiate operating systems that operate on separate computers from those that are integrated…
A: According to the information given;- We have to differentiate operating systems that operate on…
Q: Simplify the difference between the types of multiprocessing: What are the advantages and…
A: Multiprocessing: A multiprocessor computer hardware design known as symmetric multiprocessing (SMP)…
Q: Write a code to display the prime numbers between 1 and 1000.
A: Since no programming language is mentioned, I am using python Code: lower = 1upper = 1000…
Q: What exactly is computer science, and how is it distinct from other academic research…
A: What exactly is computer science, and how is it distinct from other academic research…
Q: Design a code converter that converts a decimal digit from1. (a) The 8, 4, − 2 , − 1 code to BCD…
A: According to the information given:- We have to follow the instruction and develop and simulate an…
Q: Explain the need of having a domain name system (DNS) with the Internet, then go on to define its…
A: The domain name system (DNS) is a naming database in which internet domain names are located and…
Q: Our understanding of operating system processes is limited. Nobody can talk to them.
A: A process may be considered an entity representing the system's basic unit of work. In other words,…
Q: Explain the workings of the internet and list all gadgets that are part of the internet connection?
A: Introduction: THE INTERNET'S OPERATION: According to Wikipedia, the internet is a computer network…
Q: State the following is true or false. If false, explain why."Empty parentheses following a function…
A: Solution: The syntax of functions is used in most programming languages such as C, C++, Java, and…
Q: When constructing a database, an organization has to give careful consideration to the following…
A: In reality, databases are used to store data. When developing a database, businesses must take a…
Q: Mobile devices and cloud computing are intertwined, but how? A lot of benefits for mobile devices…
A: Given: Examine the similarities and differences between mobile computing and cloud storage using…
Q: If adding a data object to a data model is not recommended, why is this the case?
A: A data model, also known as an abstract model, unifies informational components and standardizes…
Q: how to comprehend and define an integrated information system from an organisational and…
A: Given: What is an integrated information system, and how can you understand and describe it from an…
Q: When constructing a database, an organization has to give careful consideration to the following…
A: Constructing a Database: Organizations must take into account both a complicated method to secure…
Q: Cloud-based services and applications for networks
A: Introduction: In the cloud networking environment, some or all of an organization's network…
Q: Is there a significant difference between the architecture of a computer and the organisation of a…
A: Computer Architecture Computer Architecture is a diagram for the plan and execution of a PC…
Q: possible to distinguish between the architecture of a computer and the organisation of a computer?…
A: Introduction to computer architecture and organization: Computer Structure and Architecture is the…
Q: What is the "Hybrid Approach" in data warehousing?
A: ANSER IS GIVEN IN NEXT STEP:
Q: It is becoming more common to use symmetrical multiprocessing systems." Symmetric multiprocessing…
A: Symmetrical Multiprocessing Systems: Multiple processors working together to process data using…
Q: could you please explain and type the code for calculating the error size between random and non…
A: The estimated standard deviation of the sample distribution is what a statistic's standard error is.…
Step by step
Solved in 2 steps with 2 images

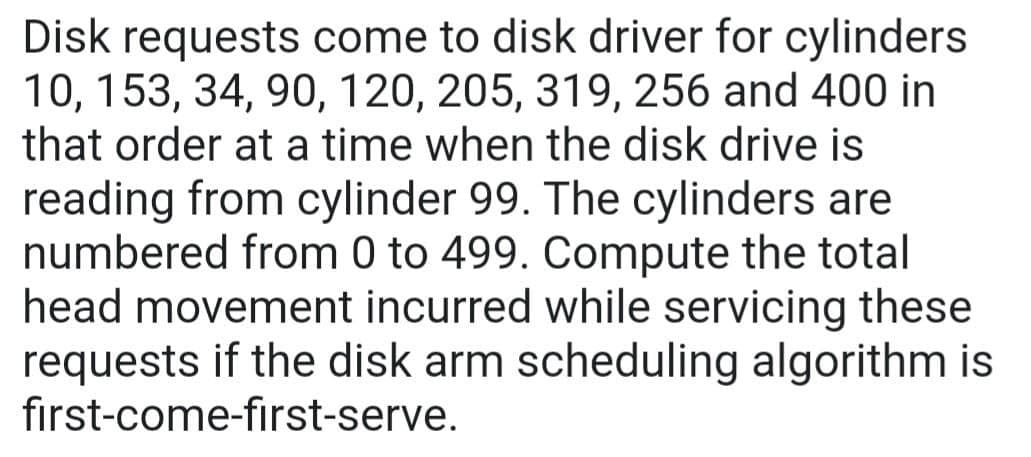
- Disk requests are received by a disk drive for cylinders 13 , 6 , 1 , 29 , 28 , 8 in that order and the head pointer starts at 9 . A seek takes 5 ms per cylinder moved. How much seek time is needed to serve these requests by using the First Come First Served (FCFS) disk scheduling algorithm? a. 315 b. 305 c. 325 d. 320 e. 310c) Suppose a disk has 300 cylinders, numbered from 0 to 299. The drive is currently serving an I/O request at cylinder 111 and the disk head was previously serving a request at cylinder 99, and there is a queue of disk access requests for cylinders as below: 181, 199, 150, 160, 85, 178, 109, 75 Starting from the current head position, calculate the total head movements using the following disk scheduling algorithms.(i) SSTF scheduling (ii) SCAN schedulingSuppose the head of a moving-head disk with 200 tracks numbered 0 to 199 is currently serving a request at track 99 and has just finished a request at track 125. The queue of outstanding requests in FIFO order is: 5, 95, 75, 100,30 and 155. What is the total number of head movements (in cylinders) for the following disk-scheduling algorithms? FCFS Scheduling SCAN Scheduling SSTF Scheduling
- Assume that you have a disk that has 191 tracks (numbered 0- 190) and the header current position is at track 49. A request queue has the following track numbers: 98, 193, 38, 107, 9, 168, 85, 79 Compute the total seek time using FCFS, SSTF, SCAN, CSCAN, LOOK, CLOOK and compare their performance.Find the total head movements for a request queue given below, using FCFS scheduling for a disk of 100 cylinders (0-99). It is assumed that read write head is initially present at cylinder number 50. Request queue for disk cylinders: 75, 25, 30, 68, 40, 89, 10Hi, please solve it correctly ,else i will downvote Consider the following disk request sequence for a disk with 100 tracks. 98, 183, 37, 122, 14, 124, 65, 67 Head pointer starting at 53 (current position of R/W heads) and moving in right direction. Find the number of head movements in cylinders using FCFS scheduling. Subject code - rcs509
- A file system with 300 GByte disk uses a file descriptor with 8 direct block addresses, I indirect block address and 1 doubly indirect block address. The size of each disk block is 128 Bytes and the size of each disk block address is 8 Bytes. The maximum possible file size in this file system will be ?Suppose the head of a moving-head disk with 200 tracks numbered 0 to 199 is currently serving a request at track 99 and has just finished a request at track 125. The queue of outstanding requests in FIFO order is: 5, 95, 75, 100,30 and 155. What is the total number of head movements (in cylinders) for the following disk-scheduling algorithms? a.FCFS Scheduling b.SCAN Scheduling c.SSTF SchedulingOn a 16 GB hard disk drive (HDD), each cluster consists of 32 sectors and each sector has a fixed size of 512 bytes. A text file with a size of 150,000 bytes is to be stored. a. i.What is the size of the slack space, in bytes, once the file has been stored?
- Suppose a disk has N cylinders, numbered from 0 to P. At some time, the disk arm is at cylinder X, and there is a queue of disk access requests for cylinders R1, R2, R3, R4. Explain which Disk scheduling algorithm should be the best to be used between the following a) FIFO b) CSCAN c) SSTF d) FSCAN e) CLOOK N: B • • Choose any acceptable numeric numbers for N, P, X, R1, R2, R3 and R4 • • Plagiarism Will be penalized heavilyOn a 16 GB hard disk drive (HDD), each cluster consists of 32 sectors and each sector has a fixed size of 512 bytes. A text file with a size of 150,000 bytes is to be stored. a. i.How many clusters does the text file take up in memory? ii.What is the size of the slack space, in bytes, once the file has been stored?In our discussion of the SSTF disk scheduling algorithm, we stated that the problem of starvation “is at its worst with low disk utilization rates.” Explain why this is so.

