10 4751-5 7 Graph 2
Q: The operating system is responsible for arranging the file blocks on the hard disk in a sequential…
A: Start: At the very bottom of the stack is where you will find all of the physical components, such…
Q: Before going into specific examples, provide a general overview of real-time operating systems.…
A: System performance in real-time: When a large number of events must be received and processed…
Q: The fundamental goal of businesses that make computers is to fulfill the requirements of customers…
A: Launch: It is vital to develop a system that is of a good quality and has adequate processing power…
Q: Describe the Information Security (InfoSec) programme with regard to the field of computer science
A: Please find the answer below :
Q: Watchdog timers are required in a wide variety of embedded systems; what are some of the reasons for…
A: Introduction: A watchdog timer (WDT) is a safety mechanism that restarts the system if it crashes…
Q: which of the following is the longest prefor match for IP address 211.112.156.937 Select one…
A: We need to find the longest prefix match.
Q: Il of the mentioned ostname-to-address records
A: Solution - In the given question, we have to select the correct answer among the given options.
Q: In the process of building software, which stage comes first: designing the software, developing the…
A: Launch: A method for systems engineering, information systems engineering, and software engineering…
Q: True or False? we set our threshold in committing a type II error by specifying alpha
A: Please find the answer below
Q: Define the risk from the perspective of the network/OS system? Also, what are some real-world…
A: A network operating system is a version of Windows designed specifically for network devices such as…
Q: Identify and briefly explain a few of global information systems problems.
A: Information systems that are global in scope have been implemented in some different nations.
Q: Take a look at these five moral considerations for computer systems.
A: The five moral aspects of information systems are as follows: 1. Informational rights and…
Q: Include information on the components of information technology—namely, the communications, the…
A: Start: Information Technology (IT) is the foundation of the computer, which allows it to store,…
Q: Why aren't the most essential ideas discussed in this topic applied to software engineering
A: Given: Any set of executable instructions is intended to perform a calculation of some sort.…
Q: Which of the following is not one of the eight principles that the Software Engineering Code of…
A: Given: Which of the eight principles adhered to by the Software Engineering Code of Ethics and…
Q: In this video, I'll explain why I feel that people and information systems are the primary forces…
A: Please find the answer below :
Q: How did everything come to this stage, and where and how did it all get started in the first place,…
A: Introduction: In fact, the Internet of Things (IoT) is a network of physical items that are linked…
Q: Q1) Write a C++ program to compute the value of S using function called Compute_S(x, n), where the…
A: Here I have created the function pwr(). In this function if the value of y is 0 then return 1,…
Q: Consider a given itemset (I1, I2, I4). The table below indicates whether its subsets are frequent (1…
A: Task : Given the itemset = {I1,I2,I4}. The task is to find if the itemset is frequent or not.
Q: has a wide rang requires in-depth
A: Cybercrime is a crime that includes a computer and a network. The PC might have been utilized in the…
Q: Refer to the incidence table below. Which of the following statements is/are TRUE? (1) The graph is…
A: Given incidence table contains, Set of vertices= {A, B, C, D, E} Set of edges={E1, E2, E3, E4, E5,…
Q: Computer Science You are requesting a webpage with three images stored in three different servers.…
A: It is a permanent connection, which means it does not need to be set up again and again. Connection…
Q: Using the terminology of computer science, please explain in as few words as possible any four of…
A: Introduction According to your question System engineering software (SoSE) is not a new discipline;…
Q: 1. Create a search method in your program that allows the user to find a tax payer and display their…
A: import java.util.Scanner; class Income { public static void main(String args[]) { double tax=0,it;…
Q: Describe the steps that a business may take to keep hackers out of its systems and what constitutes…
A: The effect on hacks like this reaches from simple humiliation through to critical monetary…
Q: 1. Is the following language A regular or non-regular? A = {1" 0m 1" | 0 ≤ m, n ≤ 3 and m=n+2} 2. If…
A: The above language A has following conditions. 0≤m,n≤3 and m=n+2 So one possibility is , n=0 and…
Q: Before going on to other things, it is essential to establish the function of the firewall with…
A: INTRODUCTION: It is crucial to comprehend these firewall functions for network security and…
Q: In what ways are SpecC and SystemC distinct from one another, and what are those differences?
A: Given: The first step is to figure out how Spec differs from System. There is a distinction between…
Q: It is important to identify and define each of the five primary task management strategies that are…
A: It is important to identify and define each of the five primary task management strategies that are…
Q: Which of the below items are the application areas of the database?
A: Answer;
Q: computer science Why is it so difficult to estimate how efficiently a system will function when it…
A: Given: The system performance is difficult to calculate during the design phase since the design is…
Q: What steps should be taken by organisations in the event of a breach in security?
A: Security Breach: It is the situation in which the fundamental security systems of an organization…
Q: What precisely is it that people study under the category of 'computer science,' and how is it…
A: Introduction: Both computer software and hardware design are studied in computer science. It…
Q: When it comes to the protection of email, do administrators of networks have any moral or ethical…
A: Start: In most cases, network administrators have access to every file and byte of data on a…
Q: If the marks obtained by a student in five different subjects are input through the keyboard, find…
A: ANSWER:-
Q: What part does a trusted platform module (TPM), also known as a security key, play in the process of…
A: Beginning: The technique of encrypting all of the data on a disc is known as whole disc encryption.…
Q: Provide some instances of both software quality assurance and software engineering, as well as…
A: Introduction To ensure the program's quality, we use a method called as software quality assurance…
Q: that you provide a more in-depth explanation of the metrics that are involved in the process of…
A: A software metric is a standard of measure of a degree to which a software system or process has…
Q: What aspects of programming are distinct from scripting, and how do these differences come about?
A: Difference between scripting language and programing language.
Q: The length & breadth of a rectangle and radius of a circle are input through the keyboard. Write a…
A: Code in step 2
Q: Why would it be advantageous for your internet business to make use of cloud computing? What are the…
A: Given: Businesses spend a lot on software to improve operations. Cloud computing lets your firm…
Q: What are some of the things you know about the cloud computing that VMware provides?
A: Cloud does VMware use: VMware Cloud on AWS introduces VMware's enterprise-class Software-Defined…
Q: What procedures are involved in the process of retrieving data from a solid-state disk using a…
A: Introduction: Although the forensic recovery method is distinct from other recovery procedures, it…
Q: In a town, the percentage of men is 52. The percentage of total literacy is 48. If total percentage…
A:
Q: Please inform me of the disadvantages that using the cloud has for schools and their pupils. Is…
A: Given: Tell me about some of the drawbacks that students and instructors face when using cloud…
Q: What does the word "interdependence" refer to in terms of system thinking, and how does it differ…
A: Given: The term "interdependent" refers to objects that are mutually dependent on one another.…
Q: Access and Authentication in Information Security should be examined.
A: Authorization is any mechanism by which a system grants or revokes the right to access some data or…
Q: Shouldn't a succinct overview of the two components that the majority of people say are the most…
A: Operating system: It is software that manages and maintains computing devices, such as smartphones,…
Q: Strategies cyber security specialists might use to effect change
A: Please find the answer below
Q: When Jeff Immelt talks about the "digitalization of the industrial world" and the "industrial…
A: Given: Industry digitalization is a process that evolves through time, and data and data analytics…
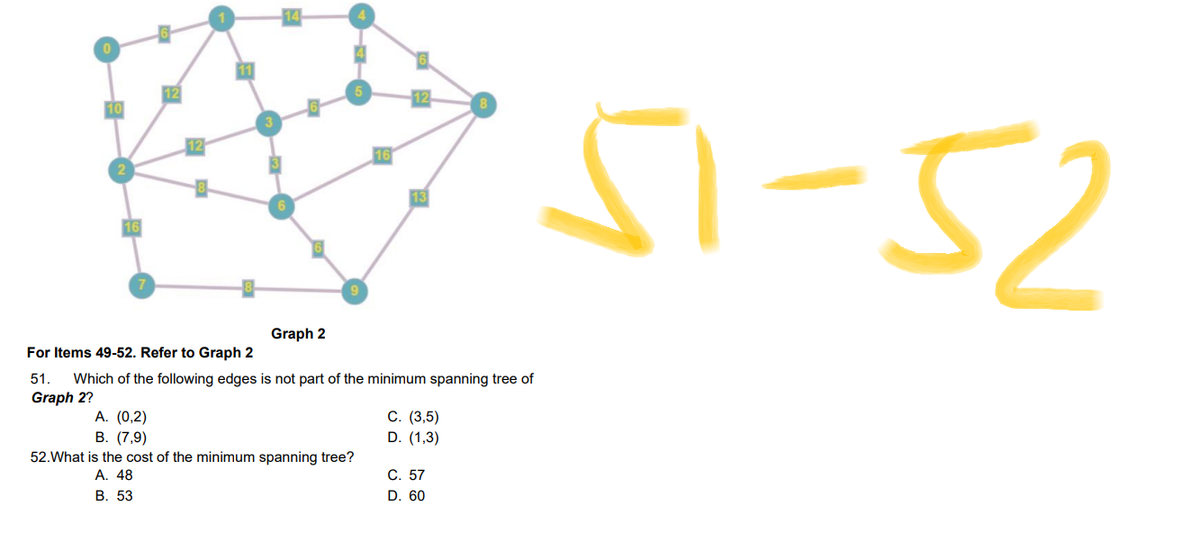
Step by step
Solved in 3 steps with 2 images

- Find the minimum cost spanning tree on the graph above using Kruskal's algorithm. Which of the edges below are included in the minimum cost tree? PLEASE HELP[This is multiple choice#3and4] 3) In the given figure, using Kruskal’s algorithm, which edge should we choose last?a. BCb. ABc. ACd. CDe. None of the above 4) In the given figure, which of the following edges of the given graph are not part of the minimum spanning tree?a. ACb. EFc. AGd. BGe. None of the above12- A Graph consists of four vertices A, B, C and D. If we start from A, which vertex will be visited first of all by breadth-first search (BFS) algorithm? A C D B
- Please help... Adding one more vertices... highlighted with with bold... Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weightIf a minimum spanning tree has edges with values 41, 13, 32 and 39, then what is the length of the minimum spanning tree?a) What is Minimum Spanning Tree. b) State the number of edges in a minimum spanning tree of a network with10vertices. c) State the number of edges in a minimum spanning tree of a network withnver tices.
- ID - 1542553 Problem 2Consider the graph from Problem 1 (Figure 1).The goal is to find single source shortest paths (in particular, the Shortest Paths Tree) starting from source node s (see Weights and Source Node in picture). (i) Find the Shortest Paths Tree (SPT) in G starting with source vertex s using Dijkstra’s algorithm. Show the main steps of the algorithm. Note that the graph has a negative weight edge. Does Dijkstra’s algorithm still find the correct shortestpaths? (ii) Find the Shortest Paths Tree (SPT) in G starting with source vertex s using Bellman-Ford’s algorithm. Show the main steps of the algorithm. (iii) Suppose we want to the shortest path distances between all pairs of nodes such that the shortest paths use intermediate vertices only from the set {a, b, g}. Use the Floyd-Warshall algorithm to compute these distances between all pairs of nodes.Consider flight network having places of departure and destination. Flight network represent Page 4 of 4place name as a node and flight trajectories between palce names are the edges. ConsiderPakistan cities as a node and show the source and destination paths, show all the paths separatelywith their labels and include their code as well.Analyze this scenerio that tree or graph should implement here, justify and also implement thiswith appropiate data structure.Example:Network represents that there are three cities named Karachi, Islamabad and Lahore. Flightschedule from Karachi to Islamabad, Islamabad to Lahore and Lahore to Karchi. Places save asclass having departure time and day also.Note: You are not allowed to use any built-in Data Structure classes to implement abovescenarioLet A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weight spanning tree of G. Round your answer to the nearest integer. Note: I encourage you to add n additional points (for n=1, 2, 3) to your graph and see if you can figure out where these point(s) need to…
- Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weight spanning tree of G. Round your answer to the nearest integer. Attention: Please don't just copy these two following answers, which are not correct at all. Thank you.…Please show step-by-step explanations. Thank you. About the Petersen Graph, (a) The Petersen Graph P is shown below. Assign an edge weight of 1 to each edge of P. Use either Kruskal or Prim’s Algorithm to find a (necessarily minimum weight)spanning-tree of P. you must be clear about whichthe algorithm you choose and show and explain each step leading to the spanning tree.modify this code to find the required output; graph={ 1: [2,3], 2: [1,3], 3: [1,2,5, 4], 4: [6,11,3,5], 5: [7,4,3], 6: [8,4], 7: [5,9], 8: [6], 9: [7,10], 10: [9,12], 11: [12,4], 12: [10,11] } #perform depth-first search def dfs(graph, start, visited, charge): #current node as visited visited.add(start) #Check the Roomba needs to enter the charging station if charge <= 6: print(f" {start} (Charging, {charge} Wh) -> ") charge =12 else: print(f"{start} (Cleaning, {charge} Wh) ->") charge -= 1 #Take he list of adjacent nodes adj_nodes = graph[start] #Visit the unvisited adjacent nodes for node in adj_nodes: if node not in visited: dfs(graph, node, visited, charge) #user to enter the starting node start_node = int(input ("Enter starting node: ")) # Perform depth-first search starting from the starting node visited = set() dfs(graph, start_node, visited, 12) # Sample outputEnter starting node: 11 (Cleaning, 12 Wh) ->2…











